Abstract
Unlike traditional communication, quantum key distribution (QKD) can reach unconditional security and thus attracts intensive studies. Among all existing QKD protocols, round-robin-differential-phase-shift (RRDPS) protocol can be running without monitoring signal disturbance, which significantly simplifies its flow and improves its tolerance of error rate. Although several security proofs of RRDPS have been given, a tight finite-key analysis with a practical phase-randomized source is still missing. In this paper, we propose an improved security proof of RRDPS against the most general coherent attack based on the entropic uncertainty relation. What’s more, with the help of Azuma’s inequality, our proof can tackle finite-key effects primely. The proposed finite-key analysis keeps the advantages of phase randomization source and indicates experimentally acceptable numbers of pulses are sufficient to approach the asymptotical bound closely. The results shed light on practical QKD without monitoring signal disturbance.
Similar content being viewed by others
Introduction
As the maturest field of quantum information sciences, quantum key distribution (QKD)1 is well-known for its information-theoretic security. In QKD, the law of quantum mechanics enables communicators to upper bound the potential information leakage to the eavesdropper (Eve). Since the BB841 protocol was proposed, more and more QKD protocols sprang up, such as device-independent (DI)2 protocol, measurement-device-independent (MDI)3 protocol and twin-field (TF)4 protocol. In most of these protocols, estimating Eve’s information is dependent on monitoring signal disturbance, e.g., information leakage in BB84 is a function of the error rate of sifted key bits. However, in 2014, Toshihiko Sasaki et al. proposed an exceptional protocol, named round-robin-differential-phase-shift (RRDPS)5, which can upper bound Eve’s information without using any parameter of signal disturbance. After that, the verification of RRDPS has been completed in several experiments6,7,8,9.
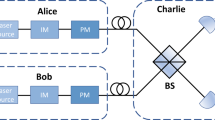
In RRDPS, Alice firstly prepares an n-photon L-pulse train as a packet and encodes key bit 0(1) on every pulse by modulating phase 0(π), while these phase information are recorded in Alice’s register. Then Alice sends the train to Bob through a quantum channel. Once Bob receives the train which is assumed to be a single-photon quantum state, his local quantum random number generator (QRNG) generates an integer r ∈ [1, L − 1]. Bob interferes the a-th and b-th (b = a + r ≤ L) pulses in the train to decode his sifted key bit 0(1) corresponding to phase shift 0(π). After that, Bob announces (a, b) and Alice does xor on key bits on a-th and b-th pulses to get her sifted key bit. In ref. 5, Sasaki et al. proved Eve’s information on sifted key bit is no larger than \({H}_{2}(\frac{n}{L-1})\), where H2 is the Shannon entropy \({H}_{2}(x):=-x{\mathrm{log}}\,x-(1-x){\mathrm{log}}\,(1-x)\). And we subscribe that \({\mathrm{log}}\,\) represents log2. It’s clear that RRDPS protocol has a high error rate tolerance and doesn’t need to monitor bit error rate to estimate information leakage.
Although ref. 5 has beautiful results, the bound for Eve’s information is not tight. In 2018, Yin et al. put forward a phase-randomized method to improve it by constructing the optimal collective attack model10. Until now, their work has kept the highest secure key rate among all related works. However, their results cannot be directly used in finite-key cases because the collective attack is not equivalent to the most general coherent attack in finite-key cases. In order to remove this restriction, Liu et al. applied the post-selection technique11 to the results of ref. 10, then completed finite-key analysis12. Unfortunately, the results showed that RRDPS needed too many pulses to obtain satisfactory performance. Therefore, finite-key analysis for RRDPS is still an open issue.
RRDPS protocol will never be considered into practice until finding a proper method to reduce finite-size effects and minimize the number of emitted pulses as far as possible. Here we give a tight finite-key analysis for RRDPS with widely used phase-randomized weak coherent source. The essential idea is observing that the randomized phases of each pulse of the train lead the composite system of Alice, Bob and Eve into becoming a mixture state, in which different components may have different information leakage. Next one can apply the entropic uncertainty relation13 to estimate phase error rates and min-entropies for each mixture components. Moreover, by introducing Azuma’s inequality14, the effects of coherent attacks are well-considered. Note that the entropic uncertainty relation has been applied to BB8415, MDI16 and even TF17 protocol, although not to RRDPS yet, our analysis shows that it’s doubtlessly feasible to use this technique in RRDPS. Numerical simulations fully demonstrate that our theoretical model is almost the optimal solution of the finite-key RRDPS with phase-randomized weak coherent source: experimentally acceptable amounts of pulses can help RRDPS behave closely to the asymptotic bounds given in ref. 10.
Results
Definition of protocol
The flow of actual RRDPS protocol has been given in ref. 5. On the other hand, it’s pointed out in ref. 5 that the security of RRDPS protocol is essentially regarded as a virtual protocol. Specifically, since the security proof can be reduced to how to bound Eve’s potential information on Alice’s key bits, one can just consider the virtual protocol 1 given as below.
Step. 1 Alice prepares \({\left|\Psi \right\rangle }_{{\rm{B}}}\), which is the state of L-pulse train as a packet containing n-photon. Meanwhile, Alice prepares local L-qubit \({\left|+\right\rangle }_{{{\rm{A}}}_{1}}=({\left|0\right\rangle }_{{{\rm{A}}}_{1}}+{\left|1\right\rangle }_{{{\rm{A}}}_{1}})/\sqrt{2},{\left|+\right\rangle }_{{{\rm{A}}}_{2}},...,{\left|+\right\rangle }_{{{\rm{A}}}_{L}}\), obtains the encoding state \(\sqrt{{2}^{-L}}{\otimes }_{i = 1}^{L}{\sum }_{s = 0,1}{\left|s\right\rangle }_{{{\rm{A}}}_{i}}{(-1)}^{s{\hat{n}}_{i}}{\left|\Psi \right\rangle }_{{\rm{B}}}\), where \({\hat{n}}_{i}:={\hat{a}}_{i}^{\dagger }{\hat{a}}_{i}\) is the photon number operator for the i-th pulse in \({\left|\Psi \right\rangle }_{{\rm{B}}}\), and then emits B to Bob via an unreliable quantum channel. The first step will be repeated for Nem times.
