Abstract
Quantum communication between distant parties is based on suitable instances of shared entanglement. For efficiency reasons, in an anticipated quantum network beyond point-to-point communication, it is preferable that many parties can communicate simultaneously over the underlying infrastructure; however, bottlenecks in the network may cause delays. Sharing of multi-partite entangled states between parties offers a solution, allowing for parallel quantum communication. Specifically for the two-pair problem, the butterfly network provides the first instance of such an advantage in a bottleneck scenario. In this paper, we propose a more general method for establishing EPR pairs in arbitrary networks. The main difference from standard repeater network approaches is that we use a graph state instead of maximally entangled pairs to achieve long-distance simultaneous communication. We demonstrate how graph-theoretic tools, and specifically local complementation, help decrease the number of required measurements compared to usual methods applied in repeater schemes. We examine other examples of network architectures, where deploying local complementation techniques provides an advantage. We finally consider the problem of extracting graph states for quantum communication via local Clifford operations and Pauli measurements, and discuss that while the general problem is known to be NP-complete, interestingly, for specific classes of structured resources, polynomial time algorithms can be identified.
Similar content being viewed by others
Introduction
Quantum communication schemes over optical networks necessarily suffer from transmission losses and errors. For this reason, in order to achieve the vision of secure quantum communication over arbitrary distances, several schemes have been proposed that are based on entanglement swapping and purification.1,2,3,4,5 However, such existing “quantum repeater” approaches are based on sharing and manipulating close to maximally entangled “EPR” pairs between the nodes. A lot of emphasis has been put onto identifying efficient ways of achieving this task,2,3,6,7 amounting to challenging prescriptions. Yet, for multi-partite quantum networks going beyond point-to-point achitectures, much less is known about how to meaningfully manipulate resources. This is particularly unfortunate since a number of protocols have been devised for tasks like secret sharing,8,9 quantum voting10 and quantum conference key agreement,11,12,13 that exploit the genuine multi-partite character of a quantum network, having the vision of a quantum internet in mind.14 In fact, one could argue that the true potential of quantum communication is expected to lie in such multi-partite applications beyond point-to-point architectures.
Specifically in multi-partite quantum networks, it could well be preferable that the involved processes are run offline, i.e., before a request for communication is received. However, methods like the ones described in ref. 15 require big quantum memories, as well as a high channel capacity. Consequently, network efficiency is limited by the memory capacities of the quantum repeater stations,16 as well as by possible bottlenecks imposed by the quantum network architecture. In this context, new questions of quantum routing emerge. We use the term quantum routing as referring to the task of manipulating entangled resources in multi-partite quantum networks between arbitrary nodes, not necessarily making use of local knowledge only, as is common in classical routing, but allowing for global classical communication. The key question in this framework is how to optimally establish communication between distant nodes using the intermediate nodes of a quantum network.
In this work, we consider methods for sharing entanglement between nodes of a network that are favorable in terms of memory and channel capacity. We start from the same setting where nodes connected via optical links share maximally entangled qubit pairs. By suitable entanglement swapping steps,7,17,18 the resulting state is a graph state.19,20 Methods for purifying any graph state via measurements and classical communication have been studied21 and applications in quantum networks considered.22,23 Setting up the shared quantum state before the actual request for communication is preferable in terms of efficiency, but also allows for detection and prevention of channel and node failure.
For a given graph state and a request for communication between two distinct nodes, a straightforward solution would be to find a shortest path between the nodes, create a “repeater” line (by isolating the path from its environment), and then perform measurements on the intermediate nodes, thereby creating an EPR pair between the two. However, this approach is far from optimal since it requires measuring a large number of nodes and therefore diminishes the secondary use of the residual quantum state. Here, we propose another method that requires at most as many measurements as this “repeater” protocol, in general leaving a larger part of the graph state intact, while simultaneously solving bottleneck issues in the network. The method is based on local complementation19,24 and is already underlying in the prominent bottleneck example of the butterfly scheme.25,26 The lack of studies in this area is due to the fact that local complementation does not provide an advantage in classical network coding, since there is no classical equivalent to the application of local Clifford operations in order to achieve serviceable long-range correlations. Finally, we turn towards the problem of extracting graph states from given larger graph states via local Clifford operations and Pauli measurements. Using known results from graph theory,27,28,29,30 we discuss that while the general problem is known to be NP-complete,31 for specific classes of more structured resources, polynomial time algorithms can be found. All our schemes are based on local complementation, but are genuinely quantum in the way that multi-partite quantum graph states are manipulated.
