Abstract
We introduce a repeater scheme to efficiently distribute multipartite entangled states in a quantum network with optimal scaling. The scheme allows to generate graph states such as 2D and 3D cluster states of growing size or GHZ states over arbitrary distances, with a constant overhead per node/channel that is independent of the distance. The approach is genuine multipartite, and is based on the measurement-based implementation of multipartite hashing, an entanglement purification protocol that operates on a large ensemble together with local merging/connection of elementary building blocks. We analyze the performance of the scheme in a setting where local or global storage is limited, and compare it to bipartite and hybrid approaches that are based on the distribution of entangled pairs. We find that the multipartite approach offers a storage advantage, which results in higher efficiency and better performance in certain parameter regimes. We generalize our approach to arbitrary network topologies and different target graph states.
Similar content being viewed by others
Introduction
The distribution of entangled quantum states over large distances is a central task in quantum information processing. Initial studies have focused on point-to-point communication between a sender and a single receiver, where quantum repeaters1,2,3,4,5,6,7,8,9,10 have been developed to enable long-distance quantum communication over noisy channels in the presence of imperfect local control operations. Recent experimental developments, together with the promise of exciting applications of quantum technology, make large-scale networks or even a full-scale quantum internet a viable possibility. In such networks, not only the distribution of Bell states–which might be used for quantum communication between two parties via teleportation11, or for quantum key distribution12,13–is of relevance, but also the generation of multipartite entangled states shared among several nodes of the network. This opens the way for applications such as secret voting and secret sharing14, conference key agreement15,16,17, clock synchronization18, or distributed quantum computation19.
One important aspect in such quantum networks is efficiency - i.e. the required overhead for distributing entangled states shared between the communication partners. While a direct communication over noisy and lossy channels suffers from exponentially growing overheads with the distance (and hence small rates per channel usage), quantum repeater schemes (see e.g.1,2,3,4,5,6,7,20) or transmission of encoded information5,8,9,10,21 allow for an efficient generation of bipartite entangled states between two communication partners with overheads that scale polynomially or polylogarithmically with the distance. For a comparison of different approaches to generate long distance entanglement see22 and23.
Similar schemes have been proposed for the direct distribution of multipartite entangled states24,25, while in26 a quantum repeater scheme that is based on the usage of multipartite states that are connected and purified was introduced. While such schemes are in principle efficient, overheads significantly increase with the distance and rates are hence limited.
In23 a solution to this problem was proposed, where a quantum repeater scheme based on hashing–a deterministic entanglement purification protocol that operates on a large ensemble—is used to establish long-distance quantum communication between a sender and a receiver with overheads per channel that do not grow with the distance. A key element in this approach is the measurement-based implementation of purification and connection processes27.
Here, we introduce a similar scheme for the direct distribution of multipartite entangled states in a long-distance quantum network. Our scheme is capable of generating high-fidelity multipartite entangled target states shared between different nodes of the network with a constant overhead per channel, which is independent of the distance. To this aim, we combine the idea of so-called 2D quantum repeaters26 (or multipartite network repeaters) with the new type of repeaters based on hashing23 in a multipartite setting. We analyze finite-size multipartite hashing schemes28,29,30 which are a central element in our approach, and provide lower bounds on the global output fidelity of these entanglement purification protocols in terms of the number of input copies, initial fidelities and noise levels on the resource states of the measurement-based implementation. We illustrate the overall approach for the generation of 2D and 3D cluster states of growing size in the network, and also discuss the distribution of three-party GHZ states. However, the approach is not limited to regular networks, but can easily be adapted to other network topologies and different target states. Note, however, that the schemes we propose are not optimized for a near-term implementation with a very small number of resources as they require the storage and processing of a few hundred copies or more. Rather, they provide a long-term perspective for large-scale implementations and we obtain an efficient, scalable scheme that allows for the transmission of big quantum data in an intrinsically multipartite way.
We also discuss alternative schemes based on pairwise generation of entangled states, which are subsequently combined to form the desired multipartite target state (scheme B), and a hybrid approach that makes use of bipartite and multipartite elements (scheme C). We compare these three approaches, and develop optimized strategies to minimize the storage requirements of stations in the network. We also introduce and discuss variants of the multipartite protocol that use elementary building blocks of different size and shape (scheme A). The multipartite approach (A) offers an advantage over bipartite and hybrid approaches in this respect, as the storage requirements per repeater or network node are smaller. We analyze the performance of the different schemes with respect to reachable fidelities and obtainable number of output copies.
To this aim we concentrate on a scenario where the available quantum memory is limited. This is of practical relevance in a future quantum network. We consider the case where the overall storage capacity in the network is bounded, as well as a scenario where each node in the network has a quantum memory of the same (limited) size. In both cases, we identify parameter regimes (reachable target fidelity, channel noise and errors in resource states) where scheme (A) is superior to (B) and (C). We also remark that the hybrid approach (C) performs well in certain settings, and can even be more efficient than the multipartite approach. However, in particular in three-dimensional networks the storage advantage of the multipartite approach dominates.
The paper is organized as follows. In Sec. 2 we summarize basic concepts and required methods. We briefly review graph states and 2D repeater schemes, as well as the measurement-based implementation of repeater elements. We also discuss multipartite hashing schemes and analyze their performance for finite number of input states. In Sec. 3 we define the problem setting and introduce different schemes to generate long-distance entangled states in the network using (A) an intrinsic multipartite approach, (B) a bipartite approach based on the distribution of entangled pairs and (C) a hybrid approach with bipartite and multipartite elements. In particular, we compare the different schemes in scenarios where the size of quantum memory is limited in Sec. 4. In Sec. 4.1 we consider three-party GHZ states with growing distance. In Sec. 4.2.1 we discuss explicit ways to efficiently obtain cluster states of growing size in networks with a 2D and 3D geometry and analyse them in a scenario where (i) the local memory per network node or (ii) the total memory is limited in Sec. 4.2.2 and 4.2.3 respectively. In case of (ii) memory can be freely distributed among nodes to optimize performance. Furthermore, we discuss an additional scenario that starts from only Bell pairs distributed between neighboring parties in Sec. 4.2.4. We provide a generalization of our approach to arbitrary network topologies and different kinds of target states in Sec. 5, and summarize and conclude in Sec. 6.
Methods and Background
Long-distance entangled states and quantum repeaters
In this paper we focus on the generation of long-distance entangled states. For bipartite entangled states, such as Bell-pairs, this problem is addressed via quantum repeaters. Quantum repeaters were originally designed to establish Bell states over large distances in the presence of imperfections. There are various different architectures, in particular the approach based on quantum error correction8 and the one based on iterative entanglement purification and swapping1. In3 and31 the need for two-way communication in the original entanglement-based quantum repeater1 was removed. In all these approaches the local resources grow polylogarithmically or polynomially with the distance.
The problem of creating graph states in quantum networks was adressed in25,32,33,34. In particular, the work of25 shows how to generate long-distance graph states by generalizing the concept of quantum repeaters to multipartite entangled states. In32 different techniques were proposed for establishing small-scale graph states where clients need to merge small scale GHZ states for establishing the target graph states. Finally33, proposes a recursive architecture for quantum repeater networks, with the aim of creating arbitrary graph states between its clients, while34 introduces a modular architecture that relies on quantum network devices to fullfil arbitrary graph state requests.
