Abstract
Researchers, policymakers and law enforcement agencies across the globe struggle to find effective strategies to control criminal networks. The effectiveness of disruption strategies is known to depend on both network topology and network resilience. However, as these criminal networks operate in secrecy, data-driven knowledge concerning the effectiveness of different criminal network disruption strategies is very limited. By combining computational modeling and social network analysis with unique criminal network intelligence data from the Dutch Police, we discovered, in contrast to common belief, that criminal networks might even become ‘stronger’, after targeted attacks. On the other hand increased efficiency within criminal networks decreases its internal security, thus offering opportunities for law enforcement agencies to target these networks more deliberately. Our results emphasize the importance of criminal network interventions at an early stage, before the network gets a chance to (re-)organize to maximum resilience. In the end disruption strategies force criminal networks to become more exposed, which causes successful network disruption to become a long-term effort.
Similar content being viewed by others
Introduction
Organized crime forms a great threat to societies across the globe. International criminal drugs organizations try to infiltrate legal businesses and governments, infecting economic branches with corruption and violence. Moreover upcoming threats like cybercrime, child porn, maritime piracy, match fixing and identity theft cause substantial harm and ask for proactive interventions to control the criminal organizations behind them1,2. Government and law enforcement agencies worldwide seek ways to disrupt these criminal organizations effectively, preferably at an early stage. Over the past decade a growing number of studies emerged that provide empirical evidence of the use of social network analyses to get a better understanding of organized crime. These studies show that criminal organizations need to be considered as social networks that form collectives rather than organizations with unique features, such as flexible and non-hierarchical internal relations2,3,4,5,6,7,8. This approach has serious implications for the way we think about law enforcement control of organized crime. It has long been assumed that targeting the ‘kingpin’ leader at the top of the pyramid structured mafia organization, would result in the collapse of the entire criminal organization4,9,10. However, new insights from social network analyses emphasize that the fluidity and flexibility of the social structure of criminal networks makes them highly resilient against these traditional law enforcement strategies7,10. For instance, it was found that even though a drug trafficking network was structurally targeted over a substantial period of time, the trafficking activities continued and its network structure adapted11. Research concerning the resilience of criminal networks involved in the production of ecstasy in the Netherlands lead to the same conclusions10. How can this be explained?
The complexity of criminal networks
An answer to this question can be found within the specific features of the associated ‘dark’ network structures and, more importantly, the conditions under which these exist9,12. Criminal network structures are known to be very complex systems. As Morselli describes it “Criminal networks are not simply social networks operating in criminal contexts. The covert settings that surround them call for specific interactions and relational features within and beyond the network”7. Criminal networks therefore differ from legal networks in that they face a constant trade-off between security and efficiency which directly affects its network structure13. On the one hand illegal activities need to stay concealed from the government or criminal competition. This means that direct communication between co-conspirators concerning illegal activities needs to be restricted to a minimum. On the other hand risks have to be taken in times of action, often demanding highly efficient communication and trust among the participants12,14. Criminal networks therefore continuously balance between efficiency and security according to the given circumstances of the illegal activities.
This trade-off has a direct effect on its network structure as revealed by a study from Baker and Faulkner15. They found that within a covert network, involved in a price-fixing scheme, the most important actors deliberately operated from the peripheries of the network, thus protecting these essential players from immediate detection after government intervention. In addition, Morselli et al. found that the balance between efficiency and security within covert networks was influenced by its network objective. They compared the structure of a criminal network with terrorist networks and showed that criminal networks need more efficiency in their direct lines of communication as compared to terrorist networks. Consequently this made them less secure and more vulnerable to disruption14. This can be explained by the fact that economically driven criminal networks need shorter time frames between action (time-to-task) as opposed to ideologically driven terrorist networks. Terrorist networks might achieve their goals by just one successful terrorist attack. Criminal networks are often action oriented, resulting in higher levels of risk of becoming detected. In response, criminal networks try to remain flexible and agile. This flexibility gives them the ability to adapt quickly to external shocks9,16.
Although these studies help us to understand that remaining flexible is the key to criminal network resilience against disruption, little is known about how these flexible network structures actually recover from an attack and continue their illegal activities. In other words: What actually makes these flexible criminal network structures so difficult to disrupt? In search for an answer, we first need to understand that like every social network, criminal networks are not static, but dynamic in nature3,7. Criminal networks can change for several reasons: as a result of new business opportunities, as a consequence of competition that requires a defensive orientation or as a direct result of law enforcement controls that may lead to the downfall, stagnation or adaptation of the network7. The changing effects of network disruption can therefore only be understood within its dynamics, these networks are truly complex adaptive systems17. Many researchers of criminal networks agree that “studying … the dynamics in criminal networks is probably the most challenging obstacle facing anyone approaching this area.”3,7 Although we recognize the complexity and difficulty that is associated with studying change within social networks, we attempt to capture these dynamics within a computational framework.
Research aim
The aim of this study is twofold. The first aim is to unravel the dynamics of the interaction between disruption and resilience within criminal networks. Understanding these dynamics might have major implications for the way we think about control strategies aimed at organized crime. The second aim is to find the most effective criminal network disruption strategy according to this model, by simulating the effects of different network disruption strategies on network topology. We combine methods of computational modeling and social network analysis to simulate the behavior of a criminal network involved in organized cannabis cultivation based on intelligence data from the Dutch Police.
Organized cannabis cultivation as a criminal network problem
Organized cannabis cultivation is one of the growing problems concerning international organized crime throughout different continents18,19,20,21. Recent studies show that cannabis cultivation is associated with the use of more sophisticated methods, from outdoor cannabis sites towards sophisticated indoor settings. A Dutch study based on a study of 19 closed police investigations reveals that cannabis cultivation is a hard crime, involving extreme violence and mutual rip-offs and is rapidly expanding internationally22. Different studies concerning cannabis cultivation reveal expanding co-operations between criminal networks from Belgium, the Netherlands, Germany and the UK22,23. Outside the EU these trends are also observed within Canada and the US20. These trends of worldwide expansion and increased levels of sophistication and violence, indicates that cannabis cultivation involves professional criminal cooperation with many roles and functions.
Although different countries recognize organized cannabis cultivation as a serious problem, different studies show that law enforcement efforts do not seem to have reduced the problem19,22,24. Current interventions show no significant effect on large-scale growers, although proximately 6000 cannabis cultivation sites are being dismantled annually. A first reason is that thorough investigations of the criminal networks behind large-scale cannabis cultivation are extremely time-consuming and costly24. Secondly law enforcement interventions in for instance The Netherlands aimed at cannabis cultivation can be described as a hit-and-run practice, busting a maximum number of sites with maximum efficiency without paying attention to the potential impact on the associated criminal networks19,24. This seemingly lack of effective strategy within law enforcement interventions was also recognized for the UK situation21. It was observed that law enforcement strategies focused on cannabis cultivation was largely reactive in nature, instead of proactively disrupting the responsible criminal networks. These studies all recognize the fact that law enforcement control strategies aimed at organized cannabis cultivation lack a focused direction and strategy.
These criminal network problems do not exclusively relate to the control of criminal networks involving organized cannabis cultivation, rather they are observed within the control of criminal networks at large4,7,10. Understanding how the observed cannabis cultivation network adapts to network disruption, might therefore contribute to a better understanding of the effectiveness of disruption strategies and network resilience. Before we discuss our research design in detail, we introduce the concepts of criminal network disruption and criminal network resilience.
The concept of criminal network disruption
According to previous studies, three indicators of network destabilization can be distinguished: a reduction in the rate of information flow in the network, a reduction in the ability to conduct its tasks or a failure or significant slowing down of the decision making process25. Therefore network disruption can be defined in general as the state of a network that cannot efficiently diffuse information, goods and knowledge26. Based on previous studies, strategies for criminal network disruption can be divided into two main approaches: The social capital approach and the human capital approach.
The social capital approach
The social capital approach aims at strategic positions that individual actors occupy within criminal networks3,4,6,25,27. Like legal business, criminal networks depend to a large extent on social contacts and the ability to extract the necessary resources for their operations. The advantages that result from having social networks is called social capital28,29. Research in this field is often based on social network analysis (SNA) to identify central actors in the network, that are associated with influential or powerful positions of social capital30. There are many ways within SNA to measure network centrality, but the two most common centrality measures that relate to strategic positions are degree centrality and betweenness centrality3,4.
