Abstract
The entangled network structure of the quantum Internet formulates a high complexity routing space that is hard to explore. Scalable routing is a routing method that can determine an optimal routing at particular subnetwork conditions in the quantum Internet to perform a high-performance and low-complexity routing in the entangled structure. Here, we define a method for routing space exploration and scalable routing in the quantum Internet. We prove that scalable routing allows a compact and efficient routing in the entangled networks of the quantum Internet.
Similar content being viewed by others
Introduction
Quantum information and quantum computations1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19 will not only reformulate our view of the nature of computation and communication, but will also open new possibilities for realizing high-performance computer architectures and telecommunication networks10,11,12,13,14,15,16,17,28,29,30,31,33,34,45,62,63,77. Since our traditional data will no longer remain safe in the traditional Internet when quantum computers become available, there will be a need for a fundamentally different network structure: the quantum Internet20,21,22,23,25,26,27,29,30.
In a quantum Internet scenario20,21,22,23,24,25,26,27,28,29,30,31,43,44,45,46,47,48,49,50,51,52,53,55,56,61,78,79,80, a primary task is to distribute quantum entanglement54,81,82,83,84,85,86,87,88,89,90,91,92,93,94,95,96,97,98 from a source quantum node to a target quantum node through a set of intermediate quantum nodes called quantum repeaters32,99,100,101,102,103,104,105,106,107,108,109,110,111,112. The entanglement distribution is realized in a step-by-step manner by the generation of short-distance entangled connections between quantum nodes. Next, the level of entanglement of the entangled connections is increased to generate longer-distance entangled connections. The entanglement level of an entangled connection determines the hop-distance (number of quantum nodes spanned by the particular entangled connection) between a source node and the target node of the given entangled connection. The level increment is realized by the so-called entanglement swapping (entanglement extension) procedure applied in the intermediate quantum repeaters. Specifically, the entanglement distribution is achieved within the framework of the so-called doubling architecture28,43,44, where each increment of the level of entanglement doubles the hop-distance. Using the entanglem ent distribution procedure, the distant source node and the target node can share a long-distance entangled connection.
The entangled quantum network structure integrates several entangled paths between a distant source and destination quantum nodes. In a general Internet setting with several legal and transmit users, numerous entangled paths exist in parallel, so the quantum repeaters must process all paths simultaneously. The properties of the entangled paths, along with the internal and external attributes of quantum repeaters (quantum memory usage, auxiliary internal processes and communication between quantum repeaters), formulate an abstracted space, called the routing space, of the quantum Internet. Due to the complex mechanisms of the quantum Internet and to the large number of variables associated with modelling these processes, an efficient method for exploring the routing space of the quantum Internet is essential for high-performance and high-efficiency routing.
A fundamental problem in the quantum Internet is that while routing methods for finding the shortest path in a quantum network are available28,43,44,46,47,48,49,53, a mathematical model for the working mechanism of the quantum repeaters in the quantum Internet is still missing. While the shortest paths can be determined only with respect to the cost function associated with the quantum links, these models omit the service capabilities and processes of quantum repeaters, which represent a bottleneck in experimental settings. As a corollary, a comprehensive and exhaustive model is required for the description of entanglement distribution and the construction of entangled paths.
Another issue is the lack of scalable routing in the quantum Internet. Scalable routing refers to a routing method that can determine the most appropriate routing mechanism of a particular subnetwork of the quantum Internet. Specifically, scalable routing can decide whether deterministic routing or adaptive routing would be optimal for a given subnetwork. In deterministic routing, the paths between a subset of quantum repeaters are fixed, while in adaptive routing, the paths are selected dynamically in an adaptive manner according to the actual status of the network. The main advantage of deterministic routing is a more compact and faster realization, since it requires no further path selection in a particular subnetwork. However, this is not generally applicable to the whole quantum Internet due to the dynamically changing conditions. However, performance improvement in the quantum Internet is possible if deterministic routing remains are applied in a particular set of subnetworks while quantum network adaptive routing is applied in the remaining parts. Thus, a scaled routing in the quantum Internet would have a more compact structure and be more efficient for path selection in the entangled network.
Here, we define a method for routing space evaluation and for scalable routing in the quantum Internet. The routing space evaluation integrates the derivation of the external and internal characteristics of quantum repeaters and compacts them into a term called the service rate of quantum repeaters. The scalable routing method utilizes the results of routing space exploration to decompose the quantum Internet into subnetworks with deterministic and adaptive routing between the quantum repeaters of the subnetwork. By utilizing the fundaments of queueing theory113,114,115, we define mathematical models for the service rate evaluation of quantum repeaters and entangled paths in the quantum Internet. The routing space exploration method utilizes the developed mathematical models to formulate the routing space that integrates the characteristics of the available paths, the service rates of quantum repeaters and the path service rates between the legal users of the network. Scalable routing results in more efficient routing overall, since it decreases the routing complexity and utilizes the available resources of the quantum Internet more conveniently than does unscaled routing.
The novel contributions of our manuscript are as follows:
- 1.
We define a mathematical model for the service rate evaluation of quantum repeaters and entangled quantum paths in the quantum Internet.
- 2.
We propose a method for routing space exploration of the quantum Internet.
- 3.
We conceal a method for scaled routing in the quantum Internet with deterministic and adaptive routing in the subnetworks.
- 4.
The methods fuse the fundamentals of queueing theory and the theory of quantum networking and entangled networks.
This paper is organized as follows. “System model and problem statement” section presents the system model and the problem statement. “Service rate of a quantum repeater” section defines the service rate evaluation model. “Service rate of a quantum repeater” section proves the evaluation of the service rate of an entangled path. “Routing space exploration and scalable routing” section provides the routing space exploration and scalable routing method. Finally, “Conclusions” section concludes the results. Supplemental information is included in the Appendix.
System model and problem statement
System model
The quantum Internet setting is modeled as follows46. Let V refer to the nodes of an entangled quantum network N, with a transmitter quantum node \(A\in V\), a receiver quantum node \(B\in V\), and quantum repeater nodes \(R_i\in V\), \(i=1,\ldots ,q\). Let \(E=\left\{ E_j\right\} \), \(j=1,\ldots ,m\), refer to a set of edges between the nodes of V, where each \(E_j\) identifies an \({\text {L}}_l\)-level entangled connection, \(l=1,\ldots ,r\), between quantum nodes \(x_j\) and \(y_j\) of edge \(E_j\), respectively. The entanglement levels of the entangled connections in the entangled quantum network structure are defined as follows.
Entanglement levels in the quantum Internet
In a quantum Internet setting, an \(N=\left( V,E\right) \) entangled quantum network consists of single-hop and multi-hop entangled connections, such that the single-hop entangled nodes (The l-level entangled nodes x, y refer to quantum nodes x and y connected by an entangled connection \({{\text {L}}_l}\).) are directly connected through an \({\text {L}}_1\)-level entanglement, while the multi-hop entangled nodes communicate through \({\text {L}}_l\)-level entanglement. Focusing on the doubling architecture28,29,30 in the entanglement distribution procedure, the number of spanned nodes is doubled in each level of entanglement swapping (entanglement swapping is applied in an intermediate node to create a longer distance entanglement28). Therefore, the \(d{\left( x,y\right) }_{{\text {L}}_l}\) hop distance in N for the \({\text {L}}_l\)-level entangled connection between \(x,y\in V\) is denoted by37,46
with \(d{\left( x,y\right) }_{{\text {L}}_l}-1\) intermediate quantum nodes between x and y. Therefore, \(l=1\) refers to a direct entangled connection between two quantum nodes x and y without intermediate quantum repeaters, while \(l>1\) identifies a multilevel entanglement.
Entanglement fidelity
Let
be the target Bell state subject to be created at the end of the entanglement distribution procedure between a particular source node A and receiver node B. The entanglement fidelity F at an actually created noisy quantum system \(\sigma \) between A and B is
where F is a value between 0 and 1, \(F=1\) for a perfect Bell state and \(F<1\) for an imperfect state28,30,37.
Routing space
Definition 1
The \({{\mathrm{S}}}_{\mathfrak {R}} \) routing space of N is defined as
where \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \) is an entangled path between source user \(A_{i} \) and destination user \(B_{i} \), \(i=1,\ldots ,K\), where K is the total number of entangled paths in the quantum network N.
An entangled path \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \) is characterized as
where \(S_{A_{i} \rightarrow B_{i} } \) is the service rate of \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \) defined as
where \(S\left( A_{i} \right) \) is the service rate of source \(A_{i} \), \(S\left( R_{p} \right) \) is the service rate of the p-th quantum repeater in path \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \), \(p=1,\ldots ,q\), q is the total number of quantum repeaters in \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \) [the service rate will be defined in (13)]; \(\gamma _{i} \), \(\gamma _{i} \le 0\) is the service rate fluctuation of \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \) defined as
where \(\gamma \left( x\right) \) of a particular quantum node x will be defined in (48), \(\Omega _{i} \) is the number of available \({{\mathscr {R}}}\) routes in the quantum Internet for the entanglement distribution from \(A_{i} \) to \(B_{i} \), while \({{\mathscr {S}}}\left( \Omega _{i} \right) \) is a set of the \(\Omega _{i} \) available routes for \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \), as
where \({{\mathscr {R}}}_{k}^{i} \) is the k-th available route with \(S_{A_{i} \rightarrow B_{i} } \) and \(\gamma _{i} \), with a shortest route \({{\mathscr {R}}}_{*}^{i} \)
Assuming a doubling architecture for the entanglement distribution, an entangled path \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \) consists of \(\left| {{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \right| \) nodes as
where \(d\left( A,B\right) _{{{\mathrm{L}}}_{l} } =2^{l-1} \) is the hop-distance between A and B at an l-level entangled connection \(L_{l} \left( A,B\right) \) between A and B.
Cycle
Definition 2
A cycle C with cycle-time \({{t}_{C}}={1}/{{{f}_{C}}} \,{\hbox {s}}\) is set via an oscillator \(O_{C} \) with frequency \({{f}_{C}}={1}/{{{t}_{C}}}\) in the quantum nodes used for synchronization of a quantum network.
From Definition 2, sC cycles identify \(s{{t}_{C}}={s}/{{{f}_{C}}} \,{\hbox {s}}\), where s is a nonzero real number.
Problem statement
The problem statement is given in Problems 1–3.
Problem 1
Determine the \(S\left( R\right) \)service rate of all quantum repeaters of the quantum network at a given set of incoming and outcoming entangled connections.
