Abstract
In this study, a simplified version of the entanglement-swapping protocol, commonly used in the deployment of quantum networks, is presented. Quantum repeaters are essential in extending the range of quantum networks, especially when they are implemented through the laying of optical fiber. The simplified version of the entanglement-swapping protocol does not require the use of unitary transforms to finish characterizing the shared Bell state at both ends to be connected, as happens in the traditional version of the protocol, facilitating and reducing costs in quantum repeater implementations. Both a theoretical demonstration and an experimental one on an optical table, based on two revealing experiments, show the excellent performance of the presented protocol.
Similar content being viewed by others
Introduction
Entanglement1,2,3 constitutes one of the two scenarios where special relativity4 and quantum mechanics5 confront each other in a fierce fight, these being two of the main pillars of physics. This is the reason why, even today, the intrinsic springs of what, without a doubt, constitutes the most interesting and useful phenomenon in physics, i.e., entanglement, are unknown in all its magnitude. However, even with incomplete knowledge of it, the twenty-first century has become the moment of the birth of the so-called quantum information science6, of which quantum computation7,8,9,10,11, and quantum communications12,13,14,15 represent the most promising verticals, both having entanglement as an essential tool for their development. The advances produced in this area intrinsically imply small and important steps, due to the need to avoid a certain number of obstacles grouped in a family of no-go theorems6, of which the most conspicuous is without a doubt the no-cloning theorem16.
Of all the quantum communications protocols developed to date, quantum teleportation and super-dense coding17 are the first and most important. Countless efforts have been made during the last two decades to extend the applicability of these protocols to:
All these efforts aim to improve the performance of transmission protocols for their application in the future network of networks, i.e., the quantum Internet32,33,34,35,36,37,38,39,40,41.
In the case of this last option, a recurring concern, that arises in people who are not dedicated to technological aspects, is summarized in the following question: if the quantum internet will be implemented exclusively optically, then, what is the main difference with the optical implementations of the current Internet that justify such an investment in a new infrastructure? The answer is very simple, the security that the quantum version of the internet will offer using the laws of quantum mechanics5 to preserve the integrity and privacy of the information. This attribute is what will make the difference between both versions of the Internet, given that quantum cryptography protocols42,43 are the only ones that will be prepared to resist future attacks by quantum computers6,7,8,9,10,11, which use, for example, the famous Shor’s algorithm44, which allows factoring an integer, the basis of the cryptographic algorithm of Rivest, Shamir, and Adleman (RSA)45, in polynomial time.
Among the families of quantum cryptography algorithms with the best performance, we can highlight the following technologies:
-
(a)
quantum key distribution (QKD)46,47,48,49, with and without entangled photons, where both ends of the quantum channel share a key to encrypt and decrypt the Information that is transmitted by the classical channel,
-
(b)
quantum secure direct communications (QSDC)50,51,52,53,54,55,56,57,58,59,60,61,62,63,64, with and without entangled photons, which does not use a key to encrypt/decrypt the shared information, with all that this means from the point of view of security in quantum cryptography42,43, positioning itself as the family of protocols with the most future in quantum communications12,13,14,15, in general, and the future quantum internet32,33,34,35,36,37,38,39,40,41, in particular,
-
(c)
quantum secret sharing (QSS)65, which uses entangled photon configurations of the Greenberger–Horne–Zeilinger (GHZ) type1,2,3,6,7,8, and does not use keys to encode the information; and
-
(d)
quantum key secure communication (QKSC)19, which also uses entangled photon configurations of the GHZ type, also does not use keys and is fundamentally based on a version of the super-dense coding protocol extended to N qubits, where N is an arbitrary number.
Depending on the quantum cryptography protocol and whether it works with continuous variables, the pre-existing infrastructure of the current internet can be reused in its new quantum version.
Another aspect as important as security is the range of the future quantum internet, which must be extended using quantum repeaters, both in fiber optic runs66 and in free-space implementations employing CubeSats in the so-called low-earth-orbits (LEO)67,68.
Quantum repeaters are based on the entanglement-swapping protocol69,70,71,72,73,74,75, which has a series of drawbacks for its efficient implementation. These drawbacks are fundamentally represented using multiple classical channels, which distribute classical disambiguation bits that activate or deactivate unitary transforms at both ends to be connected by the quantum repeater. Synchronization problems in the activation of both unitary transforms, located at both ends to be connected, must be compensated with intensive use of quantum memories76. This becomes even more complicated as more and more quantum repeaters are incorporated to appropriately extend the link range. Therefore, any simplification in the implementation of the entanglement-swapping protocol, such as the one presented in the present study, will be very welcome.
This paper comprises various sections as follows. The next section explains the theoretical foundations of the simplified entanglement swapping protocol and its most notable differences from the original protocol. The “Bell state change test” section is dedicated to explaining the theory of the first experiment that will verify the correct functioning of the new protocol, while in the “Bell test from two independent sources of entangled photons” section, we do the same with the second prepared experiment. In the section “Optical table”, we will implement both tests on the optical table. In the “Discussions about the outcomes” section, we discuss the results of the proposed protocols by showing the fidelity of the circuits. Finally, we end our paper with a brief conclusion in the last section.
Simplified entanglement swapping
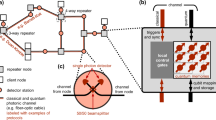
Entanglement swapping protocol69,70,71,72,73,74,75 is represented in Fig. 1, which shows two independent EPR (Einstein–Podolsky–Rosen)6 sources of entanglement photons, one quantum repeater66, and the resulting density matrix between the extreme qubits q[0] and q[3]. The first EPR source is allocated between the qubits q[0] and q[1], while the second one is between the qubits q[2] and q[3]. At the output of each crystal used to generate the entangled photons, the Bell6 state obtained is of the following type:
where \(\left| H \right\rangle = \left| 0 \right\rangle = \left[ {\begin{array}{*{20}c} 1 \\ 0 \\ \end{array} } \right]\), \(\left| V \right\rangle = \left| 1 \right\rangle = \left[ {\begin{array}{*{20}c} 0 \\ 1 \\ \end{array} } \right]\), and the relative phase ϕ depends mainly on the phase-matching conditions and the width of the crystal used77. However, in order not to complicate the subsequent theoretical deduction of the new protocol, the Bell state considered here will be the following:
where \(CNOT = \left[ {\begin{array}{*{20}c} 1 & 0 & 0 & 0 \\ 0 & 1 & 0 & 0 \\ 0 & 0 & 0 & 1 \\ 0 & 0 & 1 & 0 \\ \end{array} } \right]\) is the Feynman’s gate6, \(H = \frac{1}{\sqrt 2 }\left[ {\begin{array}{*{20}c} 1 & {\;\;1} \\ 1 & { - 1} \\ \end{array} } \right]\) is the Hadamard’s gate6, \(I = \left[ {\begin{array}{*{20}c} 1 & 0 \\ 0 & 1 \\ \end{array} } \right]\) is the identity matrix, (·)T means transpose of (·), and ⨂ is the Kronecker’s product6.
