Abstract
Most qubit-based quantum key distribution (QKD) protocols extract the secure key merely from single-photon component of the attenuated lasers. However, with the Scarani-Acin-Ribordy-Gisin 2004 (SARG04) QKD protocol, the unconditionally secure key can be extracted from the two-photon component by modifying the classical post-processing procedure in the BB84 protocol. Employing the merits of SARG04 QKD protocol and six-state preparation, one can extract secure key from the components of single photon up to four photons. In this paper, we provide the exact relations between the secure key rate and the bit error rate in a six-state SARG04 protocol with single-photon, two-photon, three-photon and four-photon sources. By restricting the mutual information between the phase error and bit error, we obtain a higher secure bit error rate threshold of the multiphoton components than previous works. Besides, we compare the performances of the six-state SARG04 with other prepare-and-measure QKD protocols using decoy states.
Similar content being viewed by others
Introduction
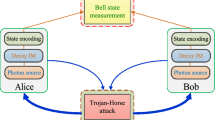
Quantum key distribution (QKD)1,2 offers information-theoretic security for two authorized users, Alice and Bob, when communicating secret information along an insecure quantum channel, while the laws of quantum mechanics bound the behavior of an eavesdropper3,4,5,6. Since its introduction in 1984 by Bennett and Brassard1, QKD has experienced great advances both theoretically7,8,9,10,11,12 and experimentally13,14,15,16,17,18 and has become the most mature quantum information technology for commercial use19. The study of QKD today is driven by the necessity to close the gap between its theory and practice, as experimental systems tend to differ remarkably from their simplified mathematical models and any of these deviations may open doors to new attacks from Eve to compromise security. Some of Eve’s eavesdropping techniques include simple individual attacks and Trojan-horse attacks, which one can overcome by investigating the bounds of information leakage in different scenarios and apply the suitable amount of privacy amplification to obtain the final secure key20. Other side-channel attacks, such as detector blinding attacks21 and time-shift attack22 that base on specific device imperfections, require more complicated QKD settings than the original BB84 to retrieve security again. Hence the measurement-device-independent (MDI) QKD23,24,25,26,27,28,29,30,31,32 and device-independent (DI) QKD33,34,35 were developed to combat these experimental flaws.
Compared with the entanglement-based QKD protocols, prepare-and-measure QKD protocols are widely studied. The photon-number distribution of weak coherent states is Poisson distribution, which contains a fraction of multiphoton components. However, exploiting photon-added coherent states36, one can acquire large probabilities of single-photon, two-photon, three-photon or four-photon component. For the BB84 protocol, the single-photon source is usually replaced by weak coherent states, which suffer from the photon number splitting (PNS) attack37. The PNS attack, in which Eve blocks all single photon pulses and splits multiphoton pulses, results from the experimental variation of replacing the single photon sources from the original BB84 protocol with practical attenuated lasers. In this situation, Eve would forward some portion of multiphoton pulses to Bob through a lossless channel while keeping the rest to herself in the quantum memory38,39,40 and measure her photons after receiving the basis reconciliation information obtained via Alice and Bob’s public communication. The security basis of QKD provided by single photon pulses was guaranteed by the no-cloning theorem41 and thus this attack was regarded as a major threat to QKD and has been extensively studied37. Two major counter methods have been proposed. One is the decoy state method42,43,44, which is a powerful method devised to analyze rigorously the extractible secret key rate from the single-photon component of signal states, though its implementations would differ slightly from the prepare-and-measure setup45,46,47. To overcome this attack at a protocol level, the SARG04 QKD protocol48, which differs from the BB84 only in the classical post-processing part49,50, was proposed. In the SARG04 protocol, the reconciliation information is a pair of nonorthogonal states, which cannot be perfectly distinguished and can be able to address the PNS attack48. Subsequently, this prepare-and-measure SARG04 protocol was further investigated and ingeniously converted to an unconditionally secure entanglement distillation protocol (EDP) by Tamaki and Lo51, who showed that by exploiting the same arguments of Shor and Preskill4, SARG04 protocol possesses the unique ability to extract the secure key from not only the single-photon component but also two-photon component51,52. This opens the interesting question that under certain modifications of the original BB84 protocol, how the secret key can be extracted from multiphoton states. The SARG04 protocol has been widely investigated in theories49,50,51,52,53,54,55,56 and experiments57,58. Similarly to the MDIQKD protocol, which was proposed to make BB84 protocol naturally immune to all side-channel attacks on detectors, the SARG04 protocol in MDI setting has been considered likewise59. Also, with the advantage of secure key generation from two-photon component, recently a nonorthogonal state encoding method of SARG04 has been successfully applied to circumvent the forging attack of quantum digital signature with insecure quantum channel60. A generalized SARG04 with six states (six-state SARG04) protocol has been analyzed in ref. 51, which showed that one could extract the secure key from the single-photon component to up to four-photon component. However, without the explicit relations between the phase error rate and bit error rate of the six-state SARG04 protocol51, one cannot acquire the exact secure key rate.
Here, we generalize the EDP of ref. 51 to acquire the exact relationships between the phase error rate and bit error rate of single-photon, two-photon, three-photon and four-photon components in the six-state SARG04 protocol. Furthermore, we carefully analyze the mutual information between phase error and bit error and discover that the mutual information of two-photon component in a four-state SARG04 protocol and that of three-photon and four-photon components in a six-state SARG04 protocol are not zero, so the secure bit error rate threshold of those cases are higher than the results of previous works51. Finally, we perform a numerical simulation to study the performance of six-state SARG04 with weak coherent states in an infinite decoy states setting. Also, we compare the performance of six-state SARG04 and other prepare-and-measure QKD protocols, i.e., BB841,43, four-state SARG0448,52 and round-robin differential phase-shift (RRDPS) QKD protocols61,62,63 in the same situation.
