Abstract
Motivated by multi-hop communication in unreliable wireless networks, we present a percolation theory for time-varying networks. We develop a renormalization group theory for a prototypical network on a regular grid, where individual links switch stochastically between active and inactive states. The question whether a given source node can communicate with a destination node along paths of active links is equivalent to a percolation problem. Our theory maps the temporal existence of multi-hop paths on an effective two-state Markov process. We show analytically how this Markov process converges towards a memoryless Bernoulli process as the hop distance between source and destination node increases. Our work extends classical percolation theory to the dynamic case and elucidates temporal correlations of message losses. Quantification of temporal correlations has implications for the design of wireless communication and control protocols, e.g. in cyber-physical systems such as self-organized swarms of drones or smart traffic networks.
Similar content being viewed by others
Introduction
Renormalization group (RG) theory elegantly addresses percolation in static networks1,2,3. Percolation refers to the existence of large connected components in a random graph. Specifically, for subgraphs of a regular lattice, a giant connected component emerges above a critical lattice filling fraction, thus marking a phase transition of percolation. Percolation theory has been applied to a range of phenomena, from fluid flow in porous materials to epidemic spreading4,5,6,7,8. In this paper, we apply RG theory to time-varying communication networks.
Our work is motivated by wireless communication networks that often exhibit unreliable links. There, a key question concerns the existence of a multi-hop path of simultaneously active links, which permits sending a message from a source to a destination node via one or several intermediate relay nodes. Real-world applications of particular relevance include self-organizing swarms of flying drones9, smart traffic networks of communicating cars10, and networks of cooperating robots in production lines11. Recent flooding and multi-path routing protocols were shown to be more reliable than traditional single-path routing in field experiments12,13. The emergence of ever larger wireless networks that serve as critical communication infrastructures for cyber-physical applications14 prompts the need for a theoretical understanding of message losses and their temporal correlations when using these protocols15. Widely used schemes to estimate the quality of a wireless link assume that message losses are uncorrelated in time16. But temporal correlations among losses render these estimates invalid, and hence may cause existing communication protocols and control algorithms to fail17,18. This question of temporal correlations of message losses falls into a recent, application-driven interest in time-varying networks19,20,21.
Here, we introduce a minimal model of percolation in time-varying networks, which captures key features of multi-path wireless communication with unreliable links. Most real-world applications exhibit fairly regular network topologies, such as swarms of drones flying in a formation9, or sensor arrays in smart production facilities. Thus, we consider the case of network nodes distributed on a regular lattice, connected by links that stochastically switch between being active or inactive with finite switching time. The case of two states per link, active and inactive, serves as illustrative example, and corresponds to, e.g. a data transmission rate of an individual link that is either above or below the threshold, which guarantees a certain quality of service. We ask for the existence of multi-hop paths consisting of simultaneously active links that connect a designated source and destination node. We assume that transmission delays are short compared to the stochastic switching time of individual links. Indeed, in low-power wireless networks, transmission times are at most a few milliseconds per link, whereas the stochastic switching times of links can be on the order of hundreds of milliseconds. Now, if one were just interested in the probability to find a multi-hop path at a single point in time, the question would reduce to a bond-percolation problem for a static network, where the probability of an individual link to be active plays the role of the lattice filling fraction. Previous mean-field descriptions have shown that this probability converges to 1 for large networks if the lattice filling fraction is above a critical value known as the percolation threshold5,8. However, mean-field descriptions cannot account for temporal correlations of message losses at the network level. This motivates us to extend classical percolation theory for static networks to the dynamic case by formulating an RG theory that provides effective switching rates at different coarse-graining levels of a network. Using this theory, we quantify how message losses are correlated in time. We thus assess the validity of a common practice to assume uncorrelated message losses during the design and analysis of wireless protocols and control loops17,18.