Degree centrality measures the number of direct contacts surrounding an actor31. Because high scores on degree centrality as associated with better access to resources, these actors are associated with influential and powerful positions within social networks. Since they are important for the flow of information and resources throughout the network, these actors are called hubs. Hubs have major influence on overall network structure, networks that gravitate around a few hubs, for instance, are defined as ‘scale-free’ (centralized) networks. In social network terms these networks are characterized by a power-law degree distribution, which means that a small percentage of actors have a large number of links32. In addition it was found that scale-free networks are resistant against random attacks, because the majority of less connected nodes will more likely be targeted33. Moreover the loss of peripheral nodes for networks with central hubs is less significant for its network survival. On the contrary, decentralized networks are mostly affected by random attacks because the loss of any single actor will be more important for the remainder of the network. Ironically, in the context of targeted attacks, network vulnerability inverses: central actors are more likely targeted, making centralized networks more vulnerable than decentralized networks. Knowledge of a network's structural features is therefore essential before the effects of any network intervention can be understood.
As opposed to degree centrality, betweenness-centrality incorporates the indirect contacts that surround an actor and is calculated by the number of times that an actor serves as a bridge (shortest paths) between other pairs of actors31,34,35. Therefore betweenness centrality represents the ability of some actors to control the flow of connectivity (information, resources etc.) within the network36,37. Because these actors often bridge the ‘structural holes’ between disconnected (sub)groups, these actors are called ‘brokers’. Burt explained the importance of brokers for an increase of social capital within entrepreneurial networks. Entrepreneurs on either side of the brokerage position rely on the broker for indirect access to resources and information beyond their reach36,37. There is empirical evidence that brokers play important roles in connecting criminal networks connecting separate criminal collectives within illegal markets6,7,38,39,40,41,42. By attacking these brokers, important non-redundant opportunities to expand an illegal business might decrease. This is especially relevant for decentralized networks, such as terrorist networks43. Based on these studies betweenness centrality attack is recognized as another important strategy for criminal network disruption. In line with these studies, both centrality strategies will be applied to the organized cannabis cultivation network within our models for network disruption (section 6.3).
Although centrality strategies can be a very effective approach for disrupting centralized or decentralized networks in general, the application of this approach within criminal networks is not without discussion7. Peterson argues that the most central actors in covert networks might also be the most visible. Therefore they might be the most likely to be detected. According to Peterson high degree centrality can therefore also be associated with vulnerability instead of strength57. In addition, Carley, Lee and Krackhardt also demonstrate that the most central actor isn't necessarily the network member with the most leadership potential. For instance, they found that in networks were leadership and centrality are fulfilled by different actors, targeting the central node would not necessarily lead to a downfall of the network and that a targeted leader is not necessarily replaced by the most central actor25. Robins emphasizes that features of network topology also interact with individual-level factors. Therefore qualities of individual actors (e.g. skills, expertise, information and knowledge) cannot be ignored in understanding the complex dynamics within criminal networks58. In addition, a recent finding by Quax, Appoloni and Sloot show the diminishing role of hubs in dynamical processes on complex networks, indicating the need for alternative intervention strategies64. These studies illustrate that although the centrality approach is a useful approach to identify potentially ‘critical’ actors for criminal network disruption, an additional qualitative assessment on the individual level is essential for understanding the effects of network disruption. Moreover, besides centrality propositions, individual qualities (human capital) might be a vital criterion for selecting critical actors for network disruption by itself. This is called the ‘human capital’ approach.
The human capital approach
The importance of the human capital approach to criminal network disruption has been addressed by several authors e.g.3,4,51,59. Human capital is a term originated from economics that is defined as the stock of competencies, knowledge, social and personality attributes, including creativity, embodied in the ability to perform labor so as to produce economic value. Equal to legal business, every criminal market consists of a business process involving different steps of production or activity4,7,10. In each sequent step of the process different information, goods and human capital is exchanged and added to the next, following a chainlike structure. This process can therefore be defined as a value chain60. Every step of the value chain requires a different range of skills and knowledge human capital, depending on the specific characteristics of the illegal activity40,44,45. Illegal entrepreneurs involved in different criminal markets find these ‘human resources’ in embedding trusted social networks. In this way human capital is assembled and integrated into tight goal-oriented criminal collectives.
Sparrow suggested that identifying the actors fulfilling the most specialized tasks offers great opportunities for destabilizing the criminal network. Hence, as these are often thinly populated within the embedding social networks, they are the most difficult to replace if extracted from the network. Sparrow argues that ‘substitutability’ might therefore be an important criterion for network disruption3. To understand the structure of a criminal value chain Cornish introduced the crime scripting method44. This method helps systematize knowledge about the procedural aspects and procedural requirements of crime commission, by generating a blueprint of all sequential phases within the value chain. In addition, Bruinsma and Bernasco combined this crime scripting method with social network analysis, to identify ‘human capital’ and ‘substitutability’ within criminal networks45. They found that specific specialized roles could be identified in different criminal markets by analyzing crime scripts within the context of the criminal network. Morselli and Roy applied this method to study ‘brokerage roles’ within criminal value chains40. Their observations reveal that ‘value chain brokers’ were essential for integrating ‘human capital’ from the criminal network, within the different phases of the value chain. In addition, Spapens identified this brokerage role within Dutch ecstasy production value chains and observed that these brokers not only increased ‘social capital’ within these criminal collectives, but added ‘human capital’ as well8. Hence, these brokers possessed sufficient resources and reputation that is essential to initiate and coordinate a ecstasy production value chain. In fact, these findings emphasize that combining social capital approach and the human capital approach the effects of network disruption might be amplified. It can be concluded therefore that crime script analysis is an important method for identifying ‘human capital’ within criminal value chains.
The concept of criminal network resilience
As a consequence of being disrupted, criminal networks develop the capacity to absorb and withstand disruption and to adapt to change when necessary, that is called network resilience. According to several authors the concept of resilience consists of two aspects: first, the capacity to absorb and thus withstand disruption and secondly the capacity to adapt, when necessary, to changes arising from that disruption46,47.
The first aspect of the resilience concept depends on the level of redundancy that is inhabited in its criminal network structure. The more its network structure is characterized by high levels of redundancy in sense of diversity of relationships between actors, the more options there are to compensate for loses in ‘human capital’ or finding new methods to continue the value chain48. Redundancy enables members of the network to take over tasks of actors that are targeted by successful law enforcement operations. Even if some connections are broken, the diversity of different ties between actors allows the network to function. Redundancy in the network is associated with strong ties between network members. Strong criminal ties offer reciprocated trust, which is essential within the uncertain en hostile criminal environment7. Replacements with a reliable reputation are therefore often found within the social connections directly embedding the actors involved within the criminal business process. These cohesive criminal collectives often initiate from already established social networks of for instance kinship, friendship or affective ties49,50. This means that replacements are often found in short social distances, from this cohesive core.
However, actors with essential skills or knowledge might have to be replaced. If these specialists are thinly populated within these redundant collectives, replacements have to come from the ‘external’ criminal environment. In these settings non-redundant social connections within the embedding network become important for finding ‘human capital’ at a greater social distance from the trusted criminal core. As described above ‘criminal brokers’ are essential catalysts for finding these replacements within the embedding network11. This principle is called the ‘strength of weak ties’, were non-redundant ties within the embedding network offer access to new opportunities, resources and information, that are not available within redundant networks52,53 work offers a framework for understanding criminal network phenomena, such as criminal careers in organized crime. For instance is was found that the social opportunity structure of social ties offers an explanation for late-onset offending and people switching from conventional jobs to organized crime, also later in life50.
Although weak ties might reveal new business opportunities, finding replacements across these connections inhabits great risks to network security for two reasons. First, trust is more easily built between like-minded individuals, as compared to outsiders from different social and ethnic backgrounds8,16. This means that criminal networks in search for capable and trustworthy replacements might need to cooperate with criminal actors for who reliability is difficult to assess. Secondly, coordinating the search for replacements from the embedding network demands more efficient ways of internal and external communication. This increased transfer of information as a result of disruption or internal ‘noise’ within social networks in general, was also observed in a study of artificial complex networks54. This study shows that stochastic resonance in the presence of noise can actually enhance information transfer in hierarchical complex social networks, such as illegal networks54. However, this increased transfer of information containing potential incriminating evidence throughout the network, also increases the risk of exposing the whole network by a single arrest55,56. The capacity to adapt to these changed circumstances of increased risk refers to the second aspect of the resilience concept.
