Abstract
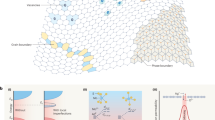
Digital keys are commonly used in today’s hardware security systems. However, the provable destruction of these keys after use remains a challenging problem. Most security primitives built using traditional complementary metal–oxide–semiconductor transistors are not well suited to address this issue because of their volatility and unreliability at small scales. Here we show that the unique physical fingerprint of a 128 × 64 hafnium oxide memristor crossbar array integrated with transistors is capable of provable key destruction. The fingerprint is extracted by comparing the conductance of neighbouring memristors, and it can be revealed only if a digital key stored on the same array is erased. On the basis of this provable key destruction technique, we propose a protocol for logic locking/unlocking that can support secure outsourcing of integrated circuit manufacturing. By leveraging the unique properties of memristors, including reconfigurability and variability, our chip demonstrates the integration of security, memory and computing functionalities into the same circuits, and could be used to develop more secure, compact and efficient memristive hardware systems.
This is a preview of subscription content, access via your institution
Access options
Access Nature and 54 other Nature Portfolio journals
Get Nature+, our best-value online-access subscription
$29.99 / 30 days
cancel any time
Subscribe to this journal
Receive 12 digital issues and online access to articles
$119.00 per year
only $9.92 per issue
Buy this article
- Purchase on Springer Link
- Instant access to full article PDF
Prices may be subject to local taxes which are calculated during checkout





Similar content being viewed by others
Data availability
The data that support the plots within this paper and other findings of this study are available from the corresponding author upon reasonable request.
References
Bonomi, J. & Botta, P. E. Nineveh and its Palaces: the Discoveries of Botta and Layard Applied to the Elucidation of Holy Writ (Illustrated London Library, London, 1852).
Evans, D. The Internet of Things: How the Next Evolution of the Internet is Changing Everything (Cisco, 2011).
Weber, R. H. Internet of Things – New security and privacy challenges. Comput. Law Secur. Rev. 26, 23–30 (2010).
Sahay, S. & Suri, M. Recent trends in hardware security exploiting hybrid CMOS-resistive memory circuits. Semicond. Sci. Technol. 32, 123001 (2017).
Van der Leest, V., Maes, R., Schrijen, G. J. & Tuyls, P. Hardware intrinsic security to protect value in the mobile market. In Proc. Information Security Solutions Europe Conference (ISSE) (eds Reimer, H., Pohlmann, N. & Schneider, W.) 188–198 (Springer Vieweg, 2014).
Gao, Y., Ranasinghe, D. C., Al-sarawi, S. F., Kavehei, O. & Abbott, D. Emerging physical unclonable functions with nanotechnology. IEEE Access 4, 61–80 (2016).
Xie. Y. & Srivastava, A. Mitigating SAT attack on logic locking. In Proc. International Conference on Cryptographic Hardware and Embedded Systems (eds Gierlichs, B. & Poschmann, A.) 127–146 (Springer, 2016).
Roy., J. A., Koushanfar, F. & Markov, I. L. EPIC: ending privacy of integrated circuits. Computer 43, 30–38 (2010).
Holcomb, D. E., Burleson, W. P. & Fu, K. Power-up SRAM state as an identifying fingerprint and source of true random numbers. IEEE Trans. Computers 58, 1198–1210 (2009).
Lofstrom, K., Daasch, W. & Taylor D. IC identification circuit using device mismatch. In Proc. IEEE International Solid-State Circuits Conference Digest of Technical Papers (ISSCC) 372–373 (IEEE, 2000).
Su, Y., Holleman, J. & Otis, B. A. 1.6 pJ/bit 96% stable chip ID generating circuit using process variations. In Proc. IEEE International Solid-State Circuits Conference Digest of Technical Papers (ISSCC) 406–407 (IEEE, 2007).
Xiong, W. et al. Run-time accessible DRAM PUFs in commodity devices. In Proc. International Conference on Cryptographic Hardware and Embedded Systems 432–453 (IACR, 2016).
Wang, Y. et al. Flash memory for ubiquitous hardware security functions: true random number generation and device fingerprints. In Proc. IEEE Symposium on Security and Privacy 33–47 (IEEE, 2012).
Xu, X. & Burleson, W. Hybrid side-channel/machine-learning attacks on PUFs: A new threat? Design, Automation and Test in Europe Conference and Exhibition (DATE) 24–28 (IEEE, 2014).
Pi, S., Lin, P. & Xia, Q. Cross point arrays of 8 nm×8 nm memristive devices fabricated with nanoimprint lithography. J. Vacuum Sci. Technol. B 31, 06FA02 (2013).
Pi, S. et al. Memristor crossbars with 4.5 terabits per inch square density and two nanometer dimension. Preprint at https://arxiv.org/abs/1804.09848 (2018).
Xia, Q. et al. Memristor−CMOS hybrid integrated circuits for reconfigurable logic. Nano Lett. 9, 3640–3645 (2009).
Choi, B. J. et al. High-speed and low-energy nitride memristors. Adv. Funct. Mater. 26, 5290–5296 (2016).
Lee, M. J. et al. A fast, high-endurance and scalable non-volatile memory device made from asymmetric Ta2O5–x/TaO2–x bilayer structures. Nat. Mater. 10, 625–630 (2011).
Pickett, M. D. & Williams, R. S. Sub-100 fJ and sub-nanosecond thermally driven threshold switching in niobium oxide crosspoint nanodevices. Nanotechnology 23, 215202 (2012).
Yang, J. J., Strukov, D. B. & Stewart, D. R. Memristive devices for computing. Nat. Nanotech. 8, 13–24 (2013).
Li, C. et al. Analogue signal and image processing with large memristor crossbars. Nat. Electron. 1, 52–59 (2018).