Problem 2
Evaluate the \(S\left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) \)service rate of an entangled path in the quantum Internet between distant source quantum nodes A and B.
Problem 3
Define the routing space of the quantum Internet (available paths, service rates of quantum repeaters and service rates of the paths). Determine a scaled routing method with deterministic and adaptive routing in particular subnetworks of the quantum Internet.
Service rate of a quantum repeater
By utilizing the fundamentals of queueing theory on priority queueing and quantum Shannon theory, we define the service rate of a quantum repeater as follows113,114,115. The system model utilizes a G/G/1 priority queueing model (also referred to as single-server queue with first-in-first-out serving in queueing theory)113 for the service rate evaluation of a particular quantum repeater in the quantum Internet. In the proposed G/G/1 setting, the service rates (measured in Bell states per C) and the inverse incoming entanglement throughput values (measured in C per Bell states) are independent and identically distributed with a general distribution.
Theorem 1 derives the closed-form service rate of a quantum repeater in a G/G/1 setting.
Theorem 1
(Closed-form service rate of a quantum repeater in a G/G/1 setting) The \(S\left( R_{i} \left( l_{j},l_{k} \right) \right) \) service rate of an i-th quantum repeater \(R_{i} \) can be expressed in a closed-form in a G/G/1 setting, where \(l_{j} \) is an incoming entangled connection of \(R_{i} \), while \(l_{k} \) is the outcoming entangled connection of \(R_{i} \).
Proof
The aim of the proof is to derive the \(S\left( R_{i} \left( l_{j} ,l_{k} \right) \right) \) service rate of \(R_i\) in a closed-form. Let \(R_{i} \left( {{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) ,l_{k} \right) \) refer to an i-th quantum repeater node \(R_{i} \) with a set \({{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) \) of p input entangled connections,
and an output entangled connection \(l_{k} \).
Then, let \(S\left( R_{i} \left( l_{j},l_{k} \right) \right) \) be the service rate (measured in Bell states per C cycle) of \(R_{i} \) with incoming entangled connection \(l_{j} \) and outcoming entangled connection \(l_{k} \); let \(B_{F} \left( l_{k} \right) \) be the entanglement throughput (The \(B_{F}\) entanglement throughput identifies the number of Bell states per cycle of a particular entanglement fidelity F.), measured in Bell states per cycle, of the output entangled connection \(l_{k} \) of \(R_{i} \).
The optimization problem can be evaluated as a maximization,
where \(S\left( A\left( l_{k} \right) \right) \) is the service rate of source node A with outcoming entangled connection \(l_{k} \).
Then, by using the G/G/1 priority queueing model, the \(S\left( R_{i} \left( l_{j},l_{k} \right) \right) \) service rate for a quantum repeater \(R_{i} \left( l_{j},l_{k} \right) \) with a given \({{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) \ne \emptyset \) is defined in a closed-form as
where
while \(\left| B_{F}^{in} \left( l_{j} \right) \right| \) is the number of incoming entangled states (measured in Bell states) in the input entangled connection \(l_{k} \) of \(R_{i} \), \({{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) \in {{\mathscr {P}}}\left( A\rightarrow B\right) \) refers to the situation if the input of \(R_{i} \) is from a previous node \(R_{h} \) such that \(R_{h} \in {{\mathscr {P}}}\left( A\rightarrow B\right) \), and where \({{\mathscr {P}}}\left( A\rightarrow B\right) \) is a main path between A and B, and \({{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) \in R_{h} \notin {{\mathscr {P}}}\left( A\rightarrow B\right) \) refers to the case if the input of \(R_{i} \) is from a previous node \(R_{h} \) such that \(R_{h} \) is not part of the main path, \(R_{h} \notin {{\mathscr {P}}}\left( A\rightarrow B\right) \).
The terms of \(S\left( R_{i} \left( l_{j},l_{k} \right) \right) \) are explained as follows.
The quantity \(\alpha _{k} \left( R_{i} \right) \) is ratio that models the unavailability of the \(l_{k} \) of output \(R_{i} \) as
where \(\mu \left( B_{F} \left( l_{k} \right) \right) \) is the average entanglement throughput of output entangled connection \(l_{k} \) of \(R_{i} \), \(\mu \left( B_{F} \left( l_{j} \rightarrow l_{k} \right) \right) \) is the average entanglement throughput of the input entangled connection \(l_{j} \), \(l_{j} \in {{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) \), \(j=1,\ldots ,\left| {{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) \right| \), \(\left| {{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) \right| \) is the cardinality of \({{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) \), \(\chi _{in}^{2} \left( R_{i} \right) \) is the coefficient of variation113,114,115 for the Z inverse of the \(\omega _{k} \left( R_{i} \right) \) sum of average entanglement throughput of all incoming entangled connections of connection \(l_{j} \) in \(R_{i} \) (measured in C per Bell states), as
where
thus
where \({\bar{Z}}\) is the average of Z,
where \(g=1\) if \({{\mathscr {S}}}_{l_{in} } \left( R_{i} \right) \in {{\mathscr {P}}}\left( A\rightarrow B\right) \), while \(\left\langle Z^{2} \right\rangle \) is the average of \(Z^{2} \) as
The term \(\omega _{k} \left( R_{i} \right) \) in (17) can be rewritten via (15) weighted by the ratio of (15) as
Then, \(\chi _{in}^{2} \left( R_{i} \right) \) can be set as a constant113,114,115 for all quantum repeaters, \(\chi _{in}^{2} \left( R_{i} \right) =\chi _{in}^{2} \left( R\right) \), for \(\forall R_{i} \).
The term \(\chi ^{2} \left( C\left( M\left( R_{i} \left( l_{k} \right) \right) \right) \right) \) is the coefficient of variation113,114,115 of cycles \(C\left( M\left( R_{i} \left( l_{k} \right) \right) \right) \), where \(C\left( M\left( R_{i} \left( l_{k} \right) \right) \right) \) characterizes the cycles of the \(M\left( R_{i} \left( l_{k} \right) \right) \) internal processes of \(R_{i} \) (quantum memory usage, error correction, purification, etc), will be defined in (37). These cycles reduce the service rate through \(l_{k} \) of \(R_{i} \).
The term \(\mu \left( B_{F} \left( l_{j} \rightarrow l_{k} \right) \right) \) (average Bell states per C) can be rewritten as
where \(\mu \left( B_{F} \left( A\right) \right) \) is the average output entanglement throughput (Bell states per C) of source node A, \(\Pr \left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) \) is the probability that a source A and a target B are connected an entangled path \({{\mathscr {P}}}\left( A\rightarrow B\right) \),
while \({{\mathscr {R}}}\left( AB,R_{i} \left( l_{j},l_{k} \right) \right) \) is a routing function defined as
thus the routing function in (24) therefore equals to 1, if quantum repeater \(R_{i} \left( l_{i},l_{k} \right) \) is part of the path \({{\mathscr {P}}}\left( A\rightarrow B\right) \), and 0 otherwise.
The \(\Phi \left( R_{i} \left( l_{j},l_{k} \right) \right) \) inverse of the service rate \(S\left( R_{i} \left( l_{j},l_{k} \right) \right) \) [see (13)] of \(R_{i} \left( l_{j},l_{k} \right) \) (measured in C per Bell states) is defined as
Using (25), the \(f\left( {{\mathscr {P}}}\right) \) objective function subject to a minimization (While the objective function in (12) subject to a maximization utilizes the service rate formula of (13) derived via the G/G/1 priority queueing model, the objective function in (26) utilizes the inverse of (13) and defines a minimization problem.) can be written as
The validation of the formula of (13) is as follows.
It can be verified114,115, that \(\Phi \left( R_{i} \left( l_{j},l_{k} \right) \right) \) [see (25)] can be decomposed as
where \(\varsigma \left( R_{i} \left( l_{j},l_{k} \right) \right) \) is defined as a ratio of incoming and outcoming entanglement throughputs
while \(\psi _{k} \left( R_{i} \right) \) is the number of residual cycles (measured in C cycles) defined via (28) as
where \(\chi _{in}^{2} \left( R_{i} \right) \) is given in (18).
The sum of \(\sum _{j=1}^{g}\varsigma \left( R_{i} \left( l_{j},l_{k} \right) \right) \) in (29) can be rewritten via (15) as
where \(\omega _{k} \left( R_{i} \right) \) is as given in (21).
As follows, (29) can be rewritten as
Thus, using (31), the term in (27) can be rewritten as given in (25), and as a corollary, the formula of (13) is validated.
Next, let study the case if there are multiple possible output paths are available for a given incoming entangled connection. Let \(R_{h} \) be a source neighbor node of \(R_{i} \), \(R_{h} \in {{\mathscr {P}}}\left( A,B\right) \) associated with an incoming entangled connection \(l_{j} \) of \(R_{i} \), and let us assume that \(R_{i} \) has \(\left| {{\mathscr {S}}}_{l_{out} } \left( R_{i} \right) \right| \) outcoming entangled connections, where \({{\mathscr {S}}}_{l_{out} } \left( R_{i} \right) \) is the set of r output entangled connections of \(R_{i} \), \({{\mathscr {S}}}_{l_{out} } \left( R_{i} \right) =\left( l_{out,1},\ldots ,l_{out,r} \right) \).
Using (13), the \(\mu \left( S\left( R_{h} \left( l_{k} \right) \right) \right) \) average service rate for the output entangled connection \(l_{k} \) of a particular \(R_{h} \) from set \({{\mathscr {S}}}_{S} \left( R_{i} \right) \) can be evaluated as
where \(\theta \left( R_{h} \left( l_{k} \right) \right) \) is the first moment of \(C\left( M\left( R_{h} \left( l_{k} \right) \right) \right) \) defined as
where \(\Phi \left( R_{i} \left( l_{j},l_{k} \right) \right) \) is evaluated via (27), and \(\Pr \left( R_{i} \left( l_{j} \rightarrow l_{k} \right) \right) \) is the probability that an incoming entangled state from \(l_{j} \) of \(R_{i} \) is distributed through the output \(l_{k} \) of \(R_{i} \), evaluated as
where \(\omega _{k} \left( R_{i} \right) \) is defined in (21); term \(d\left( R_{i} \right) \) is the sum of additional internal and external C cycles related to \(R_{i} \), as
where \(C\left( \Delta \left( R_{h},R_{i} \right) \right) \) is an external term associated to the \(\Delta \left( R_{h},R_{i} \right) \) transmission process between nodes \(R_{h} \) and \(R_{i} \), while \(\zeta \left( R_{i} \right) \) identifies the cycles of usage of the internal quantum memory of \(R_{i} \), as
where \(\left| {{\mathscr {M}}}\left( R_{i} \left( l_{j} \right) \right) \right| \) is the number of entangled states received from \(l_{j} \) and stored in the quantum memory \({{\mathscr {M}}}\) of \(R_{i} \), \(\left| {{\mathscr {M}}}\left( R_{i} \left( l_{k} \right) \right) \right| \) is the number of entangled states readout from the quantum memory \({{\mathscr {M}}}\) of \(R_{i} \) and distributed through connection \(l_{k} \).