In adapting to these changed security settings, controlling the flow of information becomes the number one priority within illegal networks47. Based on previous studies, this is often achieved through ‘compartmentalization’, meaning that important information is isolated within different compartments or ‘organizational cells’. This strategy prevents that the whole network becomes exposed, if one compartment becomes detected and disrupted48. As described above, this compartmentalization is often found in terrorist networks with longer times to task43. In addition, Baker and Faulkner also found a level of compartmentalization between the core and periphery within illegal price-fixing networks as a result of disruption15. By deliberately separating the flow of information between members within the periphery and the ‘visible’ core, the price-fixing network decreased the chance of the ‘leaders’ becoming exposed after a single arrest. These studies show that in order to adapt to the changes circumstances after disruption, criminal networks tend to organize a form of non-redundancy within its internal flow of information in order to protect its important members from becoming discovered.
In fact, these features make criminal network resilience a paradoxical concept. On the one hand it depends on redundancy, that's essential for finding trustworthy replacements after losses due to disruption. On the other hand it depends on non-redundancy, as the increased risks associated with the search replacement, demand compartmentalization of the flow of information to prevent further detection. The importance of either aspect depends on the given network objectives of recovery or security at a certain moment. This demonstrates again that criminal network resilience is a dynamical process that evolves along the tradeoff between efficiency and security which shapes its network structure accordingly.
Research Design and Datasets
As described above, the aim of this study is to unravel the dynamics of resilience within criminal networks, as a consequence of network disruption. This is done by simulating and observing the mechanisms of disruption and –resilience in a criminal network involved in cannabis cultivation. First, we introduce five different approaches for network disruption, according to strategies based on the ‘social capital’- and ‘human capital’ approach previously described. Secondly, we introduce three models for network recovery, according to the principles associated with the resilience concept described above. These include redundancy and non-redundancy in relation to the social structure embedded in the disrupted criminal network. By simulating these disruption strategies and resilience mechanisms at the same time, we observe the way this affects its network structure in terms of efficiency and security. Our simulations are aimed at a real life criminal cannabis cultivation network that we analyzed from a large unique dataset obtained by a regional criminal intelligence unit resorting under the Dutch Police. This dataset contains information on criminals, criminal relationships and criminal activities collected over the period January 2008–December 2011. The details of the datasets are described in the next section, followed by a description of the final network representation and its properties in terms of degree distribution.
Datasets
The dataset utilized in this research is built by the aggregation of two distinct datasets: Dataset Soft and Dataset Hard, details of these datasets are provided in Appendix A.
Dataset soft (Dsoft)
The data for this dataset was collected by a regional criminal intelligence unit resorting under the Dutch police over the period January 2008–January 2012. The data is primarily retrieved from criminal informants and consists of anonymous intelligence reports on criminals and their criminal relationships involved in serious- and organized crime (N = 6020). Secondly, it contains information and reports from closed criminal cases aimed at organized crime. Both data sources contain specific variables on the individual roles that network actors occupy within different illegal markets in relation to the specific crime scripts (e.g. cannabis cultivation and trade, cocaine trade, heroin trade, ecstasy production and trade, trafficking of human beings etc.). These role variables are scored by intelligence analysts through structural analysis of intelligence reports on role specific information.
Criminal informants have different motives to talk to the police and their identities stay covered for security reasons. In some cases, this makes it difficult to check the facts. For this reason this data is called soft data. Therefore we call this dataset soft (Dsoft). However, based on detailed intelligence reports written after every conversation, the reliability of facts were checked by intelligence analysts by comparing this soft information with facts covered in other police data sources, such as criminal investigations data or street police reports. In addition to intelligence retrieved from criminal informants the dataset therefore also contains observations from street police officers during their duty and information from (closed) criminal investigations. This includes detailed data from wiretaps and surveillance reports, as well as eyewitness and suspect statements containing additional information about criminal relationships. Incidentally information retrieved from online communities (e.g. Facebook) was also used in addition to construct relations between all known actors in the criminal network.
The main strength of this dataset is therefore that it contains detailed narrative information on criminal cooperation, individual roles and involvement within illegal markets from multiple data sources, including informants that are sometimes part of the criminal network themselves. This offers the opportunity to combine methods of crime scripting with social network analysis. Moreover it involves information about important criminal individuals that were never arrested nor detected within criminal investigations. In addition to previous studies on criminal networks that are based on closed criminal investigations, this dataset might give a unique perspective on criminal network structure, including the role of actors that are never observed before.
A weakness of this dataset is that it is in part biased; there is a reasonable possibility that there are some blind spots within the criminal network we do not know about, because there aren't informants within these networks. Another point of concern is that data collection is affected by police priorities. Secondly, not all facts that are written within the intelligence reports can be checked. This might be a risk to reliability of the data, if we want to look at a single criminal relationship in detail. However, for this study we are only interested in features of the overall network structure, therefore our results will not be affected by one or two false reports. Moreover, informants that turn out to be unreliable are fired directly; this results in a kind of natural selection of the most reliable informants. In order to alleviate some of these weak aspects we introduce a second dataset: Dataset Hard.
Dataset hard (Dhard)
This dataset consists of arrest records over the period 2008–2011. The dataset on arrest information consists of persons with a police arrest registration dating from the period 2008 until 2011 (N = 24.284) within the same police region from which the soft data was collected. Every police suspect is registered into a police database with a connection to her or his arrest registrations. This arrest record contains variables of the date, time, place and law article for which they were arrested. This means that in case more actors are arrested for the same felony, they are connected to the same arrest record. Therefore it can be assumed with a reasonable level of certainty, that these actors have a criminal relationship at the time of the arrest registration.
The strength of this dataset is that it was retrieved from police officers themselves, which makes it reliable. For instance, every personal identity is being checked on the bases of identification. In practice police officers need more hard evidence than solely a criminal intelligence report to arrest a potential suspect. Therefore all potential criminal relationships following this dataset are based on more concrete evidence as opposed to dataset soft. Therefore we'll call this dataset hard (Dhard). Secondly it is bulk data over a relatively long period of time containing many criminal relationships. This offers the opportunity two recover a network structure based on arrests. Unfortunately arrest registrations do not contain much narrative information. Another weakness of this dataset is that important network actors might be under represented in this dataset, because they don't get arrested easily as opposed to the more visible working roles in these networks. In addition, these arrest records are also to a certain extend biased towards police priorities.
The description of both datasets reveals that this study isn't immune to the same dark figure problem that influenced previous criminal network research (e.g.7). However, every source of data offers another perspective on the criminal network that is the focus of this study. By combining intelligence reports (soft) with criminal investigations data, surveillance data and arrest data (hard), different perspectives of the same criminal network complement each other in offering us the most optimal observation of the criminal network possible.
The criminal network structure
As described above, the key property of the current dataset is the presence of information about criminal activities of actors, their individual roles and connections to other actors. By combining the two datasets we have recovered the structure of a criminal network involved in multiple criminal markets operating within the Netherlands. In accordance criminal network theory described above, we can distinguish between two network levels: the criminal network involved in a specific illegal market and the (social) embedding macro- network from which criminal cooperation originates8,16,49. The embedding macro network contains all actors and criminal relationships between all actors disregarding their illegal activities. A criminal relationship is defined as the social links that enable individual members of the network to freely exchange information about potential illegal activities. Therefore this embedding network is called the ‘macro network’ and we will denote it by GMacro. By itself, GMacro is built up from the dataset Dsoft, which is collected by criminal intelligence operations as well as the dataset Dhard, which is gathered from arrest registrations. In constructing GMacro, the two datasets show little overlap (see Table 1). This can be explained by the fact that central key players are often protected by the network structure and therefore have a lower chance of becoming arrested, as compared to actors directly involved in the value chain. As a consequence these actors are generally underrepresented within investigative or arrest data, which also characterizes dataset Dhard. In contrast dataset Dsoft is built from criminal intelligence gathering and is collected with the specific aim of identifying the invisible actors, who stay largely unknown within criminal investigations. Both datasets therefore offer a different observation of the same criminal network. The combination of these two observations provides us with a unique empirical perspective of a criminal network structure.
The second level of network structure consists of all actors involved in the specific value chain of organized cannabis cultivation. This second level micro-network is obtained by removals of all actors and connections from GMacro, which are not involved in the value chain of cannabis cultivation as qualitatively scored within Dsoft. This sub-network will be denoted by GVC. Within GVC there is data on the specific roles of individual actors within the value chain of organized cannabis cultivation. Properties of both networks are described in Table 1 and depicted in figure 1.
In order to test the effectiveness of the three network disruption strategies described above, we need specific data on the value-chain activity of the individual actors within the network. Because data on value chain roles is qualitatively scored for all individual actors involved in cannabis cultivation, we focus mainly on the effectiveness of disrupting the cannabis cultivation network GVC as part of the criminal macro network GMacro.