Model and Metrics
A minimal model of time-varying networks
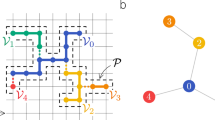
We consider a network (V, E) with nodes V and undirected edges \(E\subset V\times V\). Every edge represents a communication link that can be either active or inactive. Active links can relay information from one node to the next, while inactive links cannot. In each time step, a link can switch between the active and the inactive state with respective transition probabilities q I = qA→I and q A = qI→A, which corresponds to a time-discrete telegraph process, see Fig. 1(a). We assume that the switching dynamics of different links is uncorrelated, which is a valid assumption for the vast majority of links in real wireless networks18. Our goal is to accurately represent a given network (V, E) by a coarser version (V′, E′) with fewer nodes and links, while reproducing key metrics.
Renormalization of a two-link motif. (a) We consider communication links that can switch between an active and an inactive state with transition probabilities q I and q A . (b) The switching dynamics of a two-link motif can be well approximated by a single link with effective transition probabilities \({q^{\prime} }_{I}\) and \({q^{\prime} }_{A}\). (c) Waiting times for the transition I → A are approximately exponentially distributed for the two-link motif shown in (b). (d) Comparison of simulation results (solid line) and analytical results (dashed line) for the state correlation function given by Eq. (3) with slope −ln β′. (e) Comparison of simulation results (circles) and analytical results (solid line) for \({q^{\prime} }_{I}\).
Reliability
We define the reliability of a link as the probability Φ to find the link in the active state. In our two-state description, we have
Bernoulliness score
To characterize temporal correlations between states s n = s(t n ) of a link at different times t n = nΔt, we introduce a Bernoulliness score β
The probability P(sn+k = s n ) to find a link in the same state after k time steps is a function of the Bernoulliness β
The corresponding correlation time is τ = −Δt/ln β. For β = 0, the stochastic switching of a link becomes a memoryless Bernoulli process with τ = 0, whereas for β > 0 it retains memory and must be described as a Markov process.
Bernoulliness impacts the estimation of reliability
Temporal correlations in the state of a link become important, e.g. in protocols that estimate the link reliability Φ by observing the state of a link at n subsequent time steps. The estimate Φest = n A /n, where n A is the number of time steps for which the link is active, is itself a random variable. In the absence of temporal correlations with β = 0, the variance σ2(Φest) of Φest is given by
For β > 0, this result changes to
corresponding to a reduced effective number n β of independent time steps n β = −n/(2 ln β). The derivation of Eq. (5) as well as a comparison with simulations is given in the Supplementary Material text (SM) that accompanies this paper.
Renormlization theory of time-varying networks
Illustrating the method: renormalization of a two-link motif
We compute an effective Bernoulliness score for networks of arbitrary size. To illustrate the general procedure, we first consider the simple case of a chain of n = 2 links with a set of nodes E = {1, 2, 3} and a set of links V = {(1, 2), (2, 3)}, see Fig. 1(b). We say this network is active if the outermost nodes 1 and 3 are connected by a path of active links. In general, the state space is S = {A, I}n, where n = |E| denotes the number of nodes. The transition probabilities qs→s′ for a transition from state s ∈ S to a new state s′ ∈ S read
Here, the n’s denote the respective number of links that switch or retain their state, as indicated by the subscript, e.g., nA→I denotes the number of links that switch from active (A) to inactive (I) upon a change of state s to s′. The steady-state probability of state s reads
which defines a probability distribution \({{\bf{P}}}^{\ast }={\{{P}_{s}^{\ast }\}}_{s\in S}\). Here, n A and n I denote the number of active and inactive links in network state s, respectively.
For the example of the two-link motif, the set S A of active network states is simply S A = {AA}. The probabilities P A and P I for the network to be active or inactive at steady state are \({P}_{A}={\sum }_{s\in {S}_{A}}\,{P}_{s}^{\ast }\) and \({P}_{I}={\sum }_{s\in {S}_{I}}\,{P}_{s}^{\ast }\), respectively, where S I = S\S A denotes the set of inactive network states. The probability current JA→I from the active to the inactive state of the motif reads
and similarly for the probability current JI→A from the inactive back to the active state. Eq. (8) is exact in the absence of temporal correlations, β = 0, and represents a valid approximation in the case of temporal correlations, where the probability distribution of network states relaxes to P* on a time-scale τ, with correlation time τ = −Δt/ln β as it was introduced above. This motivates a replacement of the two-link chain by a single link with effective transition probabilities \({q^{\prime} }_{I}\) and \({q^{\prime} }_{A}\) with
see Fig. 1(b). For the two-link motif, we have \({q^{\prime} }_{I}={q}_{I}(2-{q}_{I})\) and \({q^{\prime} }_{A}={q}_{A}^{2}\mathrm{(2}-{q}_{I})/({q}_{I}+2{q}_{A})\). The renormalization map can be equivalently expressed in terms of an end-to-end reliability Φ′ and an end-to-end Bernoulliness β′ of the two-link network motif
Thus, we have approximated the Markovian dynamics with |S| = 4 states of the network motif by an effective two-state Markov model. Figure 1(c–e) compare these analytical results with numerical simulations, validating the applicability of this two-state approximation.
