Abstract
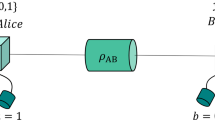
Cryptographic key exchange protocols traditionally rely on computational conjectures such as the hardness of prime factorization1 to provide security against eavesdropping attacks. Remarkably, quantum key distribution protocols such as the Bennett–Brassard scheme2 provide information-theoretic security against such attacks, a much stronger form of security unreachable by classical means. However, quantum protocols realized so far are subject to a new class of attacks exploiting a mismatch between the quantum states or measurements implemented and their theoretical modelling, as demonstrated in numerous experiments3,4,5,6. Here we present the experimental realization of a complete quantum key distribution protocol immune to these vulnerabilities, following Ekert’s pioneering proposal7 to use entanglement to bound an adversary’s information from Bell’s theorem8. By combining theoretical developments with an improved optical fibre link generating entanglement between two trapped-ion qubits, we obtain 95,628 key bits with device-independent security9,10,11,12 from 1.5 million Bell pairs created during eight hours of run time. We take steps to ensure that information on the measurement results is inaccessible to an eavesdropper. These measurements are performed without space-like separation. Our result shows that provably secure cryptography under general assumptions is possible with real-world devices, and paves the way for further quantum information applications based on the device-independence principle.
This is a preview of subscription content, access via your institution
Access options
Access Nature and 54 other Nature Portfolio journals
Get Nature+, our best-value online-access subscription
$29.99 / 30 days
cancel any time
Subscribe to this journal
Receive 51 print issues and online access
$199.00 per year
only $3.90 per issue
Buy this article
- Purchase on Springer Link
- Instant access to full article PDF
Prices may be subject to local taxes which are calculated during checkout




Similar content being viewed by others
Data availability
The datasets generated during the current study are available from D.P.N. and C.J.B. on reasonable request.
Code availability
The custom code generated during the current study is available from the corresponding authors on reasonable request.
References
Rivest, R. L., Shamir, A. & Adleman, L. A method for obtaining digital signatures and public-key cryptosystems. Commun. ACM 21, 120–126 (1978).
Bennett, C. H. & Brassard, G. Quantum cryptography: public key distribution and coin tossing. Theor. Comput. Sci. 560, 7–11 (1984).
Zhao, Y., Fung, C.-H. F., Qi, B., Chen, C. & Lo, H.-K. Quantum hacking: experimental demonstration of time-shift attack against practical quantum-key-distribution systems. Phys. Rev. A 78, 042333 (2008).
Lydersen, L. et al. Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photon. 4, 686–689 (2010).
Gerhardt, I. et al. Full-field implementation of a perfect eavesdropper on a quantum cryptography system. Nat. Commun. 2, 349 (2011).
Weier, H. et al. Quantum eavesdropping without interception: an attack exploiting the dead time of single-photon detectors. New J. Phys. 13, 073024 (2011).
Ekert, A. K. Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67, 661 (1991).
Bell, J. S. On the Einstein Podolsky Rosen paradox. Phys. Phys. Fiz. 1, 195–200 (1964).
Mayers, D. & Yao, A. Self testing quantum apparatus. Quantum Inf. Comput. 4, 273–286 (2004).
Acín, A. et al. Device-independent security of quantum cryptography against collective attacks. Phys. Rev. Lett. 98, 230501 (2007).
Vazirani, U. & Vidick, T. Fully device-independent quantum key distribution. Phys. Rev. Lett. 113, 140501 (2014).
Arnon-Friedman, R., Dupuis, F., Fawzi, O., Renner, R. & Vidick, T. Practical device-independent quantum cryptography via entropy accumulation. Nat. Commun. 9, 459 (2018).
Gisin, N., Ribordy, G., Tittel, W. & Zbinden, H. Quantum cryptography. Rev. Mod. Phys. 74, 145–195 (2002).
Scarani, V. et al. The security of practical quantum key distribution. Rev. Mod. Phys. 81, 1301–1350 (2009).
Lo, H.-K., Curty, M. & Tamaki, K. Secure quantum key distribution. Nat. Photon. 8, 595–604 (2014).
Acín, A., Gisin, N. & Masanes, L. From Bell’s theorem to secure quantum key distribution. Phys. Rev. Lett. 97, 120405 (2006).