Identical to any social network, criminal networks have no strict boundaries48. Therefore we emphasize that the embedding macro network is in theory a worldwide network10. However, our observations of the embedding criminal network are limited to where the data collection process within the police region ends. Within social network analysis methodology this is called the ‘boundary specification problem’ (e.g.4,7), meaning that setting a boundary of the network as a result of the available data, might affect the results of the applied SNA methodology. But, as described above, replacements are preferably found in the ‘trusted’ and ‘like-minded’ network directly embedding the disrupted criminal network, instead of replacements from outside through other backgrounds. Moreover, from a practical point of view, finding replacements within substantial physical distances would be counterproductive4,8.
Degree Distribution
For one part the effect of different disruption strategies depends on network topology. As described above, one important measure for network topology is the network degree distribution. If the network degree distribution follows a power law, then the network is scale-free. This means, besides other implications, that network robustness depends on actors with a relatively high degree, so-called hubs. If these hubs are attacked the network will fall apart into subnetworks32. We estimate the power-law distribution P(x) = Cx−λ to fit the degree distributions in the GMacro and GVC networks using maximum likelihood estimators as well as a goodness-of-fit based approach to estimate the lower cutoff for the scaling region61, the results of which are shown in Figure 2.
Analysis of the graphs show that for GMacro the degree distribution fits a power-law with a lower cutoff of xmin = 34 and λ = 1.5. For GVC the lower cutoff equals 1 and λ = 1.5. In both cases the p value is relatively high, indicating that with high likelihood these distributions follow a power law distribution. This means that both networks probably are scale-free and might therefore be vulnerable to deliberate attacks, targeting actors with high degree centrality (hubs).
In the next paragraph describe in more detail how it the networks are structured with respect to the value chain structure of the cannabis cultivation.
Value chain configuration of organized cannabis cultivation
As described above, organized cannabis production is a delicate business process, involving many tasks and roles and flow of human capital, information and resources, which can be described in a value chain by using crime script analysis. Fig. 3 shows the result of crime script analysis of an illegal market of cannabis cultivation, containing all phases and corresponding tasks/roles in sequential order8,22,41,62.
Understanding the value chain of a specific criminal activity is important for developing network disruption strategies from the ‘human capital’ approach. Specific roles can be identified, that are critical for value chain continuation. Within the technical system of cannabis cultivation the roles of ‘coordinator’ and ‘growshop owner’ are essential for initiating a criminal collective (Fig. 3). They control almost every stage of the value chain and operate as criminal brokers in bringing essential roles together at the right place and time. Coordinators and Growshop owners are important for the flow of information and keeping the value chain participants together. Therefore these roles can be marked as vulnerable for network disruption from both a ‘human capital’- and ‘social capital’ approach, as they might also score high on degree and betweenness centrality within the value chain network.
Secondly specialists can be identified within the criminal collective, that bring specific knowledge or skills needed to complete the value chain7,8,22. These specialists are often sparsely populated within the embedding macro-network and are therefore often part of more than one value chain at a certain point in time. Within the value chain of cannabis cultivation the network members that fulfill the role of diverting electricity can be identified as specialists for two reasons: First this role requires specific knowledge and technical skills needed for illegally diverting electricity that fits the needs within cannabis cultivation. Secondly these roles demand high levels of trust and reputation. Hence, these ‘electricians’ might retrieve sensitive information about critical locations and participants that is related to their flexible role of specialist22,62. Therefore involvement of these actors increases the risk of information being leaked to competitors or the government63. A trustworthy reputation is therefore essential for these specialists to operate freely. For cannabis networks, finding or replacing these ‘specialists’ is not an easy task because reliability and integrity is not particularly part of the ethics within criminal networks. Therefore network members involved within ‘diverting electricity’ can also be identified as vulnerable targets for network disruption from a ‘human capital’ approach. This will be included as a specific strategy within the disruption model discussed in section 6.1.
As was previously described criminal network resilience against disruption depends on network redundancy. Redundant criminal networks offer many alternatives to replace targeted actors within the network. Figure 4 shows the direct relationships between value chain roles that are derived from the value chain network of cannabis cultivation (Gvc). In this figure the VC roles are also connected if one actor in the social system fulfills more than one role within the value chain (Fig. 3). The size of the actors in Fig. 4 is proportional to the amount of actors having this role within the data. The thickness of the links corresponds to the number of direct connections between actors with these roles within the GVC network.
Observed configuration of the social system of the cannabis cultivation value chain using soft and hard datasets, see also appendix A. Within this system roles are connected if there is at least one link in the value chain network (Gvc) between actors of these roles.
The sizes of the actors correspond with the number of actors fulfilling this role and link thickness corresponds with the total number of links between roles within the data.
The infographic shows that some roles within the value chain are highly connected and some roles are not. This indicates that some actors involved in common roles within GVC might easily be replaced by directly reconnecting the ‘orphaned actors’ with actors with that same role in Gvc (e.g. network members that are involved in ‘coordination’ and ‘taking care of plants’ in fig. 4). For roles that aren't that well connected within Gvc (such as manipulating electricity and building a plantation in fig. 4) replacement isn't that easy, for reaching the possible replacements might take several indirect connections. As described above trust and reputation are the basis for criminal cooperation7,16,42. Therefore actors connected within a specific value chain network are often surrounded by a social structure of social ties (e.g. kinship or friendship) or previous criminal cooperation concerning other criminal activities. As descibed in 5.2 this surrounding social structure is called the ‘embedded macro network’ GMacro. Trustworthy replacements within criminal network are generally found at the shortest paths from the targeted actor towards the nearest potential replacement. This means its also possible that replacements are found trough actors that are part of the embedding macro network but have no involvement in the value chain network of cannabis cultivation at all. These actors from the embedding macro network form a ‘bridge’ between the ‘orphaned actors’ and replacements with the same role in Gvc. Therefore replacement follows the shortest paths through actors from the embedding macro network, instead of solely the value chain network. This interaction between the embedding macro network (GMacro) and the value chain network is therefore important for understanding criminal network recovery after intervention and will be explained further in paragraph 6.3.
Methodology
The second aim of our research is to test the effectiveness of different strategies to disrupt an illegal cannabis cultivation network GVC, taking into account that the network will try to recover itself by replacing targeted actors and relations using ties and connections of the embedding criminal network GMacro. Therefore a modeling framework for both network disruption and network resilience is needed.
Modeling network disruption
From a law enforcement perspective criminal network disruption aims at stopping or frustrating the value chain of a criminal activity by removing active actors from the criminal network. In practice this can be obtained by strategically targeting and arresting individual actors involved in the value chain. The sequential order in which actors are targeted depends on the disruption strategy applied. For this study five different disruption strategies are selected according to the general disruption approaches described above:
Random disruption
-
1
The Randomstrategy follows no preference or ranking during selection of candidates for removal. This strategy can be associated with opportunistic law enforcement control lacking any form of strategy. As describes in section 2, this is sometimes the case within the control of organized cannabis cultivation, for instance randomly busting cannabis cultivation sites and making arrests on the spot.
Two types of social capital disruptionThe social capital approach aims at strategic positions within criminal networks. As described in section 3, this can be divided in two main strategies: degree centrality attack (hubs) and betweenness centrality attack (brokers).
-
2
The Total degreestrategy aims at the actors with highest degree centrality (hubs) within the GVC network. From this approach the order of actors being targeted follows individual degree centrality scores from high to low. Both GMacroand GVC networks have heavy-tailed degree distributions, which might make them vulnerable to these hub attacks (Fig. 2). This strategy is associated with control strategies that focus on ‘the kingpin’. However, as described above the most central actor does not necessarily have to be the most powerful. Leaders might be hidden in anonymous periphery, but because we use intelligence data in addition to investigative data, degree centrality might correlate with powerful positioning (e.g.64).
-
3
The Betweennessstrategy aims at actors with the highest betweenness centrality (bridges) within the GVC network. From this approach the order of actors being targeted follows individual betweenness centrality scores from high to low. This strategy is associated with the ‘key player’ control strategy in law enforcement. This strategy might be highly correlated with coordinators of growshop owners, but could also involve actors in other roles that might be or importance because of their informal social capital within the value chain. It aims at strategically positioned brokers, connecting several criminal groups as described in section 3.1.
Two types of human capital disruption Besides targeting actors based on their general positioning within the criminal network, this approach aims at targeting actors by their individual specific characteristics (Human Capital).