In26 a generalization of the 1998 quantum repeater protocol1 to multipartite states like GHZ or cluster states, was proposed. It is based on the preparation of elementary multipartite states, which are generated over short distances. Subsequently these states are purified via recurrence protocols. Then they are connected via measurements, similar to entanglement swapping, in order to obtain the desired multipartite state over a larger distance. This process is then iterated. The 2D quantum repeater shares the polynomial scaling of resources with the original quantum repeater scheme. There is also a variant of the 2D quantum repeater, where one does not aim at preparing a multipartite state of fixed size (number of parties) but rather tries to let the number of parties grow with the distance26. A major insight of26 was that there are parameter regimes for the noise in which a truly multipartite quantum repeater approach performs better than a bipartite approach (where one would first establish long-distance Bell pairs which are then used to create the desired multipartite state).
Measurement-based implementation
Measurement-based quantum computation35,36,37 is a scheme for quantum computing which is based on adaptive single qubit measurements on a resource state. A prominent resource state for universal measurement-based quantum computing is the 2D cluster state36. However, instead of using a state which is universal for quantum computation like the 2D cluster state, one can alternatively use the Jamiolkowski isomorphism to identify smaller quantum states (in terms of qubits) which achieve a given computational task at hand. More specifically, the Jamiolkowski isomorphism establishes a one-to-one correspondence between completely positive (CP) maps and quantum states which implement the given CP-map probabilistically on an input state, which is read in via Bell measurements, similar to teleportation11.
The protocols we consider here consist only of Clifford operations and Pauli measurements, which can be implemented deterministically using resource states of minimal size, i.e. they consist of only input and output qubits and no intermediate qubits. The map described by the circuit is performed solely by the Bell measurements at the read-in. Many quantum error correcting codes and entanglement purification protocols have this property.
Quantum repeater based on hashing
In23 a new quantum repeater scheme based on hashing38 with superior scaling was introduced. The hashing protocol for bipartite entanglement purification operates on a large number of Bell pairs and outputs m = n(1 − S) perfect Bell pairs in the asymptotic limit. Here, n denotes the number of input pairs and S their entropy. The protocol has a non-zero yield (ratio of output and input pairs in the asymptotic limit) in contrast to recurrence protocols39,40, where the yield vanishes. In the novel quantum repeater protocol, the nested levels of entanglement purification and swapping are replaced by a single, combined step of entanglement purification via the hashing protocol38 and simultaneous swapping of all pairs. This setup is depicted in Fig. 1. In this way the scaling of the local resources per transmitted qubit is reduced from polynomial to constant. We remark that there are no nested repeater levels in this scheme as the whole scheme is implemented in a single step.
Illustration of the measurement-based implementation of the bipartite quantum repeater based on hashing. The initial Bell pairs (blue) are distributed to the neighboring stations and each station prepares a resource state with input (red) and output qubits (black). Note that local noise on the resource states (orange stars) can be shifted to the input states, but noise on the output qubits (blue stars) will still act on the output of the protocol.
Graph states and the graph state basis
Graph states are a special subset of quantum states that are associated with mathematical graphs. A graph G = (V, E) consists of N vertices V and edges E and the corresponding graph state \(|G\rangle \) is given by:
with \({U}_{{\rm{C}}{\rm{Z}}}^{ab}=|0\rangle \langle {0|}^{(a)}\otimes {I}^{(b)}+|1\rangle \langle {1|}^{(a)}\otimes {Z}^{(b)}\), the controlled phase gate acting on qubits a and b, and \(|\,+\,\rangle =1/\sqrt{2}(\mathrm{|0}\rangle +\mathrm{|1}\rangle )\). We call a graph state k-colorable if k is the smallest number of colors needed to color each vertex in its associated graph such that no two vertices of the same color are connected by an edge.
The graph state basis is an orthonormal basis that is defined with respect to a certain graph G:
where \({\boldsymbol{\mu }}=({\mu }_{1},{\mu }_{2},\ldots ,{\mu }_{N})\in {\{0,1\}}^{N}\).
For the purpose of this work we concern ourselves with states diagonal in the graph state basis, which we write as:
This diagonal form can always be achieved by depolarization.
Connecting graph states
In this work we will often mention connection operations to connect graph states. We employ two different connection operations, one where two qubits are merged into one, and one where both connection qubits are projected out.
For the first method one takes two qubits a and b, which correspond to vertices of the graph states that we want to connect, and applies the CNOT operation \({\rm{C}}{\rm{N}}{\rm{O}}{{\rm{T}}}^{a\to b}=|0\rangle \langle {0|}^{(a)}\otimes {I}^{(b)}+|1\rangle \langle {1|}^{(a)}\otimes {X}^{(b)}\) with qubit a as the source and qubit b as the target, followed by a Z-measurement on qubit b. The resulting state is a graph state (up to local Clifford corrections) that corresponds to a graph without vertex b and the neighborhood \({N}_{a}^{{\rm{^{\prime} }}}\) (i.e. all vertices connected to a with an edge) of vertex a is now given by \({N}_{a}\cup {N}_{b}-{N}_{a}\cap {N}_{b}\).
The second kind of connection operation works in a similar fashion. But first one needs to transform the initial graph states by applying the local complementation operation τ (see e.g.41) on both qubits a and b, which are initially not connected by an edge. Then, just as before, one applies CNOTa→b followed by measuring qubit b in the Z-basis. Finally, one measures qubit a in the Y basis. The resulting state is, again, a graph state that corresonds (up to local Clifford corrections) to a graph with vertices a and b removed and changed edges according to: \({N}_{i}^{{\rm{^{\prime} }}}={N}_{i}\cup {N}_{b}-{N}_{i}\cap {N}_{b}\) for all i that were initially in Na and \({N}_{j}^{{\rm{^{\prime} }}}={N}_{j}\cup {N}_{a}-{N}_{j}\cap {N}_{a}\) for all j in Nb. In this work we only use this second connection operation in the context of GHZ states as described in section 4.1, where its effect can be understood as mapping two n-qubit GHZ states to a state that is local Clifford-equivalent to a GHZ state with (2n − 2) qubits.
See41 for a detailed summary on the properties of graph states and how noise and other transformations acting on graph states can be described.
Noise model
We model noise via local depolarizing noise (LDN), which is given by the map \({\mathscr{D}}\) and acts on a qubit with density matrix ρ in the following way:
Here the error parameter q ∈ [0, 1] describes the strength of the noise, q = 1 corresponds to no noise and q = 0 to complete depolarization and X, Y, Z refer to the usual Pauli matrices. It should be noted that LDN can be interpreted as a worst case estimate for local noise42.
We describe the noise that occured during the initial distribution of the state, for example by sending them through noisy quantum channels, by LDN with error parameter q acting on all qubits independently, e.g. a noisy graph state is described by
where the subindex refers to the qubit on which \({{\mathscr{D}}}_{i}\) acts on.
The second source of noise we consider is the imperfections of the resource states we use for the measurement based implementation of our schemes. We describe the noise on the resource states, which are generated locally at each party, by LDN with a different error parameter p acting on all qubits of the resource state.
An important property of LDN is that its location can be exchanged if it is followed by a Bell projection43, i.e.,
where ρ is some density matrix and P1,2 denotes a projector on one of the four Bell states, acting on qubits 1 and 2. The noise on the input qubits of the resource states can thus be (formally) shifted to the input states instead (see Fig. 1).
This allows one to interprete a noisy, measurement-based implementation of an entanglement purification protocol or a quantum repeater as additional noise acting on the input states followed by the perfect protocol and noise on the output qubits. This is due to the fact that the resource states for such protocols have only input and output qubits (see above) and the processing of the input states is performed via Bell measurements. For more details see43.