The linear chain
We can apply the above coarse-graining argument iteratively to a larger network, such as the linear chain of length n with set of nodes E = {1, 2, …, n + 1} and set of links V = {(1, 2), (2, 3), …,(n, n + 1)}. The only active network state that allows information transmission between the outer-most nodes 1 and n + 1 of the chain is AA … A. We consider the special case n = 2k for some integer k. By applying the renormalization map \(({q}_{I},{q}_{A})\to ({q^{\prime} }_{I},{q^{\prime} }_{A})\) k-times to a 2k-chain, we reduce the chain to a single link with effective transition probabilities \({q}_{I}^{[k]}\) and \({q}_{A}^{[k]}\), where the superscript [k] denotes the k-th iterate of the renormalization map. Explicitly,
For this simple example, we can also compute the effective transition probabilities for the n-link chain directly, using Eq. (9). Thereby, we recover the right-hand sides of Eq. (11) for arbitrary n, which validates our RG approach.
We now ask for the fixed points under the renormalization map, defined by \(({q^{\prime} }_{I},{q^{\prime} }_{A})=({q}_{I},{q}_{A})\). These fixed points correspond to special values of the transition probabilities of individual links, q I and q A , for which the two-link motif will have the same effective transition probabilities as its individual links. By induction, the same will hold true for the linear chain with n = 2k links. We find a trivial set of unstable fixed points with q I = 0, which corresponds to the case of perfect communication links with Φ = 1. Further, there is a unique stable fixed point (q I , q A ) = (1, 0), which corresponds to the case of permanently inactive links with Φ = 0. The end-to-end reliability of a linear chain with Φ > 0 converges to this stable fixed point as Φ[k] = Φn for increasing chain length n = 2k. This is consistent with the intuition that longer chains become more unreliable. Concomitantly, the end-to-end Bernoulliness converges as a geometric series to zero
Next, we apply a similar coarse-graining procedure to networks of node degree d > 2 that allow for multi-path routing.
Triangular networks
As an example, we consider an infinite triangular network with nodes \(V=\{m{{\bf{e}}}_{1}+n{{\bf{e}}}_{2}\in {{\mathbb{R}}}^{2}|m,n\in {\mathbb{Z}}\}\) on a lattice spanned by basis vectors e1 = (1, 0) and \({{\bf{e}}}_{2}=(1/2,\sqrt{3}/2)\) and corresponding set of links E, see Fig. 2(a). We define a sub-network (V′, E′), whose nodes correspond to the lattice spanned by new basis vectors \({{\bf{e}}{\boldsymbol{^{\prime} }}}_{1}={{\bf{e}}}_{1}+{{\bf{e}}}_{2}\) and \({{\bf{e}}{\boldsymbol{^{\prime} }}}_{2}=2{{\bf{e}}}_{2}-{{\bf{e}}}_{1}\), which is shown in blue in the same figure panel. This sub-network can be equivalently obtained by considering the original lattice as a tessellation by the 4-node motif shown in Fig. 2(b) and replacing each motif by a single link. This purely geometric procedure of network coarse-graining can be repeated.