-
4
The Value chain degreestrategy aims at individuals with the highest Value Chain (VC) degree within the GVC network. The VC degree of a particular actor is measured by the amount of links defined within the social system of the value chain configuration (see Fig. 3). This strategy is associated law enforcement controls aimed at actors that inhabit a great reputation. It can be assumed that actors with a higher reputation will be involved within more and different value chains within the value chain network. From a network perspective this means that these actors will automatically have a higher degree centrality and will be more visible within the network.
-
5
The Specific Value Chain Rolestrategy aims at specific ‘human capital’ within a specific criminal value chain. As compared to other strategies, actors are targeted qualitatively based special skills or knowledge and the presumed ‘substitutability’ within the value chain. Based on observations within the data under study and the literature on the cannabis cultivation value chain22,62 the role of ‘diverting electricity’ was selected to analyze this strategy. From this approach the sequence of actors being targeted follows all actors that are labeled for the ‘diverting electricity’ role within the value chain of cannabis cultivation. This strategy is associated with the ‘facilitator’ strategy within law enforcement control, for targeting thinly populated specialists in order to frustrate the operational criminal process.
By simulating these strategies we can measure the effect they will have on the network and cannabis production. For each strategy, different runs are being performed and for each run thirty actors are being removed.
Modeling network resilience
The effect of network disruption cannot be measured without understanding network resilience. Therefore the ability of a criminal network to recover its value chain structure after applying a network disruption strategy has to be simulated. In order to recover the value chain, the actors that are not targeted (orphaned actors) will have to find a replacement that can fill the gap that a targeted value chain actor left behind. This replacement needs the same skills and knowledge (VCrole) as its ancestor. By replacing the actor by someone in the network with the same VCrole, the essential VC links are reestablished and the value chain can be operational again. As described in section 4, these replacements are often found through redundant or non-redundant contacts from the embedding network GMacro. By modeling resilience, we therefore simulate the dynamic interaction between the value chain network GVC and the embedding criminal network GMacro in the search for suitable replacements for network recovery.
At each step of the simulation an actor is targeted by applying one of the disruption strategies. This targeted actor is indicated by nrem. All nrem actors will be accounted for in a set O(nrem) of ‘orphaned’ actors, which were connected to nrem by a value chain connection (VC link). For each broken VC link, it is assumed that recovery will start from these orphaned actors. These actors will be the first to find replacements within the embedding macro-network (GVC) as depicted in Fig. 5.
Dismantling and recovery of a network: (a) Actor A is selected as a target actor by a chosen strategy. (b) Actor A is detached from actors B, C, D and removed from the network. (c) Orphaned actors B and C recover their connections by linking to actor E of the same role as actor A (here: coordinator).
At first target actor (A) is selected by one of the preferred dismantling strategies (Fig. 5a). Actor A has two adjacent VC Links with actors B and C. In the next step (Fig. 5b) target actor A is removed from the network, leaving two dangling links. The orphaned actors B and C tend to recover the lost links by connecting to actor with the same VC role of coordinator as the A actor had by using one of recovering algorithms. In this way the broken VC links are recovered by connecting to actor E (Fig. 5c). In simulating network resilience three recovery mechanism algorithms are applied: random recovery, recovery preferred by distance and recovery preferred by degree. The general recovery algorithm is depicted below.
General recovery algorithm
GVC(N,E) — subnetwork with a set of actors N and set of edges E;
nrem— actor which was removed from GVC;
O(nrem) — set of orphaned actors nO, which were adjacent to nrem;
role(n) — VC role of actor n;
RN(nrem) = {n∈N:role(n) = role(nrem)} — set of actors from GVC which can replace value chain position of actor nrem.
For each orphaned actor nO from O(nrem):
-
1
With likelihood
 evaluate whether or not the lost VC link will be recovered by nO.
evaluate whether or not the lost VC link will be recovered by nO. -
2
If previous step gave positive answer, then select recovery candidate nc from the RN(nrem) following specific preference, which is chosen based on the recovery mechanism.
-
3
Connect actors nO and nc.
Next, we introduce three algorithms, which are based on this general recovery algorithm but have a specific preference among candidates for recovery. See also figure 6.
Random and preferential recoveries of broken VC links are depicted, after strategically removing actor B: (a) Candidates for replacement are chosen randomly without preference. (b) An actor with a smaller distance to orphaned actor A is more likely to be chosen as replacement. (c) An actor with a higher degree is more likely to be chosen as replacement.
Random recovery algorithm
The random recovery algorithm suggests that no candidate from RN(nrem) has preference over others and all of them are treated equally. This algorithm implies that the macro network is heterogeneous and that replacements can be chosen from all parts of the network, hence, at step 2 of the general recovery algorithm candidate nc from RN(nrem) is selected randomly.
Preference by distance recovery algorithm
As described in section 4 trust and skills are important criteria for selecting suitable replacements. Therefore it's more likely that preferred replacements are preferably found within the redundant network of the actors involved in the value chain. This means that candidates with the shortest path from orphaned actors within the macro network (GMacro) will have more chance of becoming a replacement than actors further away. This can be translated into a preference by distance recovery algorithm, in which the selection of replacement of actors from RN(nrem) in step 2 depends on the distance between a possible candidate actor and an orphaned actor. Within this preferential recovery algorithm the likelihood of actor nc to be selected is proportional to  , where d is the distance between the orphaned actor and nc. Within this recovery mechanism, the likelihood that a value chain link will be recovered depends on both the substitutability and the network distance between replacement candidates and orphaned actors.
, where d is the distance between the orphaned actor and nc. Within this recovery mechanism, the likelihood that a value chain link will be recovered depends on both the substitutability and the network distance between replacement candidates and orphaned actors.
Preference by degree recovery algorithm
A second criterion for criminal cooperation is reputation. This means that actors with a good reputation have a higher chance of becoming a replacement than actors with a bad reputation. It can be assumed that actors with a higher reputation will be involved within more and different value chains throughout the overall network (GMacro). As identical to the VC degree disruption strategy, this will be associated with actors with high degree centralities. Therefore we introduce a third recovery algorithm with a preference for replacements by degree-centrality, in which the selection of replacement actors from RN(nrem) in step 2 of the general recovery algorithm depends on the degree centrality of the potential replacement. Within this preferential recovery algorithm the likelihood of actor nc to be selected is proportional to  , where d is the degree of nc within GMacro.
, where d is the degree of nc within GMacro.
Within the general recovery algorithm, the likelihood of value chain link recovery Prewire depends on the exchangeability of the targeted actor. If RN(nrem) = 0 then the connection with an actor of a particular role could not be recovered.
The difference between random recovery (a), distance recovery (b) and degree recovery (c) is depicted in Fig. 6. Here, actor B is targeted by one of the disruption strategies. As a result the orphaned actor A has lost its value chain connection ‘international trade–transporting’ and will therefore try to re-establish a link with a suitable candidate in order to restore the value chain. The list of candidates, who can fulfill the same role as A, is shown in the first column. In case (a) the candidates are chosen randomly and have no preference between each other to be chosen as a candidate for recovery. In case (b) the actors with the shortest distance to A, are more likely to be selected for replacement. In case (c) the actors with the highest degree are more likely to be selected for replacement.
Measuring the effects on network structure
After the disruption strategies and the recovery strategies are applied at the same time, after a number of attacks following the same strategy, we want to measure the impact this has on its networks structure, in terms of efficiency and security. Therefore we introduce the measure of efficiency within the Value Chain network GVC that is computed by the following metric:

In this metric dij corresponds to the distance between actors i and j of GVC and N equals the amount of actors in GVC The denominator creates a measure that varies from 0 to 1, where 1 is complete connectivity and 0 indicates that the network is completely separated into isolated components. Note that in this metric the distance between actors is measured by the shortest paths within the embedding network (GMacro). This implies that some essential values can flow through criminal relationships that are not directly derived from the subnetwork of cannabis cultivation (GVC). The metric shows how efficiently actors within the network can communicate and exchange values (information, goods) between each other65,66.
In addition to the efficiency of the network we introduce a second metric that estimates the influence of network disruption on the secrecy within the value chain network. Criminal network structures arrange a level of secrecy by minimizing the direct transfer of information, thereby reducing the risk of exposing direct involvement in illegal activities of individual members to police surveillance- or intelligence services. Secrecy is strongly associated with the metric of ‘network density’. This measurement is intended to give a sense of how well communication pathways in the network are capable of getting information out to the network's participants. Density (or the equivalent ‘brightness’) is calculated by dividing the number of direct connections by the maximum possible connections within the observed network. Therefore density decreases by a decreasing number of direct connections. This slows down the direct transfer of information throughout network. A network with a high density is more effective thanks to the large number of direct connection between actors, but it has higher vulnerability as well, because if one actor is caught he can provide critical information about other participants of criminal business42. This metric is based on the analysis of network density after interference, in comparison to its initial state. The density, or brightness, of the network is calculated by the following metric:

In this metric E(Gvc) corresponds with amount of links in GVC and N equals to amount of actors in GVC. The values of this metric are also bounded between 0 and 1, where 1 happens to be in complete network where all actors are interconnected and, hence, exposed and 0 indicates that the network is completely dismantled, dark and secure.