Results
Six-state SARG04 QKD protocol
In this section, we introduce the six-state SARG04 QKD protocol with ν-photon (ν ∈ {1, 2, 3, 4}) source. In this protocol, there are six polarization encoding quantum states, |H〉, |V〉,  ,
,  and
and  . The six states are then arranged into twelve sets {|H〉, |−〉}, {|−〉, |V〉}, {|V〉, |+〉}, {|+〉, |H〉}, {|H〉, |R〉}, {|R〉, |V〉}, {|V〉, |L〉}, {|L〉, |H〉}, {|R〉, |−〉}, {|−〉, |L〉}, {|L〉, |+〉}, {|+〉, |R〉}, where the first and second states of each set correspond to logic 0 and 1, respectively. The steps of the six-state SARG04 QKD protocol with a ν-photon source are outlined as follows. Alice sends a series of signals to Bob. Each pulse is chosen randomly from the twelve sets listed above and Alice randomly sends one state from each set to Bob through the insecure quantum channel. Bob randomly measures the incoming bit strings with one of the three bases, Z, X and Y. Afterwards, he exploits an authenticated classical channel to announce to Alice the situations where he did not register any click at his detection unit and both of them discard these signals. Alice reveals to Bob the sets on which she encodes her information. Bob then compares his measurement results with Alice’s set information. If Bob’s measurement result is orthogonal to one of the states in the set, he concludes that the other state has been sent, which represents a conclusive result; he concludes an inconclusive result otherwise. He discards all the inconclusive results and broadcasts to Alice which of his results are conclusive. Alice selects randomly a portion of her remaining signals and announces them to Bob and Bob calculates the bit error rate to test for eavesdroppers. If the bit error rate is much higher than the upper bound, they abort the protocol. They perform error correction and privacy amplification on the remaining bit string to obtain the shared secret key.
. The six states are then arranged into twelve sets {|H〉, |−〉}, {|−〉, |V〉}, {|V〉, |+〉}, {|+〉, |H〉}, {|H〉, |R〉}, {|R〉, |V〉}, {|V〉, |L〉}, {|L〉, |H〉}, {|R〉, |−〉}, {|−〉, |L〉}, {|L〉, |+〉}, {|+〉, |R〉}, where the first and second states of each set correspond to logic 0 and 1, respectively. The steps of the six-state SARG04 QKD protocol with a ν-photon source are outlined as follows. Alice sends a series of signals to Bob. Each pulse is chosen randomly from the twelve sets listed above and Alice randomly sends one state from each set to Bob through the insecure quantum channel. Bob randomly measures the incoming bit strings with one of the three bases, Z, X and Y. Afterwards, he exploits an authenticated classical channel to announce to Alice the situations where he did not register any click at his detection unit and both of them discard these signals. Alice reveals to Bob the sets on which she encodes her information. Bob then compares his measurement results with Alice’s set information. If Bob’s measurement result is orthogonal to one of the states in the set, he concludes that the other state has been sent, which represents a conclusive result; he concludes an inconclusive result otherwise. He discards all the inconclusive results and broadcasts to Alice which of his results are conclusive. Alice selects randomly a portion of her remaining signals and announces them to Bob and Bob calculates the bit error rate to test for eavesdroppers. If the bit error rate is much higher than the upper bound, they abort the protocol. They perform error correction and privacy amplification on the remaining bit string to obtain the shared secret key.
A virtual EDP-based six-state SARG04 protocol
To estimate phase error for privacy amplification, one can construct an equivalent EDP version of the six-state SARG04 protocol. First, we introduce some notations. {|0x〉, |1x〉} and {|0z〉, |1z〉} are the eigenstates for X and Z basis, respectively.  ; T0 = I is an identity operation;
; T0 = I is an identity operation;  is a π/2 rotation around the
is a π/2 rotation around the  axis;
axis;  is a
is a  rotation around the
rotation around the  axis. In the EDP-ν protocol, Alice prepares many pairs of qubits in the state
axis. In the EDP-ν protocol, Alice prepares many pairs of qubits in the state  , where
, where  (j ∈ {0, 1}). She then randomly rotates TlRk and sends system B to Bob, where l ∈ {0, 1, 2} and k ∈ {0, 1, 2, 3}. Upon receiving the qubits, Bob first applies a random reverse rotation
(j ∈ {0, 1}). She then randomly rotates TlRk and sends system B to Bob, where l ∈ {0, 1, 2} and k ∈ {0, 1, 2, 3}. Upon receiving the qubits, Bob first applies a random reverse rotation  , before performing a filtering operation defined by a Klaus operator
, before performing a filtering operation defined by a Klaus operator  . Then Alice and Bob would compare their indices k, l and k′, l′ via public communication and keep the qubit pairs with k = k′ and l = l′ when Bob’s filtering operation is successful. They then choose some states randomly as test bits and measure them in the Z basis and compare their results publicly to estimate the bit error rate and the information acquired by Eve. Finally, they utilize the corresponding Calderbank-Shor-Steane (CSS) code to correct the bit and phase errors4 and perform a final Z measurement on their qubits to obtain the secure key.
. Then Alice and Bob would compare their indices k, l and k′, l′ via public communication and keep the qubit pairs with k = k′ and l = l′ when Bob’s filtering operation is successful. They then choose some states randomly as test bits and measure them in the Z basis and compare their results publicly to estimate the bit error rate and the information acquired by Eve. Finally, they utilize the corresponding Calderbank-Shor-Steane (CSS) code to correct the bit and phase errors4 and perform a final Z measurement on their qubits to obtain the secure key.
The six-state SARG04 QKD protocol is equivalent to the EDP-based six-state SARG04 QKD protocol, except for the only difference, a π/4 total rotation around Y basis. By analyzing the virtual EDP-based six-state SARG04 QKD protocol, we give the exact phase error rate formula, whose detailed analysis is provided in the Methods section. For the case with a single-photon source, we have