Braunstein, S. L. & Pirandola, S. Side-channel-free quantum key distribution. Phys. Rev. Lett. 108, 130502 (2012).
Lo, H.-K., Curty, M. & Qi, B. Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2012).
Rubenok, A., Slater, J. A., Chan, P., Lucio-Martinez, I. & Tittel, W. Real-world two-photon interference and proof-of-principle quantum key distribution immune to detector attacks. Phys. Rev. Lett. 111, 130501 (2013).
Ferreira da Silva, T. et al. Proof-of-principle demonstration of measurement-device-independent quantum key distribution using polarization qubits. Phys. Rev. A 88, 052303 (2013).
Liu, Y. et al. Experimental measurement-device-independent quantum key distribution. Phys. Rev. Lett. 111, 130502 (2013).
Brunner, N., Cavalcanti, D., Pironio, S., Scarani, V. & Wehner, S. Bell nonlocality. Rev. Mod. Phys. 86, 419–478 (2014).
Barrett, J., Hardy, L. & Kent, A. No signaling and quantum key distribution. Phys. Rev. Lett. 95, 010503 (2005).
Masanes, L. Universally composable privacy amplification from causality constraints. Phys. Rev. Lett. 102, 140501 (2009).
Reichardt, B. W., Unger, F. & Vazirani, U. Classical command of quantum systems. Nature 496, 456–460 (2013).
Ho, M. et al. Noisy preprocessing facilitates a photonic realization of device-independent quantum key distribution. Phys. Rev. Lett. 124, 230502 (2020).
Schwonnek, R. et al. Device-independent quantum key distribution with random key basis. Nat. Commun. 12, 2880 (2021).
Woodhead, E., Acín, A. & Pironio, S. Device-independent quantum key distribution with asymmetric CHSH inequalities. Quantum 5, 443 (2021).
Sekatski, P. et al. Device-independent quantum key distribution from generalized CHSH inequalities. Quantum 5, 444 (2021).
Brown, P., Fawzi, H. & Fawzi, O. Device-independent lower bounds on the conditional von Neumann entropy. Preprint at https://arXiv.org/abs/2106.13692 (2021).
Masini, M., Pironio, S. & Woodhead, E. Simple and practical DIQKD security analysis via BB84-type uncertainty relations and Pauli correlation constraints. Preprint at https://arXiv.org/abs/2107.08894 (2021).
Clauser, J. F., Horne, M. A., Shimony, A. & Holt, R. A. Proposed experiment to test local hidden-variable theories. Phys. Rev. Lett. 23, 880 (1969).
Dupuis, F., Fawzi, O. & Renner, R. Entropy accumulation. Commun. Math. Phys. 379, 867–913 (2020).
Liu, W.-Z. et al. Device-independent randomness expansion against quantum side information. Nat. Phys. 17, 448–452 (2021).
Murta, G., van Dam, S. B., Ribeiro, J., Hanson, R. & Wehner, S. Towards a realization of device-independent quantum key distribution. Quantum Sci. Technol. 4, 035011 (2019).
Tan, E.Y.-Z. et al. Improved DIQKD protocols with finite-size analysis. Preprint at https://arXiv.org/abs/2012.08714 (2020).
Moehring, D. L. et al. Entanglement of single-atom quantum bits at a distance. Nature 449, 68–71 (2007).
Stephenson, L. J. et al. High-rate, high-fidelity entanglement of qubits across an elementary quantum network. Phys. Rev. Lett. 124, 110501 (2020).
Maunz, P. et al. Heralded quantum gate between remote quantum memories. Phys. Rev. Lett. 102, 250502 (2009).
Lettner, M. et al. Remote entanglement between a single atom and a Bose-Einstein condensate. Phys. Rev. Lett. 106, 210503 (2011).
Ritter, S. et al. An elementary quantum network of single atoms in optical cavities. Nature 484, 195–200 (2012).
Hensen, B. et al. Loophole-free Bell inequality violation using electron spins separated by 1.3 kilometres. Nature 526, 682–686 (2015).
Rosenfeld, W. et al. Event-ready Bell test using entangled atoms simultaneously closing detection and locality loopholes. Phys. Rev. Lett. 119, 010402 (2017).
Portmann, C. & Renner, R. Security in quantum cryptography. Preprint at https://arXiv.org/abs/2102.00021 (2021).