Results
In order to test the network resilience of GVC, three sets of simulation experiments were conducted – with random recovery, with distance recovery and degree recovery algorithms. Each simulation was performed on GMacro and because the aim is to disrupt the value chain of organized cannabis cultivation, disruption strategies are targeted at the actors who are specifically part of GVC. In each simulation thirty runs for every disruption strategy were conducted, resulting in an average score for each strategy (the numerical experiments showed that ten runs were enough to get stable results with standard deviations less than 5%). As described above, the role-specific strategy was targeted at all actors involved in the role of ‘diverting electricity’.
Fig. 7 presents the efficiency of the value chain network GVC with random recovery at each step of the law enforcement strategy. In contrast with the aim of the applied strategies, it shows that as the disruption strategies are being applied the efficiency of GVC actually increases. This means that when more specific actors are being targeted from the value chain, the more efficient the network becomes after random recovery. Fig. 7 also indicates that Random and Role-specific disruption strategies slightly increase the network efficiency. From a topological perspective this implies the network is highly resilient and flexible in restoring these crucial value chain facets from its network structure. On the other hand, when the ‘role specific’ specialist strategy is taken into account the network might be much more vulnerable. Hence, the value chain simply ends when a single facet within the technical system of the value chain (as depicted in Figure 4) cannot be restored from its social structure. Therefore, this role specific disruption strategy is only effective in the long run (after removing 18 actors), when the VC network is not able to replace the specialists of ‘diverting electricity’ any more. Furthermore the VC degree attacks seem to have the most disrupting effect on the network efficiency during the initial steps of the simulation. In summary, Fig. 7 shows, counter intuitively, that when the criminal network recovers itself randomly from all five disruption strategies, the network becomes more efficient as compared to its previous state.
In Fig. 8 the results for the simulation of ‘preference by distance’ recovery is depicted. For this recovery mechanism the network efficiency does increase with a slightly lower rate in comparison to the previous case with random recovery due to the fact that fewer shortcuts appear in the network during the recovery process. These results show that if the network restores itself by finding replacements that are close, the VC disruption strategy will have the biggest impact on the network efficiency.
In Fig. 9 the results for simulation with ‘preference by degree’ recovery are depicted. This means that the VC network prefers to replace someone by actors that are most easy to find, because they are more visible within the network. This recovery mechanism shows almost the same pattern as the preference by ‘distance recovery’ mechanism.
In addition to these simulations, Fig. 10 shows the roles that are removed from the network by applying three different disruption strategies (‘Random’ and ‘Role-specific’ strategies showed no relevant effects). This figure indicates the difference in impact that the three interventions have on specific roles within the value chain. In accordance with criminal network theory, it shows that ‘visible’ roles like taking care of the plants and transporting the product are vulnerable to these network disruption strategies. In general these roles are directly involved in the value chain and as a result score high on degree centrality. But it is important to note that central key player roles, like Coordinator, International trade and Financing also seem to be highly affected. This implies that these central key players are not that much concealed in the criminal network, as was assumed in previous studies. Furthermore Fig. 10 shows that ‘specialist’ roles, like ‘diverting electricity’ and ‘building plantation’, are not affected by these strategies and are therefore the ones that might be protected within the network structure.
Fig. 11 depicts what happens with the density (brightness) of value chain network GVC, before and after applying the disruption strategies. It shows that the brightness of the value chain network actually increases as a consequence of intervention. This is a result of the fact that network members that try to continue criminal activities are forced to communicate efficiently as a result of the applied network disruption strategy. Hence in order to recover the value chain, these members have to act as brokers to establish new value chain relationships. Consequently overall network density increases and it becomes more redundant after each intervention, forcing the cannabis cultivation value chain network to expose itself increasingly from the dark.
Discussion
In this paper we present the impact of dynamic network recovery on the effectiveness of four different criminal network disruption strategies. A unique dataset of a large complex criminal network involved in organized cannabis cultivation was the starting point for the simulation and analyses of these disruption strategies. In addition three different network recovery mechanisms were investigated, in order to assess the effects on network structure in terms of network efficiency and security (secrecy).
Previous studies of criminal network resilience showed that coordinators try to keep a social distance from the actual flow of illicit goods within the value chain. These key players therefore limit their direct connections to actors involved in executive tasks, to minimize the risk of exposure10,15,42,40,67. Based on these studies, high scores for degree and betweenness centrality were expected for executive actors directly involved within the technical value chain of cannabis cultivation. This hypothesis is partly consistent with our observations for the roles of ‘transport’ and ‘taking care of plantation’ (see Fig. 10), which are vulnerable to degree- and betweenness attacks. However our results also show, that central key-player roles within the value chain of cannabis cultivation, such as ‘coordinator’, ‘financing’ and ‘(inter)national trade’, are highly visible and therefore vulnerable to degree centrality attacks as well (see Fig. 4 and Fig. 10). From an efficiency/security perspective, this implies that the structure of the observed cannabis cultivation network is very efficient and flexible, but rather insecure. Hence, if these key players become exposed, the whole value chain might become visible. How can this be explained? The answer to this question is concealed into two factors: a) specific features of the cannabis cultivation process b) the observed properties of the dataset.
Cannabis cultivation is a delicate process, involving many roles and functions. In order to bring these roles together at a certain time and place, the role of ‘coordinator’ is essential for retaining the technical system of the value chain (Fig. 2). To fulfill this role, information needs to be exchanged efficiently through the value chain network. Coordinators therefore need to occupy strategic hub or bridge positions within the network, naturally resulting in higher than average scores on degree and betweenness centrality observed within our data.
However, in practice this doesn't necessary make these actors easy targets for network disruption strategies that focus on high degree- or betweenness positions, since these vulnerable positions are also recognized by criminal networks themselves. Non-redundant and compartmentalized ways of communication are applied, keeping these central key players highly concealed from direct involvement within the value chain7,10,12,14,15,47. As a consequence, reliable incriminating evidence of involvement of the direct involvement of these ‘critical actors’ within illegal markets and activities is harder to retrieve, as compared to actors directly involved within operational activities of the value chain. This explains why these actors can operate from the core of the network but stay concealed in the dark at the same time. However, this is still in contrast with the high levels of ‘visibility’ these key players seem to have as we observed from the data (see also Appendix A). An explanation can be found within the detailed properties of our dataset:
Empirical criminal network research is often based on a single source of data, such as closed criminal investigations e.g4,8,14,15,16. These datasets often contain detailed observations of the behaviors and roles of the suspects under investigation. However, due to limited resources and time, criminal investigations generally start off with a specified and restricted objective. Depending on this objective, the scope of data collection within these investigations is naturally confined by the jurisdiction, money or law enforcement capacity7. Because of these investigative boundaries, chances that powerful or influential actors become exposed within criminal investigation data are relatively low. To overcome this potential bias in our study, multiple data sources were combined to retrieve the final network representation. Some of the data-sources were criminal informants, who sometimes are part of the criminal activities themselves and operate as direct eyewitnesses for ‘unknown’ criminal cooperation. One of the initial goals of this specific intelligence process is deliberately discovering ‘hidden’ critical actors, who try to keep their identities concealed in the dark. These unique data properties offer us a different perspective on the criminal network structure, often hidden within data solely retrieved from criminal investigations. This offers another explanation for the visibility of the ‘hubs’ observed within our results.
We recognize that our dataset is not immune to missing data and boundary specification problems and we understand the difficulty involved with retrieving reliable criminal network data. But, interestingly our results emphasize the importance of ‘no boundary’ intelligence gathering focused on criminal networks at a ‘macro’ level, for retrieving a better strategic understanding of the way these networks operate and react. Combining multiple sources of data on criminal cooperation seems to be essential in confining these data validity problems. The importance of a ‘no boundary’ intelligence gathering strategy, was also one of the results of a recent study by Dijkstra et al.68 that show how a dark population of susceptible and infected drug users in Russia can be identified on the basis of social media information. This strategy opens the door for actually seeking rather than assuming criminal network structure7. In addition, our study shows the importance of applying combinations of methods to unravel the complex dynamic network structures. The knowledge generated by combining social network analysis with computational simulation in this paper, might be of direct relevance for thinking about the effectiveness of control strategies of organized crime on an operational level.