Step. 2 For each B of Nem emissions from Alice, Bob receives an L-pulse train (or a packet) B and measures its photon number. Bob just retains the trial that there is only one photon in the train. For each of the retained trials, Bob measures which pulse in the train the single-photon is in. Assuming the single-photon is in the a-th pulse, Bob generates another random number b ∈ [1, L] and b ≠ a, then announces (a, b) and the index of this trial through an authenticated classical channel. One may note that in the actual protocol, Bob measures the phase shift between two pulses through a variable-delay interferometer to obtain his sifted key bit. Anyway, the actual protocol is equivalent to the virtual one in the sense of security proof.
Step. 3 Given (a, b) for each of the retained trials, Alice applies a controlled-NOT operation to the corresponding local qubits Aa and Ab, where the former is the control qubit and the latter is the target qubit. Then Alice measures Aa with \({\mathbb{Z}}\)-basis to obtain the sifted key bit for each trial. We denote \(\widetilde{{\bf{Z}}}\) as the bit string of the sifted key bits from N retained trials and \(\left|\right.\widetilde{{\bf{Z}}}\left|\right.=N\).
Step. 4 Alice and Bob evaluate some parameters used in privacy amplification, e.g., Eve’s smooth min-entropy on \(\widetilde{{\bf{Z}}}\), which is essential for the security proof. Note that the results calculated here can be directly applied in the actual protocol to perform a post-processing step of sifted key bits and generate the final secret key.
Note that in the actual RRDPS protocol, Alice measures each of \({\left|+\right\rangle }_{{{\rm{A}}}_{1}}{\left|+\right\rangle }_{{{\rm{A}}}_{2}}...{\left|+\right\rangle }_{{{\rm{A}}}_{L}}\) with \({\mathbb{Z}}\)-basis at the very beginning of the protocol, and does not perform the controlled-NOT operation. Based on this observation, it’s easy to see that the Step. 3 can be replaced by the Step. \(3^{\prime}\), say
Step. \(3^{\prime}\) Given (a, b) for each trial of the retained trials, Alice applies a controlled-NOT operation to the corresponding local qubits Aa and Ab, where the former is the target qubit and the latter is the control qubit. Then Alice measures Aa with \({\mathbb{Z}}\)-basis to obtain the sifted key bit for each trial. We denote \(\widetilde{{\bf{Z}}}\) as the bit string of the sifted key bits from N retained trials and \(\left|\right.\widetilde{{\bf{Z}}}\left|\right.=N\).
We name the virtual protocol 1 with Step. \(3^{\prime}\) instead of Step. 3 as virtual protocol 2. As a matter of fact, the virtual protocols 1 and 2 generates same sifted key bits, and Eve cannot distinguish Alice is performing virtual protocol 1 or virtual protocol 2. Therefore, from the view of security proof, the smooth min-entropy of the actual protocol can be lower bounded by the larger one of min-entropies calculated in virtual protocols 1 and 2. This consideration is the first reason that our analysis can converge to the optimal key rate given in ref. 10. In the following, we sketch how to estimate these smooth min-entropies.
The bound for smooth min-entropy
Calculating the smooth min-entropies is a complicated problem, especially when the photon-number of \({\left|\Psi \right\rangle }_{{\rm{B}}}\) is large. For the ease of understanding, we only sketch the single-photon case here, while one can refer to Supplementary Note 7: General n photon-number case for the detailed proof for general cases. In single-photon case, we have \({\left|\Psi \right\rangle }_{{\rm{B}}}=\mathop{\sum }\nolimits_{i = 1}^{L}{\left|i\right\rangle }_{{\rm{B}}}\) where \({\left|i\right\rangle }_{{\rm{B}}}\) represents the single-photon is in the i-th pulse. Then the encoding state in step. 1 for each trial can be written in a simple form given by \(\mathop{\sum }\nolimits_{i = 1}^{L}{\left|i\right\rangle }_{{\rm{A}}}{\left|i\right\rangle }_{{\rm{B}}}\), where \({\left|i\right\rangle }_{{\rm{A}}}={\left|+\right\rangle }_{{{\rm{A}}}_{1}}{\left|+\right\rangle }_{{{\rm{A}}}_{2}}...{\left|-\right\rangle }_{{{\rm{A}}}_{i}}...{\left|+\right\rangle }_{{{\rm{A}}}_{L}}\), i.e., only the i-th local qubit Ai is in \(\left|-\right\rangle\) state while all others are in \(\left|+\right\rangle\) state.