Sketch of the entanglement swapping protocol composed of three well-defined sectors: two independent EPR sources of the \(\left| {\beta_{00} } \right\rangle\)-type, one quantum repeater between both sources, and the density matrix of the final state \(\rho_{{\left| {\beta_{00} } \right\rangle }}\), where a gray element represents a value of 0.5, while a white element is equal to a value of 0.
As we will see in the experiments on the optical table, all measurement modules will be implemented using polarizing beam-splitting (PBS)77, and avalanche photodiodes (APD), and configured according to the H/V basis. Since we will use PBSs of the best quality on the market, and we consider that we will manipulate Bell states of the type of Eq. (2), we expect quasi-perfectly equiprobable outputs for both faces of the PBSs used in configurations like that of Fig. 1:
where M is the measurement operator, Ph is the horizontal polarization operator, and Pv is the vertical polarization operator.
In Fig. 1, the intervention of the quantum repeater gives rise to transitivity (q[0] is entangled with q[1], and q[2] is entangled with q[3] ⟹ q[0] is entangled with q[3], but q[1] is not entangled with q[2]), where the original entangled states at the output of each EPR source end up linking in a new unique and final Bell state, between the qubits furthest from the configuration, which is concomitant with the idea of extending the range of the entanglement so that the quantum network reaches where it is necessary.
From now on, in all theoretical figures, single lines represent quantum wires, while double lines will be classical wires.
The resulting density matrix, between the extreme qubits q[0] and q[3], will be identical to the density matrices of the original EPR sources between the respective qubits q[0] and q[1], and q[2] and q[3]. In consequence, considering Eq. (2), yields:
Therefore, in the following theoretical figures, a gray element of the density matrix represents a value of 0.5, while a white element is equal to a value of 0.
Figure 2 shows a more complete intervention of the entanglement swapping protocol when it is used with four independent EPR sources, then intervening three quantum repeaters, but with identical results to the previous case, given that we obtain a density matrix like that of Eq. (4) between the most extreme qubits, i.e., q[0] and q[7]. In this case, we are in the presence of a double transitivity, because the application of the protocol takes place involving pairs of EPR sources. Thus, q[0] is entangled with q[1], and q[2] is entangled with q[3] ⟹ q[0] is entangled with q[3]; but q[1] is not entangled with q[2], and q[4] is entangled with q[5], and q[6] is entangled with q[7] ⟹ q[4] is entangled with q[7]; but q[5] is not entangled with q[6], ⟹ q[0] is entangled with q[7]; but q[3] is not entangled with q[4].
Sketch of the entanglement swapping protocol composed of three well-defined sectors: four independent EPR sources of the \(\left| {\beta_{00} } \right\rangle\)-type, three quantum repeaters between those sources, and the density matrix of the final state \(\rho_{{\left| {\beta_{00} } \right\rangle }}\). The application of the protocol is carried out by grouping the states of the \(\left| {\beta_{00} } \right\rangle\)-type in pairs until reaching a single final state between the extreme qubits q[0] and q[7], thus reaching the maximum extension of the entanglement range for this configuration.
Figure 3 shows the simplified entanglement swapping protocol applied to the simplest possible case, which is equivalent to that of Fig. 1 for the original version of the protocol. In this case, we will proceed to the theoretical deduction of the protocol to verify its performance. For this, we calculate the joint state of the four qubits at each of the six instants \(\left( {t_{i} \forall i \in \left[ {0,5} \right]} \right)\) indicated in Fig. 1:
where \(\left| + \right\rangle = \left[ {\begin{array}{*{20}c} {{1 \mathord{\left/ {\vphantom {1 {\sqrt 2 }}} \right. \kern-0pt} {\sqrt 2 }}} & {{1 \mathord{\left/ {\vphantom {1 {\sqrt 2 }}} \right. \kern-0pt} {\sqrt 2 }}} \\ \end{array} } \right]^{T}\),
and
Sketch of the proposed entanglement swapping protocol also composed of three well-defined sectors: two independent EPR sources of the \(\left| {\beta_{00} } \right\rangle\)-type, one quantum repeater between both sources and the density matrix of the final state \(\rho_{{\left| {\beta_{00} } \right\rangle }}\), where the only difference with the scheme in Fig. 1 lies in the quantum repeater.
The strange final state resulting from Eq. (5f) is the same one obtained in the far right of Fig. 3, where we have a shared state of the \(\left| {\beta_{00} } \right\rangle\)-type between the qubits q[0] and q[3], while the central qubits remain at \(\left| 0 \right\rangle\). We also noticed a drop of 3dB, i.e., ½, in the final state modulus due to the action of both horizontal polarizers Ph. However, this decay only takes place in the central qubits and not in the extreme ones, i.e., those that share the \(\left| {\beta_{00} } \right\rangle\) state, which is complete and without attenuation.
In other words, at time t5 in Fig. 3 we obtain the same identity matrix as that of the original protocol in Figs. 1 and 2, with gray elements at ½ and white elements at 0.
Comparing both versions of the entanglement swapping protocol, see Figs. 1 and 3, we can observe the simplicity of the new version compared to the traditional one.
In Appendix A, we discuss the impact of non-maximal entangled states because of the presence of noise in the quantum channel, which degrades the fidelity of the entanglement.
Figure 4 shows an extension of the new protocol of Fig. 3, which inherits the simplicity in the transitivity from the last one, but for the case of four independent EPR sources and three quantum repeaters. As in Figs. 1 and 2, in Figs. 3 and 4 we can see three well-defined areas: EPR sources, quantum repeaters, and density matrix (outcomes). In Fig. 4, the total absence of classic channels, as well as the unitary transforms associated with them, simplifies implementation, lowers costs, and reduces the time involved in the project. Finally, as we will see in the experiments on the optical table, the great regularity in the structure of the quantum repeater modules will be reflected in their optical implementation, where said implementation will be exclusively optical with all the advantages that this will entail for the future industry associated with the future quantum internet32,33,34,35,36,37,38,39,40,41.
Sketch of the new entanglement swapping protocol is also composed of three well-defined sectors: four independent EPR sources of the \(\left| {\beta_{00} } \right\rangle\)-type, three quantum repeaters between those sources, and the density matrix of the final state \(\rho_{{\left| {\beta_{00} } \right\rangle }}\). As in Fig. 2, the application of the new protocol is carried out by grouping the states of the \(\left| {\beta_{00} } \right\rangle\)-type in pairs until reaching a single final state between the extreme qubits q[0] and q[7], thus reaching the maximum extension of the entanglement range for this configuration.