Multipartite quantum hashing protocol
Quantum hashing protocols28,29,38,44,45,46,47,48 are a type of entanglement purification protocol. They are based on the quantum analogon of the noiseless coding theorem49,50 and rely on the fact that it is exponentially likely that the input states are in a so-called likely subspace. One notable feature of the hashing protocols is that, unlike recursive entanglement purification approaches (e.g.39,40), they can deterministically provide a non-zero asymptotic yield. Unfortunately due to the nature of operations required, a gate-based implementation cannot tolerate any imperfections in the operations. However, recently it was shown that a measurement-based implementation makes hashing protocols practical in the presence of imperfections27.
In this work we use the measurement implementation of the multipartite quantum hashing protocol described in28,29, which works for graph states. The most prominent difference to the bipartite case is that to purify a k-colorable graph state one separate subprotocol for each color is necessary to obtain all the necessary information29.
We will briefly describe the basic mechanisms of the bipartite hashing protocol and discuss how the multipartite hashing protocol differs from the bipartite case and what challenges arise from them. Consult the supplementary material for additional details on estimating fidelities and28,29 for details on the multipartite hashing protocol.
The bipartite protocol that we consider here38 roughly works as follows: Starting from n input copies of a noisy Bell state ρ with sufficiently high fidelity with respect to the desired Bell state \(|{{\rm{\Phi }}}^{+}\rangle \), we want to extract m copies of the perfect \(|{{\rm{\Phi }}}^{+}\rangle \) state. First, the possible Bell states are encoded as ai = 00, 01, 10, 11 for \(|{{\rm{\Phi }}}^{+}\rangle ,|{{\rm{\Psi }}}^{+}\rangle ,|{{\rm{\Phi }}}^{-}\rangle ,|{{\rm{\Psi }}}^{-}\rangle \) respectively and the coefficients of ρ⊗n can be interpreted as probabilities of being in a state corresponding to a bitstring \(\tilde{a}={a}_{1}{a}_{2}\ldots {a}_{n}\). Now one proceeds to measure random subset parities to determine the string \(\tilde{a}\). Such a measurement is performed by applying bilateral CNOT operations to accumulate parity information of the ensemble onto one Bell pair and then measuring it. This approach works because one does not have to consider all possible strings \(\tilde{a}\). Since it is exponentially likely that \(\tilde{a}\) will lie in the likely subspace, one only needs to differentiate between those strings. It is possible to obtain m = n(1 − S(ρ) − 2δ) output copies this way, where S(ρ) is the von Neumann entropy of ρ and δ > 0 is allowed to approach 0 as n tends to infinity. For n → ∞ one can deterministically obtain a yield of Y = m/n = 1 − S(ρ). For finite n however, there is a chance that the bitstring \(\tilde{a}\) either falls outside of the likely subspace or cannot be successfully distinguished from other bitstrings in the likely subspace. This case is especially relevant for this work as we want to consider scenarios with limited storage capacities, i.e. small n. One can find a lower bound for the success probability23,30, which leads directly to a lower bound f(a, n, δ) for the global fidelity, i.e. the overlap of the output pairs with \(|{{\rm{\Phi }}}^{+}{\rangle }^{\otimes m}\). While δ can be chosen freely in this context, it is important to consider that δ is directly connected to the number of output pairs m.
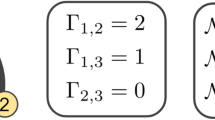
For the multipartite protocol28,29 one can enumerate the states in the graph state basis (see (2)) in a similar way as with the different Bell states previously. However, the main limitation one faces is that arbitrary substring-parities cannot be extracted via local measurements. Therefore, one has to consider subset parities separately and employ one subprotocol per color. Rather than dealing one bitstring \(\tilde{a}\) for the whole ensemble, one considers one separate bitstring for each vertex in the graph, e.g. \({a}^{(k)}={a}_{1}^{(k)}\ldots {a}_{n}^{(k)}\) for the k-th vertex. To learn each of these strings, one performs multilateral CNOT operations that accumulate subset parity information in one copy of the ensemble and perform stabilizer measurements corresponding to one color of the graph. The parity information of all bitstrings corresponding to one color can be extracted simultaneously, which is why the number of required subprotocols is given by number of colors in the graph.
The relevant entropy associated to the bitstring a(k) is the entropy of the k-th bit in the graph state basis vector:
where \({\lambda }_{k,i}={\sum }_{{\mu }_{j\ne k}}{\lambda }_{{\mu }_{1}\ldots {\mu }_{k-1}i{\mu }_{k+1}\ldots {\mu }_{N}}\) is the probability that the k-th bit in the graph state basis vector μ equals i. The whole protocol can only be considered successful if all the separate bitstrings are identified correctly, therefore we obtain a lower bound for the overall fidelity \({\prod }_{k}f({a}^{(k)},{\delta }_{k})\). For two-colorable graph states the asymptotic yield is given by \(Y={\rm{l}}{\rm{i}}{{\rm{m}}}_{n\to \infty }m/n=1-{S}_{A}-{S}_{B}\), where \({S}_{A}={{\rm{\max }}}_{k\in A}{S}_{k}\) and \({S}_{B}={{\rm{\max }}}_{k\in B}{S}_{k}\) for vertices in colors A and B, respectively.
Schemes to establish multipartite states in a quantum network
We consider a quantum network, i.e. a set of spatially separated parties that are connected via quantum channels. The parties are equipped with storage devices (quantum memory), and are capable to manipulate their stored states. We assume that the transmission between parties takes place via a noisy quantum channel with error parameter q, while the local manipulation is done in a measurement-based way. There, we assume noisy resource states with local noise per qubit specified by error parameter p. The goal is to establish multipartite entangled states, specifically some graph states, shared between all (or some of the) parties. We will consider this problem in different settings: First, when storage is unlimited and we are interested in scaling of resources and overhead only. Second, in a scenario where storage is limited (either in total, or at each station).
The schemes we propose here are capable to establish multiple copies of graph states over arbitrary distance, with an optimal scaling. The overhead per transmitted state is only constant. In this sense, our schemes are a generalization of the 1D repeater scheme of ref.23 that allows one to establish Bell pairs between two distant parties to arbitrary target states and network geometries. The key element of our scheme is the generation of elementary building blocks, which are then purified via hashing, and merged or connected. In contrast to recurrence-based repeater schemes, no nesting or repeater levels–which lead to polynomial or polylogarithmical scaling of resources with the distance–are required. The fast convergence of the hashing protocol to maximally entangled states allows one to connect or merge all elementary building blocks in a single step, and obtain multiple copies with an overhead per transmitted qubit that is constant.
These elementary building blocks could be Bell pairs shared between neighboring parties, or also multi-party states such as GHZ or cluster states. The crucial observation here is that the aforementioned properties of the hashing purification protocol for Bell-pairs, i.e. finite yield and exponentially fast convergence towards unit fidelity, also hold for the multipartite hashing protocol. Hence these states can be merged or connected in an arbitrary way. In the following we describe the three schemes for purifiying multipartite graph states as outlined in Sec. 1. All schemes have in common that their ultimate goal is to obtain a fixed multipartite entangled state after their completion, for example a 3-party GHZ state shared between distant parties, or a cluster state shared between all parties of the network. The schemes differ in the elementary building blocks, i.e. whether they work with multipartite entangled states (scheme A), or with bipartite entangled states (schemes B and C). In addition, the purely bipartite scheme (B) performs purification and merging/connection in two separate steps, while in schemes A and C these two steps are performed simultaneously in a measurement-based implementation. This is in fact crucial to obtain a scalable scheme. At intermediate stations the perfect hashing plus connection/merging is performed on a slightly noisier input state, and no additional errors are introduced as there are no output particles. In contrast, when performing hashing and connection/merging in two steps, additional noise on output states is introduced, and leads to a (exponentially) vanishing fidelity when combining multiple elementary building blocks. The schemes also differ in their storage requirements, as storing a multipartite state requires less memory than the storage of Bell pairs shared between different parties.