Then, the \(\chi ^{2} \left( C\left( M\left( R_{h} \left( l_{k} \right) \right) \right) \right) \) coefficient of variation113,114,115 from \(\theta \left( R_{h} \left( l_{k} \right) \right) \) [see (33)] can be evaluated as
where \(\nu \left( R_{h} \left( l_{k} \right) \right) \) is the second moment of \(C\left( M\left( R_{h} \left( l_{k} \right) \right) \right) \), as
Then, using (37), the term \(\Phi \left( R_{h} \left( l_{k} \right) \right) \) can be evaluated via (25).
The proof is concluded here. □
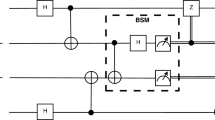
Figure 1 depicts the proposed system model for the service rate evaluation of a quantum repeater.
A network situation in a quantum Internet setting with an i-th quantum repeater \(R_i\) with service rate \(S\left( R_i\left( l_j,l_k\right) \right) \) in a main path \({\mathscr {P}}\left( A\rightarrow B\right) \) between a source quantum node A and receiver quantum node B. The previous neighbour of \(R_i\) is \(R_h\) and the next neighbour of \(R_i\) is \(R_j\). The \(R_i\) node has an incoming entangled connection \(l_j\) from the main path with \(\left| B^{in}_F\left( l_j\right) \right| \) incoming Bell states, and with \(\left| {{\mathscr {S}}}_{l_{in}}\left( R_i\right) \right| -1\) other incoming entangled connections from other nodes, where \(\left| {{\mathscr {S}}}_{l_{in}}\left( R_i\right) \right| \) is the number of incoming entangled connections and an outcoming entangled connection \(l_k\). The entangled connections have different l levels of entanglement (depicted by different colours: the entangled connections of the main path are denoted by red arrows). A C cycle in the quantum network is set via an \(O_C\) oscillator in the quantum nodes (depicted by a dashed grey line), \(t_C={1}/{f_C}\), at a particular oscillator frequency \(f_C\).
Service rate of entangled paths
Theorem 2 derives the closed-form service rate of an entangled path in a G/G/1 setting, at a doubling architecture.
Theorem 2
(Closed-form service rate of an entangled path) The \(S\left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) \) service rate of an entangled path \({{\mathscr {P}}}\left( A\rightarrow B\right) \) between distant quantum nodes A and B at a doubling architecture is \(S\left( {\mathscr {P}}\left( A\rightarrow B \right) \right) ={1}/{\left( {{\Phi }_{l=1}}\left( A,{{R}_{1}} \right) +\sum \nolimits _{i=2}^{q-2}{{{\Phi }_{l=1}}\left( {{R}_{i}},{{R}_{i+1}} \right) }+{{\Phi }_{l=1}}\left( {{R}_{q}},B \right) +\Upsilon \left( {{U}_{swap}} \right) \right) }\), where q is the total number of quantum repeaters in \({{\mathscr {P}}}\left( A\rightarrow B\right) \), \(\Phi _{l=1} \left( x,y\right) =\Phi \left( x\right) +\Phi \left( y\right) +C\left( M\left( x\right) \right) +C\left( M\left( y\right) \right) +C\left( \Delta \left( x,y\right) \right) \), x and y are \(l=1\) level entangled source and target quantum nodes connected by \({{\mathrm{L}}}_{1} \left( x,y\right) \), while \(\Upsilon \left( U_{swap}\right) \) is the service rate decrement in the entanglement distribution caused by the \(U_{swap}\) entanglement swapping operation.
Proof
Let \(R_{S} \) and \(R_{D} \) be two quantum repeaters connected by an \(l=1\) level entangled connection \({{\mathrm{L}}}_{1} \left( x,y\right) \), with service rates \(S\left( {{R}_{S}} \right) \) and \(S\left( {{R}_{D}} \right) \) determined via Theorem 1.
Then, the \(S_{l=1} \left( R_{S},R_{D} \right) \) service rate between \(R_{S} \) and \(R_{D} \) is as
where term \(\xi \left( R_{S},R_{D} \right) \le 0\) refers to service rate degradation, defined as
where the simplified notations of \(\Phi \left( R_{i} \right) \) and \(C\left( M\left( R_{i} \right) \right) \) are used for \(\Phi \left( R_{i} \left( l_{j},l_{k} \right) \right) \) and \(C\left( M\left( R\left( l_{k} \right) \right) \right) \), respectively.
Let assume that N is utilized via the doubling architecture, with hop-distance \(d\left( x,y\right) _{{{\mathrm{L}}}_{l} } =2^{l-1} \) for an \({{\mathrm{L}}}_{l} \)-level entangled connection between quantum nodes x and y. Then, for a source A and destination B, the entanglement distribution process and the generation of the \({{\mathscr {P}}}\left( A\rightarrow B\right) \) entangled path is characterized via the \(S\left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) \) service rate (The formula of (41) assumes a path in a doubling architecture with a source node A, destination node B, and with q intermediate quantum repeaters. The formula defines the inverse of the sum of service rate inverses—service rate inverse is given in (25)—taken for the total \(q+2\) nodes of the path, amended by a \(\Upsilon \left( U_{swap}\right) \) residual quantity (42) that identifies a service rate decrement caused by entanglement swapping in the nodes.), as
where q is the total number of quantum repeaters of \({{\mathscr {P}}}\left( A\rightarrow B\right) \), \(q-2\) is the total number of intermediate quantum repeater pairs on the path excluding the boundary nodes, \(\Upsilon \left( U_{swap}\right) \) is the service rate decrement (measured in C cycles) in the entanglement distribution caused by the \(U_{swap}\) entanglement swapping operations
where \(n_{swap} \) is the number of entanglement swapping operations required for an \({{\mathrm{L}}}_{l} \)-level entangled connection between distant A and B,
while \(C\left( R_{i}^{swap} \right) \) is the cycles required for the entanglement swapping an i-th swapping quantum repeater \(R_{i}^{swap} \). □
Path service rate algorithm
Using (41), a cumulative service rate \(S_{\Sigma } \left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) \) can be evaluated for all source A and destination B in the network N as
where \(\Pr \left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) \) is the probability of an entangled path \({{\mathscr {P}}}\left( A\rightarrow B\right) \) between A and B, and \(\sum _{A}\sum _{B}\Pr \left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) =1 \).
The steps are detailed in Algorithm 1. The algorithm utilizes the proposed system parameterization for a given path \({{\mathscr {P}}}\left( A\rightarrow B\right) \) between source node A and target node B, with q intermediate quantum repeaters. The algorithm evaluates \(\mu \left( B_{F} \left( l_{i} \rightarrow l_{k} \right) \right) \) via (22), the coefficient \(\omega _{k} \left( R_{j} \right) \) via (21), determines \(\Pr \left( l\left( R_{i} \left( l_{j} \right) , R_{i} \left( l_{k} \right) \right) \right) \) via (34), evaluates \(\theta \left( R_{j} \left( l_{k} \right) \right) \) via (33), \(\nu \left( R_{j} \left( l_{k} \right) \right) \) via (38), and \(\chi ^{2} \left( M\left( R_{i} \left( l_{j},l_{k} \right) \right) \right) \) via (37), along with the determination of the cycle reduction via the usage of the internal quantum memory \(\varsigma \left( R_{i} \left( l_{j} ,l_{k} \right) \right) \) by (28), and \(\psi _{k} \left( R_{i} \right) \) via (29). Finally, the \(S\left( R_{i} \left( l_{j},l_{k} \right) \right) \) service rates of node \(R_{i} \) with incoming entangled connection \(l_{j} \) and outcoming entangled connection \(l_{k} \) are determined using (13) for all nodes of the path, and outputs \(S\left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) \) of the entangled path \({{\mathscr {P}}}\left( A\rightarrow B\right) \) via (41).
Algorithm 1 Service rate of a path | |
|---|---|
Input: Parameterization of path \({{\mathscr {P}}}\left( A\rightarrow B\right) \) between source node A and target node B, with q intermediate quantum repeaters. Output: Service rate \(S\left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) \) of \({{\mathscr {P}}}\left( A\rightarrow B\right) \). Step 1. Set the C cycle via oscillator \(O_{C} \) used in the quantum nodes of the quantum network N. Step 2. Parameterize the quantum network via \(\mu \left( B_{F} \left( A\right) \right) \), \(\chi _{in}^{2} \left( A\right) \), \(\Pr \left( l\left( A,B\right) \right) \) for a source node A and target node B, and via \(\mu \left( B_{F} \left( l_{k} \right) \right) \), and \(C\left( M\left( R_{i} \left( l_{k} \right) \right) \right) \) for an \(R_{i} \) i-th quantum repeater, \(i=1,\ldots ,q\). Step 3. Determine \(\mu \left( B_{F} \left( l_{i} \rightarrow l_{k} \right) \right) \) via (22), and \(\omega _{k} \left( R_{j} \right) \) via (21). Step 4. Evaluate \(\Pr \left( l\left( R_{i} \left( l_{j} \right) ,R_{i} \left( l_{k} \right) \right) \right) \) via (34). Step 5. Determine \(\theta \left( R_{j} \left( l_{k} \right) \right) \) via (33), \(\nu \left( R_{j} \left( l_{k} \right) \right) \) via (38), and \(\chi ^{2} \left( M\left( R_{i} \left( l_{j},l_{k} \right) \right) \right) \) via (37). Step 6. Evaluate the cycle reduction via the usage of the internal quantum memory \(\varsigma \left( R_{i} \left( l_{j},l_{k} \right) \right) \) by (28), and \(\psi _{k} \left( R_{i} \right) \) via (29). Step 7. Compute the \(S\left( R_{i} \left( l_{j},l_{k} \right) \right) \) service rate of node \(R_{i} \) with incoming entangled connection \(l_{j} \) and outcoming entangled connection \(l_{k} \) via (13). Step 8. Output \(S\left( {{\mathscr {P}}}\left( A\rightarrow B\right) \right) \) of the entangled path \({{\mathscr {P}}}\left( A\rightarrow B\right) \) via (41). |
Routing space exploration and scalable routing
Theorem 3 derives the optimal routing for the subnetworks, using the closed-form service rate formulas of Theorems 1–2. The derivations utilize a G/G/1 setting and a doubling architecture.