Bell state change test
Below is the theoretical description of the first experiment that will help us evaluate the performance of the new entanglement swapping protocol.
In the upper right corner of Fig. 5, after carrying out the supposedly successful entanglement swapping by the new protocol, we introduce two gates, of the Pauli6 matrix type {X, Z}, in the qubit q[0]:
Bell state change test: the same configuration of Fig. 1 with a pair of Pauli gates {X, Z} with their respective activation bits {bx, bz} in the qubit q[0], after entanglement swapping.
\(X = \left[ {\begin{array}{*{20}c} 0 & {\quad 1} \\ 1 & {\quad 0} \\ \end{array} } \right]\), and
\(Z = \left[ {\begin{array}{*{20}c} 1 & {\quad 0} \\ 0 & {\quad - 1} \\ \end{array} } \right]\),
Each with its respective activation bit, i.e., phase and parity bits {bx, bz}. Both gates will be implemented on the optical table as two half-wave plates (HWP).
The experiment consists of demonstrating that as a result of the action of the new protocol, two originally independent qubits, such as q[0] and q[3], are now maximally correlated, sharing a Bell state of the \(\left| {\beta_{00} } \right\rangle\)-type, in such a way that the activation of the X and Z gates will force a change of state in the Bell state between both qubits. This can be seen in detail in Table 1, where if we assume the success of the protocol, the qubits q[0] and q[3] will share a Bell state of the \(\left| {\beta_{00} } \right\rangle\)-type, for bx = 0 and bz = 0, i.e., both qubits are correlated. However, if, for example, we activate the parity bit bx, the gate X, we then go from the state of Bell \(\left| {\beta_{00} } \right\rangle\) to the state of Bell \(\left| {\beta_{01} } \right\rangle\), with the qubits q[0] and q[5] now being anti-correlated. The transitions between Bell states in Table 1 should be checked on the optical table by comparing and analyzing the correlations between the qubits q[0] and q[5].
As a theoretical check, if the final state of Eq. (5f) we first apply a SWAP gate between the states q[3] and q[2], and then another SWAP gate between the qubits q[2] and q[3], we will have:
If we now activate the parity bit, i.e., bx = 1, we will thus activate the gate X in Fig. 5, therefore, the state of Eq. (5f) will be affected as follows:
If we now apply to Eq. (7) the same procedure that concluded in Eq. (6), we will have:
Equations (6) and (8) constitute a double theoretical verification that the new protocol works correctly, given that the following can be directly observed:
-
(1)
at the output of Fig. 3 we effectively have a shared state of type \(\left| {\beta_{00} } \right\rangle\) between the qubits q[0] and q[3] and as a consequence,
-
(2)
by applying the X gate to the qubit q[0], a new Bell state is shared between the qubits q[0] and q[3], where in this case it is a \(\left| {\beta_{01} } \right\rangle\) state.
Finally, Fig. 6 shows the theoretical 3D density matrices of the Bell states in terms of phase and parity bits {bx, bz}. During the implementation of this experiment on the optical table, we will compare these matrices with those obtained there. As we have mentioned before, in that case, both Pauli matrices {X, Z} will be implemented by adjustments to the angles θ of two half-wave plates (HWPs), where said angle will be θ = {0, π/4} ⇌ {X, Z}, respectively.
Bell test from two independent sources of entangled photons
Except for the fact that the Bell state of the \(\left| {\beta_{00} } \right\rangle\)-type, shared between the qubits q[0] and q[3], results from the application of the presented entanglement swapping protocol, given that before this these qubits were completely independent, the experiment Fig. 7 represents a simple Bell test78,79,80,81. In this way, if the protocol works correctly and the qubits q[0] and q[3] really share a Bell state of the \(\left| {\beta_{00} } \right\rangle\)- type, the appropriate rotation of the linear polarizers, Pα in the qubit q[0] and Pβ in the qubit q[3], they should show us the probability curves that are typical in this type of experiment. Then, defining the 2D rotation matrix for a generic angle θ as:
we can define the generic polarizer Pθ from Rθ,
Therefore, if we now define a generic outcome because of the application of the generic polarizer Pθ, it results:
Consequently, for the case of Fig. 7, in which we have a Bell state \(\left| {\beta_{00} } \right\rangle\) shared between the qubits q[0] and q[3], and a polarizer Pα in the qubit q[0] and a polarizer Pβ in the qubit q[3], the associated probability is:
The result obtained in Eq. (12a), corresponds to the case that before the polarizer Pα, we do not activate any of the X or Z matrices. If instead, we decide to activate Pauli gates, as in the case of Fig. 5, for each remaining Bell state we will have:
In the experiment on the optical table, we will evaluate the performance of Fig. 7 when we work with a Bell state of type \(\left| {\beta_{00} } \right\rangle\) between the qubits q[0] and q[3]. In this case, we assign a fixed angle to Pβ from the set β = {0, π/4, π/2, 3π/4}, and for each of those angles, we rotate the polarizer Pα completely. If the new entanglement swapping protocol works correctly, we should experimentally verify the coincidences or probabilities of Eq. (12a).
Optical table
Next, we will implement the experiments from the previous section on the optical table, for which this section is organized into three well-defined subsections:
-
(a)
Preparation of the configuration common to both experiments,
-
(b)
Bell state change test, and
-
(c)
Bell test from two independent sources of entangled photons.
Preparation of the configuration common to both experiments.- Here, we will carry out the linear tomography82 and the maximum likelihood tomography82 from the experimental data of the two EPR sources of the \(\left| {\beta_{00} } \right\rangle\)-type used. With these, we calculate the respective density matrices of both sources. The density matrix from the linear tomography of Source #1 (LT1) is:
while the density matrix from the maximum likelihood tomography of Source #1 (MT1) is:
The density matrix from the linear tomography of Source #2 (LT2) is:
while the density matrix from the maximum likelihood tomography of Source #2 (MT2) is:
The four density matrices of Eq. (13) can be seen in Fig. 8. From these density matrices, we will obtain the tangle, the linear entropy, the Fidelity, and the errors. The state was calibrated several times to progressively improve the tangle. Two completely independent sources of entangled photons were used, from two 405nm pump lasers, with a range of power between 20mw and 50mW, and two pairs of solid blocks (5 × 5 × 3 mm3) of β-barium-borate (BBO) crystal to produce Type-I down-conversion. In each source, one crystal was attached after another, where the second is rotated 90º with respect to the first. Although in each source, two Type-I crystals were used, the joint action of both crystals mutually rotated by 90º generates Bell states of the \(\left| {\beta_{00} } \right\rangle\)-type.