Li, C. et al. Efficient and self-adaptive in-situ learning in multilayer memristor neural networks. Nat. Commun. 9, 2385 (2018).
Sheridan, P. M. et al. Sparse coding with memristor networks. Nat. Nanotech. 12, 784–789 (2017).
Chen, A. Utilizing the variability of resistive random access memory to implement reconfigurable physical unclonable functions. IEEE Electron Devices Lett. 59, 1172–1182 (2012).
Liu, R., Wu, H., Pang, Y., Qian, H. & Yu, S. Experimental characterization of physical unclonable function based on 1kb resistive random access memory arrays. IEEE Electron Devices Lett. 36, 1380–1383 (2015).
Gao, L., Chen, P., Liu, R. & Yu, S. Physical unclonable function exploiting sneak paths in resistive cross-point array. IEEE Trans. Electron Dev. 63, 3109–3115 (2016).
Liu, R., Wu, H., Pang, Y., Qian, H. & Yu, S. A highly reliable and tamper-resistance RRAM PUF: design and experimental validation. In Proc. IEEE International Symposium on Hardware Oriented Security and Trust (HOST) 13–18 (IEEE, 2016).
Pang, Y. et al. Optimization of RRAM-based physical unclonable function with a novel differential readout method. IEEE Electron Dev. Lett. 38, 168–171 (2017).
Zhang, R. et al. Nanoscale diffusive memristor crossbars as physical unclonable functions. Nanoscale 10, 2721–2726 (2018).
Nili, H. et al. Hardware-intrinsic security primitives enabled by analogue state and nonlinear conductance variations in integrated memristors. Nat. Electron. 1, 197–202 (2018).
Huang, C. Y., Shen, W. C., Tseng, Y. H., King, Y. C. & Lin, C. J. A contact-resistive random-access-memory-based true random number generator. IEEE Electron Dev. Lett. 33, 1108–1110 (2012).
Balatti, S., Ambrogio, S., Wang, Z. & Ielmini, D. True random number generation by variability of resistive switching in oxide-based devices. IEEE J. Emerg. Select. Top. Circuits Syst. 5, 214–221 (2015).
Balatti, S. et al. Physical unbiased generation of random numbers with coupled resistive switching devices. IEEE Trans. Electron Dev. 63, 2029–2035 (2016).
Wei, Z. et al. True random number generator using current difference based on a fractional stochastic model in 40-nm embedded ReRAM. In Proc. IEEE Electron Devices Meeting 4.8.1–4.8.4 (IEEE, 2016).
Jiang, H. et al. A novel true random number generator based on a stochastic diffusive memristor. Nat. Commun. 8, 882 (2017).
Rührmair, U. & Dijk, M. V. PUFs in security protocols: attack models and security evaluations. In Proc. IEEE Symposium on Security and Privacy 286–300 (IEEE, 2013).
Zidan, M. A., Strachan, J. P. & Lu, W. D. The future of electronics based on memristive systems. Nat. Electron. 1, 22–29 (2017).
Jiang, H. et al. Sub-10 nm Ta channel responsible for superior performance of a HfO2 memristor. Sci. Rep. 6, 28525 (2016).
Hu, M. et al. Memristor-based analog computation and neural network classification with a dot product engine. Adv. Mater. 30, 1705914 (2018).
Chen, P. et al. Exploiting resistive cross-point array for compact design of physical unclonable function. In Proc. IEEE International Symposium on Hardware Oriented Security and Trust (HOST) 26–31 (IEEE, 2015).
Zhang, Y. et al. Recryptor: a reconfigurable cryptographic cortex-M0 processor with in-memory and near-memory computing for IoT security. IEEE J. Solid-State Circuits 53, 995–1005 (2018).
Acknowledgements
This work was supported in part by the US Air Force Research Laboratory (AFRL; grant no. FA8750-15-2-0044), and the National Science Foundation (CNS-1749845). Any opinions, findings and conclusions or recommendations expressed in this material are those of the authors and do not necessarily reflect the views of AFRL. R.Z. and P.Y. are on leave from Tianjin University and Huazhong University of Science and Technology, and acknowledge the support from the Chinese Scholarship Council (CSC) under grants 201606250162 and 201606160074, respectively. The authors would like to thank X. Xu and S. Pi for helpful discussions.
Author information
Authors and Affiliations
Contributions
Q.X., D.H., J.J.Y. and H.J. conceived the idea and designed the experiments. P.Y., C.L. and H.J. built the integrated chips. H.J., C.L. and R.Z. performed electrical measurements. Q.X., D.H., J.J.Y and H.J. analysed the data. Y.L. and P.L. helped with experiments and data analysis. Q.X., D.H. and H.J. wrote the manuscript. All authors discussed the results, and commented on and approved the final version of the manuscript.
Corresponding authors
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note: Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Supplementary Information
Supplementary Figures 1–6, Supplementary Table 1, and Supplementary Notes 1–3
Rights and permissions
About this article
Cite this article
Jiang, H., Li, C., Zhang, R. et al. A provable key destruction scheme based on memristive crossbar arrays. Nat Electron 1, 548–554 (2018). https://doi.org/10.1038/s41928-018-0146-5
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1038/s41928-018-0146-5
This article is cited by
-
Tunable stochastic memristors for energy-efficient encryption and computing
Nature Communications (2024)
-
A memristor fingerprinting and characterisation methodology for hardware security
Scientific Reports (2023)
-
Laser printed microelectronics
Nature Communications (2023)
-
Generative complex networks within a dynamic memristor with intrinsic variability
Nature Communications (2023)
-
All-in-one, bio-inspired, and low-power crypto engines for near-sensor security based on two-dimensional memtransistors
Nature Communications (2022)