Renormalization of a time-varying network on a triangular lattice. (a) Subsequent stages of network coarse-graining: gray (V, E), blue (V′, E′), red (V″, E″). (b) The 4-node motif used in the coarse-graining procedure. (c) Flow in (Φ, β)-space under the action of the renormalization group showing example trajectories (black), stable fixed points (solid circles), respective basins of attraction (rosé/green), and saddle node (Φ c , 0) = (1/2, 0) (half-filled circle). (d) Network iterates M k used in simulations. End-to-end reliability and Bernoulliness for iteratively fine-grained network motifs correspond to the renormalized reliability and Bernoulliness of individual effective links in coarse-grained networks, see Eq. (14). (e) Simulation results for end-to-end reliability Φ(M k ) and Bernoulliness β(M k ) for motifs M k .
Following an analogous procedure as for the two-link motif, we compute the end-to-end reliability Φ′ and end-to-end Bernoulliness β′ for the 4-node motif expressible in terms of a renormalization map
The renormalization map expresses the metrics of the network motif in terms of the metrics of the individual links it is composed of. The full analytic expression for Eq. (13) is given in the accompanying SM. We find that there exists a critical value \({{\rm{\Phi }}}_{c}^{{\rm{RG}}}=1/2\) such that the renormalized reliability decreases, Φ′ < Φ, if \({\rm{\Phi }} < {{\rm{\Phi }}}_{c}^{{\rm{RG}}}\), while it increases, Φ′ > Φ, if \({\rm{\Phi }} < {{\rm{\Phi }}}_{c}^{{\rm{RG}}}\). The critical value \({{\rm{\Phi }}}_{c}^{{\rm{RG}}}\) thus represents a percolation threshold: if the reliability of individual links is below this value, repeated application of the renormalization map Eq. (13) predicts a decreasing end-to-end reliability of networks of increasing size that converges to zero, whereas if the link reliability is above this value, the end-to-end reliability will converge to a perfectly reliable network. If Φ = 0 or Φ = 1, the analytic expression for β′ simplifies to β′ = β2.
Figure 2(d) summarizes the RG action in (Φ, β)-parameter space. We can analyze this RG action using concepts from dynamical systems theory. The point \(({{\rm{\Phi }}}_{c}^{{\rm{RG}}},\mathrm{0)}\) is a saddle node with unstable manifold given by β = 0 and stable manifold given by \({\rm{\Phi }}={{\rm{\Phi }}}_{c}^{{\rm{RG}}}\). This stable manifold serves as separatrix, separating the basins of attraction of two stable fixed points (0, 0) and (1, 0). Thus, repeated coarse-graining of an infinite triangular lattice will converge to a sub-lattice with perfectly transmitting links if and only if \({\rm{\Phi }} > {{\rm{\Phi }}}_{c}^{{\rm{RG}}}\), consistent with classical percolation theory22. Moreover, our analysis shows that the switching dynamics converges to a memoryless Bernoulli process on increasingly coarse-graining scales. Generally, the renormalized correlation time τ[k] after k coarse-graining steps satisfies τ > τ[k] ≥ τ/n, where n = 2k is the length of the shortest path between source and destination node. We have equality at the lower bound τ[k] = τ/n precisely in the limit cases of perfectly unreliable or perfectly reliable links, Φ = 0 and Φ = 1. For intermediate values of the link reliability Φ, 0 < Φ < 1, the correlation time τ[k] decays logarithmically as 1/ln(n) in the asymptotic limit of large n. Interestingly, the coefficient α1(Φ) in the polynomial expression \(\beta ^{\prime} ={\sum }_{i=1}^{5}\,{\alpha }_{i}({\rm{\Phi }}){\beta }^{i}\) is maximal at \({\rm{\Phi }}={{\rm{\Phi }}}_{c}^{{\rm{RG}}}\), implying that the asymptotic decay of temporal correlations is slowest right at the percolation threshold.