We use two identical gallium-nitride (GaN) diode lasers for two reasons:
-
(a)
it has greater stability and temperature control, and.
-
(b)
its short wavelength allows us to work with efficient detectors of 810 nm.
Each blue diode laser beam (405 nm, 50mW) passes through a zero-order half-wave plate (HWP) with a phase of 22.5º, which represents a Hadamard matrix6. Then, the laser beam passes through a narrow bandpass filter or quartz plate of 405 nm, i.e., a ∝ -BBO, as a phase-matching crystal. Thanks to this, photons with a state of polarization of diagonal type \(\left| + \right\rangle\) are obtained. At each source, a beam with that polarization enters the first crystal, it generates a pair \(\left| {HH} \right\rangle\), while upon entering the second crystal, it generates a pair \(\left| {VV} \right\rangle\), in such a way that together both pairs generate the state \(\left| {\beta_{00} } \right\rangle\).
After each configuration of double Type-I crystal, a BBO is used on each beam. Besides, a block of pinhole + filter(808 nm) + lens at the entrance of each avalanche photodiode (APD). Other elements were used in the compensation and calibration phases.
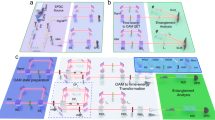
Using a 405 nm laser pump, this configuration produces a 6º cone at the output of the second crystal, i.e., 3º for the branch known as signal (810 nm) and -3º for the branch known as idler (810 nm), with a phase matching angle for Type-I down-conversion of approximately 29º. In both figures, 9 and 11, the angle between both beams (signal and idler) was exaggerated to better appreciate the layout, where the beam path dimensions are not to scale.
Continuing with the implementation of the protocols of Figs. 9 and 11, both outgoing beams of the second BBO are deflected by two mirrors so that all the geometry of the protocol is completely contained within the useful perimeter of the optical table. A third beam collinear with the beam incident to the first BBO crystal and forming the same angle with respect to the two beams mentioned before (signal, and idler) is intercepted by a beam blocker.
Bell state change test on the optical table. The angles of the HWPs located in the upper beam are set manually, such that {0, π/4} ⇌ {X, Z}, respectively. The results obtained by all the detectors, from 1 to 6, are sent to their respective APDs, and from these to a time-tagger, which collects all the signals coming from the APDs at the same time and sends them to the computer to obtain the final density matrices of the four Bell states obtained.
Two dual-wavelength 405/810 nm polarizing beam-splitter (PBS) of 0.5″ × 0.5″ × 0.5″ are used in both experiments. When working at 810 nm, the APDs have an efficiency of 60%, and we have worked with acquisition times ranging from 50 ms to 1 s, with and without a block of pinhole + filter(808 nm) + lens before the APDs. A six-channel time-tagger device is used after the four APDs.
Several elements are not shown in Figs. 9 and 11 of both experiments on the optical table so as not to complicate them.
In both experiments, the quantum repeater is implemented thanks to a beam-splitter of 808/810 nm, four mirrors, a zero-order half-wave plate (HWP) with a phase of 22.5º, which represents a Hadamard matrix6, and two 810 nm calcite film polarizer fixed at horizontal polarization (which is good throughout the visible spectrum and has high extinction ratios).
Two lasers were used although a single one could have been used and resorted to the central outgoing beam of the spontaneous parametric down conversion (SPDC) process77 at the exit of the first BBO crystal, so that it impacts a new pair of Type I crystals and thus generate the second pairs of entangled photons83, but we abandoned this option to avoid any eventual spurious coupling between the pairs of entangled photons from both sources that would disturb the performance of the experiments. In this way, aligning both independent configurations to produce entangled photons of the \(\left| {\beta_{00} } \right\rangle\)-type, the metrics obtained with each source were the following:
-
Source #1: tangle = 0.9715 ± 0.0003, linear entropy = 0.0648, Fidelity = 0.9819 ± 0.0001, and errors of the order of 0.014, and
-
Source #2: tangle = 0.9685 ± 0.0003, linear entropy = 0.0703, Fidelity = 0.9783 ± 0.0001, and errors of the order of 0.014.
As we can see, both sources have practically identical metrics, which is extremely convenient for the performance of both experiments.
Bell state change test.-Fig. 9 shows the layout of this experiment, with two 808/810nm zero-order half-wave plates (HWP) employed for the implementation of the X and Z Pauli matrices with angles of {0, π/4} ⇌ {X, Z}, respectively. The intervention of these HWPs, as well as their values depends on the transition that is carried out between the original state generated by each source of entangled photons, i.e., \(\left| {\beta_{00} } \right\rangle\), and the states that must be reached to verify the performance of the new protocol and that are the central axis of the present experiment, that is, \(\left\{ {\left| {\beta_{01} } \right\rangle ,\left| {\beta_{10} } \right\rangle ,\left| {\beta_{11} } \right\rangle } \right\}\). In this way, these transitions are:
In Eq. (14), the identity matrix I represents the absence of an HWP in that position. The angles of both HWPs located in the upper beam of Fig. 9 are set manually, according to the transitions of Eq. (14). The results obtained by the six detectors, labeled from 1 to 6, are sent to their respective APDs, and from these to a time-tagger, which collects all the signals coming from the APDs at the same time and sends them to the computer to obtain the final density matrices of the four Bell states obtained.
Figure 10 shows the state density matrices in terms of the phase and the parity bits, both for the original state \(\left| {\beta_{00} } \right\rangle\) generated because of the action of the new protocol and those due to the transitions resulting from Eq. (14). In Fig. 5, those bits acted as exponents of the respective Pauli matrices {Z, X}, therefore,
the parity and phase bits of Fig. 10 act as activation bits {bz, bx} of the HWPs that represent the Pauli matrices X and Z, giving rise to the transitions of Eq. (14), so that, for {bz, bx} = {0, 0}, we see the density matrix corresponding to the Bell state generated by the new protocol, i.e., \(\left| {\beta_{00} } \right\rangle\), while for the remaining cases, we have {bz, bx} = {0, 1} = > \(\left| {\beta_{01} } \right\rangle\), {bz, bx} = {1, 0} = > \(\left| {\beta_{10} } \right\rangle\), and {bz, bx} = {1, 1} = > \(\left| {\beta_{11} } \right\rangle\).
A simple visual inspection shows the similarity between Figs. 6 and 10, theoretical and experimental, respectively, which tells us about the excellent performance of the new protocol, leaving no doubt that the extreme qubits of the protocol share a common \(\left| {\beta_{00} } \right\rangle\)-type entangled state.