Let’s consider Eve launches a coherent attack for the N communication rounds, which results in a tripartite quantum state shared by Alice, Bob and Eve, i.e.,
Here, the superscripts denote the indices of the retained trials of step. 2 in virtual protocols. \({\left|{i}^{1}{i}^{2}...{i}^{N}\right\rangle }_{{\rm{A}}}\triangleq {\left|{i}^{1}\right\rangle }_{{{\rm{A}}}^{1}}{\left|{i}^{2}\right\rangle }_{{{\rm{A}}}^{2}}...{\left|{i}^{N}\right\rangle }_{{{\rm{A}}}^{N}}\). For example, \({\left|{i}^{1}\right\rangle }_{{{\rm{A}}}^{1}}={\left|+\right\rangle }_{{{\rm{A}}}_{1}^{1}}{\left|+\right\rangle }_{{{\rm{A}}}_{2}^{1}}...{\left|-\right\rangle }_{{{\rm{A}}}_{{i}^{1}}^{1}}...{\left|+\right\rangle }_{{{\rm{A}}}_{L}^{1}}\) represents Alice’s local qubits for the first retained trial. Similarly, \({\left|{j}^{1}{j}^{2}...{j}^{N}\right\rangle }_{{\rm{B}}}\triangleq {\left|{j}^{1}\right\rangle }_{{{\rm{B}}}^{1}}{\left|{j}^{2}\right\rangle }_{{{\rm{B}}}^{2}}...{\left|{j}^{N}\right\rangle }_{{{\rm{B}}}^{N}}\) means that in the first retained trial the single photon is in the j1-th pulse, in the second retained trial the single photon is in the j2-th pulse, and in the last retained trial the single photon is in the jN-th pulse. \({C}_{{i}^{1}{j}^{1}{i}^{2}{j}^{2}...{i}^{N}{j}^{N}}\) is a complex number.
Since we are interested in the Alice and Bob’s local states for the l-th retained trial, the quantum state \({\left|\Phi \right\rangle }_{{\rm{ABE}}}\) can be rewritten as
where \({\widetilde{C}}_{{i}^{l}{j}^{l}}^{l}:={\sum }_{{i}^{1}{j}^{1}{i}^{2}{j}^{2}...{i}^{N}{j}^{N}/{i}^{l}{j}^{l}}{C}_{{i}^{1}{j}^{1}{i}^{2}{j}^{2}...{i}^{N}{j}^{N}}{|{i}^{1}{i}^{2}...{i}^{N}/{i}^{l}\rangle }_{{{\rm{A}}}^{\ne l}}{|{j}^{1}{j}^{2}...{j}^{N}/{j}^{l}\rangle }_{{{\rm{B}}}^{\ne l}}{|{e}_{{i}^{1}{j}^{1}{i}^{2}{j}^{2}...{i}^{N}{j}^{N}}\rangle }_{{\rm{E}}}\).
Moreover, assuming that Bob announces (a, b) in the l-th trial, we obtain the quantum state
where \({\mathcal{P}}\left\{\left|x\right\rangle \right\}:=\left|x\right\rangle \left\langle x\right|\). Note that \({\widetilde{C}}_{{i}^{l}{j}^{l}}^{l}\) is a quantum system of A≠l, B≠l and E. Then, it’s very clear that the first part \({\mathcal{P}}\left\{{\widetilde{C}}_{aa}^{l}{\left|-\right\rangle }_{{{\rm{A}}}_{a}}{\left|+\right\rangle }_{{{\rm{A}}}_{b}}+{\widetilde{C}}_{ba}^{l}{\left|+\right\rangle }_{{{\rm{A}}}_{a}}{\left|-\right\rangle }_{{{\rm{A}}}_{b}}\right\}\) is coupled with Eve, which means Eve may learn sifted key bit from this mixture component. Conversely, the second part \({\sum }_{{i}^{l}\ne a,b}{\mathcal{P}}\left\{{\widetilde{C}}_{{i}^{l}a}^{l}{\left|+\right\rangle }_{{{\rm{A}}}_{a}}{\left|+\right\rangle }_{{{\rm{A}}}_{b}}\right\}\) is decoupled with Eve, which will result in perfect secret key evidently. We call the former coupled case and the latter decoupled case, whose probabilities are \({P}_{{\rm{co}}}^{l}=\frac{{\sum }_{b}\left|\right.{\widetilde{C}}_{aa}^{l}{\left|\right.}^{2}+\left|\right.{\widetilde{C}}_{ba}^{l}{\left|\right.}^{2}}{{\sum }_{b}{\sum }_{{i}^{l}}\left|\right.{\widetilde{C}}_{{i}^{l}a}^{l}{\left|\right.}^{2}}\) and \({P}_{{\rm{deco}}}^{l}=\frac{{\sum }_{b}{\sum }_{{i}^{l}\ne a,b}\left|\right.{\widetilde{C}}_{{i}^{l}a}^{l}{\left|\right.}^{2}}{{\sum }_{b}{\sum }_{{i}^{l}}\left|\right.{\widetilde{C}}_{{i}^{l}a}^{l}{\left|\right.}^{2}}\) respectively.