Simulations corroborate this picture. Figure 2(e) shows end-to-end reliability Φ(M k ; Φ, β) and Bernoulliness β(M k ; Φ, β) for iterated network motifs M k with link reliability Φ and link Bernoulliness β. Here, M0 is a single link, and M k is the motif, for which a single coarse-graining step gives Mk−1, see Fig. 2(c). We have
and analogously for β(M k ; Φ, β). Thus, the end-to-end reliability and Bernoulliness of iterated network motifs are approximately given by the effective reliability and Bernoulliness of individual links of iteratively coarse-grained networks. Deviations between RG theory and simulations stem from the fact that the 4-link motifs that are used to coarse-grain the network Mk+1 to the smaller network M k share common links. Consequently, switches of the effective links of M k are not completely uncorrelated to each other, as assumed in our RG calculation. The percolation threshold \({{\rm{\Phi }}}_{c}^{{\rm{RG}}}\) from RG theory overestimates the value Φ c ≈ 0.35 for a static triangular network23, a feature known from zeroth-order RG theory1.
The RG approach generalizes in a straight-forward manner to the case, where the switching rates are drawn from a distribution with given mean and variance, resulting in a renormalization of the distributions, see Fig. S2 in SM.
Our theory assumes that transmission and processing delays are much shorter than the time-scale of link switching, which is a realistic assumption. If each message would spend a non-zero processing delay at each node, we find that this delay has only a minor effect on the network Bernoulliness, provided the sending interval at which messages are injected into the network at the source node stays constant, see Fig. S3 in SM.
Other network topologies
Our general approach can be applied in a similar manner to other networks with varying node degree d, including regular 1-, 2-, and 3-dimensional lattices. Table 1 summarizes the results. As coarse-graining motif, we used a 2-link motif in the case of the linear chain, a 4-link motif in the case of the triangular lattice [see Fig. 2(b)], a 33-link motif consisting of 4 unit cubes in the case of the cubic lattice (see Fig. S4 in SM), and the lattice unit cell in all other cases.
In line with classical percolation theory, the end-to-end reliability Φ[k] converges to 0 with increasing number k of coarse-graining steps if \({\rm{\Phi }} < {{\rm{\Phi }}}_{c}^{{\rm{RG}}}\) for some critical value \({{\rm{\Phi }}}_{c}^{{\rm{RG}}}\) and converges to 1 otherwise. The number of multi-hop paths of given length between source and destination node increases with node degree d, which is reflected by lower values of the percolation threshold \({{\rm{\Phi }}}_{c}^{{\rm{RG}}}\). The end-to-end Bernoulliness β[k] predicted by RG theory converges to zero, yet at different speeds. For perfectly unreliable or perfectly reliable links, Φ = 0 or Φ = 1, β[k] decreases with a specific exponent in each coarse-graining step: we have \({\mathrm{lim}}_{{\rm{\Phi }}\to 0}\,{\beta }^{[k]}={\beta }^{ak}\), where a denotes the number of links in the shortest path connecting the source and the destination node of the coarse-graining motif, and \({\mathrm{lim}}_{{\rm{\Phi }}\to 1}\,{\beta }^{[k]}={\beta }^{bk}\), where b denotes the number of links starting from the source node in the coarse-graining motif (or the minimum of this number and the number of links starting from the destination node, in case these two numbers are different). Contrastingly, close to the percolation threshold \({{\rm{\Phi }}}_{c}^{{\rm{RG}}}\), temporal correlations decay only logarithmically, reflected by β′ ~ β.
Application case study: a swarm of communicating drones
As an application of our RG approach, we consider a simple model of a swarm of drones that communicate using short-range wireless radios9. Each drone diffusively explores a region around a fixed grid position (x0, y0) in two-dimensional space, see Fig. 3(a). The dynamics of its time-dependent position r(t) = (x(t), y(t)) shall follow an Ornstein-Uhlenbeck process \(\gamma \dot{x}(t)={x}_{0}-x(t)+\xi (t)\), where ξ(t) is white Gaussian noise with 〈ξ(t)ξ(t′)〉 = a2γδ(t − t′), and analogous dynamics for the y coordinate. This model matches a physical scenario where swarms of drones fly in regular formation with fluctuations in position due to, e.g. wind gusts and navigation imperfections. We assume that a pair of drones can communicate with a dynamic probability f(r) that is a function of the Euclidean distance r = |r i − r j | between the current positions r i and r j of the two drones. Indeed, this is a valid assumption in free-space aerial environments24. We choose a Hill function, f(r) = 1/[1 + (r/r0)h], with Hill coefficient h and half-saturation constant r0. We define an effective link reliability Φ as the time-averaged communication probability for a pair of drones at neighboring grid positions, Φ = 〈f(r)〉. A designated source drone sends messages in regular intervals of tsend.