Scheme A
In scheme A the stations of the network share several copies of a noisy multipartite entangled state with neighbouring stations. Furthermore, each station prepares a resource state for the measurement-based implementation of the hashing protocol for two-colorable graph states (end nodes), or hashing followed by state merging or state connection at intermediate nodes. Each station of the network now couples the copies of the multipartite entangled state to the resource state via Bell-measurements, thereby purifying the states (see Fig. 2a), and merging or connecting the output states. As long as the initial fidelity (and fidelity of resource states) is sufficiently large, the protocol deterministically generates several copies of multipartite entangled target states.
The figure depicts the different schemes we consider. (a) Starting with multiple copies of a multipartite state (GHZ states in this example) each station implements the multipartite hashing protocol (marked by the orange box) in a measurement-based way to obtain fewer copies of that state with higher fidelity. (b) Before the protocol neighboring stations share several copies of Bell pairs. The stations implement the bipartite hashing protocol (orange boxes) in a measurement-based way to obtain purified Bell pairs. Then, in a separate step, the stations prepare another resource state for merging the Bell-pairs (blue box) into the desired multipartite state. (c) The neighboring stations share, like in scheme B, several copies of noisy Bell pairs. Each station performs the measurement based implementation of the multipartite hashing protocol (orange boxes) or the hashing protocol combined with the merging operation (purple box) where connections are needed.
Scheme B
In contrast to scheme A all neighbouring stations share impure Bell-pairs in scheme B. This scheme comprises the following steps: First, each station prepares several copies (one for each neighbouring station) of the resource state for the measurement-based implementation of the hashing protocol for Bell-pairs. Next, each station couples the resource states to the impure Bell-pairs via Bell-measurements, thereby performing the hashing protocol. Assuming the initial fidelity is sufficiently high, one obtains fewer, but purified copies of Bell-pairs. Finally, depending on the multipartite target state, the stations merge or connect the purified Bell-pairs to obtain copies of the multipartite state (see Fig. 2b). This is done in a separate step that requires an additional resource state for the measurement-based connection of the Bell-pairs.
Observe that noise will act in this scenario at two steps: noise from the hashing protocol, and noise from the merging operation. In addition, one needs to store qubits corresponding to Bell states shared between all neighboring parties instead, which leads to a larger storage requirement for this scheme.
Scheme C
Finally we discuss scheme C, which is a combination of the bipartite and multipartite approach. In particular, we can obtain a combined resource state for both the bipartite hashing protocol and the merging or connection operation applied afterwards. This state can be readily obtained by virtually combining the two resource states via Bell-measurements. This leads to a smaller resource state which performs both tasks within a single step (see Fig. 2c). This has the advantage that noise from imperfect resource states will act only once, in contrast to scheme B where noise will act on the output of the purification protocol twice. Note that the architecture has to be flexible enough to generate different resource states depending on the desired graph state to profit from this advantage in general. The scheme however works with initial Bell pairs as input states, and hence has the same memory disadvantage as scheme B when compared to the truly multipartite scheme A.
Scaling of schemes
We now discuss the scaling of the local resources of the different schemes. We are interested in the scaling with the distance of the number of qubits which need to be stored/processed at each repeater station in order to obtain a target state with a fidelity exceeding a fixed value. For the fidelity we choose the global, private fidelity Fgp, which is the fidelity of the ensemble of output target states prior to the action of the noise on the output qubits of the resource states relative to the desired tensor product of target states (for more details see23,30).
From this one can already see that scheme B is not scalable because for any non-zero value of noise one obtains Bell pairs with non-unit fidelity. These pairs are then further processed and the fidelity will drop similar to the case of swapping imperfect Bell pairs. The situation is different for scheme A and C, where the purification of elementary states and their further processing (merging) are executed in a single, simultaneous step. Here, a lower bound on the global, private fidelity Fgp can be obtained from the probability that all hashing protocols in the entire quantum repeater protocol succeed simultaneously. For a quantum repeater where N states are merged one obtains
for a sufficiently large number n. Here n is the number of input states of the hashing protocol and α and β depend on properties of the input states and certain choices within the hashing protocol. More details can be found in the supplementary material. One can ensure that Fgp is close to one, i.e., \({F}_{{\rm{gp}}}\ge 1-\varepsilon \) by choosing n such that \(N\alpha \exp (\,\,-\,\beta {n}^{\mathrm{1/2}}) < \varepsilon \). This shows that one has to choose the number of input states according to N (which is usually related to the distance) and the desired fidelity. For larger values of N one will require (logarithmically) larger values of n. Note, however, that this will also lead to a larger number of output states m. Thus the overhead, i.e. the ratio \(\tfrac{n}{m}\), becomes constant for large n, which is the optimal scaling.
We emphasize that this result is in contrast to previous schemes based on recurrence protocols that have polynomially or polylogarithmically scaling overheads.
Application to a limited storage scenario
Here, we address a setting with memory restrictions, which are crucial to consider for practical implementations. In particular, we consider a situation where the memory sizes of the intermediate repeater stations are limited. This implies that an efficient strategy for memory usage and consumption needs to be applied to obtain the target state with highest possible fidelity. Due to the nature of the hashing protocols, the estimated fidelities with a limited amount of input copies are only bounds (see supplementary material).
In Sec. 4.1 we investigate the application of the multipartite hashing protocol to GHZ states and discuss the distribution of a 3-qubit GHZ state over long distances. Then, in Sec. 4.2, we investigate multiple scenarios of generating two-dimensional and three-dimensional cluster states from smaller building blocks. Since the memory usage is of utmost importance, we identify building blocks for cluster states that need to store as few qubits as possible in section 4.2.1.
3-qubit GHZ state
To begin the comparison between multipartite and bipartite approaches, we investigate the application of the multipartite hashing protocol to the 3-qubit GHZ state. The GHZ state is a truly multipartite entangled state and furthermore it is local-Clifford equivalent to a two-colorable graph state (see Fig. 2a), which allows the direct application of the hashing protocol for graph states. The GHZ state makes for an interesting graph state to analyze not only because of its simplicity but it is also at the core of the GHZ based two-dimensional repeater scheme of26. First, we take a look at input states for which each qubit has been affected by local depolarizing noise with parameter q. This corresponds e.g. to a situation where a perfect GHZ or Bell pair is generated locally by some source, and the states are distributed via noisy channels to the parties that are involved in the protocol.
Even in this simple model the storage advantage of employing a multipartite approach becomes apparent. When relying only on Bell pairs (scheme B), the station, where the Bell pairs are connected to obtain the final GHZ state, needs to store twice as many qubits. This means that for each separate bipartite hashing protocol between the different parties only half as many copies (when compared to scheme A) of Bell states will be available if the storage capacity of the stations is limited. However, for this particular case the storage advantage is not sufficient for the multipartite approach to obtain better fidelities when using the hashing protocol as a n → 1 protocol, which is done by choosing δA and δB such that the number of output copies m = 1. (The advantage of looking at the n → 1 variant is that the output fidelity directly corresponds to the state fidelity. However, the usual use case of the quantum hashing protocol is when multiple output copies are required.) These results are depicted in Fig. 3 for a fixed choice of q = 0.98.