To analyze the smooth min-entropy in the coupled case, we refer to the entropic uncertainty relation13,15,18. Indeed, a so-called phase error rate eph can be used to characterize the smooth min-entropy. In ref. 5, eph is defined as the probability of finding Ab in \(\left|-\right\rangle\). Differently, we define \({P}_{a}^{l}\) to be the probability of finding \({{\rm{A}}}_{a}^{l}\) in \(\left|-\right\rangle\) and \({P}_{b}^{l}\) the probability of finding \({{\rm{A}}}_{b}^{l}\) in \(\left|-\right\rangle\), just corresponding to the virtual protocols 1 and 2 respectively. Then it’s straightforward to obtain \({P}_{a}^{l}=\frac{{\sum }_{b}\left|\right.{\widetilde{C}}_{aa}^{l}{\left|\right.}^{2}}{{\sum }_{b}{\sum }_{{i}^{l}}\left|\right.{\widetilde{C}}_{{i}^{l}a}^{l}{\left|\right.}^{2}}\), \({P}_{b}^{l}=\frac{{\sum }_{b}\left|\right.{\widetilde{C}}_{ba}^{l}{\left|\right.}^{2}}{{\sum }_{b}{\sum }_{{i}^{l}}\left|\right.{\widetilde{C}}_{{i}^{l}a}^{l}{\left|\right.}^{2}}\). For ease of notations, we define variables \({x}_{1}^{l}=\left|\right.{\widetilde{C}}_{aa}^{l}{\left|\right.}^{2}\) and \({x}_{2}^{l}={\sum }_{b}\left|\right.{\widetilde{C}}_{ba}^{l}{\left|\right.}^{2}\), which satisfy \({\sum }_{b}\left|\right.{\widetilde{C}}_{aa}^{l}{\left|\right.}^{2}=(L-1){x}_{1}^{l}\) and \({\sum }_{b}{\sum }_{{i}^{l}\ne a,b}\left|\right.{\widetilde{C}}_{{i}^{l}a}^{l}{\left|\right.}^{2}=(L-2){x}_{2}^{l}\). Here b ∈ {1, 2, . . . , L} and b ≠ a. Then, \({P}_{{\rm{deco}}}^{l}=\frac{(L-2){x}_{2}^{l}}{(L-1)\mathop{\sum }\nolimits_{j = 1}^{2}{x}_{j}^{l}}\), \({P}_{{\rm{co}}}^{l}=\frac{(L-1){x}_{1}^{l}+{x}_{2}^{l}}{(L-1)\mathop{\sum }\nolimits_{j = 1}^{2}{x}_{j}^{l}}\), \({P}_{a}^{l}=\frac{(L-1){x}_{1}^{l}}{(L-1)\mathop{\sum }\nolimits_{j = 1}^{2}{x}_{j}^{l}}\) and \({P}_{b}^{l}=\frac{{x}_{2}^{l}}{(L-1)\mathop{\sum }\nolimits_{j = 1}^{2}{x}_{j}^{l}}\).
Above formulae of calculating \({P}_{{\rm{deco}}}^{l}\), \({P}_{{\rm{co}}}^{l}\), \({P}_{a}^{l}\) and \({P}_{b}^{l}\) are just for the l-th bit of \(\widetilde{{\bf{Z}}}\). On the other hand, the security proof needs to estimate the upper bound of smooth min-entropy of \(\widetilde{{\bf{Z}}}\). We resort to Azuma’s inequality to complete estimation. The basic idea is to think of above cases as the flip of coins. Consider N coin tosses, and the results of the l-th coin maybe head or not, which is dependent on previous l − 1 tosses. We set a random variable \({X}_{i}={h}_{i}-\mathop{\sum }\nolimits_{l = 1}^{i}{p}^{l}\), where pl is the probability of having a head in the l-th round, and hi is the number of heads. X0, X1, . . . is a martingale, and for two adjacent variables, \(\left|{X}_{k}-{X}_{k-1}\right|\le 1,k\in \{1,2,...,i\}\). According to Azuma’s inequality, for all N ≥ 0 and any α ≥ 0 we can get
It’s very similar between “coin cases” and our cases, which means in the l-th round, Alice’s local qubits Aa and Ab in Step. 3 can be classified into decoupled cases or coupled cases, while coupled ones can be classified into with phase error and no phase error. For every kind of cases, we could construct a martingale, respectively, which justifies the application of Azuma’s inequality. The same logic can be seen in ref. 19. Among the N bits sifted key \(\widetilde{{\bf{Z}}}\), we denote Ndeco(Nco) as the bit number of decoupled(coupled) sifted key \({\widetilde{{\bf{Z}}}}_{{\rm{deco}}}\)(\({\widetilde{{\bf{Z}}}}_{{\rm{co}}}\)), and eph as the phase error rate of the Nco bits coupled key \({\widetilde{{\bf{Z}}}}_{{\rm{co}}}\). According to Azuma’s inequality, for all N ≥ 0 we can find
holds with probability at least \(1-2{\epsilon }_{{\rm{deco}}}^{N}\). Similarly,
and
hold with probabilities at least \(1-2{\epsilon }_{{\rm{co}}}^{N}\) and \(1-2{\epsilon }_{{\rm{co}}}^{{e}_{{\rm{ph}}}}\), respectively. Note that, \({P}^{l}:=\min \{{P}_{a}^{l},{P}_{b}^{l}\}\).
We further set \(\mathop{\sum }\nolimits_{l = 1}^{N}\frac{{x}_{1}^{l}}{\mathop{\sum }\nolimits_{j = 1}^{2}{x}_{j}^{l}}\triangleq {c}_{1}\), and \(\mathop{\sum }\nolimits_{l = 1}^{N}\frac{{x}_{2}^{l}}{\mathop{\sum }\nolimits_{j = 1}^{2}{x}_{j}^{l}}\triangleq {c}_{2}\), where c1, c2 ∈ [0, N], c1 + c2 ≤ N. Then these inequalities could be rewritten by
where
Now, we are ready to calculate Eve’s smooth min-entropy \({H}_{\min }^{\epsilon }(\widetilde{{\bf{Z}}}| {\rm{E}})\). According to chain rules and entropic uncertainty relation, we have
where the smooth parameters satisfy \(\epsilon =2{\epsilon }_{{\rm{deco}}}+{\epsilon }_{{\rm{co}}}+{\epsilon }_{0}^{\prime}=2{\epsilon }_{{\rm{co}}}^{N}+2{\epsilon }_{{\rm{co}}}^{{e}_{{\rm{ph}}}}+{\epsilon }_{0}^{\prime}\) and ϵdeco = 0. Finally, the smooth min-entropy \({H}_{\min }^{\epsilon }(\widetilde{{\bf{Z}}}| {\rm{E}})\) depends on Nco and eph, which are further decided by parameters c1 and c2. This means that we can optimize these parameters to obtain the maximum of \({H}_{\min }^{\epsilon }(\widetilde{{\bf{Z}}}| {\rm{E}})\).