A dynamic communication network of mobile drones. (a) Drones diffusively explore space around reference positions on a triangular grid (color-code: probability density of positions). A communication link between two drones is active with probability f(r), depending on their mutual distance r. (b) Representative time-series for the existence of an active link between two neighboring drones. (c) Correlation time τ for direct communication between drones 1 and 2 (gray squares), and end-to-end Bernoulliness β′ for multi-hop communication between 1 and 3 via 2 in panel (a) (blue circles). The red line shows β′ calculated from the observed β according to RG theory for the two-link motif. (d) End-to-end reliability Φ(M k ) and Bernoulliness β(M k ) for communication between source and destination nodes in network motifs M k [cf. Fig. 2(c)]. (e) Definition of modified flooding regions (rosé): these comprise all nodes within a distance M of the shortest path (red line) between source and destination node (red dots). (f) Values (Φ M , β M ) for multi-path routing, for increasing size M of modified flooding region. (g) Minimal value M95% to achieve an end-to-end reliability of at least 95% for three different distances l between source and destination node (l = 1: black, 2: red, 5: blue). Parameters: h = 20, γ/Δtsend = 100, D = 0.2a2/γ, with a lattice spacing, l = 2 in (f).
The correlation time for end-to-end communication along a single multi-hop path from simulations compares favorably to RG predictions based on values for a single link, see Fig. 3(c). For swarm motifs M k of increasing size k, we compute end-to-end reliability and Bernoulliness, see Fig. 3(d). We observe again key features predicted by RG flow: a percolation transition and slow reduction of temporal correlations.
Hence, for a routing protocol that uses flooding regions M k as suggested by our coarse-graining procedure, we find that transmission will be highly reliable provided two conditions are met (i) the network must be above the percolation threshold, Φ > Φ c , and (ii) the distance between source and destination node is sufficiently large, allowing for multiple renormalization steps. We now present a modified routing protocol that relaxes the second condition by enlarging the flooding region, thereby increasing the number of potential multi-hop paths. Specifically, exactly those drones shall relay the signal whose reference positions are within a distance M of the shortest path between the source and the destination node, see cartoon in Fig. 3(e).
Depending on whether the network is above or below the percolation threshold, the end-to-end reliability Φ M exhibits a qualitatively different behavior as function of M, see Fig. 3(e): For effective link reliabilities above the percolation threshold Φ > Φ c , the end-to-end reliability Φ M for flooding regions of increasing width M converges to 1, corresponding to reliable end-to-end transmission, while for link reliabilities above the percolation threshold Φ < Φ c , the end-to-end reliability Φ M converges to a fixed point Φ∞ with Φ∞ < 1. Remarkably, the end-to-end Bernoulliness β M converges to a non-zero value β∞, even for Φ > Φ c , in this case of a fixed distance between source and destination node. This highlights the role of hop distance for the decay of temporal correlations. We can ask for the minimal width M95% of flooding regions that ensures a specified end-to-end reliability, here chosen as 95% based on typical application requirements25, see Fig. 3(g). Remarkably, for effective link reliabilities Φ in a range [0.6, 1], M95% takes moderate values of 2–3, which are largely independent of both link reliability and the distance between source and destination node, thus suggesting a simple multi-path routing protocol of restrained flooding for robust wireless multi-hop communication.
Discussion
Here, we presented a percolation theory for time-varying networks, inspired by multi-hop communication in wireless networks with unreliable links. We introduced a minimal model of networks on regular lattices, where individual network links switch stochastically between active and inactive states. While active links can relay messages from one node to the next, message loss occurs at inactive links. With the help of this minimal model, we address the fundamental question of how temporal correlations of message losses for large communication networks scale with network size. To quantify these temporal correlations, we introduce a new metric of Bernoulliness. Our analytical theory allows to calculate end-to-end reliability and end-to-end Bernoulliness for networks of arbitrary size by repeated application of a renormalization map.