where ep and eb are the phase error rate and bit error rate, respectively. a is the probability that both bit flip and phase shift occur, which restricts the mutual information between phase error and bit error. For the case of a two-photon source, the relationship can be given by

For the case with a three-photon source, the error rates can be written as

For the case with a four-photon source, the error rates are calculated by

where

Now we reexamine the four-state SARG04 QKD protocol51,52 and we find that the mutual information between bit error and phase error of a two-photon source is not zero. The expression can be given by

where

from which we can see that this phase error rate formula is the same as the result in ref. 51.
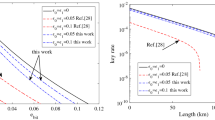
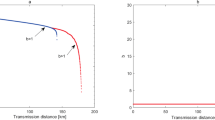
The secure key rate of the EDP-based QKD using one-way classical communication can be given by52

where H(x) = −x log2(x) − (1 − x) log2 (1 − x) is the binary Shannon entropy, H(ep|eb) is the conditional Shannon entropy function shown in the Methods section. We calculate the secure key rates versus the bit error rates for the six-state SARG04 QKD protocol with single-photon, two-photon, three-photon and four-photon sources, as shown in Fig. 1. For comparison, we also calculate the secure key rate versus bit error rate for BB84 protocol4, six-state protocol64 and four-state SARG04 QKD protocol51. For the six-state SARG04 QKD protocol, one can extract the secure key rate from ν-photon component when the bit error rate is no larger than 11.235% (with ν = 1), 5.602% (with ν = 2), 2.438% (with ν = 3) and 0.802% (with ν = 4). For the four-state SARG04 QKD protocol with our calculation, one can extract the secure key rate from two-photon component when the bit error rate is lower than 2.726%. We can see that the bit error rate thresholds of single-photon and two-photon in the six-state SARG04 QKD protocol are the same with the results in ref. 51, while the bit error rate thresholds of three-photon and four-photon in the six-state SARG04 QKD protocol and two-photon in the four-state SARG04 QKD protocol are larger than the results in ref. 51. If we neglect the mutual information between phase error and bit error, the bit error rate thresholds of three-photon (2.370%) and four-photon (0.788%) in the six-state SARG04 QKD protocol and two-photon (2.710%) in the four-state SARG04 QKD protocol are the same with the results in ref. 51.
For the phase randomized weak coherent state sources65, we study the secure key rate with infinite decoy states42,43,44, which can be given by