When considering imperfect resource states, we can see an interesting development depending on whether the bipartite approach is given the information of what the target state is before building the resource states (scheme C), see Fig. 4. If the bipartite approach is not able to adapt to different output states (scheme B), the states will need to be connected afterwards, which exposes them to additional noise. Therefore, the qubits at the station connected to the two other parties will be affected by additional noise after the purification has taken place. If this step is also implemented in a measurement-based way, the additional noise takes the form of the imperfections in the extra resource state that needs to be created to perform the connection. In Fig. 4 it is obvious that the reachable fidelity of such a bipartite approach that is oblivious to the final use of their purified states has a smaller reachable fidelity than the multipartite approach. If the bipartite approach is allowed to use custom resource states that implement the bipartite hashing protocol as well as the connection operation, which we called scheme C, then the bipartite approach is superior for this case.
Restricted error model
We consider a restricted error model for the graph state version of the GHZ state and n → 1 protocols. The main reason why the multipartite approach performs worse is that a separate protocol is needed for each of the two colors, which the small storage advantage in this scenario is not able to overcome. Now, we look at a situation where the noise only affects one color, namely only Z-noise acting on the outer two qubits (the qubits at the dangling ends on the right in Fig. 2a). This situation could e.g. arise when distributing two qubits of a locally generated GHZ state via a noisy channel where dephasing is predominant, and the channel can be described by a phase-flip channel.
In this case the second protocol is not needed and the storage advantage immediately translates to higher reachable fidelities as shown in Fig. 5.
However, if there is an additional, small amount of X-noise, also only acting on the outer qubits, it becomes mandatory to use the second subprotocol. We describe the action of the noisy channel by:
In this case with very asymmetric noise, it is important to distribute the additional input states that we have available in a n → 1 protocol appropriately among the subprotocols, i.e. choosing the same δ for both subprotocols (i.e. δA = δB) is a bad choice in this case. Figure 6 illustrates that in such a situation some of the advantage of the multipartite approach (A) still remains. It highlights in particular that much can be gained by optimizing the distribution of the leftover copies, i.e. the choice of δA and δB for the different subprotocols. For local depolarizing noise, which is symmetric, the improvement gained by the optimization is negligible.
Long-distance GHZ on triangular network
One way we can use the multipartite hashing repeater scheme is for distributing an entangled state over long distances. Exemplary we look at distributing a long-distance GHZ state with repeater stations arranged on a triangular grid as depicted in Fig. 7, similar to the setup in26.
While using the measurement-based implementation, which combines hashing and connecting the resulting states into a single step, asymptotically provides a scalable and deterministic protocol, in contrast to26 we cannot make use of the error detection process from using additional information gained at intermediate steps. Also, as we consider a scenario with limited storage and therefore the high amount of GHZ states used leads to a fidelity estimate by \({F}_{{\rm{GHZ}}}^{{3}^{k}}\) where \(k={\mathrm{log}}_{2}L\) of the desired length L in multiples of the elementary distance between stations on the triangular grid. In the bipartite (B) and hybrid (C) case one obtains \({F}_{{\rm{bip}}}^{{2}^{k+1}}\), which makes it clear that the advantage the multipartite approach (A) might have at small distances does not scale well for long distances. In Fig. 8 one can see that the multipartite advantage is relevant for a short distances, but loses its advantage at longer distances.
Comparing the reachable fidelities of n → 1 protocols for the multipartite scheme and the fully bipartite scheme for different numbers of repeater levels with a storage capacity of 1600 qubits at each repeater station. The inital states are affected by local depolarizing noise with error parameter q = 0.99 and the resource states with error parameter p = 0.98 on each qubit.
Cluster state
Rather than distributing the same state over longer and longer distances, one can also consider a setup where the goal is to generate a state with a growing number of parties. To illustrate this mode of operation we consider building up large 2D and 3D cluster states from smaller building blocks.
Building blocks for cluster states
In this section we present an approach for creating a 2D cluster state by merging smaller building blocks. We will arrive at two classes of building blocks, which we term windmill and shifter grid. They have in common that they reduce the required local storage capacity by a factor of two as compared to a strategy based on entangled pairs only.
Let us start with a grid of Bell pairs as shown in Fig. 9a. If all stations merge their respective qubits we obtain a cluster state, which corresponds to the bipartite strategy. Note that at each node, four qubits need to be stored. That is, if a station is capable of storing n qubits, the number of initial copies for the entanglement distillation protocol is n/4.
(a) One can create a cluster state from a grid of Bell-pairs by merging them (orange rectangles). The numbers indicate how many qubits need to be stored at each of the stations. (b) Optimizing the storage required at the stations by using multipartite states: For the red qubits (GHZ-states) and the green qubits (2 colorable graph state) the entanglement distillation protocol for two colorable graph states are employed. The red numbers indicate where we have reduced the number of qubits which need to be stored at the station.
However, it is possible to consider different kinds of initial states to cover the whole grid such that combining the building blocks still results in a cluster state. In particular, any set of elementary building blocks that is obtained by merging some of the initial Bell-pairs in a grid can be used. Such covers of the cluster state, consisting of possibly several different substructures, can be highly irregular and one possible choice is shown in Fig. 9b. Already from this example it is apparent that multipartite states can effectively reduce the storage capacity needed by the stations.
Essentially, we have to identify covers that provide favorable storage requirements, ideally only needing to store two qubits at the borders of the elementary building blocks, so one can use n/2 initial copies for the multipartite entanglement purification protocol if each station can store n qubits. This advantage is important as the fidelity of the output state after entanglement distillation strongly depends on the available number of initial states.
We follow the idea of identifying possible configurations using two instead of four qubits at each station and we obtain two classes that form distinct blocks which are invariant under rotations with an angle of π/2. The idea is straightforward: one considers four neighboring stations, each storing four qubits belonging to Bell-pairs connecting them. Then, one merges these four qubits into two, thereby obtaining a small subgraph. By rotating this subgraph with an angle of π/2 four times one obtains a building block.
Figures 10 and 11 show the windmill and shifted grid classes of building blocks as well as how these can be extended to larger building blocks, which have some central stations that only need to store one qubit per copy. These approaches can also be extended to 3D cluster states where we find coverings that use cubes instead of squares. The windmill blocks need to be modified to fit the 3D cluster but some stations will need to store 3 qubits per copy as the neccessary dangling ends cannot be arranged in a better way. Here, the shifted grid approach shows that it scales very well to higher dimensions as the required graph states are simply cubes connected at each corner and only 2 qubits per copy need to be stored at each station.
2D-cluster building blocks in a windmill formation with a block size of (a) two or (b) four. (c) The blocks can be connected to a larger cluster state. The connection operations are performed on the qubits in the rectangles, which are stored at the same repeater station. Note that only two qubits per copy need to be stored at each location.
Construction from smaller blocks
We investigate using different schemes of constructing a 64 × 64 2D-cluster state with periodic boundary conditions from smaller building blocks. We compare the approaches using the windmill and shifted grid building blocks (Figs 10 and 11 respectively), which are both different variants of the multipartite approach (scheme A), and the bipartite approach (scheme B). Again, we use a straightforward error model of local depolarizing noise with error parameter q acting on each qubit of the initial state. In this section we do not include noisy resource states as this only leads to a lower reachable fidelity for the purely bipartite scheme (B). Note that without imperfections in the resource states, schemes B and C are equivalent.
First, let us consider a scenario where the storage capacity per location is limited. The achievable fidelities for a n → 100 protocol are depicted in Fig. 12a and b. While for the 2D cluster state the storage advantage is only a factor of two it is still very relevant.