Barrett, J., Colbeck, R. & Kent, A. Memory attacks on device-independent quantum cryptography. Phys. Rev. Lett. 110, 010503 (2013).
Pironio, S. et al. Random numbers certified by Bell’s theorem. Nature 464, 1021–1024 (2010).
Pironio, S. et al. Device-independent quantum key distribution secure against collective attacks. New J. Phys. 11, 045021 (2009).
Pirandola, S. et al. Advances in quantum cryptography. Adv. Opt. Photon. 12, 1012–1236 (2020).
Heshami, K. et al. Quantum memories: emerging applications and recent advances. J. Mod. Opt. 63, 2005–2028 (2016).
Wright, T. A. et al. Two-way photonic interface for linking the Sr+ transition at 422 nm to the telecommunication C band. Phys. Rev. Appl. 10, 044012 (2018).
Schupp, J. et al. Interface between trapped-ion qubits and traveling photons with close-to-optimal efficiency. PRX Quantum 2, 020331 (2021).
Sangouard, N., Simon, C., de Riedmatten, H. & Gisin, N. Quantum repeaters based on atomic ensembles and linear optics. Rev. Mod. Phys. 83, 33–80 (2011).
Bourdeauducq, S. et al. m-labs/artiq: 6.0. Zenodo https://doi.org/10.5281/zenodo.6619071 (2021).
Acknowledgements
J.-D.B. and E.Y.-Z.T. thank R. Arnon-Friedman for discussions. We thank Sandia National Laboratories for supplying HOA2 ion traps. This work was supported by the UK Engineering and Physical Sciences Research Council Hub in Quantum Computing and Simulation (EP/T001062/1), the EU Quantum Technology Flagship Project AQTION (No. 820495) and the UKRI Fellowship of C.J.B. (MR/S03238X/1). E.Y.-Z.T. and R.R. acknowledge funding by the Swiss National Science Foundation, through the National Centers for Competence in Research QSIT and SwissMAP, and by the Air Force Office of Scientific Research through grant FA9550-19-1-0202. J.-D.B and N.S. acknowledge funding by the Institut de Physique Théorique, Commissariat á l’Énergie Atomique et aux Energies Alternatives and the Region Île-de-France in the framework of DIM SIRTEQ.
Author information
Authors and Affiliations
Contributions
D.P.N., P.D., B.C.N., G.A., D.M. and R.S. built and operated the experimental apparatus. D.P.N. and P.D. led the collection of the experimental data and performed the data analysis. J.-D.B. and D.P.N. extracted the key from the raw data. K.I., R.L.U. and J.-D.B. designed the error correction code. J.-D.B., E.Y.-Z.T., N.S., P.S. and R.R. established the detailed protocol steps and derived the corresponding security proof. N.S., J.-D.B., D.P.N. and C.J.B. wrote the manuscript. C.J.B. and D.M.L. supervised the experimental work, and J.-D.B. and N.S. supervised the theoretical work. N.S. and J.-D.B. initiated the project. All authors contributed to the discussion and interpretation of results, and contributed to the manuscript.
Corresponding authors
Ethics declarations
Competing interests
C.J.B. is a director of Oxford Ionics. The remaining authors declare no competing interests.
Peer review
Peer review information
Nature thanks Marcos Curty, Lynden Shalm and the other, anonymous, reviewer(s) for their contribution to the peer review of this work. Peer reviewer reports are available.
Additional information
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Supplementary information
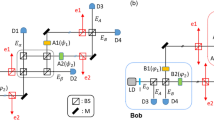
This file contains 11 sections with 16 figures, 5 tables and further references.
Rights and permissions
About this article
Cite this article
Nadlinger, D.P., Drmota, P., Nichol, B.C. et al. Experimental quantum key distribution certified by Bell's theorem. Nature 607, 682–686 (2022). https://doi.org/10.1038/s41586-022-04941-5
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1038/s41586-022-04941-5
This article is cited by
-
NOON-state interference in the frequency domain
Light: Science & Applications (2024)
-
Demonstration of quantum-digital payments
Nature Communications (2023)
-
Quantum networks with neutral atom processing nodes
npj Quantum Information (2023)
-
Recent progress in quantum photonic chips for quantum communication and internet
Light: Science & Applications (2023)
-
Progress in quantum teleportation
Nature Reviews Physics (2023)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.