Basically, the derivations of \({H}_{\min }^{\epsilon }(\widetilde{{\bf{Z}}}| {\rm{E}})\) for n-photon case is following the same manner and detailed in Supplementary Note 7: General n photon-number case. In short, ρABE is a mixture of decoupled component and n different types of coupled components, which implies \({H}_{\min }^{\epsilon }(\widetilde{{\bf{Z}}}| {\rm{E}})\) is characterized by the bits of decoupled key Ndeco, the bits of the i-th type of coupled key Ncoi and its corresponding phase error rate ephi, 1 ≤ i ≤ n.
Secret key rate
We have obtained the smooth min-entropy in n photon-number case. However, it’s more complex in actual QKD system with phase-randomized weak coherent source, which makes \({\left|\Psi \right\rangle }_{{\rm{B}}}\) to be a mixture of Fock states with Poisson distribution. Similarly, with the idea in ref. 5, we set a threshold value of photon-number as vth and classified \(\widetilde{{\bf{Z}}}\) into \({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}\) and \({{\bf{Z}}}_{n \,{>}\,{v}_{{\rm{th}}}}\), where \({{\bf{Z}}}_{n \,{>}\,{v}_{{\rm{th}}}}\)(\({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}\)) represents the sifted key bits generated by \({\left|\Psi \right\rangle }_{{\rm{B}}}\) of photon-number (no) larger than vth. Without compromising the security, Eve’s smooth min-entropy of \({{\bf{Z}}}_{n \,{>}\,{v}_{{\rm{th}}}}\) is treated as 0, while each of \({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}\) is regarded as the vth photon-number case, whose smooth min-entropy can be solved by the results in the last section.
Accordingly, we present the secret key length ℓ as
where \({N}_{n\le {v}_{{\rm{th}}}}=| {{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}|\). ξ refers to bit error correction efficiency, and ebit is the bit error rate. Besides, for simplicity, we have set all failure parameters to be the same \(\widetilde{\epsilon }\). See the Methods for a detailed derivation.
Now we are going to evaluate the performance of RRDPS with a phase randomized weak coherent source in finite regions. We use Mathematica to simulate the final secret key rate per pulse marked as R = ℓ/LNem under different conditions. The detailed formula and the simulation parameters of R can be seen in Methods.
In Fig. 1, we show R versus channel loss at different number of pulses and L, while R versus Nem with different L are shown in Fig. 2. The results show that to eliminate finite-key effects, pulse numbers less than 1011 are sufficient for typical values of L.
The full lines show the secret key rate R versus channel loss for the RRDPS protocol when Nem is finite. From left to right, L is 3, 8, 16, 32, and the corresponding total emitted pulses are 2 × 109, 1010, 4 × 1010, 6 × 1010, respectively. While the dashed lines represent the asymptotic results correspond to ref. 10. The total security parameter of final key is ϵtot: = 10−10. Dark counts rate is d = 10−6 per pulse, and the misalignment of measurement is emis = 0.015. The efficiency of error correction ξ is 1.1.
The full lines show the secret key rate R versus Nem for the RRDPS protocol when Nem is finite. These lines from bottom to up with L = 8, 16, 32. The dashed lines represent the asymptotic results. The total security parameter of the final key is ϵtot: = 10−10. The channel loss is fixed at 20 dB. Dark counts rate is d = 10−6 per pulse, and the misalignment of measurement is emis = 0.015. The efficiency of error correction ξ is 1.1.
Discussion
From the results of simulations, we can see that the larger the value of L, the more emitted pulses needed. Despite all this, it’s evident that our method makes R to be sufficiently close to the asymptotic bound when the number of emitted pulses is achievable in practical high speed QKD systems20,21,22,23,24.
The protocol most commonly used for comparison is decoy-state25,26,27 BB84 protocol. Evidently, if the optical misalignment is large, e.g., emis ≥ 0.11, RRDPS with relevant L always has higher key rate. This is because BB84 can tolerant error rate ebit up to 0.11. Besides, RRDPS protocol does not require monitoring signal disturbance, which obviously reduces finite-size effects and simplifies the flow of post-processing. A comparison in finite-key region, especially when pulse number is particularly small, is more meaningful. Before comparison, one should note that Azuma’s inequality is used in our proof which makes our proof applicable to arbitrary correlations and sifting28,29. Meanwhile, most of works on decoy-state BB84, typically the finite-key analysis in ref. 18, assume independent random variables, and thus only applicable in non-iterative sifting28,29. Therefore, in some sense it’s not fair to directly compare our results with decoy-state BB84 finite-key analyses. In order to solve this problem, we derive a corollary based on our general theory. Please see Supplementary Method: A corollary of an improved bound on phase error rate for details. This corollary gives a simple but improved (compared with ref. 5) bound on phase error rate eph, i.e., eph ≤ n/L. Then we can use Chernoff’s inequality instead of Azuma’s inequality to obtain a simple finite-key analysis just applicable for independent random variables and non-iterative sifting. With the same channel model and parameters, it’s easy to verify that our method exhibits positive key rate when total number of pulses is 106.85 with L = 53, while decoy-state BB84 needs 107.44 pulses. Please see Fig. 3 for the complete curves. This implies the advantage of RRDPS over deocy-state BB84 when communication time is very short.