Comparison of numerical results for generating 64 × 64 cluster states from smaller building blocks with hashing protocols using different architectures. (a) Reachable fidelities with local storage capacities of 1200 qubits for n → 100 protocols. (b) Difference in fidelity Fsg − Fbip between the shifted grid architecture Fsg and the bipartite scheme Fbip for n → 100 protocols. The red area signifies the parameter regime where the multipartite approach (A) achieves higher fidelities. The advantage of the multipartite approach for scenarios with low noise and very limited storage becomes apparent. (c) Number of output copies which can be provided with a fidelity of at least 0.9 with local storage capacities of 1200 qubits. Here the multipartite approach shows better scaling for low error rates. (d) Difference in obtainable output copies msg − mbip with a fidelity of at least 0.9 by the shifted grid architecture msg (A) and the bipartite approach mbip (B, C).
Alternatively, instead of fixing the number of outputs, a practical question to ask is how many output pairs we can expect while still staying above a certain threshold fidelity. In Fig. 12c and d the achievable number of output copies while keeping above a global threshold fidelity of 0.9 is shown. Here it becomes clear that for q close to 1 the multipartite approaches can deliver more copies.
The same analysis is also extended to a 3D cluster states of size 64 × 64 × 64. See Fig. 13 for the reachable fidelities and obtainable output copies in that case. Here the differences between the windmill and shifted grid blocks become more pronounced, as the shifted grid architecture allows to obtain a storage advantage of factor three while the windmill blocks only allow to store twice as many copies as in the bipartite approach. This is the reason why the shifted grid architecture performs very well in the three-dimensonal case.
Comparison of numerical results for generating 64 × 64 × 64 cluster states from smaller building blocks with hashing protocols using different architectures. (a) Reachable fidelities with local storage capacities of 1800 qubits for n → 100 protocols. (b) Difference in fidelity Fsg − Fbip between the shifted grid architecture Fsg and the bipartite scheme Fbip for n → 100 protocols. The red area signifies the parameter regime where the multipartite approach (A) achieves higher fidelities. (c) Number of output copies which can be provided with a fidelity of at least 0.9 with local storage capacities of 1800 qubits. Here the multipartite approach shows better scaling for low error rates. Difference in obtainable output copies msg − mbip with a fidelity of at least 0.9 by the shifted grid architecture msg (A) and the bipartite approach mbip (B, C).
Building blocks with globally limited storage
However, if one increases the block sizes, only the few repeater stations at the edges of the blocks need to store multiple qubits per copy. This means that if the system is limited by the total available storage rather than the storage per repeater station, the multipartite approach can benefit from this. This situation is akin to classical hard drives that are modular and can be moved to different servers depending on the requirements. Figure 14 depicts the results for a two-dimensional cluster state. Here it becomes apparent that larger block sizes allow one to obtain an even bigger advantage. Another interpretation is that since the additional storage is only needed at the stations at the edge of the blocks, using a multipartite approach allows one to achieve the same or better result by only upgrading some of the locations with additional storage.
Comparison of generating 64 × 64 cluster states from smaller building blocks when the storage capacity of 1200 × 642 qubits can be freely distributed among the involved stations. The multipartite approaches can profit from distributing the storage for more qubits to critical stations at the edges of the building blocks while the bipartite protocol cannot. (a) Reachable fidelities for n → 100 protocols. (b) Number of output copies that can be provided with a fidelity of at least 0.9.
Similarly, Fig. 15 shows the results for the 3D cluster state when the storage capacity is limited globally. Interestingly, increasing the complexity of the building blocks actually makes them more vulnerable to noise at first as suddenly there are qubits with six neighbors in the input state. However, at larger block sizes the overwhelming storage advantage proves advantageous.
Comparison of generating 64 × 64 × 64 cluster states from smaller building blocks when the storage capacity of 1800 × 643 qubits can be freely distributed among the involved stations. (a) Reachable fidelities for n → 100 protocols. (b) Number of output copies that can be provided with a fidelity of at least 0.9.
Construction directly from Bell pairs
Rather than relying on smaller building blocks, this model uses only Bell pairs with a noise model that has a clear physical interpretation. Bell pairs that are distributed between neighboring parties by sending one of the qubits through a noisy channel modeled by local depolarizing noise. We compare a bipartite approach where the Bell pairs are purified and then connected to a cluster state in the end and a multipartite approach where the Bell pairs are connected first, so only one qubit per site and copy needs to be stored, which consequently is purified using the multipartite hashing protocol. This intermediate step of storing the qubits is sensible for setups with imperfect storage capabilities because storing the resource state for the measurement-based implementation of the hashing protocol over long time periods is undesirable as any noise affecting the output qubits cannot be corrected.
The error pattern that arises from connecting these noisy Bell pairs where one qubit has been subject to local depolarizing noise with error parameter q can be described by the noise channel:
acting on every edge of the cluster graph. A detailed explanation can be found in the supplementary material. So the initial state for the multipartite entanglement distillation is given by:
where G is the graph associated with the cluster state.
In Fig. 16 the results for both the reachable fidelity and obtainable output copies for a 2D cluster with dimensions 64 × 64 are depicted. One can clearly see that considering the multipartite approach for this scenario is also very relevant if storage capacities are limited.
Comparison of multipartite (A) and bipartite (B, C) approach when distilling 64 × 64 cluster states generated directly from Bell pairs shared between adjacent parties where one half of the Bell pair is sent through a depolarizing noise channel with parameter q. (a) Reachable fidelity for n → 50 protocols with 800 qubits storage capacity at each station. (b) Difference in fidelity between the multipartite and the bipartite architecture fmulti − fbip. The red area signifies where the multipartite approach achieves higher fidelities. (c) Number of output copies which can be provided with a fidelity of at least 0.9 with local storage capacities of 800 qubits.
Arbitrary networks and generalization
The scheme for efficient generation of entangled states in a network that we have introduced and discussed for GHZ and cluster states can be generalized to other target states and network geometries. The key observation is that entanglement purification protocols for all graph states exist29. This includes recurrence protocols, but also breeding and hashing protocols. The latter ones allow for entanglement purification of a large ensemble with constant yield, and can be implemented in a measurement-based way. The private fidelity23 one can reach is arbitrarily close to one, approaching unit fidelity exponentially fast with the number of initial copies while the yield remains constant. This in turn allows one to connect and to merge arbitrary graph states in such a way that the final target state is generated with any desired target fidelity. It is essential that connection or merging processes are performed in the same step as the entanglement purification protocol, i.e. a single resource state implements both tasks. This leads to a drop in fidelity of the target state which can be lower bounded by \(\prod {F}_{i}\), where Fi are the (global) private fidelities of the connected or merged states, similarly as in the 1D case23. This can be compensated by using a logarithmically larger number of copies, where however the overhead per produced target state remains constant.
We start with the generalization of states with fixed number of qubits, but over larger distance as discussed in Sec. 4.1 for three-particle GHZ states. In this case one merges and projects out short-distance states in such a way that a long-distance state of the same kind is produced, i.e. self-similar structures of growing scale are generated. This requires a regular network whose topology is associated with the desired target state. This is called operational mode I in ref.26, where an example for the distribution of a 2D cluster-type state is described. The essential modification here is that hashing is used for entanglement purification for all states at once without nested levels, and is combined with the merging process in a measurement-based implementation. Some of the qubits are measured in this scheme, which is also combined with the purification process and implemented in a single step.