Theorem 3
(Scalable routing in the quantum Internet) An \({{\mathscr {R}}}_{S} \left( N\right) \) scaled routing function for the quantum Internet can be determined as \({{\mathscr {R}}}_{S} \left( N\right) =p_{d} {{\mathscr {R}}}_{d} +p_{a} {{\mathscr {R}}}_{a}\), where \({{p}_{d}}={\left| {{{\mathscr {S}}}_{{{{\mathscr {R}}}_{d}}}} \right| }/{\left| {{V}_{R}} \right| }\) and \({{p}_{a}}={\left| {{{\mathscr {S}}}_{{{{\mathscr {R}}}_{a}}}} \right| }/{\left| {{V}_{R}} \right| }\) are the probabilities of \({{\mathscr {R}}}_{d} \) deterministic routing and \({{\mathscr {R}}}_{a} \) adaptive routing in the network N, \(p_{a} +p_{d} =1\), while \(\left| V_{R} \right| =\left| {{\mathscr {S}}}_{{{\mathscr {R}}}_{a} } \right| +\left| {{\mathscr {S}}}_{{{\mathscr {R}}}_{d} } \right| \) and \(\left| \cdot \right| \) is the cardinality, \({{\mathscr {S}}}_{{{\mathscr {R}}}_{d} } \) is a set of subnetworks in which \({{\mathscr {R}}}_{d} \) deterministic routing can be applied, \({{\mathscr {S}}}_{{{\mathscr {R}}}_{d} } ={{\mathscr {S}}}_{{{\mathscr {R}}}_{d,1} } \bigcup \cdots \bigcup {{\mathscr {S}}}_{{{\mathscr {R}}}_{d,{{\mathscr {D}}}} } \), where \({{\mathscr {D}}}\) is the number of subsets, and \({{\mathscr {S}}}_{{{\mathscr {R}}}_{a} } \) is a set of subnetworks in which \({{\mathscr {R}}}_{a} \) adaptive routing can be applied, \({{\mathscr {S}}}_{{{\mathscr {R}}}_{a} } ={{\mathscr {S}}}_{{{\mathscr {R}}}_{a,1} } \bigcup \cdots \bigcup {{\mathscr {S}}}_{{{\mathscr {R}}}_{a,{{\mathscr {A}}}} }\), where \({{\mathscr {A}}}\) is the number of subsets.
Proof
The proof includes a predictive method for routing space exploration in the quantum Internet. The method utilizes the properties of the quantum nodes, such as transmission between the nodes, and also integrates an updating mechanism motivated by machine learning approaches116,117,118 to find the highest service rate path in the quantum network. The scalable routing function is derived via Algorithm 2.
Let A and B be the source and target quantum nodes. Then, let \(S\left( R_{i} \right) \) refer to the service rate of \(R_{i} \) as defined in (13). Let \(R_{j} \) be a neighbor node connected by an entangled connection with \(R_{i} \), and let \(R_{k} \) be a next neighbor of \(R_{j} \), with service rates \(S\left( R_{j} \right) \) and \(S\left( R_{k} \right) \), respectively.
Let \(R_{j} \left( W_{R_{k} \rightarrow B} \right) \) be the maximal weighted service rate \(S_{R_{k} \rightarrow B} \) from the k-th quantum repeater to the destination B evaluated in the j-th node \(R_{j} \), as
where \({{\mathscr {S}}}_{N} \left( R_{j} \right) \) is the set of next (i.e., toward destination) quantum nodes that share entangled connection with \(R_{j} \), \(R_{k} \in {{\mathscr {S}}}_{N} \left( R_{j} \right) \), while \(W_{R_{n} \rightarrow B} \) is the weighted service rate from \(R_{n} \) to B, defined as
where \(V_{R_{n} \rightarrow B} \) is the number of quantum repeaters of path \({{\mathscr {P}}}\left( R_{n} \rightarrow B\right) \) from \(R_{n} \) to B, defined as
where \(\left| {{\mathscr {P}}}\left( R_{n} \rightarrow B\right) \right| \) is refers to the total number of nodes of path \({{\mathscr {P}}}\left( R_{n} \rightarrow B\right) \), while \(\gamma \left( R_{p} \right) \le 0\) is the entanglement throughput reduction associated with \(R_{p} \), defined as
where \(C\left( \Delta \left( R_{p},R_{p+1} \right) \right) \) is a delay between \(R_{p} \) and \(R_{p+1} \), (\(R_{V_{R_{n} \rightarrow B} +1} =B\)); in (48) the simplified notations of \(\Phi \left( R_{i} \right) \) and \(C\left( M\left( R_{i} \right) \right) \) are used for \(\Phi \left( R_{i} \left( l_{j},l_{k} \right) \right) \) and \(C\left( M\left( R\left( l_{k} \right) \right) \right) \), respectively.
By propagating backward (see Fig. 2) the value of \(R_{j} \left( W_{R_{k} \rightarrow B} \right) \) [see (45)] to node \(R_{i} \), node \(R_{i} \) can determine the estimation \({\mathbb {E}}\left( R_{i} \left( W_{R_{j} \rightarrow B} \right) \right) \) as (A backpropagation method is also used in Q-learning based routing methods117, 118.)
Using the side information available, an algorithm can be defined to determine the routing space of the quantum Internet. The details are given in Algorithm 2.
The proof concludes here. □
Figure 2 shows the procedure for determining the service rates of the paths. The initial path between an i-th quantum repeater \(R_{i} \) and the target node B is \({{\mathscr {P}}}^{\left( 0\right) } \left( R_{i} \rightarrow B\right) \).
Routing space exploration in the quantum Internet. This method evaluates the service rates of paths between a source quantum repeater \(R_{i} \) and target node B; \(\gamma \) is the entanglement throughput reduction associated with the nodes and coefficients \(\Omega \), \({{\mathscr {S}}}\left( \Omega \right) \) and \({{\mathscr {R}}}_{*} \) for a given \({{\mathscr {P}}}\left( A\rightarrow B\right) \). An i-th quantum repeater \(R_{i} \) has a next neighbour set \({{\mathscr {S}}}_{N} \left( R_{i} \right) \) (depicted by a cloud) with a set of neighbouring quantum repeaters. From each \({{\mathscr {S}}}_{N} \left( R_{i} \right) \), a particular quantum repeater \(R_{j} \) is selected such that the \(W_{R_{j} \rightarrow B} \) weighted service rate from \(R_{j} \) to B is maximized (the quantum repeaters of the initial path are depicted by green nodes). The \(R_{k} \left( W_{R_{k+1} \rightarrow B} \right) \) service rate information is backpropagated from \(R_{k} \) to \(R_{j} \) as side information, and \(R_{j} \left( W_{R_{k} \rightarrow B} \right) \) is backpropagated from \(R_{j} \) to \(R_{i} \) to update estimation \({\mathbb {E}}\left( R_{i} \left( W_{R_{j} \rightarrow B} \right) \right) \) (classical links are depicted by grey dashed lines).
Routing space exploration algorithm
Algorithm 2 utilizes local and nonlocal information for the determination of the service rate of a particular path. The algorithm uses the proposed service rates formulas of quantum nodes of N, and evaluates the related coefficients. The algorithm determines the \(W_{R_{i} \rightarrow B} \) maximized weighted service rate between \(R_{i} \) and B in an iterative manner. The algorithm also utilizes an \(\ell \) learning rate coefficient in the parameter updating mechanism. The algorithm evaluates \(S_{A\rightarrow B} \), \(\Omega \), \({{\mathscr {S}}}\left( \Omega \right) \) [see (8)] and \({{\mathscr {R}}}_{*} \) [see (9)] of path \({{\mathscr {P}}}\left( A\rightarrow B\right) \), for all paths \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \), \(i=1,\ldots ,K\). In the internal steps, it evaluates \(\gamma _{i} \) via (7), along with the number \(\Omega _{i} \) of available routes for \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \), determines \({{\mathscr {S}}}\left( \Omega _{i} \right) \) via (8), and \({{\mathscr {R}}}_{*}^{i} \) via in (9). Finally, the algorithm outputs the routing space \({{\mathrm{S}}}_{\mathfrak {R}} \left( N\right) \) via (4).