Conclusion
The aim of this study is to unravel the dynamics of resilience within criminal networks, as a consequence of network disruption. Based on the numerical studies of four different disruption strategies and three different recovery mechanisms presented here, it can be concluded that disruption of the criminal cannabis network is relatively ineffective. After applying multiple removals of actors the network efficiency is hardly affected. On the contrary, efficiency actually increases over time for the value chain degree disruption strategy, as a direct result of efficient network recovery. It was shown that the integration of a replacement within the network leads to new shortcuts, which in turn reduces overall dimensionality. Our results point out that a delicate criminal process, such as cannabis cultivation, is organized in a flexible and adaptive network structure, which is highly resilient against network disruption.
In part these results can be explained by the natural evolution of these criminal networks over time. As reciprocal connections within the embedding macro-network expand over time, existing connections between value chain members might have become sub-optimal. However, if the value chain itself is still functional, these ‘inefficient’ connections within the value chain configuration might not cause any problems for a criminal value chain to evolve. In fact, they might even increase security within the value chain, by naturally shaping the network in non-redundant way. Within these settings, chances are that in search for a replacement non-redundant value chain connections become optimized (redundant), leaving the network more efficient then in its previous state.
Previous criminal network studies attribute this phenomenon to a ‘snowball effect’, by which ‘structural holes’ between different criminal sub-networks dry out by increasing reciprocal social relationships over time (e.g. friendship, kinship, affective)52. As new illegal opportunities for criminal network expansion emerges, this process starts all over again leading to further network expansion16. According to this interpretation, our results emphasize that interference in an established ‘old’ value chain network will be less effective than intervening in a recently established criminal network or value chain. In fact, the best way to disrupt a criminal network might be not to apply any disruption strategy at all.
These conclusions might sound disturbing for government- and law enforcement that fight to control criminal networks on a daily basis. However, we need to realize that network effectiveness depends on both efficiency as well as secrecy9,14,15,55. The capability of criminal networks to organize secrecy after an attack depends on the flexibility of the network to benefit both from the redundancy as well as the non-redundancy that's inhabited within its network structure, according to the circumstances. Redundancy is needed when looking for trustworthy replacements within the embedding network. In addition, non-redundancy is essential for finding replacements that are difficult to find at a greater social distance and for keeping critical roles and information differentiated and secret, in order to prevent revealing the whole network by one arrest. From this perspective, Fig. 11 shows that the number of actors close to the average degree centrality increases, meaning that also ‘not so well-connected’ actors will become more visible than before disruption strategies were applied. This means that after every attack the criminal network becomes more and more redundant. Forcing the network to become efficient, but at the price of a higher visibility (brightness), the network becomes less ‘dark’. The criminal network might even become imbalanced, leading to progressively more exposure after replacements are integrated within its structure.
From a network resilience perspective, overall network exposure increases the risk to reveal the critical actors for value chain survival, such as specialists from which multiple criminal value chains have become dependent. Because these specialists are underrepresented within the macro-network, these roles are hard to replace. Moreover replacing specialists demands direct interference of central brokers (coordinators) within the value chain, leading to even more exposure of these strategic network positions7. In this sense, our results indicate that network disruption causes these networks to become more efficient at first, but rather ineffective in the end as recovery forces them to light up more and more from the dark.
This increased visibility might induce a serious change within agencies involved in contemporary law enforcement control of organized crime, as new opportunities for surveillance and advanced intelligence gathering arise to identify and target more critical actors, specialists or even potential future replacements. With this strategy, the network resilience progressively declines and additional cracks within network structure will emerge in the long run, offering more specific disruption opportunities in the end. Our results emphasize the importance of considering these criminal network structures within their complex adaptive dynamics, instead of focusing on a snapshot of a group at a certain point in time. In practice this means that disrupting a criminal network demands a long-term consistent intervening effort.
A popularized version of some of this research has been presented in a scientific documentary on Criminal Networks by the Dutch National TV network VPRO69.
References
Europol. OCTA: EU Organized Crime Threat Assessment. European Police Office, the Hague, The Netherlands (2011).
United Nations Office on Drugs and Crime. The globalization of crime: A transnational organized crime threat assessment. United Nations publication, Vienna (2010).
Sparrow, M. The application of network analysis to criminal intelligence: an assessment of the prospects. Social Networks 13, 251–274 (1991).
Klerks, P. P. H. M. The network paradigm applied to criminal organizations. Connections 24, 53–65 (2001).
Krebs, V. E. Mapping networks of terrorist cells. Connections 24(3), 43–52 (2001).
Natarajan, M. Understanding the structure of a large heroin distribution network: A quantitative analysis of qualitative data. J. of Quant. Criminology 22(2), 171–192 (2006).
Morselli, C. Inside Criminal Networks. New York: Springer. (2009).
Spapens, T. Macro networks, collectives and business processes: An integrated approach to organized crime. Eur. J of Crime, Crim. Law and Crim. Justice 18, 185–215 (2010).
Raab, J. & Milward, H. B. Dark Networks as Organizational Problems: Elements of a Theory. J. of Publ. Administr. and Theory 13(4), 413–439 (2003).
Spapens, T. Interaction between criminal groups and law enforcement: the case of ecstasy in the Netherlands. Global Crime 12(1), 19–40 (2011).
Morselli, C. & Petit, K. Law enforcement disruption of a drug importation network. Global Crime 8(2), 109–130 (2007).
Erickson, B. Secret societies and social structure. Social Forces 60, 188–210 (1981).
Toth, N., Gulyas, L., Legendi, R. O., Duijn, P. A. C., Sloot, P. M. A. & Kampis, G. The importance of centralities in dark network value chains. Eur. Phys. J. Special Topics 222, 1413–1439 (2013).
Morselli, C., Giguère, C. & Petit, K. The efficiency/security trade-off in criminal networks. Social Networks 29(1), 143–153 (2006).
Baker, W. E. & Faulkner, R. R. The social organization of conspiracy: illegal networks in the heavy electrical equipment industry. American Sociological Review 58, 837–860 (1993).
Kleemans, E. R. & Bunt, H. G. The Social embeddedness of Organized Crime. Transnational Organized Crime 5, 19–36 (1999).
Sloot, P. M. A., Kampis, G. & Gulyas, L. Advances in dynamic temporal networks: understanding the temporal dynamics of complex adaptive networks. Eur. Phys. J. Special Topics 222, 1287–1293 (2013).
Bouchard, M. A capture-recapture derived method to estimate cannabis production in industrialized countries. First annual conference of the International Society for the Study of Drug Policy, Oslo, Norway. (2007b).
Decorte, T. The case of small-scale domestic cannabis cultivation. Int J. of Drug Policy 21, 271–275 (2010).
Malm, A., Nash, R. & Vickovic, S. Co-offending networks in cannabis cultivation. World Wide Weed: Global Trends in Cannabis Cultivation and Its Control 127, (2011).
Potter, G. R. Weed, need and greed: A study of domestic cannabis cultivation. Free Association. (2010).
Spapens, T., Van de Bunt, H. G. & Rastovac, L. The world behind cannabis cultivation. De wereld achter de wietteelt. Den Haag: Boom Juridische Uitgevers (2007).
Potter, G. R., Bouchard, M. & Decorte, T. The globalization of cannabis cultivation. World Wide Weed: Global Trends in Cannabis Cultivation and Its Control. 1–20 (2011).
Wouters, M. Controlling cannabis cultivation in the netherlands. In: Korf, D. J. (ed.) Cannabis in Europe: dynamics in perception, policy and markets. Lengerich: Pabst Science Publishers. (2008).
Carley, K. M., Ju-Sung, L. & Krackhardt, D. Destabilizing networks. Connections 24(3), 79–92 (2002).
Carley, K. M., Dombroski, M., Tvetovat, M., Reminga, J. & Kamneva, N. Destabilizing Dynamic Covert Networks. In: Proceedings of the 8th International Command and Control Research and Technology Symposium (2003).
Schwartz, D. M. & Rouselle, T. D. A. Using social network analysis to target criminal networks. Trends in Organised Crime 12, 188–207 (2009).
Coleman, J. S. Foundations of social theory. Harvard University Press, Cambridge, MA. (1990).
Hulst, R. C. Van der. Introduction to Social Network Analysis (SNA) as an investigative tool. Trends in Organized Crime 12(2), 101–121 (2009).