The full lines show the secret key rate versus total emitted pulses. The red curve represents the finite-key analysis of decoy-state BB84 protocol in ref. 18. The yellow curve represents the original finite-key analysis of RRDPS protocol given in ref. 5. The green curve represents the key rate based on our corollary. We set L = 53. The total security parameter of the final key is ϵtot: = 10−10. The channel loss is fixed at 20dB, dark counts rate is d = 10−6 per pulse, and the misalignment of measurement is emis = 0.015. The efficiency of error correction ξ is 1.1.
We note that there have been two important related works about finite-key analysis of RRDPS protocol. In ref. 30, the security proof of RRDPS protocol is refined, but their results do not benefit from phase-randomized source thus cannot reach the asymptotic secret key rate given in ref. 10. Besides, according to ref. 30, they found that their key rate is lower than ref. 5 when pulse number is small. This implies that the key rate based on our corollary is higher than ref. 30 in cases of small pulse number–see Fig. 3. As for ref. 12, it keeps the advantage of phase randomization, but the required number of pulses is too large to meet the practical systems. As far as we know, our results are optimal for RRDPS in finite-key region, which implies that QKD without monitoring signal disturbance can be realized in present QKD systems. Besides, from the view of security proofs, this is a try to apply the uncertainty relation and Azuma’s inequality in high-dimensional QKD protocols. This may shed lights on the developments of techniques for security proofs.
Methods
Calculation for secret key rate
Our analysis is based on the universally composable security theory31.
In the frame of universally composable security, Alice can extract ℓ bits of the secret key using a random leftover hash function32 or Trevisan’s extractor33. The secret key length ℓ is Δ-secret15,
where \(\widetilde{{\bf{Z}}}\) denotes the sifted key bits, \(| \widetilde{{\bf{Z}}}| =N\). \({\rm{E}}^{\prime}\) is labelled as all information Eve knows about \(\widetilde{{\bf{Z}}}\) during the protocol, i.e., Eve’s quantum system E, error correction and verification codes announced by Alice.
To justify \({{\Delta }}\le 2\varepsilon +\overline{\epsilon }\), we can set
Considering the bits announced for error correction and verification31, we have
where ξ is the efficiency of error correction we have mentioned before and ϵcor is the failure probability of error verification.
Calculating \({H}_{\min }^{\varepsilon }(\widetilde{{\bf{Z}}}| {\rm{E}})\) is essential in our proof. Following a generalized chain rule for smooth min-entropy34, we have
where \({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}\) represents the sifted key bits which are generated by \({\left|\Psi \right\rangle }_{{\rm{B}}}\) of photon-number n no larger than vth, \(| {{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}| ={N}_{n\le {v}_{{\rm{th}}}}\), and \({{\bf{Z}}}_{n \,{>}\,{v}_{{\rm{th}}}}\) represents the sifted key bits are generated by \({\left|\Psi \right\rangle }_{{\rm{B}}}\) of photon-number n larger than vth. For simplicity, we abbreviate \({\varepsilon }_{n\le {v}_{{\rm{th}}}}\) to ϵ, and then \({H}_{\min }^{{\varepsilon }_{n\le {v}_{{\rm{th}}}}}({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}| {\rm{E}})\) to \({H}_{\min }^{\epsilon }({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}| {\rm{E}})\). Besides, \(\varepsilon =\epsilon +{\varepsilon }^{\prime}\).
Right now, we are going to calculate \({H}_{\min }^{\epsilon }({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}| {\rm{E}})\). Without compromising security, it is assumed that all bits of \({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}\) are generated by \({\left|\Psi \right\rangle }_{{\rm{B}}}\) of photon-number vth. As proved in Supplementary Note 7: General n photon-number case, \({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}\) can be decomposed into decoupled bits Zdeco and vth different types of coupled bits Zcoi(i = 1, 2, . . . , vth). Using vth times of chain rule, we have
Since Zdeco is completely independent to other quantum systems including Eve’s system E,
always holds with ϵdeco = 0. And the smooth parameter \(\epsilon =2\left(\mathop{\sum }\nolimits_{i = 1}^{{v}_{{\rm{th}}}-1}{\epsilon }_{{\rm{co}}i}\right)+{\epsilon }_{{\rm{co}}{v}_{{\rm{th}}}}+\mathop{\sum }\nolimits_{i = 0}^{{v}_{{\rm{th}}}-1}{\epsilon }_{i}^{\prime}.\)
To estimate \({H}_{\min }^{{\epsilon }_{{\rm{co}}i}}({{\bf{Z}}}_{{\rm{co}}i}| {{\bf{Z}}}_{{\rm{coother}}}{\rm{E}})\), we can refer to the uncertainty relation, namely,
where \({{\bf{Z}}}_{{\rm{coother}}}={{\bf{Z}}}_{{\rm{co}}(i+1)}{{\bf{Z}}}_{{\rm{co}}(i+2)}...{{\bf{Z}}}_{{\rm{co}}{v}_{{\rm{th}}}}\), i ∈ [1, vth], \(\left|\right.{{\bf{Z}}}_{{\rm{co}}i}\left|\right.={N}_{{\rm{co}}i}\), and ephi denotes the upper bound of phase error rate for Zcoi, i.e., the chance of observing \(\left|-\right\rangle\) with a hypothetical \({\mathbb{X}}\)-basis instead of \({\mathbb{Z}}\)-basis. Meanwhile, ϵcoi is equal to the probability that number of \(\left|-\right\rangle\) is larger than Ncoiephi.
The next issue is how to calculate Ndeco, Ncoi and ephi. We prove that for an l-th retained trial (the event generating the l-th bit of \({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}\)), the probabilities of obtaining decoupled case, i-th coupled case and a corresponding phase error event, all of which can be given by some non-negative real numbers ci(i ∈ [1, vth + 1]) satisfying \(\mathop{\sum }\nolimits_{i = 1}^{{v}_{{\rm{th}}}+1}{c}_{i}={N}_{n\le {v}_{{\rm{th}}}}\). We point out that the analysis method is similar to the single-photon case above, but more complex. The detailed proof is present in Supplementary Note 7: General n photon-number case.