Bell test from two independent sources of entangled photons.-As we can see in Fig. 11, at the end of the signal beam of Source #1, we interrupt the beam with the polarizer Pα, while we do the same with Source #2, in its idler beam, with the polarizer Pβ. The Pβ polarizer, an 810nm calcite film polarizer, is set manually, while the Pα polarizer can be implemented using some of the following configurations:
-
(a)
an 808/810 nm rotatable polarizer (Pθ), i.e., a unique and special variable-angle-device, where the angle of the polarizer is controlled using external commands coming from the waveplate controller,
-
(b)
two 808 nm electro-optical modulators (EOM): \(EOM\left( \theta \right) \times P_{h} \times EOM\left( \theta \right)\), and
-
(c)
two 808/810 nm HWPs: \(HWP\left( {{\theta \mathord{\left/ {\vphantom {\theta 2}} \right. \kern-0pt} 2}} \right) \times P_{h} \times HWP\left( {{\theta \mathord{\left/ {\vphantom {\theta 2}} \right. \kern-0pt} 2}} \right)\).
Bell test from two independent sources of entangled photons on the optical table. Taking into account everything common with the experiment in Fig. 9, this experiment consists of two polarizers interrupting the upper and lower beam of the figure, one fixed, the lower one, at each of the angles β = {0, π/4, π/2, 3π/4}, while the other varies according to the commands that the computer sends to the waveplate controller, responsible for the variation of the angle in the upper polarizer.
In cases (b and c), the angle is also controlled by external commands coming from the waveplate controller. For this experiment, option (b) was used due to the availability of its components in our laboratory.
As we have mentioned previously, the experiment consists of manually setting the value of the polarizer Pβ at each of the following angles β = {0, π/4, π/2, 3π/4} and having the computer generate the necessary commands for the configuration of the option (b), corresponding a Pα, sweep all the angles from 0 to 2π to plot the probability/coincidence curves of Eq. (12a). In other words, we leave the polarizer Pβ fixed at one of the following angles β = {0, π/4, π/2, 3π/4} while Pα makes a complete rotation controlled by the waveplate controller. In this way, we will carry out a complete plot of the curves of Eq. (12a) for the four angles of the polarizer Pβ.
If we now make θ = α—β, and define the following coincidence rates:
-
R(θ) is the coincidence rate in terms of the angle with both polarizers,
-
Ro is the coincidence rate with the two polarizers removed.
-
R(θ)/Ro is the normalized coincidence rate as a function of the relative polarizer orientation.
Figure 12 shows the normalized coincidence rate R(θ)/Ro as a function of the relative polarizer orientation. Therefore, If Bob's polarizer Pβ is set to a polarization H (0º), and Alice's polarizer Pα is fully and automatically rotated by the waveplate controller, it can be seen in the top-left curve of Fig. 12 that the coincidences start at a maximum since both Bob and Alice are with their horizontal polarizers. The maxima and minima alternate every π/2 rad on the graph scale). The accounts of this experiment are complementary to those of the following experiment. The curve in green represents the ideal or theoretical case of Eq. (12a), while the distribution of the red rings represents the curve that results from the coincidences found by the computer. Now, Bob's polarizer Pβ is set to a polarization V (π/2), and Alice's polarizer Pα is again fully and automatically rotated by the waveplate controller, it can be seen in the top-right curve of Fig. 12 that the coincidences start at a minimum, since Alice always starts with horizontal polarization. In this case, the oscillations are also consistent, changing from minimum to maximum and vice versa every π/2 rad. Setting Bob Pβ's polarizer to diagonal polarization D (π/4) or \(\left| + \right\rangle = \left[ {\begin{array}{*{20}c} {{1 \mathord{\left/ {\vphantom {1 {\sqrt 2 }}} \right. \kern-0pt} {\sqrt 2 }}} & {{1 \mathord{\left/ {\vphantom {1 {\sqrt 2 }}} \right. \kern-0pt} {\sqrt 2 }}} \\ \end{array} } \right]^{T}\), and always carrying out the same procedure in the Alice Pα polarizer, the lower-left curve of Fig. 12 emerges, which we observe starts with an intermediate value. Something similar happens when Bob Pβ's polarizer is set to anti-diagonal polarization A (3π/4) or \(\left| - \right\rangle = \left[ {\begin{array}{*{20}c} {{1 \mathord{\left/ {\vphantom {1 {\sqrt 2 }}} \right. \kern-0pt} {\sqrt 2 }}} & {{{ - 1} \mathord{\left/ {\vphantom {{ - 1} {\sqrt 2 }}} \right. \kern-0pt} {\sqrt 2 }}} \\ \end{array} } \right]^{T}\), the complete rotation of Alice Pα's polarizer, always starting from the horizontal polarization, gives rise to the lower-right curve of Fig. 12, which also coincides perfectly with the expected results for this type of experiment.
Finally, the results of Fig. 12 are remarkably coincident with the theoretical probability expressed in Eq. (12a), which again proves the performance of the new protocol, given that if it did not carry out a true entanglement swapping process, it would be impossible to achieve the results of both experiments presented here.
Discussions
As we could observe throughout this study, the new protocol requires the intensive use of horizontal polarizers, such as those mentioned in Eq. (3). For this reason, this protocol can only be implemented optically, given that the version of the horizontal polarizers used in the physical computers of the IBM Q Experience program84, as well as those of Rigetti Computing85, called qubit reset gate, are of the type shown in Fig. 13. The problem with this implementation is the following: within the qubit reset gate highlighted in red and located in the qubit q[0] at the output of the entangled pair source of the \(\left| {\beta_{00} } \right\rangle\)-type, the quantum measurement module generates at its output at time t1 an equiprobable result of type \(\left\{ {\begin{array}{*{20}c} {\left| 0 \right\rangle } \\ {50\% } \\ \end{array} \begin{array}{*{20}c} , \\ {} \\ \end{array} \begin{array}{*{20}c} {\left| 1 \right\rangle } \\ {50\% } \\ \end{array} \;} \right\}\). This same result is projected to its partner qubit q[1] at that same moment. If the output of the quantum measurement module turns out to be \(\left| 0 \right\rangle\), the inverter Pauli matrix X is not activated, but if the output turns out to be \(\left| 1 \right\rangle\), then the inverter X is activated, so that the output of the qubit reset gate is always \(\left| 0 \right\rangle\) at time t2. However, the qubit q[1] will end up with any of the two possible values, that is to say, the result necessary for the correct functioning of the protocol according to Eq. (5) is never generated. This way of implementing the qubit reset gate is known as the dynamic version, which is 1000 times faster than the static version, the latter being the version required by Eq. (5) to be able to correctly implement the new protocol on any platform of the IBM Q Experience program84 or Rigetti Computing85. This is the reason why these companies do not implement a matrix version more like that of the linear polarizer used in optical implementations.