Algorithm 2 Routing space exploration | |
|---|---|
Input: Service rates of quantum nodes of N. Output: Routing space \({{\mathrm{S}}}_{\mathfrak {R}} \left( N\right) \) of N. Step 1. Let \(R_{i} \) and \(R_{j} \) be quantum repeaters with service rates \(S\left( R_{j} \right) \) and \(S\left( R_{k} \right) \) evaluated via (13) and let \({{\mathscr {P}}}^{\left( 0\right) } \left( R_{i} \rightarrow B\right) \) be an initial path from \(R_{i} \) to B with \(V_{R_{i} \rightarrow B} =\left| {{\mathscr {P}}}^{\left( 0\right) } \left( R_{i} \rightarrow B\right) \right| -1\) quantum repeaters. Set the \(R_{i}^{\left( 0\right) } \left( W_{R_{j} \rightarrow B} \right) \) initial value in \(R_{i} \) for the \(W_{R_{j} \rightarrow B} \) weighted service rate (46) from to \(R_{i} \) to B, as \(R_{i}^{\left( 0\right) } \left( W_{R_{j} \rightarrow B} \right) =W_{R_{j} \rightarrow B}^{\left( 0\right) }\), where \(W_{R_{j} \rightarrow B}^{\left( 0\right) } \) is the initial value of the weighted service rate in \(R_{i} \), as \(W_{R_{j} \rightarrow B}^{\left( 0\right) } =\sum _{p=1}^{V_{R_{j} \rightarrow B} }S^{\left( 0\right) } \left( R_{p} \right) +\gamma ^{\left( 0\right) } \left( R_{p} \right) \), and \(S^{\left( 0\right) } \left( R_{p} \right) \) is determined via (13), while \(\gamma ^{\left( 0\right) } \left( R_{p} \right) \) is via (48) for all quantum repeaters. Step 2. In \(R_{j} \), evaluate \(R_{j} \left( W_{R_{k} \rightarrow B} \right) \) via the maximization of (45) for all neighbors of \(R_{j} \),\(\forall R_{n} \in {{\mathscr {S}}}_{N} \left( R_{j} \right) \). Step 3. Propagate back \(R_{j} \left( W_{R_{k} \rightarrow B} \right) \) to \(R_{i} \), and update \(R_{i}^{\left( 0\right) } \left( W_{R_{j} \rightarrow B} \right) \) (50) via estimation \({\mathbb {E}}\left( R_{i} \left( W_{R_{j} \rightarrow B} \right) \right) \) (49) to \(R_{i} \left( W_{R_{j} \rightarrow B} \right) \) as \(R_{i} \left( W_{R_{j} \rightarrow B} \right) =R_{i}^{\left( 0\right) } \left( W_{R_{j} \rightarrow B} \right) +\ell \left( {\mathbb {E}}\left( R_{i} \left( W_{R_{j} \rightarrow B} \right) \right) -R_{i}^{\left( 0\right) } \left( W_{R_{j} \rightarrow B} \right) \right) \), where \({\mathbb {E}}\left( R_{i} \left( W_{R_{j} \rightarrow B} \right) \right) =R_{j} \left( W_{R_{k} \rightarrow B} \right) +\left( S\left( R_{j} \right) +\gamma \left( R_{j} \right) \right) ,\) and \(\ell \) is the learning rate, \(\ell \in \left[ 0,1\right] \). Step 4. Repeat step 3 to for all neighbors of \(R_{i} \), \(\forall R_{n} \in {{\mathscr {S}}}_{N} \left( R_{i} \right) \). Step 5. Output the \(W_{R_{i} \rightarrow B} \) maximized weighted service rate between \(R_{i} \) and B as \(W_{R_{i} \rightarrow B} =\mathop {\max }\limits _{R_{n} \in {{\mathscr {S}}}_{N} \left( R_{i} \right) } \left( R_{n} \left( W_{R_{j} \rightarrow B} \right) \right) \), where \(R_{n} \left( W_{R_{j} \rightarrow B} \right) \) is determined via (52). Step 6. Repeat the procedure until source node A to output \(S_{A\rightarrow B} \), \(\Omega \), \({{\mathscr {S}}}\left( \Omega \right) \) [see (8)] and \({{\mathscr {R}}}_{*} \) [see (9)] of path \({{\mathscr {P}}}\left( A\rightarrow B\right) \). Step 7. Repeat the steps for all paths \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \), \(i=1,\ldots ,K\). Determine \(\gamma _{i} \) via (7), the number \(\Omega _{i} \) of available routes for \({{\mathscr {P}}}\left( A_{i} \rightarrow B_{i} \right) \), \({{\mathscr {S}}}\left( \Omega _{i} \right) \) via (8), and \({{\mathscr {R}}}_{*}^{i} \) via in (9). Step 8. Output routing space \({{\mathrm{S}}}_{\mathfrak {R}} \left( N\right) \) via (4). | (50) (51) (52) (53) |
Routing scaling algorithm
Using the results of Algorithm 2 for determining the service rates of paths, the neighbouring quantum repeaters can be selected from each quantum repeater to establish scalable routing. The routing scaling algorithm uses the path service rate information to find the entangled path \({{\mathscr {P}}}^{*} \) with the highest weighted service rate \(W_{A\rightarrow B} \), and uses \({{\mathscr {R}}}_{d} \) deterministic routing if the service rate degradation coefficient \(\xi \left( R_{i},R_{j} \right) \) [see (40)] between a particular source and destination quantum repeater in \({{\mathscr {P}}}^{*} \) is below a critical threshold value \(\partial S^{*} \); otherwise, it uses \({{\mathscr {R}}}_{a} \) adaptive routing between the quantum nodes.
Algorithm 3 provides the steps of the routing scaling. The algorithm outputs a highest service path \({{\mathscr {P}}}^{*} \) with a scaled routing function \({{\mathscr {R}}}_{S} \left( N\right) \) for quantum network N. The algorithm utilizes the parameterized routing space \({{\mathrm{S}}}_{\mathfrak {R}} \left( N\right) \) of N outputted via Algorithm 2. As a main contribution of the algorithm, it evaluates \(S_{l=1} \left( R_{i},R_{j} \right) \) between \(R_{i} \) and \(R_{j} \) via (39) as \(S_{l=1} \left( R_{i},R_{j} \right) =S\left( R_{i} \right) +S\left( R_{j} \right) +\xi \left( R_{i} ,R_{j} \right) \), where \(S\left( R_{i} \right) \) and \(S\left( R_{j} \right) \) are determined via (13), while \(\xi \left( R_{i},R_{j} \right) \) is as in (40). Then, it makes a decision, using the relation of \(\left| \xi \left( R_{i} ,R_{j} \right) \right| <\partial S^{*} \). If the relation is true, then it sets a \({{\mathscr {R}}}_{d} \) deterministic routing between \(R_{i} \) and \(R_{j} \). Otherwise, the algorithm sets a \({{\mathscr {R}}}_{a} \) adaptive routing between \(R_{i} \) and \(R_{j} \). After some internal steps and calculations, the algorithm determines \({{\mathscr {P}}}^{*} \left( R_{S} \rightarrow R_{D} \right) \) for all \(R_{S} \) source and \(R_{D} \) destinations, and it establishes the selection of the appropriate routing method for all \(\left\{ R_{i},R_{j} \right\} \) quantum repeater pairs of path \({{\mathscr {P}}}^{*} \left( R_{S} \rightarrow R_{D} \right) \). Finally, the algorithm determines the appropriate routing mechanism for all sub-networks of the particular quantum Internet scenario.
Algorithm 3 Scalable routing in the quantum Internet | |
|---|---|
Input: Routing space \({{\mathrm{S}}}_{\mathfrak {R}} \left( N\right) \) of N. Output: \({{\mathscr {R}}}_{S} \left( N\right) \) routing scaling for the quantum network N. Step 1. Set a critical upper bound \(\partial S^{*} \ge 0\) on the service rate fluctuation in N. Assume that \(\Upsilon \left( U_{swap}\right) \) is constant for all swapping quantum repeaters (i.e., \(\Upsilon \left( U_{swap}\right) \) has no impact on routing). Step 2. Determine \(R_{j} \left( W_{R_{k} \rightarrow B} \right) \) and \(R_{i} \left( W_{R_{j} \rightarrow B} \right) \) in nodes \(R_{j} \) and \(R_{i} \) via Algorithm 2. Step 3. In \(R_{j} \), select a neighbour node \(R_{n} \) that maximizes \(R_{j} \left( W_{R_{k} \rightarrow B} \right) \) and set it as \(R_{n} =R_{k} \). In \(R_{i} \), select a neighbour node \(R_{n} \) that maximizes \(R_{i} \left( W_{R_{j} \rightarrow B} \right) \) and set it as \(R_{n} =R_{j} \). Step 4. Update the initial path \({{\mathscr {P}}}^{\left( 0\right) } \left( R_{i} \rightarrow B\right) \) to path \({{\mathscr {P}}}^{*} \left( R_{i} \rightarrow B\right) \) with the highest service rate (53) \(W_{R_{i} \rightarrow B} \) between \(R_{i} \) and B. Step 5. Compute \(S_{l=1} \left( R_{i},R_{j} \right) \) between \(R_{i} \) and \(R_{j} \) via (39) as \(S_{l=1} \left( R_{i},R_{j} \right) =S\left( R_{i} \right) +S\left( R_{j} \right) +\xi \left( R_{i},R_{j} \right) \), where \(S\left( R_{i} \right) \) and \(S\left( R_{j} \right) \) are determined via (13), while \(\xi \left( R_{i},R_{j} \right) \) is as in (40). Step 6. If \(\left| \xi \left( R_{i},R_{j} \right) \right| <\partial S^{*} \), then use \({{\mathscr {R}}}_{d} \) deterministic routing between \(R_{i} \) and \(R_{j} \). Step 7. If \(\left| \xi \left( R_{i},R_{j} \right) \right| \ge \partial S^{*} \), then use \({{\mathscr {R}}}_{a} \) adaptive routing between \(R_{i} \) and \(R_{j} \). Step 8. Repeat steps 5–7 for all \(\left\{ R_{i},R_{j} \right\} \) quantum repeater pairs of path \({{\mathscr {P}}}^{*} \left( R_{i} \rightarrow B\right) \). Step 9. Apply step 4 to find \({{\mathscr {P}}}^{*} \left( R_{S} \rightarrow R_{D} \right) \) for all \(R_{S} \) source and \(R_{D} \) destinations, and repeat step 8 for all \(\left\{ R_{i},R_{j} \right\} \) quantum repeater pairs of path \({{\mathscr {P}}}^{*} \left( R_{S} \rightarrow R_{D} \right) \). Step 10. Output sets \({{\mathscr {S}}}_{{{\mathscr {R}}}_{d} } ={{\mathscr {S}}}_{{{\mathscr {R}}}_{d,1} } \bigcup \cdots \bigcup {{\mathscr {S}}}_{{{\mathscr {R}}}_{d,{{\mathscr {D}}}} } \), and \({{\mathscr {S}}}_{{{\mathscr {R}}}_{a} } ={{\mathscr {S}}}_{{{\mathscr {R}}}_{a,1} } \bigcup \cdots \bigcup {{\mathscr {S}}}_{{{\mathscr {R}}}_{a,{{\mathscr {A}}}} } \), where \({{\mathscr {D}}}\) and \({{\mathscr {A}}}\) are the number of subsets of quantum nodes for which \({{\mathscr {R}}}_{d} \) and \({{\mathscr {R}}}_{a} \) routing functions can be applied in N. Output the \({{\mathscr {R}}}_{S} \left( N\right) \) scaled routing function for the quantum network N as \({{\mathscr {R}}}_{S} \left( N\right) =p_{d} {{\mathscr {R}}}_{d} +p_{a} {{\mathscr {R}}}_{a}\), where \({{p}_{d}}={\left| {{{\mathscr {S}}}_{{{{\mathscr {R}}}_{d}}}} \right| }/{\left| {{V}_{R}} \right| }\) and \({{p}_{a}}={\left| {{{\mathscr {S}}}_{{{{\mathscr {R}}}_{a}}}} \right| }/{\left| {{V}_{R}} \right| }\) are the probabilities of deterministic and adaptive routing in the network, \(p_{a} +p_{d} =1\), while \(\left| V_{R} \right| =\left| {{\mathscr {S}}}_{{{\mathscr {R}}}_{a} } \right| +\left| {{\mathscr {S}}}_{{{\mathscr {R}}}_{d} } \right| \) and \(\left| \cdot \right| \) is the cardinality. | (54) |
Deterministic and adaptive routing
In a \({{\mathscr {R}}}_{d} \) deterministic routing between \(R_{i} \) and \(R_{j} \), the shortest path \({{\mathscr {P}}}^{*} \left( R_{i} \rightarrow R_{j} \right) \) is fixed such that \(R_{j} \) is always selected as the neighbouring node of \(R_{i} \) from the set \({{\mathscr {S}}}_{N} \left( R_{i} \right) \) of possible neighbours in \(R_{i} \) (A shortest path is selected with respect to a particular cost function, in our setting the cost function of the path selection is the inverse of \(W_{R_{i} \rightarrow R_{j} } \)). \({{\mathscr {R}}}_{d} \) deterministic routing is theoretically more compact and faster than adaptive routing \({{\mathscr {R}}}_{d} \). Practically, this also means that \({{\mathscr {R}}}\left( AB,R_{i} \left( l_{j},l_{k} \right) \right) \) in (22) is predetermined114, 115, regardless of topology and cost function. A straightforward selection for \({{\mathscr {R}}}_{d} \) is
where \(R'\) is a current node processed by \({{\mathscr {R}}}_{d} \), while function \(f_{N} \left( R'\right) \) selects the next neighbour node of \(R'\).