Similarly, with the help of Azuma’s inequality, one can bound Ndeco, Ncoi and ephi for the sifted key bit string \({{\bf{Z}}}_{n\le {v}_{{\rm{th}}}}\) in terms of ci with some failure probabilities. Specifically, with probabilities at least \(1-2{\epsilon }_{{\rm{deco}}}^{{N}_{n\le {v}_{{\rm{th}}}}}\), \(1-2{\epsilon }_{{\rm{co}}i}^{{N}_{n\le {v}_{{\rm{th}}}}}\) and \(1-2{\epsilon }_{{\rm{co}}i}^{{e}_{{\rm{ph}}}}\) respectively,
hold. Here, if vth ∈ odd and \(j\in [1,\frac{{v}_{{\rm{th}}}+1}{2}]\),
If vth ∈ even and \(j\in [1,\frac{{v}_{{\rm{th}}}}{2}]\),
To summarize the above analysis of \({H}_{\min }^{\varepsilon }(\widetilde{{\bf{Z}}}| {\rm{E}})\), we have
where Ndeco, Ncoi and ephi can be decided by Eqs. (19)–(21). The smooth parameters satisfy
So far, we’ve completed the derivation of \({H}_{\min }^{\varepsilon }(\widetilde{{\bf{Z}}}| {\rm{E}})\). By optimizing the parameters ci, the lower bound of \({H}_{\min }^{\varepsilon }(\widetilde{{\bf{Z}}}| {\rm{E}})\) can be found. In following, \(\mathop{\sum }\nolimits_{i = 1}^{{v}_{{\rm{th}}}}{N}_{{\rm{co}}i}{H}_{2}({e}_{{\rm{ph}}i})\) represents its minimum value by optimizing ci under given smooth parameters. Substituting Eq. (22) to Eq. (14), we have
where we have set all failure probabilities or smooth parameters in Eq. (22) to be the same one \(\widetilde{\epsilon }\).
Finally, we can get the secret key rate per pulse \(R:=\frac{\ell }{L{N}_{{\rm{em}}}}\),
We use empirical results \({N}_{{\rm{deco}}}+{N}_{{\rm{co}}1}+{N}_{{\rm{co}}2}+...+{N}_{{\rm{co}}{v}_{{\rm{th}}}}={N}_{n\le {v}_{{\rm{th}}}}=(Q-{e}_{{\rm{src}}}^{{\rm{u}}}){N}_{{\rm{em}}}\) and the yield per packet \(Q=\frac{N}{{N}_{{\rm{em}}}}\). Besides, considering the fluctuation of photon-number, the upper bound of \({e}_{{\rm{src}}}:=1-\mathop{\sum }\nolimits_{i = 0}^{{v}_{{\rm{th}}}}{{\rm{e}}}^{-L\mu }{(L\mu )}^{i}/i!\) can be given by Chernoff bounds12,35: \({e}_{{\rm{src}}}^{{\rm{u}}}\le {e}_{{\rm{src}}}+\sqrt{\frac{3{e}_{{\rm{src}}}}{{N}_{{\rm{em}}}}{\mathrm{ln}}\,\frac{1}{{\epsilon }_{{\rm{PE}}}}}={e}_{{\rm{src}}}+\sqrt{\frac{3{e}_{{\rm{src}}}}{{N}_{{\rm{em}}}}{\mathrm{ln}}\,\frac{1}{\widetilde{\epsilon }}}\), where μ represents the intensity per pulse of phase-randomized weak coherent source.
The total security parameter36 of final key is ϵtot,
Note that for a fixed ϵtot, one should optimize vth to maximize R.
In the end, we further give the method used in the simulation. The channel efficiency is η = 10−loss(dB)/10. We assume that Bob’s detectors have dark counts rate of d = 10−6 per pulse, and there is a misalignment of measurement, that is emis = 0.015. Set ξ to be 1.1, ϵtot = 10−10. The observed yield Q and error rate ebit are assumed to be always equal to their asymptotic ones respectively, whose expressions can be found in ref. 10. Then by optimizing the light intensity μ, the threshold photon-number vth and \(\left\{{c}_{i}\right\}\), one can calculate the R under a fixed security parameter ϵtot.
Data availability
The data that support the findings of this study are available from the corresponding author upon reasonable request
References
Bennett, C. H. & Brassard, G. In Proceedings of IEEE International Conference on Computers Systems and Signal Processing, IEEE New York 175–179 (Bangalore, India, 1984).
Acin, A. et al. Device-Independent Security of Quantum Cryptography against Collective Attacks. Phys. Rev. Lett. 98, 230501 (2007).
Lo, H.-K., Curty, M. & Qi, B. Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2012).
Lucamarini, M., Yuan, Z. L., Dynes, J. F. & Shields, A. J. Overcoming the rate–distance limit of quantum key distribution without quantum repeaters. Nature 557, 400–403 (2018).
Sasaki, T., Yamamoto, Y. & Koashi, M. Practical quantum key distribution protocol without monitoring signal disturbance. Nature 509, 475–478 (2014).
Guan, J.-Y. et al. Experimental passive round-robin differential phase-shift quantum key distribution. Phys. Rev. Lett. 114, 180502 (2015).
Takesue, H., Sasaki, T., Tamaki, K. & Koashi, M. Experimental quantum key distribution without monitoring signal disturbance. Nat. Photonics 9, 827–831 (2015).