where Qn is the gain of the n-photon signal states which can be estimated by the decoy-state method; 
 is the phase (bit) error for the n-photon state; Qμ and Eμ are, respectively, the total gain and quantum bit error rate under signal states with μ intensity and can both be acquired directly through the experiment. We execute a numerical simulation to study its performance, as shown in Fig. 2. In our simulation, we use the following parameters: the detection efficiency is ηd = 43%, the dark count rate of each pulse is pdark = 1 × 10−7 and the intrinsic loss coefficient of standard telecom fibre is α = 0.2 dB/km. These values are adopted from the 200 km MDIQKD experiment data16. We also set the misalignment error rate to ed = 0.5%, the efficiency of error correction is f = 1.16. For comparison, we also give the secure key rates of BB84 QKD protocol43, four-state SARG04 QKD protocol52 and the RRDPS QKD protocol61 with the case of infinite decoy states. As shown in Fig. 2(a), the secure transmission distance of the six-state SARG04 QKD protocol is more than 270 km, farther than the four-state SARG04 QKD protocol because of the higher bit error rate threshold in the six-state SARG04 QKD protocol. The case of finite decoy states is considered in the Fig. 2(b). By exploiting one weak decoy state and vacuum state, one can extract the secure key from single-photon component (see Methods). However, the secure key rate and secure transmission distance of the six-state and four-state SARG04 QKD protocol are all smaller than those of BB84 protocol since the bit error rate of BB84 protocol is small and the efficiency of basis shift is high52. Meanwhile, since the security of RRDPS QKD does not rely on signal disturbance monitoring, in our case where ed is low, the secure key of RRDPS QKD is much lower than qubit-based QKD protocols.
is the phase (bit) error for the n-photon state; Qμ and Eμ are, respectively, the total gain and quantum bit error rate under signal states with μ intensity and can both be acquired directly through the experiment. We execute a numerical simulation to study its performance, as shown in Fig. 2. In our simulation, we use the following parameters: the detection efficiency is ηd = 43%, the dark count rate of each pulse is pdark = 1 × 10−7 and the intrinsic loss coefficient of standard telecom fibre is α = 0.2 dB/km. These values are adopted from the 200 km MDIQKD experiment data16. We also set the misalignment error rate to ed = 0.5%, the efficiency of error correction is f = 1.16. For comparison, we also give the secure key rates of BB84 QKD protocol43, four-state SARG04 QKD protocol52 and the RRDPS QKD protocol61 with the case of infinite decoy states. As shown in Fig. 2(a), the secure transmission distance of the six-state SARG04 QKD protocol is more than 270 km, farther than the four-state SARG04 QKD protocol because of the higher bit error rate threshold in the six-state SARG04 QKD protocol. The case of finite decoy states is considered in the Fig. 2(b). By exploiting one weak decoy state and vacuum state, one can extract the secure key from single-photon component (see Methods). However, the secure key rate and secure transmission distance of the six-state and four-state SARG04 QKD protocol are all smaller than those of BB84 protocol since the bit error rate of BB84 protocol is small and the efficiency of basis shift is high52. Meanwhile, since the security of RRDPS QKD does not rely on signal disturbance monitoring, in our case where ed is low, the secure key of RRDPS QKD is much lower than qubit-based QKD protocols.
(a) Plot of secure key rate versus fibre channel transmission for various QKD protocols with infinite decoy states. For each transmission loss, we optimize the intensity of signal states. For comparison, we set the number of pulses of each block L = 10, since the phase error rate is n/(L − 1) for n-photon in the RRDPS QKD protocol61. It means that we can extract the secure key from single-photon, two-photon, three-photon and four-photon components for RRDPS QKD protocol. (b) Plot of secure key rate versus fibre channel transmission for various QKD protocols with one weak decoy state and vacuum state.
Discussion
For each QKD protocol, how to extract as much secure key as possible is a critical task. Here, we present the exact relations between the phase error and bit error as well as the mutual information parameters with single-photon, two-photon, three-photon and four-photon sources. Through restricting the mutual information, we have obtained higher bit error rate thresholds of three-photon, four-photon six-state SARG04 and two-photon four-state SARG04 QKD protocol. In the quantum digital signature protocol with k + 1-participant60,66 (one signer and k recipients), the signer will prepares k copies of quantum states and send a copy of quantum states to each recipient through the insecure quantum channel. To guarantee the security against the forgery attack of untruthful recipient, the honest recipient needs to estimate the information leak of his received quantum states, which will correlate to the phase error rate of QKD with k-photon sources. The security analysis of the four-state and six-state SARG04 QKD protocol with two-photon sources has been used for the three-participants quantum digital signature60. Similarly, we can expect that the security analysis of the six-state SARG04 QKD protocol with three and four-photon sources can also be used for the four-participant and five-participant quantum digital signature.
Methods
The six-state SARG04 protocol with single-photon source
We consider the following four orthogonal Bell states