Qubit reset gate in an entanglement context. A version of the horizontal polarizer Ph in any physical machine of the IBM Q Experience program84, and the Rigetti Computing family85. Within the qubit reset gate located in the qubit q[0] at the output of the entangled pair source, the quantum measurement module generates at its output at time t1 an equiprobable result of type \(\left\{ {\begin{array}{*{20}c} {\left| 0 \right\rangle } \\ {50\% } \\ \end{array} \begin{array}{*{20}c} , \\ {} \\ \end{array} \begin{array}{*{20}c} {\left| 1 \right\rangle } \\ {50\% } \\ \end{array} \;} \right\}\). This same result is projected to its partner qubit q[1]. If the output of the quantum measurement module is \(\left| 0 \right\rangle\), the inverse X is not activated, but if the output is \(\left| 1 \right\rangle\), then the inverter X is activated, so that the output of the qubit reset gate is always \(\left| 0 \right\rangle\) at time t2. However, the qubit q[1] will end up with any of the two possible values, thus not generating the result necessary for the correct functioning of the protocol according to Eq. (5).
Currently, the qubit reset gate is only implemented in the manner required by Eq. (5) in simulators such as Quirk86, and Quantum Programming Studio87.
Although not necessary for the correct operation of the protocol, the 3dB drop seen in Eq. (5f) can be compensated by an optical amplifier88.
For the experimental verification of the performance of the proposed protocol, two remarkably different experiments were carried out, both from a theoretical point of view, according to Figs. 5 and 7, as experimental on the optical table, from Figs. 9 and 11. The most outstanding difference between both experiments lies in the static nature of the first and dynamic nature of the second since in the experiment of Fig. 9, the angles of both HWP are set in order to establish which of the gates X and/or Z have to interrupt the beam corresponding to the signal ray of the upper pair, then the average of all the states measured in the computer and it is confirmed that we are in the presence of another Bell state different from the original one established in \(\left| {\beta_{00} } \right\rangle\) between the signal beam of the upper pair and the idler beam of the lower pair. On the other hand, in the experiment in Fig. 11, the polarizer P∝ of the signal beam of the upper pair rotates from 0º to 2π according to the orders of the waveplate controller, while the polarizer Pβ of the idler beam of the lower pair remains fixed at some of them four relevant cases, i.e., {H, V, D, A}. Both experiments equally show that they could only give the results obtained in Figs. 10 and 12 if the signal beam of the upper pair shares a \(\left| {\beta_{00} } \right\rangle\)-type state with the idler beam of the lower pair, i.e. if the new entanglement swapping protocol has worked correctly.
Regarding the savings in implementation costs of the proposed version of the entanglement swapping protocol compared to the original, we can say that for two independent EPR sources, which implies one quantum repeater, we save one {Controlled-Z, Controlled-X} pair and two classical channels, and for four independent EPR sources, which implies three quantum repeaters, we save three {Controlled-Z, Controlled-X} pairs and six classical channels, then, for N-independent EPR sources, which implies N-1 quantum repeaters, we save N-1 {Controlled-Z, Controlled-X} pair and 2(N-1) classical channels.
The configuration of the new protocol implies more than a simple saving of physical resources during the implementation of a certain network since the proposed architecture facilitates the creation of reusable and interchangeable commercial modules in a way as natural as if they were building blocks to be used in a wall.
Finally, although this new version of the entanglement swapping protocol does not use classical disambiguation channels or unitary transforms like the original version, the protocol itself does not transmit information, but simply couples and decouples conveniently qubits from two independent sources of entangled photons, generating a third entangled state common to the most extreme qubits of the configuration to extend the range of entanglement. In this way, the range extension is more efficient when implementing a quantum network in fiber optics or free-space configurations.
Conclusions
The possibility of eliminating multiple classical channels as well as the corresponding unitary transforms allows for dramatically lower implementation costs of the new entanglement swapping protocol compared to the original version for extensive fiber optic laying, as well as long distances between member satellites of a space quantum network, which shows a clear projection of the new protocol on the future quantum internet. Furthermore, the replacement of the classical channels and their corresponding unitary transforms with the linear horizontal polarizers significantly simplifies the implementation of the new protocol on the optical table for both experiments developed in this work to study its performance. All this translates into savings in quantum memory because the new protocol is clearly less sensitive to synchronization problems between qubits than its original counterpart.
Both experiments equally demonstrated the high performance of the new version of the protocol, which allows us to estimate a similar performance in future implementations of the new protocol when it is involved in configurations that transmit information thanks to its intervention.
The fact that this protocol can only be implemented in optical environments does not represent a limitation at all since it is the natural environment in which it should intervene.
Finally, the complete dataset with the experimental outcomes of both experiments can be acquired according to the conditions established in the data availability statement.
Data availability
The data that support the findings of this study are available on request from the corresponding author.
References
Audretsch, J. Entangled Systems: New Directions in Quantum Physics (Wiley-VCH Verlag GmbH & Co., 2007).
Jaeger, G. Entanglement, Information, and the Interpretation of Quantum Mechanics (Springer-Verlag, 2009).
Horodecki, R., Horodecki, P., Horodecki, M. & Horodecki, K. Quantum entanglement. Rev. Mod. Phys. 81(2), 865–942 (2009).
Einstein, A., Lorentz, H. A., Minkowski, H. & Weyl, H. The Principle of Relativity: A Collection of Original Memoirs on the Special and General Theory of Relativity (Courier Dover Publications, 1952).
Phillips, A. C. Introduction to Quantum Mechanics (Wiley, 2003).
Nielsen, M. A. & Chuang, I. L. Quantum Computation and Quantum Information (Cambridge University Press, 2004).
Rieffel, E. & Polak, W. Quantum Computing: A Gentle Introduction (The MIT Press, 2011).
Gruska, J. Quantum computing (McGraw-Hill, N.Y., 1999–2005).
Wu, Y. M., Fan, G. & Du, F. F. Error-detected three-photon hyperparallel Toffoli gate with state-selective reflection. Front. Phys. 17(5), 51502 (2022).
Du, F. F., Wu, Y. M. & Fan, G. Refined quantum gates for ∧-type atom-photon hybrid systems. Adv. Quantum Technol. 6(9), 2300090 (2023).
Du, F. F., Fan, G., Ren, X. M. & Ma, M. Deterministic hyperparallel control gates with weak Kerr effects. Adv. Quantum Technol. 6(10), 2300201 (2023).
Cariolaro, G. Quantum Communications: Signals and Communication Technology (Springer, 2015).
Pathak, A. Elements of Quantum Computation and Quantum Communication (Taylor & Francis Group, 2013).
Mishra, V. K. An Introduction to Quantum Communication (Momentum Press, 2016).