In \({{\mathscr {R}}}_{a} \) adaptive routing between \(R_{i} \) and \(R_{j} \), the shortest path \({{\mathscr {P}}}^{*} \left( R_{i} \rightarrow R_{j} \right) \) is not fixed. The next neighbour \(R_{j} \) is adaptively selected from set \({{\mathscr {S}}}_{N} \left( R_{i} \right) \) according to the current network situation. \({{\mathscr {R}}}_{a} \) adaptive routing requires more resources and computational power than does \({{\mathscr {R}}}_{d} \). Practically, this also means that \({{\mathscr {R}}}\left( AB,R_{i} \left( l_{j},l_{k} \right) \right) \) in (22) is not predetermined and depends on the actual topology and cost function of \({{\mathscr {R}}}_{a} \). Algorithm 2 is a straightforward selection for \({{\mathscr {R}}}_{a} \) in our setting.
Figure 3 depicts scaled routing in a quantum Internet setting. The network consists of K transmit users, \(A_{1},\ldots ,A_{K} \), and K receiver users \(B_{1},\ldots ,B_{K} \). As the highest service rate path \({{\mathscr {P}}}^{*} \left( A_{i} \rightarrow B_{i} \right) \) is determined between all transmit and receiver users, the quantum repeaters nodes of the quantum network are partitioned into subnetworks \({{\mathscr {S}}}_{{{\mathscr {R}}}_{d} } ={{\mathscr {S}}}_{{{\mathscr {R}}}_{d,1} } \bigcup \cdots \bigcup {{\mathscr {S}}}_{{{\mathscr {R}}}_{d,{{\mathscr {D}}}} } \) with deterministic routing \({{\mathscr {R}}}_{d} \) and \({{\mathscr {S}}}_{{{\mathscr {R}}}_{a} } ={{\mathscr {S}}}_{{{\mathscr {R}}}_{a,1} } \bigcup \cdots \bigcup {{\mathscr {S}}}_{{{\mathscr {R}}}_{a,{{\mathscr {A}}}} } \) with adaptive routing \({{\mathscr {R}}}_{a} \) between the nodes.
Scaled routing in the quantum Internet. The network is decomposed into subnetworks with \({{\mathscr {R}}}_{a} \) adaptive routing (depicted by yellow clouds) and \({{\mathscr {R}}}_{d} \) deterministic routing (depicted by grey-blue clouds) between the nodes of the subnetwork. Each subset consists of quantum repeaters and entangled connections with heterogeneous entanglement levels.
Performance evaluation
Service rate
Assume that R is a quantum repeater in N with a standard quality optical fiber \({{\mathscr {N}}}\) with a link loss \({{\mathscr {L}}}\left( {{\mathscr {N}}}\right) \approx 3.3\; {\mathrm{dB}}\). In Fig. 4, the \(S\left( R\right) \) service rate of quantum repeater R is depicted in function of the \(\left| B_{F}^{in} \right| \) number of incoming Bell states at a particular fidelity F through \({{\mathscr {N}}}\), and in function of \(\Phi \left( R\right) \left| B^{in}_F\right| \), where \(\Phi \left( R\right) \) is evaluated via (25). The service rate is measured as the \(\left| B_{F} \right| \) number of outcoming Bell states per sC cycles, where s is selected such that \(st_{C} =1\,{\hbox {s}} \), while the \(\Phi \left( R\right) \left| B^{in}_F\right| \) quantity is measured in sC cycles. The values of \(\left| B_{F}^{in} \right| \) are set to the range of [0, 250], while \(\Phi \left( R\right) \left| B^{in}_F\right| \) is scaled between \(\Phi \left( R\right) \left| B^{in}_F\right| \in \left[ 1,2\right] \) sC cycles (Fig. 4a) and between \(\Phi \left( R\right) \left| B^{in}_F\right| \in \left[ 1,1.3\right] \) sC cycles (Fig. 4b), at node efficiency (ratio of outcoming and incoming number of Bell states) \({\eta }_R={\left| B_F\right| }/{\left| B^{in}_F\right| }=0.9\).
The \(S\left( R\right) \) service rate of a quantum repeater R with an optical fiber \({{\mathscr {N}}}\) with a standard link loss \({{\mathscr {L}}}\left( {{\mathscr {N}}}\right) \approx 3.3\; {\mathrm{dB}}\). The service rate is depicted in function of the \(\left| B^{in}_F\right| \) number of incoming Bell states at a particular fidelity F and \(\Phi \left( R\right) \left| B^{in}_F\right| \), where \(\Phi \left( R\right) \) is evaluated via (25), node efficiency (ratio of outcoming and incoming number of Bell states) \({\eta }_R={\left| B_F\right| }/{\left| B^{in}_F\right| }=0.9\). a The values of \(\left| B_{F}^{in} \right| \) are set to the range of [0, 250], while \(\Phi \left( R\right) \left| B^{in}_F\right| \) is scaled between \(\Phi \left( R\right) \left| B^{in}_F\right| \in \left[ 1,2\right] \) sC cycles. b The values of \(\left| B_{F}^{in} \right| \) are set to the range of [0, 250], while \(\Phi \left( R\right) \left| B^{in}_F\right| \) is scaled between \(\Phi \left( R\right) \left| B^{in}_F\right| \in \left[ 1,1.3\right] \, sC\) cycles.
Computational complexity
Let \(\left| V_{R} \right| \) be the total number of quantum repeaters in N, with an average number \(\left| {{\mathscr {S}}}_{in} \left( R\right) \right| \) of incoming entangled connections per quantum repeater R, and with an average number \(\left| {{\mathscr {S}}}_{out} \left( R\right) \right| \) of outcoming entangled connections. Then, by utilizing the complexity of a service rate determination114, 115, the computational complexity of the routing scaling algorithm is
Assuming that \(\left| {{\mathscr {S}}}_{in} \left( R\right) \right| =\left| {{\mathscr {S}}}_{out} \left( R\right) \right| \) in the nodes, the computational complexity is
For a detailed proof, see Section A.1 of the Appendix.
Comparison
The computational complexity of the algorithm is compared with the computational complexity of the PG (performance queueing) G/G/1 routing method115.
For analytical purposes, we assume a realistic network setting with \(\left| {{\mathscr {S}}}_{in} \left( R\right) \right| <\sqrt{\left| V_{R} \right| }\), and for simplicity we set \(\left| {{\mathscr {S}}}_{in} \left( R\right) \right| =\left| {{\mathscr {S}}}_{out} \left( R\right) \right| \), with \(\left| {{V}_{R}} \right| \in \left[ {{1,10}^{3}} \right] \), and \({{\left| {{{\mathscr {S}}}_{in}}\left( R \right) \right| }^{3}}\in \left[ {{1,10}^{3}} \right] \).
Figure 5a depicts the resulting complexity of our algorithm, the complexity of the PG routing method is depicted in Fig. 5b.
a The computational complexity (\(N_{O} \): number of operations) of the proposed algorithm at a realistic network setting, \(\left| {{\mathscr {S}}}_{in} \left( R\right) \right| <\sqrt{\left| V_{R} \right| }\), with \(\left| {{\mathscr {S}}}_{in} \left( R\right) \right| =\left| {{\mathscr {S}}}_{out} \left( R\right) \right| \), in function of \(\left| V_{R} \right| \) and \(\left| {{\mathscr {S}}}_{in} \left( R\right) \right| ^{3}\), \(\left| {{V}_{R}} \right| \in \left[ {{1,10}^{3}} \right] \), \({{\left| {{{\mathscr {S}}}_{in}}\left( R \right) \right| }^{3}}\in \left[ {{1,10}^{3}} \right] \). b The computational complexity of the PG method at a realistic network setting, \(\left| {{\mathscr {S}}}_{in} \left( R\right) \right| <\sqrt{\left| V_{R} \right| }\), \({\mathscr {O}}( {{\left| V_{R} \right| }^{{5}/{2}\;}})\) at a particular \(\left| V_{R} \right| \), \(\left| {{V}_{R}} \right| \in \left[ {{1,10}^{3}} \right] \), \({{\left| {{{\mathscr {S}}}_{in}}\left( R \right) \right| }^{3}}\in \left[ {{1,10}^{3}} \right] \).
Conclusions
Here, we defined a method for routing space evaluation and scalable routing in the quantum Internet. The derived methods utilize the framework of queueing theory along with the characteristics and physical attributes of the quantum Internet. We proved the service rate formulas of quantum repeaters and entangled paths. We defined a method for routing space evaluation to explore the service rates of quantum repeaters and entangled paths of the quantum Internet. Using the results of the routing space exploration, we defined scalable routing for the quantum Internet. The scaled routing function determines the most appropriate routing mechanism for the subnetworks to realize high efficiency and routing in the quantum Internet.
Ethics statement
This work did not involve any active collection of human data.
Data availability
This work does not have any experimental data.
References
Arute, F. et al. Quantum supremacy using a programmable superconducting processor. Nature https://doi.org/10.1038/s41586-019-1666-5 (2019).