Also the scheme to generate cluster states shared between all nodes of a 2D square network can be generalized to networks with arbitrary geometry. This corresponds to operational mode II in ref.26, where again hashing is used for entanglement purification to obtain a scalable scheme with constant overhead. The goal is to generate a graph state that corresponds to the network structure. Consider as starting point a situation where Bell states are shared between all nodes of a network that are connected by edges. Notice that this is not the physical situation we consider, but rather used to illustrate the construction of elementary building blocks that are used. As discussed in Sec. 4.2.1, we can consider any merging of Bell pairs, regular or irregular, to generate elementary building blocks. These elementary building blocks are then purified and merged. All states generated in this way are graph states and can be purified via hashing. So for any choice of elementary building blocks, one obtains a scalable scheme with constant overhead, similarly as in the case of 2D and 3D cluster states. One can use small building blocks that are purified and merged, but also larger building blocks that are directly purified.
We finally remark that one can also consider the generation of graph states that do not correspond to the network geometry. There are two different graphs involved: a graph G corresponding to the network geometry, and a graph G′ corresponding to the target graph state. There are multiple ways to generate target graph states. One strategy is to use all edges in the set \(E\cap E^{\prime} \), i.e. the direct links, and establish the missing edges \(E^{\prime} \backslash (E\cap E^{\prime} )\) by using a path formed by subsets of the edges of E. In particular, if we use the edges on such a path (which corresponds to a quantum channel) to establish short distance Bell-pairs, we can generate a virtual Bell-pair for that missing edge by performing entanglement swapping on all short distance Bell-pairs. These virtual Bell pairs can then merged again in an arbitrary way to form elementary building blocks. (We remark that the elementary building blocks may also include vertices outside the vertex set V′ of the target graph state, e.g. to establish missing edges not in the set \(E\cap E^{\prime} \). For instance, if one wants to establish a 1D cluster state with additional edges of distance two in a 2D network, one can establish the additional edges by using nodes above and below the 1D line.) Any choice of elementary building blocks with subsequent entanglement purification and merging leads to an efficient, scalable scheme with constant overhead per generated target state, independent of the size and distance of the states.
Conclusion and Outlook
In this work, we introduced a repeater architecture for distributing multipartite entangled states in a quantum network with optimal scaling. The scheme is based on the multipartite quantum hashing protocol, where we make use of its fast convergence and favorable error thresholds in a measurement-based implementation. We have illustrated that the main elements that make quantum hashing an attractive tool for long distance point-to-point quantum communication23, namely constant overhead per node independent of the distance and non-zero yield, carry over directly to the application on multipartite graph states. Therefore, by applying this concept to all kinds of graph states we introduced a whole new class of protocols with optimal scaling. This includes the generation of long-distance states of few parties in regular networks, but also states shared between many or all parties by merging small elementary structures. A central element is to purify and merge in a single step using a measurement-based implementation, which leads to a scalable scheme with favourable error thresholds that enables one to transmit big quantum data.
We have also analyzed the performance in situations with limited resources. In particular, we considered situations where the global or local storage capacities are limited. In this case we found that using a multipartite or hybrid scheme offers advantages compared to approaches based on the distribution of entangled pairs using 1D repeaters. In particular, we constructed explicit schemes for generating 2D and 3D cluster states with minimal storage requirements per node, and also considered how to generalize this approach to a wide class of target states. The scheme we propose is based on the usage of a large number of copies, and hence requires a big infrastructure that might not be available in the near future.
We however believe that the analysis of network architectures with limited storage or other resources is of practical relevance also for near-term realizations of quantum networks. Also for networks with few nodes or small storage capacity, genuine multipartite approaches offer a storage advantage that might be harnessed. In this context, it would be particularly interesting to design network or repeater architectures for small-scale systems. This requires also the development of new, efficient entanglement purification protocols that operate on a small or medium number of copies, but offers similar advantages as the large-scale hashing protocols. We will report on such protocols elsewhere.
References
Briegel, H.-J., Dür, W., Cirac, J. I. & Zoller, P. Quantum Repeaters: The Role of Imperfect Local Operations in Quantum Communication. Phys. Rev. Lett. 81, 5932–5935, https://doi.org/10.1103/PhysRevLett.81.5932 (1998).
Ladd, T. D., van Loock, P., Nemoto, K., Munro, W. J. & Yamamoto, Y. Hybrid quantum repeater based on dispersive cqed interactions between matter qubits and bright coherent light. New Journal of Physics 8, 184 (2006).
Hartmann, L., Kraus, B., Briegel, H.-J. & Dür, W. Role of memory errors in quantum repeaters. Phys. Rev. A 75, 032310, https://doi.org/10.1103/PhysRevA.75.032310 (2007).
Sangouard, N., Simon, C., de Riedmatten, H. & Gisin, N. Quantum repeaters based on atomic ensembles and linear optics. Rev. Mod. Phys. 83, 33–80, https://doi.org/10.1103/RevModPhys.83.33 (2011).
Azuma, K., Tamaki, K. & Lo, H.-K. All-photonic quantum repeaters. Nat Commun 6, 6787, https://doi.org/10.1038/ncomms7787 (2015).
Pirandola, S. Capacities of repeater-assisted quantum communications. E-print: arXiv:1601.00966 [quant-ph] (2016).
Azuma, K. & Kato, G. Aggregating quantum repeaters for the quantum internet. Phys. Rev. A 96, 032332, https://doi.org/10.1103/PhysRevA.96.032332 (2017).
Knill, E. & Laflamme, R. Concatenated Quantum Codes. E-print: arXiv:quant-ph/9608012 (1996).
Zwerger, M., Briegel, H. J. & Dür, W. Hybrid architecture for encoded measurement-based quantum computation. Scientific Reports 4, 5364 (2014).
Muralidharan, S., Kim, J., Lütkenhaus, N., Lukin, M. D. & Jiang, L. Ultrafast and fault-tolerant quantum communication across long distances. Phys. Rev. Lett. 112, 250501, https://doi.org/10.1103/PhysRevLett.112.250501 (2014).
Bennett, C. H. et al. Teleporting an unknown quantum state via dual classical and Einstein-Podolsky-Rosen channels. Phys. Rev. Lett. 70, 1895–1899, https://doi.org/10.1103/PhysRevLett.70.1895 (1993).
Ekert, A. K. Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67, 661–663, https://doi.org/10.1103/PhysRevLett.67.661 (1991).
Lo, H.-K. & Chau, H. F. Unconditional security of quantum key distribution over arbitrarily long distances. Science 283, 2050–2056, https://doi.org/10.1126/science.283.5410.2050 (1999).
Hillery, M., Ziman, M., Bužek, V. & Bieliková, M. Towards quantum-based privacy and voting. Physics Letters A 349, 75–81, https://doi.org/10.1016/j.physleta.2005.09.010 (2006).
Xu, G.-B., Wen, Q.-Y., Gao, F. & Qin, S.-J. Novel multiparty quantum key agreement protocol with ghz states. Quantum Information Processing 13, 2587–2594, https://doi.org/10.1007/s11128-014-0816-9 (2014).
Sun, Z., Yu, J. & Wang, P. Efficient multi-party quantum key agreement by cluster states. Quantum Information Processing 15, 373–384, https://doi.org/10.1007/s11128-015-1155-1 (2016).
Sun, Z. et al. Multi-party quantum key agreement by an entangled six-qubit state. International Journal of Theoretical Physics 55, 1920–1929, https://doi.org/10.1007/s10773-015-2831-8 (2016).
Komar, P. et al. A quantum network of clocks. Nat Phys 10, 582–587, https://doi.org/10.1038/nphys3000 (2014).