Alice prepares the initial quantum state  . If Eve performs no attacks and Bob does a successful filtering operation, the quantum state shared by Alice and Bob can be given by
. If Eve performs no attacks and Bob does a successful filtering operation, the quantum state shared by Alice and Bob can be given by

Here, we consider that Eve can perform the most general attack on all qubits transmitted through the insecure quantum channel. By tracing out all other qubits, we can focus on one qubit state. Let ρqubit represent a pair of qubit states that Alice and Bob share after Eve’s attack, which can be given by

where l ∈ {0, 1, 2}, k ∈ {0, 1, 2, 3}, and

Here, EB is a 2 × 2 matrix representing Eve’s operations on the single-photon qubit. Meanwhile, any quantum state in the form of a bipartite density matrix can be expressed by the Bell-basis diagonal states. From Eq. (25), we can see that the Bell state |Φ+〉 is a reference state. Thus, we have

representing the probabilities of only bit flip, only phase shift, both bit flip and phase shift, respectively. Therefore, the probabilities of bit flip and phase shift can be given by

Let pfil = Tr[ρqubit] represent the trace value of state ρqubit. One can clearly see that  ,
,  ,
,  and
and  , where Afil, Abit, Aph and AY are all 4 × 4 diagonal matrices and
, where Afil, Abit, Aph and AY are all 4 × 4 diagonal matrices and  is a 1 × 4 vector. If xAbit + yAfil − Aph ≥ 0 is a positive semi-definite matrix, xpbit + ypfil ≥ pph will always be satisfied. If pph ≤ xpbit + ypfil holds, then ep ≤ xeb + y becomes exponentially reliable as the number of successfully filtered states increases51. By using the same argument, if
is a 1 × 4 vector. If xAbit + yAfil − Aph ≥ 0 is a positive semi-definite matrix, xpbit + ypfil ≥ pph will always be satisfied. If pph ≤ xpbit + ypfil holds, then ep ≤ xeb + y becomes exponentially reliable as the number of successfully filtered states increases51. By using the same argument, if  holds, then xeb ≤ a ≤ yeb. The conditional Shannon entropy function can be given by
holds, then xeb ≤ a ≤ yeb. The conditional Shannon entropy function can be given by

The six-state SARG04 protocol with multiphoton sources
In the case of two-photon, for each quantum state prepared by Alice, the density matrix of quantum state shared by Alice and Bob after Eve’s attack can be given by

where l ∈ {0, 1, 2}, k ∈ {0, 1, 2, 3}, u ∈ {0, 1} and

EB is a 4 × 4 matrix which depends on Eve’s operation on the two-photon qubit and we can safely assume that the final state of Eve’s system is a particular state |0x〉. Afil, Abit, Aph and  are 8 × 8 diagonal matrices,
are 8 × 8 diagonal matrices,  is a 1 × 8 vector.
is a 1 × 8 vector.
In the case of three-photon, for each quantum state prepared by Alice, the density matrix of quantum state shared by Alice and Bob after Eve’s attack can be given by

where l ∈ {0, 1, 2}, k ∈ {0, 1, 2, 3}, u ∈ {0, 1}, v ∈ {0, 1} and

EB is a 8 × 8 matrix which depends on Eve’s operation on the three-photon qubit. Afil, Abit, Aph and AY are 16 × 16 diagonal matrices,  is a 1 × 16 vector.
is a 1 × 16 vector.
In the case of four-photon, for each quantum state prepared by Alice, the density matrix of quantum state shared by Alice and Bob after Eve’s attack can be given by

where l ∈ {0, 1, 2}, k ∈ {0, 1, 2, 3}, u ∈ {0, 1}, v ∈ {0, 1}, s ∈ {0, 1} and

Since the photons of Eve’s system are identical, considering their symmetry, we have