Imre, S. & Gyongyosi, L. Advanced Quantum Communications: An Engineering Approach (Wiley-IEEE Press, 2012).
Wootters, W. & Zurek, W. A single quantum cannot be cloned. Nature 299, 802–803 (1982).
Bennett, C. H. et al. Teleporting an unknown quantum state via dual classical and Einstein-Podolsky-Rosen channels. Phys. Rev. Lett. 70(13), 1895–1899 (1993).
Mastriani, M. Multi-qubit teleportation and multi-bit superdense coding via cascade splitting. Opt. Quant. Electron. 55, 1026 (2023).
Mastriani, M. Quantum key secure communication protocol via enhanced superdense coding. Opt. Quant. Electron. 55, 10 (2023).
Zhou, S. Q. et al. Bidirectional quantum operation teleportation with different states. Int. J. Quantum Inf. 16(05), 1850042 (2018).
Seida, C., Seddik, S., Hassouni, Y. & El Allati, A. Memory effects on bidirectional teleportation. Phys. A: Stat. Mech. Appl. 606(15), 128115 (2022).
Seida, C., El Allati, A., Metwally, N. & Hassouni, Y. Multi-party bidirectional teleportation. Optik 247, 167784 (2021).
Aliloute, S., El Allati, A., El Aouadi, I. & Metwally, N. Bidirectional teleportation through an entangled coherent quantum network. J. Opt. Soc. Am. B. 38(12), 3784–3793 (2021).
Seida, C., El Allati, A., Metwally, N. & Hassouni, Y. Bidirectional teleportation using Fisher information. Modern Phys. Lett. A. 35(33), 2050272 (2020).
Aliloute, S., El Allati, A. & El Aouadi, I. Bidirectional teleportation using coherent states. Quantum Inf. Process. 20, 29 (2021).
Malik, J. A., Lone, M. Q. & Malla, R. A. Symmetric bidirectional quantum teleportation using a six-qubit cluster state as a quantum channel. Pramana J. Phys. 97, 50 (2023).
Mastriani, M. How can a random phenomenon between particles be synchronized instantaneously and independently of the distance between said particles?. Opt. Quant. Electron. 54, 235 (2022).
Mastriani, M. Teleporting digital images. Opt. Quant. Electron 55(498), 1–33 (2023).
Mastriani, M. Non-ambiguous and simplified quantum teleportation protocol. EPJ Quantum Technol. 10, 14 (2023).
Mastriani, M. The theorem of unified locality. Appl. Sci. 5, 192 (2023).
Mastriani, M. Quantum stretching protocol to share states among three nonlocal qubits. Opt. Quant. Electron. 55(986), 1–41 (2023).
Cacciapuoti, A. S., Caleffi, M., van Meter, R. & Hanzo, L. When entanglement meets classical communications: quantum teleportation for the quantum internet. IEEE Trans. Commun. 68(6), 3808–3833 (2020).
Caleffi, M., Chandra, D., Cuomo, D., Hassanpour, S. & Cacciapuoti, A. S. The rise of the quantum internet. Computer 53(06), 67–72 (2020).
Cacciapuoti, A. S. et al. The quantum internet: Networking challenges in distributed quantum computing. IEEE Network 34(1), 137–143 (2020).
Caleffi, M., Cacciapuoti, A. S. & Bianchi, G. Quantum internet: From communication to distributed computing. NANOCOM '18: Proceedings of the 5th ACM International Conference on Nanoscale Computing and Communication, September 3:1–4 (2018).
Gyongyosi, L. & Imre, S. Entanglement accessibility measures for the quantum internet. Quant. Info. Proc. 19, 115 (2020).
Gyongyosi, L. & Imre, S. Entanglement access control for the quantum internet. Quant. Info. Proc. 18, 107 (2019).
Gyongyosi, L. & Imre, S. Opportunistic entanglement distribution for the quantum internet. Nature Sci. Rep. 9, 2219 (2019).
Wehner, S., Elkouss, D. & Hanson, R. Quantum internet: A vision for the road ahead. Science 362(6412), eaam9288 (2018).
Castelvecchi, D. Here’s what the quantum internet has in store: Physicists say this futuristic, super-secure network could be useful long before it reaches technological maturity, Nat. News (2018).
Kimble, H. J. The quantum internet. Nature 453, 1023–1030 (2008).
Sergienko, A. V. (ed.) Quantum Communications and Cryptography (Taylor and Francis, 2006).
Kumar, N. et al. (eds) Limitations and Future Applications of Quantum Cryptography (IGI Global, 2021).
Shor, P. W. Polynomial-time algorithms for prime factorization and discrete logarithms on a quantum computer. SIAM J. Comput. 26(5), 1484–1509 (1997).
Rivest, R., Shamir, A. & Adleman, L. A method for obtaining digital signatures and public-key cryptosystems. Commun. ACM 21(2), 120–126 (1978).
Bennett, C. H. & Brassard, G. Quantum cryptography: Public key distribution and coin tossing. In Proceedings of IEEE International Conference on Computers, Systems and Signal Processing, Bangalore, India, 175–179 (1984).
Zhang, Y. & Ni, Q. Design and analysis of random multiple access quantum key distribution. Quantum Eng. 2, e31 (2020).
Ekert, A. K. Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67(6), 661–663 (1991).
Bennett, C. H. Quantum cryptography using any two non-orthogonal states. Phys. Rev. Lett. 68(21), 3121–3124 (1992).
Long, G. L. & Liu, X. S. Theoretically efficient high-capacity quantum-key distribution scheme. Phys. Rev. A 65, 032302 (2002).
Deng, F. G. & Long, G. L. Secure direct communication with a quantum one-time pad. Phys. Rev. A 69, 052319 (2004).
Zhou, Z. R. et al. Measurement-device-independent quantum secure direct communication. Sci. Chin. Phys. Mech. Astron. 63(3), 230362 (2020).
Zhou, L., Sheng, Y. B. & Long, G. L. Device-independent quantum secure direct communication against collective attacks. Sci. Bull. 65(1), 12–20 (2020).
Xie, X. C. Quantum secure direct communication with an untrusted Charlie using imperfect measurement devices. Sci. China Phys. Mech. Astron. 63, 230361 (2020).
Chen, S. S., Zhou, L., Zhong, W. & Sheng, Y. B. Three-step three-party quantum secure direct communication. Sci. China Phys. Mech. Astron. 61, 090312 (2018).
Zou, X. F. & Qiu, D. W. Three-step semi-quantum secure direct communication protocol. Sci. China Phys. Mech. Astron. 57(9), 1696–1702 (2014).
Yan, L., Zhang, S., Chang, Y., Sun, Z. & Sheng, Z. Quantum secure direct communication protocol with mutual authentication based on single photons and bell states. Comput. Mater. Contin. 63(3), 1297–1307 (2020).