Preskill, J. Quantum computing in the NISQ era and beyond. Quantum 2, 79 (2018).
Harrow, A. W. & Montanaro, A. Quantum computational supremacy. Nature 549, 203–209 (2017).
Aaronson, S. & Chen, L. Complexity-theoretic foundations of quantum supremacy experiments. Proceedings of the 32nd Computational Complexity Conference, CCC’17, pp. 22:1–22:67 (2017).
Farhi, E., Goldstone & J., Gutmann, S. A quantum approximate optimization algorithm. arXiv:1411.4028v1 (2014).
Farhi, E., Goldstone, J., Gutmann, S. & Neven, H. Quantum algorithms for fixed qubit architectures. arXiv:1703.06199v1 (2017).
Farhi, E. & Neven, H. Classification with quantum neural networks on near term processors. arXiv:1802.06002v1 (2018).
Farhi, E., Goldstone, J., Gutmann, S. & Zhou, L. The quantum approximate optimization algorithm and the Sherrington–Kirkpatrick model at infinite size. arXiv:1910.08187 (2019).
Farhi, E., Gamarnik, D. & Gutmann, S. The quantum approximate optimization algorithm needs to see the whole graph: a typical case. arXiv:2004.09002v1 (2020).
Alexeev, Y. et al. Quantum computer systems for scientific discovery. arXiv:1912.07577 (2019).
Loncar, M. et al. Development of quantum interconnects for next-generation information technologies. arXiv:1912.06642 (2019).
Foxen, B. et al. Demonstrating a continuous set of two-qubit gates for near-term quantum algorithms. arXiv:2001.08343 (2020).
Ajagekar, A., Humble, T. & You, F. Quantum computing based hybrid solution strategies for large-scale discrete-continuous optimization problems. Comput. Chemi. Eng. 132, 106630 (2020).
Ajagekar, A. & You, F. Quantum computing for energy systems optimization: challenges and opportunities. Energy 179, 76–89 (2019).
Harrigan, M. et al. Quantum approximate optimization of non-planar graph problems on a planar superconducting processor. arXiv:2004.04197v1 (2020).
Rubin, N. et al. Hartree–Fock on a superconducting qubit quantum computer. arXiv:2004.04174v1 (2020).
Lloyd, S. Quantum approximate optimization is computationally universal. arXiv:1812.11075 (2018).
Brown, K. A. & Roser, T. Towards storage rings as quantum computers. Phys. Rev. Accel. Beams 23, 054701 (2020).
Sax, I. et al. Approximate approximation on a quantum annealer. arXiv:2004.09267 (2020).
Pirandola, S. & Braunstein, S. L. Unite to build a quantum Internet. Nature 532, 169–171 (2016).
Pirandola, S. End-to-end capacities of a quantum communication network. Commun. Phys. 2, 51 (2019).
Pirandola, S., Laurenza, R., Ottaviani, C. & Banchi, L. Fundamental limits of repeaterless quantum communications. Nat. Commun. 8, 15043. https://doi.org/10.1038/ncomms15043 (2017).
Pirandola, S. et al. Theory of channel simulation and bounds for private communication. Quantum Sci. Technol. 3, 035009 (2018).
Pirandola, S. Bounds for multi-end communication over quantum networks. Quantum Sci. Technol. 4, 045006 (2019).
Pirandola, S. Capacities of repeater-assisted quantum communications. arXiv:1601.00966 (2016).
Pirandola, S. et al. Advances in quantum cryptography. arXiv:1906.01645 (2019).
Laurenza, R. & Pirandola, S. General bounds for sender–receiver capacities in multipoint quantum communications. Phys. Rev. A 96, 032318 (2017).
Van Meter, R. Quantum Networking. ISBN 1118648927, 9781118648926, John Wiley and Sons Ltd (2014).
Lloyd, S. et al. Infrastructure for the quantum Internet. ACM SIGCOMM Comput. Commun. Rev. 34, 9–20 (2004).
Kimble, H. J. The quantum Internet. Nature 453, 1023–1030 (2008).
Gyongyosi, L., Imre, S. & Nguyen, H. V. A survey on quantum channel capacities. IEEE Communications Surveys and Tutorials https://doi.org/10.1109/COMST.2017.2786748 (2018).
Gyongyosi, L. & Imre, S. A survey on quantum computing technology. Computer Science Review, Elsevier. https://doi.org/10.1016/j.cosrev.2018.11.002, ISSN: 1574-0137 (2018).
Gyongyosi, L. & Imre, S. Optimizing high-efficiency quantum memory with quantum machine learning for near-term quantum devices. Sci. Rep. https://doi.org/10.1038/s41598-019-56689-0 (2019).
Gyongyosi, L. & Imre, S. Theory of noise-scaled stability bounds and entanglement rate maximization in the quantum Internet. Sci. Rep. https://doi.org/10.1038/s41598-020-58200-6 (2020).
Gyongyosi, L. & Imre, S. Entanglement accessibility measures for the quantum Internet. Quantum Inf. Process. 19, 115. https://doi.org/10.1007/s11128-020-2605-y (2020).
Gyongyosi, L. & Imre, S. Entanglement concentration service for the quantum Internet, Quantum Inf. Process. (in press) (2020).
Gyongyosi, L. Services for the quantum internet. DSc Dissertation, Hungarian Academy of Sciences (MTA) (2020).
Gyongyosi, L. Quantum state optimization and computational pathway evaluation for gate-model quantum computers. Sci. Rep. https://doi.org/10.1038/s41598-020-61316-4 (2020).
Gyongyosi, L. & Imre, S. Training optimization for gate-model quantum neural networks. Sci. Rep. https://doi.org/10.1038/s41598-019-48892-w (2019).
Gyongyosi, L. & Imre, S. Dense quantum measurement theory. Sci. Rep. https://doi.org/10.1038/s41598-019-43250-2 (2019).
Gyongyosi, L. & Imre, S. State stabilization for gate-model quantum computers. Quantum Inf. Process. https://doi.org/10.1007/s11128-019-2397-0 (2019).
Gyongyosi, L. & Imre, S. Quantum circuit design for objective function maximization in gate-model quantum computers. Quantum Inf. Process. https://doi.org/10.1007/s11128-019-2326-2 (2019).
Van Meter, R., Ladd, T. D., Munro, W. J. & Nemoto, K. System design for a long-line quantum repeater. IEEE/ACM Trans. Netw. 17(3), 1002–1013 (2009).
Van Meter, R., Satoh, T., Ladd, T. D., Munro, W. J. & Nemoto, K. Path selection for quantum repeater networks. Netw. Sci. 3(1–4), 82–95 (2013).
Van Meter, R. & Devitt, S. J. Local and distributed quantum computation. IEEE Comput. 49(9), 31–42 (2016).
Gyongyosi, L. & Imre, S. Decentralized base-graph routing for the quantum internet, Phys. Rev. A, American Physical Society. https://doi.org/10.1103/PhysRevA.98.022310. https://link.aps.org/doi/10.1103/PhysRevA.98.022310 (2018).
Gyongyosi, L. & Imre, S. Dynamic topology resilience for quantum networks, Proceedings of the SPIE 10547, Advances in Photonics of Quantum Computing, Memory, and Communication XI, 105470Z. https://doi.org/10.1117/12.2288707(2018).
Gyongyosi, L. & Imre, S. Topology adaption for the quantum Internet. Quantum Inf. Process. https://doi.org/10.1007/s11128-018-2064-x (2018).
Gyongyosi, L. & Imre, S. Adaptive routing for quantum memory failures in the quantum Internet. Quantum Inf. Process. https://doi.org/10.1007/s11128-018-2153-x (2018).
Gyongyosi, L. & Imre, S. Entanglement access control for the quantum Internet. Quantum Inf. Process. https://doi.org/10.1007/s11128-019-2226-5 (2019).
Gyongyosi, L. & Imre, S. Multilayer optimization for the quantum Internet. Sci. Rep. https://doi.org/10.1038/s41598-018-30957-x (2018).
Gyongyosi, L. & Imre, S. Entanglement availability differentiation service for the quantum Internet, Sci. Rep. (https://doi.org/10.1038/s41598-018-28801-3). https://www.nature.com/articles/s41598-018-28801-3 (2018).
Gyongyosi, L. & Imre, S. Entanglement-gradient routing for quantum networks, Sci. Rep. (https://doi.org/10.1038/s41598-017-14394-w). https://www.nature.com/articles/s41598-017-14394-w (2017).
Gyongyosi, L. & Imre, S. Opportunistic entanglement distribution for the quantum Internet. Sci. Rep. https://doi.org/10.1038/s41598-019-38495-w (2019).
Imre, S. & Gyongyosi, L. Advanced Quantum Communications—An Engineering Approach (Wiley-IEEE Press, New Jersey, 2013).
Caleffi, M. End-to-end entanglement rate: toward a quantum route metric, 2017 IEEE Globecom. https://doi.org/10.1109/GLOCOMW.2017.8269080 (2018).
Caleffi, M. Optimal routing for quantum networks. IEEE Access 5 https://doi.org/10.1109/ACCESS.2017.2763325 (2017).
Caleffi, M., Cacciapuoti, A.S. & Bianchi, G. Quantum Internet: from communication to distributed computing. arXiv:1805.04360 (2018).
Castelvecchi, D. The quantum Internet has arrived, Nature, News and Comment. https://www.nature.com/articles/d41586-018-01835-3 (2018).
Cacciapuoti, A. S., Caleffi, M., Tafuri, F., Cataliotti, F. S., Gherardini, S. & Bianchi, G. Quantum Internet: networking challenges in distributed quantum computing. arXiv:1810.08421 (2018).
Cuomo, D., Caleffi, M. & Cacciapuoti, A. S. Towards a distributed quantum computing ecosystem. arXiv:2002.11808v1 (2020).
Chakraborty, K., Rozpedeky, F., Dahlbergz, A. & Wehner, S. Distributed routing in a quantum Internet. arXiv:1907.11630v1 (2019).
Khatri, S., Matyas, C. T., Siddiqui, A. U. & Dowling, J. P. Practical figures of merit and thresholds for entanglement distribution in quantum networks. Phys. Rev. Res. 1, 023032 (2019).
Kozlowski, W. & Wehner, S. Towards large-scale quantum networks, Proc. of the Sixth Annual ACM International Conference on Nanoscale Computing and Communication, Dublin, Ireland. arXiv:1909.08396 (2019).