EB is a 16 × 16 matrix which depends on Eve’s operation on the four-photon qubit. Afil, Abit, Aph and AY are 16 × 16 diagonal matrices,  is a 1 × 16 vector.
is a 1 × 16 vector.
Decoy state method with weak coherent state sources
By using decoy state method42,43,44, one can have

where Yn is the yield of n-photon. In this simulation, we use the case where Eve does not interfere with the protocol. For the BB84 protocol, the Yn and  can be given by43
can be given by43

where  ,
,  is the channel transmittance and D is the distance of optical fibre. For the RRDPS protocol, the Yn and
is the channel transmittance and D is the distance of optical fibre. For the RRDPS protocol, the Yn and  can be given by61,62,63
can be given by61,62,63

where L is the number of pulses of each block. For the four-state SARG04 protocol, the Yn and  can be given by52
can be given by52

For the six-state SARG04 protocol, the Yn and  can be given by60
can be given by60

For the case with infinite decoy states, one can use the Eqs (25, 26, 27, 28) to directly calculate the yield and bit error rate of  -photon component43,44. For the case with finite decoy states, we must estimate the lower bound of yield
-photon component43,44. For the case with finite decoy states, we must estimate the lower bound of yield  and the upper bound of bit error rate
and the upper bound of bit error rate  . One can exploit three intensities μ > ν > 0 to estimate
. One can exploit three intensities μ > ν > 0 to estimate  and
and  ,
,