Full simulations of large time-varying networks are computationally expensive because long simulation times are required to accurately estimate network metrics. In contrast, the computational complexity of our approximative method to compute network metrics for large networks is independent of the size of the network, as the calculation only involves repeated application of the renormalization map, which is computationally cheap. The computational complexity for pre-computation the renormalization map scales at most as n(2n)2 if a network motif with n links is used as renormalization motif. Note here that we used the worst-case complexity of Dijkstra’s algorithm, which determines whether a given state of the motif is active or inactive.
Our analytical theory semi-quantitatively reproduces the scaling of key network metrics with network size in agreement with full numerical simulations of large time-varying networks. To the best of our knowledge, our theory is the first to address temporal correlations of message losses in time-varying networks and the first to harness methods of renormalization group theory to address this question of both fundamental and practical interest, featuring an application of theoretical physics to computer science.
In our minimal model, we considered only two states for each link, active and inactive, which serves as illustrative example of our RG theory. The theory can be extended to the case of a finite number of discrete states, e.g. for the data transmission rate of individual links exceeding a series of thresholds, corresponding to a rated quality of service.
Future work will explore refinements of the zeroth-order renormalization theory used here, e.g. cluster methods1,2,3, and generalizations to arbitrary Markov chains. We anticipate that percolation theory can guide the design of future wireless communication and control protocols that explicitly take into account temporal correlations of message losses.
References
Young, A. P. & Stinchcombe, R. B. A renormalization group theory for percolation problems. J. Phys. C 8, L535 (1975).
Reynolds, P. J., Klein, W. & Stanley, H. E. A real-space renormalization group for site and bond percolation. J. Phys. C 10, L167–L172, https://doi.org/10.1088/0022-3719/10/8/002 (1977).
Shapiro, B. Real-space renormalisation in the percolation problem. J. Phys. C 12, 3185–3195, https://doi.org/10.1088/0022-3719/12/16/007 (1979).
Broadbent, S. R. & Hammersley, J. M. Percolation processes: I. crystals and mazes. Math. Proc. Camb. Phil. Soc. 53, 629–641, https://doi.org/10.1017/S0305004100032680 (1957).
Essam, J. W. Percolation theory. Reports Prog. Phys. 43, 833–912, https://doi.org/10.1088/0034-4885/43/7/001 (1980).
Albert, R. & Barabási, A.-L. Dynamics of complex systems: Scaling laws for the period of boolean networks. Phys. Rev. Lett. 84, 5660–5663, https://doi.org/10.1103/PhysRevLett.84.5660 (2000).
Araújo, N., Grassberger, P., Kahng, B., Schrenk, K. & Ziff, R. Recent advances and open challenges in percolation. Europ. Phys. J. Special Top. 223, 2307–2321, https://doi.org/10.1140/epjst/e2014-02266-y (2014).
Saberi, A. A. Recent advances in percolation theory and its applications. Phys. Rep. 578, 1–32, https://doi.org/10.1016/j.physrep.2015.03.003 (2015).
Hayat, S., Yanmaz, E. & Muzaffar, R. Survey on unmanned aerial vehicle networks for civil applications: A communications viewpoint. IEEE Commun. Surv. & Tutorials 18, 2624–2661, https://doi.org/10.1109/COMST.2016.2560343 (2016).
Tubaishat, M., Zhuang, P., Qi, Q. & Shang, Y. Wireless sensor networks in intelligent transportation systems. Wirel. Commun. Mob. Comput. 9, 287–302, https://doi.org/10.1002/wcm.616 (2009).
Luvisotto, M., Pang, Z. & Dzung, D. Ultra high performance wireless control for critical applications: Challenges and directions. IEEE Transactions on Ind. Informatics 13, 1448–1459 (2016).
Ferrari, F., Zimmerling, M., Thiele, L. & Saukh, O. Efficient network flooding and time synchronization with glossy. In Proc. of the ACM/IEEE Int. Conf. on Information Processing in Sensor Networks (IPSN) (2011).
Chen, Y.-C. et al. A measurement-based study of multipath tcp performance over wireless networks. In Proceedings of the 13th ACM Internet Measurement Conference (IMC) (2013).