Pathumsoot, P. et al. Modeling of measurement-based quantum network coding on IBMQ devices. Phys. Rev. A 101, 052301 (2020).
Pal, S., Batra, P., Paterek, T. & Mahesh, T. S. Experimental localisation of quantum entanglement through monitored classical mediator. arXiv:1909.11030v1 (2019).
Miguel-Ramiro, J. & Dur, W. Delocalized information in quantum networks. New J. Phys https://doi.org/10.1088/1367-2630/ab784d (2020).
Miguel-Ramiro, J., Pirker, A. & Dur, W. Genuine quantum networks: superposed tasks and addressing. arXiv:2005.00020v1 (2020).
Pirker, A. & Dur, W. A quantum network stack and protocols for reliable entanglement-based networks. arXiv:1810.03556v1 (2018).
Shannon, K., Towe, E. & Tonguz, O. On the use of quantum entanglement in secure communications: a survey. arXiv:2003.07907 (2020).
Amoretti, M. & Carretta, S. Entanglement verification in quantum networks with tampered nodes. IEEE Journal on Selected Areas in Communications https://doi.org/10.1109/JSAC.2020.2967955 (2020).
Cao, Y. et al. Multi-tenant provisioning for quantum key distribution networks with heuristics and reinforcement learning: a comparative study. IEEE Transactions on Network and Service Management https://doi.org/10.1109/TNSM.2020.2964003 (2020).
Cao, Y. et al. Key as a service (KaaS) over quantum key distribution (QKD)-integrated optical networks. IEEE Commun Mag. https://doi.org/10.1109/MCOM.2019.1701375 (2019).
Liu, Y. Preliminary study of connectivity for quantum key distribution network. arXiv:2004.11374v1 (2020).
Amer, O., Krawec, W. O. & Wang, B. Efficient routing for quantum key distribution networks. arXiv:2005.12404 (2020).
Krisnanda, T. et al. Probing quantum features of photosynthetic organisms. NPJ Quantum Inf. 4, 60 (2018).
Krisnanda, T. et al. Revealing nonclassicality of inaccessible objects. Phys. Rev. Lett. 119, 120402 (2017).
Kok, P. et al. Linear optical quantum computing with photonic qubits. Rev. Mod. Phys. 79, 135–174 (2007).
Petz, D. Quantum Information Theory and Quantum Statistics (Springer, Heidelberg, 2008) (Hiv: 6).
Bacsardi, L. On the way to quantum-based satellite communication. IEEE Commun. Mag. 51(08), 50–55 (2013).
Biamonte, J. et al. Quantum machine learning. Nature 549, 195–202 (2017).
Lloyd, S., Mohseni, M. & Rebentrost, P. Quantum algorithms for supervised and unsupervised machine learning. arXiv:1307.0411 (2013).
Lloyd, S., Mohseni, M. & Rebentrost, P. Quantum principal component analysis. Nat. Phys. 10, 631 (2014).
Lloyd, S. Capacity of the noisy quantum channel. Phys. Rev. A 55, 1613–1622 (1997).
Lloyd, S. The universe as quantum computer. In A Computable Universe: Understanding and exploring Nature as computation (ed. Zenil, H.) (World Scientific, Singapore, 2013).
Shor, P. W. Scheme for reducing decoherence in quantum computer memory. Phys. Rev. A 52, R2493–R2496 (1995).
Chou, C. et al. Functional quantum nodes for entanglement distribution over scalable quantum networks. Science 316(5829), 1316–1320 (2007).
Muralidharan, S., Kim, J., Lutkenhaus, N., Lukin, M. D. & Jiang, L. Ultrafast and fault-tolerant quantum communication across long distances. Phys. Rev. Lett. 112, 250501 (2014).
Yuan, Z. et al.Nature 454, 1098–1101 (2008).
Kobayashi, H., Le Gall, F., Nishimura, H. & Rotteler, M. General scheme for perfect quantum network coding with free classical communication, Lecture Notes in Computer Science (Automata, Languages and Programming SE-52 vol. 5555), Springer) pp. 622–633 (2009).
Hayashi, M. Prior entanglement between senders enables perfect quantum network coding with modification. Phys. Rev. A 76, 040301(R) (2007).
Hayashi, M., Iwama, K., Nishimura, H., Raymond, R. & Yamashita, S, Quantum network coding, Lecture Notes in Computer Science (STACS 2007 SE52 vol. 4393) ed Thomas, W. & Weil, P. (Berlin Heidelberg: Springer) (2007).
Chen, L. & Hayashi, M. Multicopy and stochastic transformation of multipartite pure states. Phys. Rev. A 83(2), 022331 (2011).
Schoute, E., Mancinska, L., Islam, T., Kerenidis, I. & Wehner, S. Shortcuts to quantum network routing. arXiv:1610.05238 (2016).
Lloyd, S. & Weedbrook, C. Quantum generative adversarial learning. Phys. Rev. Lett., 121. arXiv:1804.09139 (2018).
Gisin, N. & Thew, R. Quantum communication. Nat. Photon. 1, 165–171 (2007).
Xiao, Y. F. & Gong, Q. Optical microcavity: from fundamental physics to functional photonics devices. Sci. Bull. 61, 185–186 (2016).
Zhang, W. et al. Quantum secure direct communication with quantum memory. Phys. Rev. Lett. 118, 220501 (2017).
Enk, S. J., Cirac, J. I. & Zoller, P. Photonic channels for quantum communication. Science 279, 205–208 (1998).
Briegel, H. J., Dur, W., Cirac, J. I. & Zoller, P. Quantum repeaters: the role of imperfect local operations in quantum communication. Phys. Rev. Lett. 81, 5932–5935 (1998).
Dur, W., Briegel, H. J., Cirac, J. I. & Zoller, P. Quantum repeaters based on entanglement purification. Phys. Rev. A 59, 169–181 (1999).
Duan, L. M., Lukin, M. D., Cirac, J. I. & Zoller, P. Long-distance quantum communication with atomic ensembles and linear optics. Nature 414, 413–418 (2001).
Van Loock, P. et al. Hybrid quantum repeater using bright coherent light. Phys. Rev. Lett. 96, 240501 (2006).
Zhao, B., Chen, Z. B., Chen, Y. A., Schmiedmayer, J. & Pan, J. W. Robust creation of entanglement between remote memory qubits. Phys. Rev. Lett. 98, 240502 (2007).
Goebel, A. M. et al. Multistage entanglement swapping. Phys. Rev. Lett. 101, 080403 (2008).
Simon, C. et al. Quantum repeaters with photon pair sources and multimode memories. Phys. Rev. Lett. 98, 190503 (2007).
Tittel, W. et al. Photon-echo quantum memory in solid state systems. Laser Photon. Rev. 4, 244–267 (2009).
Sangouard, N., Dubessy, R. & Simon, C. Quantum repeaters based on single trapped ions. Phys. Rev. A 79, 042340 (2009).
Dur, W. & Briegel, H. J. Entanglement purification and quantum error correction. Rep. Prog. Phys 70, 1381–1424 (2007).
Sheng, Y. B. & Zhou, L. Distributed secure quantum machine learning. Sci. Bull. 62, 1025–1019 (2017).
Leung, D., Oppenheim, J. & Winter, A. Quantum network communication; the butterfly and beyond. IEEE Trans. Inf. Theory 56, 3478–90 (2010).
Kobayashi, H., Le Gall, F., Nishimura, H. & Rotteler, M. Perfect quantum network communication protocol based on classical network coding, Proceedings of 2010 IEEE International Symposium on Information Theory (ISIT) pp. 2686–2690. (2010).
Bhat, U. N. The general queue G/G/1 and approximations. An Introduction to Queueing Theory. pp. 169–183. ISBN 978-0-8176-4724-7. (2008).
Kiasari, A. E., Jantsch, A. & Lu, Z. A. Heuristic framework for designing and exploring deterministic routing algorithm for NoCs. In: Palesi, M. & Daneshtalab, M. (Editors) Routing Algorithms in Networks-on-Chip, Springer, ISBN 978-1-4614-8273-4, ISBN 978-1-4614-8274-1 (eBook) (2014).
Kiasari, A. E., Lu, Z., and Jantsch, A. An analytical latency model for networks-on-chip. IEEE Trans. Very Large Scale Integr. (VLSI) Syst. 21(1) (2013).
Watkins, C. J. C. H. & Dayan, P. Q-Learning, In: Proc. Machine Learning, pp.279–292 (1992).
Choi, S. P. M. & Yeung, D. T. Predictive Q-Routing: A Memory-based Reinforcement Learning Approach to Adaptive Traffic Control, In: Advances in Neural Information Processing Systems 8 (NIPS8), pp. 945–951, MIT Press (1996).
Farahnakian, F., Ebrahimi, M., Daneshtalab, M., Liljeberg, P. & Plosila, J. Q-learning based congestion-aware routing algorithm for on-chip network. Proceedings of 2011 IEEE 2nd International Conference on Networked Embedded Systems for Enterprise Applications. https://doi.org/10.1109/NESEA.2011.6144949 (2012).
Acknowledgements
Open access funding provided by Budapest University of Technology and Economics (BME). The research reported in this paper has been supported by the Hungarian Academy of Sciences (MTA Premium Postdoctoral Research Program 2019), by the National Research, Development and Innovation Fund (TUDFO/51757/2019-ITM, Thematic Excellence Program), by the National Research Development and Innovation Office of Hungary (Project No. 2017-1.2.1-NKP-2017-00001), by the Hungarian Scientific Research Fund - OTKA K-112125 and in part by the BME Artificial Intelligence FIKP grant of EMMI (Budapest University of Technology, BME FIKP-MI/SC).
Author information
Authors and Affiliations
Contributions
L.GY. designed the protocol and wrote the manuscript. L.GY. and S.I. analyzed the results. All authors reviewed the manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher's note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Gyongyosi, L., Imre, S. Routing space exploration for scalable routing in the quantum Internet. Sci Rep 10, 11874 (2020). https://doi.org/10.1038/s41598-020-68354-y
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-020-68354-y
This article is cited by
-
Optimal and scalable entanglement distribution over crossbar quantum networks
Scientific Reports (2024)
-
Optimal quantum network decongestion strategies
Scientific Reports (2023)
-
Scalable distributed gate-model quantum computers
Scientific Reports (2021)
-
Multiparty weighted threshold quantum secret sharing based on the Chinese remainder theorem to share quantum information
Scientific Reports (2021)
-
Resource prioritization and balancing for the quantum internet
Scientific Reports (2020)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.