Wang, H. F., Zhang, S., Yeon, K. H. & Um, C. I. Quantum secure direct communication by using a GHZ state. J. Korean Phys. Soc. 49(2), 459–463 (2006).
Wen, Q. Y., Jia, H. Y., Qin, S. J. & Gao, F. Fault-tolerant quantum secure direct communication with quantum encryption against collective noise. Chin. Phys. B 21(10), 100308 (2012).
Qi, R. et al. Implementation and security analysis of practical quantum secure direct communication. Light Sci. Appl. 8, 22 (2019).
Long, G. L. & Zhang, H. Drastic increase of channel capacity in quantum secure direct communication using masking. Sci. Bull. 66(13), 1267–1269 (2021).
Sheng, Y. B., Zhou, L. & Long, G. L. One-step quantum secure direct communication. Sci. Bull. 67(4), 367–374 (2022).
Sheng, Y. B. & Zhou, L. Accessible technology enables practical quantum secret sharing. Sci. China Phys. Mech. Astron. 66, 260331 (2023).
Zhou, L., Xu, B. W., Zhong, W. & Sheng, Y. B. Device-independent quantum secure direct communication with single-photon sources. Phys. Rev. Appl. 19(1), 014036 (2023).
Joy, D., Sabir, M., Behera, B. K. & Panigrahi, P. K. Implementation of quantum secret sharing and quantum binary voting protocol in the IBM quantum computer. Quantum Inf. Process. 19, 33 (2020).
Ruihong, Q. & Ying, M. Research progress of quantum repeaters. IOP J. Phys. Conf. Ser. 1237, 052032 (2019).
Boone, K. et al. Entanglement over global distances via quantum repeaters with satellite links. Phys. Rev. A 91(5), 052325 (2015).
Mastriani, M. & Iyengar, S. S. Satellite quantum repeaters for a quantum Internet. Quantum Eng. https://doi.org/10.1002/que2.55 (2020).
Zukowski, M., Zeilinger, A., Horne, M. A. & Ekert, A. K. Event-ready-detectors bell experiment via entanglement swapping. Phys. Rev. Lett. 71(26), 4287–4290 (1993).
Pan, J. W., Bouwmeester, D., Weinfurter, H. & Zeilinger, A. Experimental entanglement swapping: Entangling photons that never interacted. Phys. Rev. Lett. 80(18), 3891–3894 (1998).
Jennewein, T., Weihs, G., Pan, J. W. & Zeilinger, A. Experimental nonlocality proof of quantum teleportation and entanglement swapping. Phys. Rev. Lett. 88(1), 017903 (2001).
Tsujimoto, Y. et al. High-fidelity entanglement swapping and generation of three-qubit GHZ state using asynchronous telecom photon pair sources. Sci. Rep. 8, 1446 (2018).
Jin, R. B., Takeoka, M., Takagi, U., Shimizu, R. & Sasaki, M. Highly efficient entanglement swapping and teleportation at telecom wavelength. Sci. Rep. 5, 9333 (2015).
Schmid, C. et al. Quantum teleportation and entanglement swapping with linear optics logic gates. New J. Phys. 11, 033008 (2009).
de Riedmatten, H. et al. Long-distance entanglement swapping with photons from separated sources. Phys. Rev. A. 71(5), 050302 (2005).
Pastawski, F. Quantum memory: Design and applications, Ph.D. thesis, Munich University (2012). https://d-nb.info/1025224361/34
Grynberg, G., Aspect, A. & Fabre, C. Introduction to Quantum Optics From the Semi-classical Approach to Quantized Light (Cambridge University Press, 2010).
Bell, J. On the Einstein podolsky rosen paradox. Phys. Phys. Fizika 1(3), 195–200 (1964).
Clauser, J. F., Horne, M. A., Shimony, A. & Holt, R. A. Proposed experiment to test local hidden-variable theories. Phys. Rev. Lett. 23(15), 880–884 (1969).
Aspect, A., Grangier, P. & Roger, G. Experimental realization of Einstein-Podolsky-Rosen-Bohm Gedankenexperiment: A new violation of Bell’s inequalities. Phys. Rev. Lett. 49(2), 91–94 (1982).
Aspect, A., Dalibard, J. & Roger, G. Experimental test of Bell’s inequalities using time-varying analyzers. Phys. Rev. Lett. 49(25), 1804–1807 (1982).
James, D. F. V., Kwiat, P. G., Munro, W. J. & White, A. G. Measurement of qubits. Phys. Rev. A 64, 052312 (2001).
Zhang, Y. et al. Simultaneous entanglement swapping of multiple orbital angular momentum states of light. Nat. Commun. 8(632), 1–7 (2017).
IBM Q Experience. https://quantum-computing.ibm.com/. Accessed 28 Mar 2023.
Rigetti Systems. https://qcs.rigetti.com/qpus. Accessed 28 Mar 2023.
Algorithmic Assertions. https://algassert.com/quirk. Accessed 9 June 2023.
Quantum Programming Studio. https://quantum-circuit.com/. Accessed 9 June 2023.
Thorlabs Optical Amplifier https://www.thorlabs.com/navigation.cfm?guide_id=2105. Accessed 28 Mar 2023.
Yan, P. S., Zhou, L., Zhong, W. & Sheng, Y. B. Measurement-based logical qubit entanglement purification. Phys. Rev. A 105(6), 062418 (2022).
Yan, P. S., Zhou, L., Zhong, W. & Sheng, Y. B. Advances in quantum entanglement purification. Sci. China Phys. Mech. Astron. 66, 250301 (2023).
Dotsenko, I. S. & Korobka, R. Entanglement swapping in the presence of white and color noise. Commun. Theor. Phys. 69, 143 (2018).
Jiang, X. X. et al. Reproducible optical noise-like signal generation subjected by digital sequences. Opt. Exp. 25(23), 29189 (2017).
Acknowledgements
M.M. thanks the Knight Foundation School of Computing & Information Sciences at Florida International University staff for their help and support.
Author information
Authors and Affiliations
Contributions
M.M. conceived the idea and fully developed the theory, developed the experiments on the optical table, wrote the complete manuscript, prepared figures, and reviewed the manuscript.
Corresponding author
Ethics declarations
Competing interests
The author declares no competing interests.
Additional information
Publisher's note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary Information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article's Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Mastriani, M. Simplified entanglement swapping protocol for the quantum Internet. Sci Rep 13, 21998 (2023). https://doi.org/10.1038/s41598-023-49326-4
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-023-49326-4
This article is cited by
-
Explaining the results of quantum mechanics via entanglement closed loop
Optical and Quantum Electronics (2024)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.