Beals, R. et al. Efficient distributed quantum computing. Proceedings of the Royal Society of London A: Mathematical, Physical and Engineering Sciences 469 (2013).
Caleffi, M. Optimal routing for quantum networks. IEEE Access 5, 22299–22312, https://doi.org/10.1109/ACCESS.2017.2763325 (2017).
Munro, W. J., Stephens, A. M., Devitt, S. J., Harrison, K. A. & Nemoto, K. Quantum communication without the necessity of quantum memories. Nature Photonics 6, 777 EP–(2012).
Muralidharan, S. et al. Optimal architectures for long distance quantum communication. Scientific Reports 6, 20463 EP–(2016).
Zwerger, M., Pirker, A., Dunjko, V., Briegel, H. J. & Dür, W. Long-Range Big Quantum-Data Transmission. Phys. Rev. Lett. 120, 030503, https://doi.org/10.1103/PhysRevLett.120.030503 (2018).
Kruszynska, C., Anders, S., Dür, W. & Briegel, H. J. Quantum communication cost of preparing multipartite entanglement. Phys. Rev. A 73, 062328, https://doi.org/10.1103/PhysRevA.73.062328 (2006).
Epping, M., Kampermann, H. & Bruß, D. Large-scale quantum networks based on graphs. New Journal of Physics 18, 053036 (2016).
Wallnöfer, J., Zwerger, M., Muschik, C., Sangouard, N. & Dür, W. Two-dimensional quantum repeaters. Phys. Rev. A 94, 052307, https://doi.org/10.1103/PhysRevA.94.052307 (2016).
Zwerger, M., Briegel, H. J. & Dür, W. Robustness of hashing protocols for entanglement purification. Phys. Rev. A 90, 012314, https://doi.org/10.1103/PhysRevA.90.012314 (2014).
Aschauer, H., Dür, W. & Briegel, H.-J. Multiparticle entanglement purification for two-colorable graph states. Phys. Rev. A 71, 012319, https://doi.org/10.1103/PhysRevA.71.012319 (2005).
Kruszynska, C., Miyake, A., Briegel, H. J. & Dür, W. Entanglement purification protocols for all graph states. Phys. Rev. A 74, 052316, https://doi.org/10.1103/PhysRevA.74.052316 (2006).
Pirker, A., Zwerger, M., Dunjko, V., Briegel, H. J. & Dür, W. Simple proof of confidentiality for private quantum channels in noisy environments. E-print: arXiv:1711.08897 [quant-ph].
Jiang, L. et al. Quantum repeater with encoding. Phys. Rev. A 79, 032325, https://doi.org/10.1103/PhysRevA.79.032325 (2009).
Cuquet, M. & Calsamiglia, J. Growth of graph states in quantum networks. Phys. Rev. A 86, 042304, https://doi.org/10.1103/PhysRevA.86.042304 (2012).
van Meter, R., Touch, J. & Horsman, C. Recursive quantum repeater networks. NII Journal 65–79, https://doi.org/10.2201/NiiPi.2011.8.8 (2011).
Pirker, A., Wallnöfer, J. & Dür, W. Modular architectures for quantum networks. New Journal of Physics 20, 053054 (2018).
Briegel, H. J., Browne, D. E., Dür, W., Raussendorf, R. & Van den Nest, M. Measurement-based quantum computation. Nat. Phys. 5, 19–26, https://doi.org/10.1038/nphys1157 (2009).
Raussendorf, R. & Briegel, H. J. A One-Way Quantum Computer. Phys. Rev. Lett. 86, 5188–5191, https://doi.org/10.1103/PhysRevLett.86.5188 (2001).
Raussendorf, R., Browne, D. E. & Briegel, H. J. Measurement-based quantum computation on cluster states. Phys. Rev. A 68, 022312, https://doi.org/10.1103/PhysRevA.68.022312 (2003).
Bennett, C. H., DiVincenzo, D. P., Smolin, J. A. & Wootters, W. K. Mixed-state entanglement and quantum error correction. Phys. Rev. A 54, 3824–3851, https://doi.org/10.1103/PhysRevA.54.3824 (1996).
Bennett, C. H. et al. Purification of Noisy Entanglement and Faithful Teleportation via Noisy Channels. Phys. Rev. Lett. 76, 722–725, https://doi.org/10.1103/PhysRevLett.76.722 (1996).
Deutsch, D. et al. Quantum Privacy Amplification and the Security of Quantum Cryptography over Noisy Channels. Phys. Rev. Lett. 77, 2818–2821, https://doi.org/10.1103/PhysRevLett.77.2818 (1996).
Hein, M. et al. Entanglement in Graph States and its Applications. In Quantum Computers, Algorithms and Chaos, vol. 162 of Proceedings of the International School of Physics “Enrico Fermi”, 115–218 (2006).
Kesting, F., Fröwis, F. & Dür, W. Effective noise channels for encoded quantum systems. Phys. Rev. A 88, 042305, https://doi.org/10.1103/PhysRevA.88.042305 (2013).
Zwerger, M., Briegel, H. J. & Dür, W. Universal and Optimal Error Thresholds for Measurement-Based Entanglement Purification. Phys. Rev. Lett. 110, 260503, https://doi.org/10.1103/PhysRevLett.110.260503 (2013).
Chen, K. & Lo, H.-K. Multi-partite Quantum Cryptographic Protocols with Noisy GHZ States. Quantum Info. Comput. 7, 689–715 (2007).
Maneva, E. N. & Smolin, J. A. Improved two-party and multi-party purification protocols. E-print: arXiv:quant-ph/0003099
Hostens, E., Dehaene, J. & De Moor, B. Hashing protocol for distilling multipartite Calderbank-Shor-Steane states. Phys. Rev. A 73, 042316, https://doi.org/10.1103/PhysRevA.73.042316 (2006).
Glancy, S., Knill, E. & Vasconcelos, H. M. Entanglement purification of any stabilizer state. Phys. Rev. A 74, 032319, https://doi.org/10.1103/PhysRevA.74.032319 (2006).
Hostens, E., Dehaene, J. & De Moor, B. Stabilizer state breeding. Phys. Rev. A 74, 062318, https://doi.org/10.1103/PhysRevA.74.062318 (2006).
Shannon, C. E. A Mathematical Theory of Communication. Bell Syst. Tech. J. 27, 379 (1948).
Schumacher, B. Quantum coding. Phys. Rev. A 51, 2738–2747, https://doi.org/10.1103/PhysRevA.51.2738 (1995).
Acknowledgements
This work was supported by the Austrian Science Fund (FWF): P28000-N27 and P30937-N27.
Author information
Authors and Affiliations
Contributions
All authors (J.W., A.P., M.Z., W.D.) contributed to this paper.
Corresponding author
Ethics declarations
Competing Interests
The authors declare no competing interests.
Additional information
Publisher’s note: Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Electronic supplementary material
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Wallnöfer, J., Pirker, A., Zwerger, M. et al. Multipartite state generation in quantum networks with optimal scaling. Sci Rep 9, 314 (2019). https://doi.org/10.1038/s41598-018-36543-5
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-018-36543-5
This article is cited by
-
Conference key agreement in a quantum network
npj Quantum Information (2023)
-
Concurrence percolation threshold of large-scale quantum networks
Communications Physics (2022)
-
Encrypted speech retrieval based on long sequence Biohashing
Multimedia Tools and Applications (2022)
-
Genuine quantum networks with superposed tasks and addressing
npj Quantum Information (2021)
-
A high security BioHashing encrypted speech retrieval algorithm based on feature fusion
Multimedia Tools and Applications (2021)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.