One can also exploit four intensities60 μ > ν > ω > 0 to estimate  and
and  ,
,


For more photon components, the analytical method will become very complex to calculate the yield and bit error rate. However, the linear programming25 is a good method. To estimate the yield and bit error rate of n-photon, one can use n + 2 kinds of intensities. Since the probability of multiphoton components is very small in the weak coherent state sources, we simply consider the single-photon component contribution using one signal state, one weak decoy state and vacuum state. The intensity of weak decoy state is 0.1 and the intensity of signal state is optimal for each distance.
Additional Information
How to cite this article: Yin, H.-L. et al. Security of quantum key distribution with multiphoton components. Sci. Rep. 6, 29482; doi: 10.1038/srep29482 (2016).
References
Bennett, C. H. & Brassard, G. Quantum cryptography: Public key distribution and coin tossing. In Proceedings of IEEE International Conference on Computers, Systems and Signal Processing, 175–179 (IEEE, New York, 1984).
Ekert, A. K. Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67, 661–663 (1991).
Lo, H.-K. & Chau, H. F. Unconditional security of quantum key distribution over arbitrarily long distances. Science 283, 2050–2056 (1999).
Shor, P. W. & Preskill, J. Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85, 441 (2000).
Kraus, B., Gisin, N. & Renner, R. Lower and upper bounds on the secret-key rate for quantum key distribution protocols using one-way classical communication. Phys. Rev. Lett. 95, 080501 (2005).
Tomamichel, M. & Renner, R. Uncertainty relation for smooth entropies. Phys. Rev. Lett. 106, 110506 (2011).
Gisin, N., Ribordy, G., Tittel, W. & Zbinden, H. Quantum cryptography. Rev. Mod. Phys. 74, 145–195 (2002).
Wang, X.-B., Hiroshima, T., Tomita, A. & Hayashi, M. Quantum information with Gaussian states. Phys. Rep. 448, 1–111 (2007).
Scarani, V. et al. The security of practical quantum key distribution. Rev. Mod. Phys. 81, 1301–1350 (2009).
Weedbrook, C. et al. Gaussian quantum information. Rev. Mod. Phys. 84, 621–669 (2012).
Lo, H.-K., Curty, M. & Tamaki, K. Secure quantum key distribution. Nature Photon. 8, 595–604 (2014).
Ekert, A. & Renner, R. The ultimate physical limits of privacy. Nature 507, 443–447 (2014).
Takesue, H. et al. Quantum key distribution over a 40-db channel loss using superconduct- ing single-photon detectors. Nature Photon. 1, 343–348 (2007).
Wang, S. et al. 2 GHz clock quantum key distribution over 260 km of standard telecom fiber. Opt. Lett. 37, 1008–1010 (2012).
Liu, Y. et al. Experimental measurement-device-independent quantum key distribution. Phys. Rev. Lett. 111, 130502 (2013).
Tang, Y.-L. et al. Measurement-device-independent quantum key distribution over 200 km. Phys. Rev. Lett. 113, 190501 (2014).
Korzh, B. et al. Provably secure and practical quantum key distribution over 307 km of optical fibre. Nature Photon. 9, 163–168 (2015).
Tang, Y.-L. et al. Measurement-device-independent quantum key distribution over untrust- ful metropolitan network. Phys. Rev. X 6, 011024 (2016).
Fröhlich, B. et al. A quantum access network. Nature 501, 69–72 (2013).
Lucamarini, M. et al. Practical security bounds against the trojan-horse attack in quantum key distribution. Phys. Rev. X 5, 031030 (2015).
Lydersen, L. et al. Hacking commercial quantum cryptography systems by tailored bright illumination. Nature Photon. 4, 686–689 (2010).
Zhao, Y., Fung, C.-H. F., Qi, B., Chen, C. & Lo, H.-K. Quantum hacking: Experimen- tal demonstration of time-shift attack against practical quantum-key-distribution systems. Phys. Rev. A 78, 042333 (2008).
Lo, H.-K., Curty, M. & Qi, B. Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2012).
Braunstein, S. L. & Pirandola, S. Side-channel-free quantum key distribution. Phys. Rev. Lett. 108, 130502 (2012).
Ma, X., Fung, C.-H. F. & Razavi, M. Statistical fluctuation analysis for measurement- device-independent quantum key distribution. Phys. Rev. A 86, 052305 (2012).
Yin, H.-L. et al. Long-distance measurement-device-independent quantum key distribution with coherent-state superpositions. Opt. Lett. 39, 5451–5454 (2014).
Curty, M. et al. Finite-key analysis for measurement-device-independent quantum key distribution. Nature Commun. 5, 3732 (2014).
Wang, Q. & Wang, X.-B. Simulating of the measurement-device independent quantum key distribution with phase randomized general sources. Sci. Rep. 4, 4612 (2014).
Yin, H.-L. et al. Measurement-device-independent quantum key distribution based on Bel- l’s inequality. arXiv:1407.7375.
Zhou, Y.-H., Yu, Z.-W. & Wang, X.-B. Making the decoy-state measurement-device- independent quantum key distribution practically useful. Phys. Rev. A 93, 042324 (2016).
Xu, F. Measurement-device-independent quantum communication with an untrusted source. Phys. Rev. A 92, 012333 (2015).
Fu, Y., Yin, H.-L., Chen, T.-Y. & Chen, Z.-B. Long-distance measurement-device- independent multiparty quantum communication. Phys. Rev. Lett. 114, 090501 (2015).
Aćın, A. et al. Device-independent security of quantum cryptography against collective attacks. Phys. Rev. Lett. 98, 230501 (2007).
Gisin, N., Pironio, S. & Sangouard, N. Proposal for implementing device-independent quantum key distribution based on a heralded qubit amplifier. Phys. Rev. Lett. 105, 070501 (2010).
Vazirani, U. & Vidick, T. Fully device-independent quantum key distribution. Phys. Rev. Lett. 113, 140501 (2014).
Agarwal, G. S. & Tara, K. Nonclassical properties of states generated by the excitations on a coherent state. Phys. Rev. A 43, 492–497 (1991).