Rajkumar, R., Lee, I., Sha, L. & Stankovic, J. Cyber-physical systems: The next computing revolution. In Design Automation Conference, 731–736, https://doi.org/10.1145/1837274.1837461 (2010).
Zimmerling, M., Ferrari, F., Mottola, L. & Thiele, L. On modeling low-power wireless protocols based on synchronous packet transmissions. In Proc. of the IEEE Int. Symp. on Modeling, Analysis and Simulation of Computer and Telecommunication Systems (MASCOTS) (2013).
Baccour, N. et al. Radio link quality estimation in wireless sensor networks: A survey. ACM Trans. Sen. Netw. 8, 34:1–34:33, https://doi.org/10.1145/2240116.2240123 (2012).
Sinopoli, B. et al. Kalman filtering with intermittent observations. IEEE Transactions on Autom. Control. 49, 1453–1464, https://doi.org/10.1109/TAC.2004.834121 (2004).
Srinivasan, K., Dutta, P., Tavakoli, A. & Levis, P. An empirical study of low-power wireless. ACM Transactions on Senor Networks 6, 16:1–16:49, https://doi.org/10.1145/1689239.1689246 (2010).
Pan, R. K. & Saramäki, J. Path lengths, correlations, and centrality in temporal networks. Phys. Rev. E 84, 016105, https://doi.org/10.1103/PhysRevE.84.016105 (2011).
Holme, P. & Saramäki, J. Temporal networks. Phys. Reports 519, 97–125, https://doi.org/10.1016/j.physrep.2012.03.001 (2012).
Valdano, E., Ferreri, L., Poletto, C. & Colizza, V. Analytical computation of the epidemic threshold on temporal networks. Phys. Rev. X 5, 021005, https://doi.org/10.1103/PhysRevX.5.021005 (2015).
Bollobás, B. & Riordan, O. Percolation (Cambridge University Press, 2006).
Wierman, J. C. Bond percolation on honeycomb and triangular lattices. Adv. Appl. Prob. 13, 298–313, https://doi.org/10.1017/S0001867800036028 (1981).
Vyssotsky, V. A., Gordon, S. B., Frisch, H. L. & Hammersley, J. M. Critical percolation probabilities (bond problem). Phys. Rev. 123, 1566–1567, https://doi.org/10.1103/PhysRev.123.1566 (1961).
Kesten, H. The critical probability of bond percolation on the square lattice equals 1/2. Comm. Math. Phys. 74, 41–59, https://doi.org/10.1007/BF01197577 (1980).
Tse, D. & Viswanath, P. Fundamentals of Wireless Communication (Cambridge University Press, 2005).
Ceriotti, M. et al. Monitoring heritage buildings with wireless sensor networks: The torre aquila deployment. In Proceedings of the 8th ACM/IEEE International Conference on Information Processing in Sensor Networks (IPSN) (2009).
Acknowledgements
The authors are supported by the DFG through the Excellence Initiative by the German Federal Government and State Government (cluster of excellence cfaed). We thank all members of the Biological Algorithms group, in particular Justus Kromer, for stimulating discussions.
Author information
Authors and Affiliations
Contributions
All authors jointly conceived the project, played an active role in formulating the model, and wrote the manuscript together. J.K. and B.M.F. developed the theory and performed simulations.
Corresponding author
Ethics declarations
Competing Interests
The authors declare no competing interests.
Additional information
Publisher's note: Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Electronic supplementary material
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Karschau, J., Zimmerling, M. & Friedrich, B.M. Renormalization group theory for percolation in time-varying networks. Sci Rep 8, 8011 (2018). https://doi.org/10.1038/s41598-018-25363-2
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-018-25363-2
This article is cited by
-
Effect of carbons’ structure and type on AC electrical properties of polymer composites: predicting the percolation threshold of permittivity through different models
Colloid and Polymer Science (2023)
-
A sampling-guided unsupervised learning method to capture percolation in complex networks
Scientific Reports (2022)
-
Scaling electrical percolation networks based on renormalization group theory
Applied Physics A (2022)
-
Analytics for directed contact networks
Applied Network Science (2019)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.