Wang, S. et al. Experimental demonstration of a quantum key distribution without signal disturbance monitoring. Nat. Photonics 9, 832–836 (2015).
Li, Y.-H. et al. Experimental round-robin differential phase-shift quantum key distribution. Phys. Rev. A 93, 030302 (2016).
Yin, Z.-Q. et al. Improved security bound for the round-robin-differential-phase-shift quantum key distribution. Nat. Commun. 9, 457 (2018).
Christandl, M., König, R. & Renner, R. Postselection technique for quantum channels with applications to quantum cryptography. Phys. Rev. Lett. 102, 020504 (2009).
Liu, H. et al. Finite-key analysis for round-robin-differential-phase-shift quantum key distribution. Opt. Express 28, 15416–15423 (2020).
Tomamichel, M. & Renner, R. Uncertainty relation for smooth entropies. Phys. Rev. Lett. 106, 110506 (2011).
Azuma, K. Weighted sums of certain dependent random variables. Tohoku Math. J. 19, 357–367 (1967).
Tomamichel, M., Lim, C. C. W., Gisin, N. & Renner, R. Tight finite-key analysis for quantum cryptography. Nat. Commun. 3, 634 (2012).
Curty, M. et al. Finite-key analysis for measurement-device-independent quantum key distribution. Nat. Commun. 5, 3732 (2014).
Currás-Lorenzo, G. et al. Tight finite-key security for twin-field quantum key distribution. NPJ Quantum Inf. 7, 1–9 (2021).
Lim, C. C. W., Curty, M., Walenta, N., Xu, F. & Zbinden, H. Concise security bounds for practical decoy-state quantum key distribution. Phys. Rev. A 89, 022307 (2014).
Boileau, J.-C., Tamaki, K., Batuwantudawe, J., Laflamme, R. & Renes, J. Unconditional Security of a Three State Quantum Key Distribution Protocol. Phys. Rev. Lett. 94, 040503 (2005).
Gordon, K. J. et al. Quantum key distribution system clocked at 2 GHz. Opt. Express 13, 3015–3020 (2005).
Thew, R. T. et al. Low jitter up-conversion detectors for telecom wavelength GHz QKD. New J. Phys. 8, 32 (2006).
Takesue, H. et al. Quantum key distribution over a 40-dB channel loss using superconducting single-photon detectors. Nat. Photonics 1, 343–348 (2007).
Yuan, Z., Dixon, A., Dynes, J., Sharpe, A. & Shields, A. Gigahertz quantum key distribution with InGaAs avalanche photodiodes. Appl. Phys. Lett. 92, 201104 (2008).
Sasaki, M. et al. Field test of quantum key distribution in the Tokyo QKD Network. Opt. Express 19, 10387–10409 (2011).
Hwang, W.-Y. Quantum key distribution with high loss: toward global secure communication. Phys. Rev. Lett. 91, 057901 (2003).
Wang, X.-B. Beating the photon-number-splitting attack in practical quantum cryptography. Phys. Rev. Lett. 94, 230503 (2005).
Lo, H.-K., Ma, X. & Chen, K. Decoy state quantum key distribution. Phys. Rev. Lett. 94, 230504 (2005).
Pfister, C., Lütkenhaus, N., Wehner, S. & Coles, P. J. Sifting attacks in finite-size quantum key distribution. New J. Phys. 18, 053001 (2016).
Tamaki, K. et al. Security of quantum key distribution with iterative sifting. Quantum Sci. Technol. 3, 014002 (2017).
Matsuura, T., Sasaki, T. & Koashi, M. Refined security proof of the round-robin differential-phase-shift quantum key distribution and its improved performance in the finite-sized case. Phys. Rev. A 99, 042303 (2019).
Renner, R. Security of quantum key distribution. Int. J. Quantum Inf. 6, 1–127 (2008).
Tomamichel, M., Renner, R. & Schaffner, C. Leftover Hashing against quantum side information. IEEE Trans. Inf. Theory 57, 5524–5535 (2011).
De, A., Portmann, C., Vidick, T. & Renner, R. Trevisan’s extractor in the presence of quantum side information. SIAM J. Comput. 41, 915–940 (2012).
Vitanov, A., Dupuis, F., Tomamichel, M. & Renner, R. Chain Rules for Smooth Min- and Max-Entropies. IEEE Trans. Inf. Theory 59, 2603–2612 (2013).
Chernoff, H. A measure of asymptotic efficiency for tests of a hypothesis based on the sum of observations. Ann. Math. Stat. 23, 493–507 (1952).
Mueller-Quade, J. & Renner, R. Composability in quantum cryptography. New J. Phys. 11, 085006 (2009).
Acknowledgements
This work has been supported by the National Key Research and Development Program of China (Grant No. 2018YFA0306400), the National Natural Science Foundation of China (Grant Nos. 61822115, 61961136004, 61775207, 61627820) and Anhui Initiative in Quantum Information Technologies. The authors acknowledge Dr.Takaya Matsuura in Department of Applied Physics, Graduate School of Engineering, University of Tokyo.
Author information
Authors and Affiliations
Contributions
Z.-Q.Y., R.W., S.W., W.C., G.-C.G., Z.-F.H. conceived the basic idea of the security proof. Z.-Q.Y. and H.L. finished the details of the security proof. H.L. designed the simulations. Z.-H.W. designed the simulation for decoy-state BB84. Z.-Q.Y. and H.L. wrote the paper.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Liu, H., Yin, ZQ., Wang, R. et al. Tight finite-key analysis for quantum key distribution without monitoring signal disturbance. npj Quantum Inf 7, 95 (2021). https://doi.org/10.1038/s41534-021-00428-9
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41534-021-00428-9