Brassard, G., Lütkenhaus, N., Mor, T. & Sanders, B. C. Limitations on practical quantum cryptography. Phys. Rev. Lett. 85, 1330–1333 (2000).
Azuma, K., Tamaki, K. & Munro, W. J. All-photonic intercity quantum key distribution. Nature Commun. 6, 10171 (2015).
Abruzzo, S., Kampermann, H. & Bruß, D. Measurement-device-independent quantum key distribution with quantum memories. Phy. Rev. A 89, 012301 (2014).
Mirza, I. M., van Enk, S. & Kimble, H. Single-photon time-dependent spectra in coupled cavity arrays. J. Opt. Soc. Am. B 30, 2640–2649 (2013).
Wootters, W. K. & Zurek, W. H. A single quantum cannot be cloned. Nature 299, 802–803 (1982).
Hwang, W.-Y. Quantum key distribution with high loss: Toward global secure communi- cation. Phys. Rev. Lett. 91, 057901 (2003).
Lo, H.-K., Ma, X. & Chen, K. Decoy state quantum key distribution. Phys. Rev. Lett. 94, 230504 (2005).
Wang, X.-B. Beating the photon-number-splitting attack in practical quantum cryptogra- phy. Phys. Rev. Lett. 94, 230503 (2005).
Peng, C.-Z. et al. Experimental long-distance decoy-state quantum key distribution based on polarization encoding. Phys. Rev. Lett. 98, 010505 (2007).
Rosenberg, D. et al. Long-distance decoy-state quantum key distribution in optical fiber. Phys. Rev. Lett. 98, 010503 (2007).
Schmitt-Manderbach, T. et al. Experimental demonstration of free-space decoy-state quan- tum key distribution over 144 km. Phys. Rev. Lett. 98, 010504 (2007).
Scarani, V., Aćın, A., Ribordy, G. & Gisin, N. Quantum cryptography protocols robust against photon number splitting attacks for weak laser pulse implementations. Phys. Rev. Lett. 92, 057901 (2004).
Aćın, A., Gisin, N. & Scarani, V. Coherent-pulse implementations of quantum cryptogra- phy protocols resistant to photon-number-splitting attacks. Phys. Rev. A 69, 012309 (2004).
Branciard, C., Gisin, N., Kraus, B. & Scarani, V. Security of two quantum cryptography protocols using the same four qubit states. Phys. Rev. A 72, 032301 (2005).
Tamaki, K. & Lo, H.-K. Unconditionally secure key distillation from multiphotons. Phys. Rev. A 73, 010302 (2006).
Fung, C.-H. F., Tamaki, K. & Lo, H.-K. Performance of two quantum-key-distribution protocols. Phys. Rev. A 73, 012337 (2006).
Koashi, M. Security of quantum key distribution with discrete rotational symmetry. arXiv quant-ph/0507154.
Xu, F.-X., Wang, S., Han, Z.-F. & Guo, G.-C. Passive decoy state SARG04 quantum-key- distribution with practical photon-number resolving detectors. Chin. Phys. B 19, 100312 (2010).
Ali, S. & Wahiddin, M. Fiber and free-space practical decoy state qkd for both BB84 and SARG04 protocols. Eur. Phys. J. D 60, 405–410 (2010).
Ali, S., Mohammed, S., Chowdhury, M. & Hasan, A. A. Practical SARG04 quantum key distribution. Opt. Quant. Electron. 44, 471–482 (2012).
Stucki, D. et al. Long-term performance of the swissquantum quantum key distribution network in a field environment. New J. Phys. 13, 123001 (2011).
Jeong, Y.-C., Kim, Y.-S. & Kim, Y.-H. Effects of depolarizing quantum channels on BB84 and SARG04 quantum cryptography protocols. Laser Phys. 21, 1438–1442 (2011).
Mizutani, A., Tamaki, K., Ikuta, R., Yamamoto, T. & Imoto, N. Measurement-device- independent quantum key distribution for scarani-acin-ribordy-gisin 04 protocol. Sci. Rep. 4, 5236 (2014).
Yin, H.-L., Fu, Y. & Chen, Z.-B. Practical quantum digital signature. Phys. Rev. A 93, 032316 (2016).
Sasaki, T., Yamamoto, Y. & Koashi, M. Practical quantum key distribution protocol without monitoring signal disturbance. Nature 509, 475–478 (2014).
Zhang, Z., Yuan, X., Cao, Z. & Ma, X. Round-robin differential-phase-shift quantum key distribution. arXiv:1505.02481.
Yin, H.-L., Fu, Y., Mao, Y. & Chen, Z.-B. Detector-decoy quantum key distribution without monitoring signal disturbance. Phys. Rev. A 93, 022330 (2016).
Lo, H.-K. Proof of unconditional security of six-state quantum key distribution scheme. Quantum Inf. Comput. 1, 81–94 (2001).
Tang, Y.-L. et al. Source attack of decoy-state quantum key distribution using phase infor- mation. Phys. Rev. A 88, 022308 (2013).
Gottesman, D. & Chuang, I. Quantum digital signatures. arXiv quant-ph/0105032.
Acknowledgements
This work has been supported by the Chinese Academy of Sciences and the National Natural Science Foundation of China under Grant No. 61125502.
Author information
Authors and Affiliations
Contributions
H.-L.Y., Y.F. and Z.-B.C. have the main idea. All results are acquired through the discussion among all authors. All authors contribute to the writing and reviewing of the manuscript.
Ethics declarations
Competing interests
The authors declare no competing financial interests.
Rights and permissions
This work is licensed under a Creative Commons Attribution 4.0 International License. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in the credit line; if the material is not included under the Creative Commons license, users will need to obtain permission from the license holder to reproduce the material. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/
About this article
Cite this article
Yin, HL., Fu, Y., Mao, Y. et al. Security of quantum key distribution with multiphoton components. Sci Rep 6, 29482 (2016). https://doi.org/10.1038/srep29482
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/srep29482
This article is cited by
-
Measurement-Device-Independent Twin-Field Quantum Key Distribution
Scientific Reports (2019)
-
Plug-and-play round-robin differential phase-shift quantum key distribution
Scientific Reports (2017)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.