Cook, K. & Burt, R. S. Social capital: Theory and Research. New York: Aldine de Gruyter. 31–56 (2001).
Wasserman, S. & Faust, K. Social network analysis: Methods and applications 8. Cambridge university press (1994).
Albert, R., Hawoong, J. & Barabási, A. Error and attack tolerance of complex networks. Nature 406, 378–382 (2000).
Watts, D. J. & Strogatz, S. H. Collective dynamics of small world networks. Nature 393(6684), 440–442 (1998).
Freeman, L. C. Centrality in social networks conceptual clarification. Social networks 1, 215–239 (1979).
Borgatti, S. P. The key player problem. In: Breiger, R., Carley, K. & Pattison, P. (Eds.) Dynamic Social Network Modeling and Analysis: Workshop Summary and Papers. National Academy of Sciences Press. 241–252 (2003).
Burt, R. S., Joseph, E. J. & James, T. M. Personality correlates of structural holes. Social Networks 20, 63–87 (1998).
Burt, R. S. Structural holes versus network closure as social capital. In: Lin, N., Cook, K. S. & Burt, R. S. (Eds.). Social Capital: Theory and Research, New Brunswick: Transaction Punblishers. 31–56 (2008).
Boissevain, J. Friends of Friends: Networks, Manipulators and Coalitions. Oxford: Basil Blackwell. (1974).
Coles, N. It's not what you know, but who you know that counts: Analyzing criminal crime groups as social networks. Brit. J. of Criminology 41, 580–594 (2001).
Morselli, C. & Roy Brokerage qualifications in ringing operations. Criminology 46(1), 71–98 (2008).
Morselli, C. Structuring Mr. Nice: Entrepreneurial opportunities and brokerage positioning in the cannabis trade. Crime, Law and Social Change 35, 203–44 (2001).
Klerks, P. P. H. M. Big in Hash: theory and practice of organized crime. Antwerpen: Samsom en Kluwer Rechtswetenschappen (2000).
Krebs, V. E. Mapping networks of terrorist cells. Connections 24, 43–52 (2002).
Cornish, D. B. The Procedural Analysis of Offending and Its Relevance for situational prevention. In: Clarcke, R. ed. (Ed.) Crime Prevention Studies 3, 151–196 (1994).
Bruinsma, G. & Bernasco, W. Criminal groups and transnational illegal markets. Crime, Law and Social Change 41, 79–94 (2004).
Bouchard, M. On the resilience of illegal drug markets. Global Crime 8(4), 325–344 (2007).
Ayling, L. Criminal Organizations and resilience. Int. J. of Law Crime and Justice 37, 182–196 (2009).
Williams, P. Transnational criminal networks. In: Arquilla, J. & Ronfeldt, D. (Eds.), Networks and Netwars. Santa Monica: Rand. (2001).
McCarthy, B., Hagan, J. & Cohen, L. Uncertainty, cooperation and crime: understanding the decision to co-offend. Social Forces 77(1), 155–176 (1998).
Kleemans, E. R. & De Poot, C. J. Criminal careers in organized crime and social opportunity structure. Eur. J. of Criminology 5, 69–98 (2008).
Morselli, C. Assessing vulnerable and Strategic positions in a criminal network. l of Contemporary Criminal Justice 26(4), 382–392 (2010).
Granovetter, M. The strength of weak ties: a network theory revisited. Sociological Theory, 201–233 (1983).
Hagen, J. & McCarty, B. Getting into street crime: the structure and process of criminal embeddedness. Social Science Research 24, 63–95 (1995).
Czaplicka, A., Holyst, J. A. & Sloot, P. M. A. Noise enhances information transfer in hierarchical network. Sci. Rep. 3, 1223 (2013). (10.1038/srep01223).
Lindelauf, R., Borm, P. & Hamers, H. The influence of secrecy on the communication structure of covert networks. Social Networks 31(2), 126–137 (2009).
Lauchs, M. A., Keast, R. L. & Chamberlain, D. Resilience of a corrupt police network: the first and second jokes in Queensland. Crime, Law and Social Change 57(2), 195–207 (2012).
Peterson, M. Applications in Criminal Analysis: A Sourcebook. Westport: Greenwood Press. (1994).
Robins, G. Understanding individual behaviours within covert networks: the interplay of individual qualities, psychological predispositions and network effects. Trends in Organized Crime 12, 166–187 (2008).
Tsvetovat, M. & Carley, K. M. Bouncing back: Recovery mechanisms of covert networks. NAACSOS Conference 2003. (2003).
Gottschalk, P. Value configurations in organized crime. Policing & Society 19(1), 47–57 (2009).
Clauset, A., Shalizi, C. R. & Newman, M. E. J. Power-law distributions in empirical data. SIAM-Review 51(4), 661–703 (2009).
Emmet, I. & Broers, J. The Green Gold. Report of a study of the cannabis sector for the National Threat assessment of Organized Crime. Zoetermeer: KLPD-IPOL (2008).
Kleemans, E. R., Brienen, M. E. I. & Van de Bunt, H. G. Georganiseerde criminaliteit in Nederland. Tweede rapportage op basis van de WODC monitor. Den Haag: BJU. (2002). http://www.wodc.nl.
Quax, R., Appoloni, A. & Sloot, P. M. A. The diminishing role of hubs in dynamical processes on complex networks. J. R. Soc. Interface, (2013) in press.
Bienenstock, E. J. & Bonacich, P. Balancing efficiency and vulnerability in social networks. Dynamic social network modeling and analysis: Workshop summary and papers, 253–264. Washington, DC: The National Academy of Sciences. (2003).
Memon, N. & Larsen, H. L. Structural analysis and destabilizing terrorist networks. Conference on Data Mining DMIN'06, 296–302 (2006).
Dorn, N., Oette, L. & White, S. Drugs Importation And The Bifurcation Of Risk: Capitalization, Cut Outs and Organized Crime. Brit. J. of Criminology 38, 537–560 (1998).
Dijkstra, L. J., Yakushev, A. V., Duijn, P. A. C., Boukhanovsky, A. V. & Sloot, P. M. A. Inference of the Russian drug community from one of the largest social networks in the Russian Federation. Quality & Quantity 37, pp. 1–17 (2013).
VPRO. http://www.youtube.com/watch?v=ZbFGrq9mWmU (date of access: December 17, 2013).
Acknowledgements
This work is supported by the Leading Scientist Program of the Russian Federation, contract 11.G34.31.0019, as well as by the Complexity Institute of NTU, Singapore. PMAS also acknowledges the support from the FET-Proactive grant TOPDRIM, number FP7-ICT-318121. This work is also supported by the Government of Russian Federation under Grant 074-U01.
Author information
Authors and Affiliations
Contributions
P.M.A. Sloot conceived and directed the research, P.A.C. Duijn provided the data and interpreted the social-criminal dynamics, V. Kashirin performed the data mining and the value-chain network simulations. Sloot and Duijn wrote the manuscript, Kashirin prepared the figures. All authors reviewed the manuscript.
Ethics declarations
Competing interests
The authors declare no competing financial interests.
Electronic supplementary material
Supplementary Information
SI: Properties of hard- and soft- datasets used in this study
Rights and permissions
This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported License. To view a copy of this license, visit http://creativecommons.org/licenses/by-nc-nd/3.0/
About this article
Cite this article
Duijn, P., Kashirin, V. & Sloot, P. The Relative Ineffectiveness of Criminal Network Disruption. Sci Rep 4, 4238 (2014). https://doi.org/10.1038/srep04238
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/srep04238
This article is cited by
-
A large-scale empirical investigation of specialization in criminal career
Scientific Reports (2023)
-
Using network analysis to identify leverage points based on causal loop diagrams leads to false inference
Scientific Reports (2023)
-
Structural resilience and recovery of a criminal network after disruption: a simulation study
Journal of Experimental Criminology (2023)
-
Navigating Criminal Responsibility in the Digital Marketplace: Implications of Network-Neutral Help Behavior and Beyond-5G Networks in E-Commerce Transactions
Journal of the Knowledge Economy (2023)
-
Multiplex key roles to disrupt criminal networks
Social Network Analysis and Mining (2023)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.

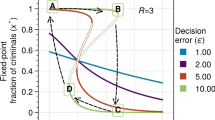
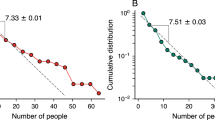





 evaluate whether or not the lost VC link will be recovered by nO.
evaluate whether or not the lost VC link will be recovered by nO. 