A graph G = (V, E) consists of a finite set of vertices \(V {\varsubsetneq} {\mathbb{N}}\) and a set \(E \subseteq V \times V\) of edges. The set of all vertices that have a shared edge with a given vertex a is called the neighborhood of a and denoted by Na. Graphs have an adjacency matrix with entries
associated with them. In this work, we only consider simple graphs, i.e., graphs that do not contain edges connecting a vertex to itself, or multiple edges between the same pair of vertices. For any G, a graph state vector |G〉 can be defined as follows; first, a qubit in \(| + \rangle = (|0\rangle + |1\rangle )/\sqrt 2\) is prepared for each of the vertices in V. Subsequently, a controlled-Z operation is applied to each pair of qubits that is adjacent in G. The resulting graph state is
It is important to stress that graph states do not have to be prepared in this fashion. In fact, we here anticipate the states to be prepared from EPR pairs and entanglement swapping in a quantum network. Note that local Pauli measurements on a graph state result in a different graph state up to local unitary corrections (cf. Proposition 7 in ref. 19). Here, we will omit these local corrections for the sake of clarity.
In this work we will make use of a graph transformation called local complementation. By τa(G) we denote the graph that results from locally complementing G with respect to the vertex a.
Definition 1
(Local complementation). A graph G = (V, E) and vertex a ∈ V define a graph τa(G) with adjacency matrix
where Θa is the complete graph of the neighborhood Na.
Local complementation on a graph is equivalent to applying local Clifford gates on the respective graph state.32 In particular, the graph state that results from local complementation with respect to node a of the graph state vector |G〉, is defined by \(|\tau _a(G)\rangle : = U_a^\tau |G\rangle\), where \(U_a^\tau : = (iX_a)^{1/2}( - iZ_{N_a})^{1/2}\). It is possible to verify whether two graph states can be transformed into each other via sequential local complementations in polynomial time.33 Note that we aim at achieving deterministic transformations to the desired final states in routing, we do not consider stochastic operations, which is an interesting problem in its own right,34 but leads to exponentially small probabilities of success in the large system size limit. As we only consider local Clifford operations and Pauli measurements, the resulting states remain graph states and can be described in terms of the pre-measurement graph with the help of local complementations and Z-measurements.20
Results
Reducing the number of measurements
We have already argued that sharing graph states between the nodes of a network allows for quicker communication with less requirements for channel capacity and memory than sharing EPR pairs between nodes. However, it is not known, given a shared graph state, what the optimal technique for entanglement sharing between nodes that are not connected via physical links is. In the following, we will prove that a “repeater” method is not optimal regarding the number of measurements to be performed. Having a significantly reduced number of measurements is extremely useful in quantum networks, since it allows us to “extract” more entanglement from the shared graph state.
The repeater protocol entails first isolating a path between two nodes a and b and then connecting a to b by measuring the intermediate nodes of the path. This can be optimized by selecting the shortest path connecting a to b that has the minimum combined neighborhood. Every node that lies in the union of neighborhoods of this path but not on the path itself is then Z-measured. This isolates the path from the rest of the graph creating a repeater line. Finally, every intermediate vertex on the line is X-measured yielding the EPR pair between the two nodes.
The X-protocol is following a different approach. First, the intermediate vertices along the same shortest path between a and b are X-measured. Subsequently, the neighborhoods of the two nodes are Z-measured (except the nodes themselves), creating the desired EPR pair between a and b.
We specifically prove the following theorem in the Supplementary Information.
Theorem 1
(Creating maximally entangled pairs). We can create an EPR pair between two nodes a and b of an arbitrary graph state using the X-protocol with at most as many measurements as with the repeater protocol.
The proof compares the number of measurements required when running the two different algorithms. Note that both protocols work because X-measurements on a shortest path create an edge between the first and the last node of the path on the underlying graph. The X-protocol decreases the number of measurements used in standard repeater scenarios, when we know a pair of nodes that intends to communicate (in this case a and b). In particular, it allows for a larger part of the graph state to remain intact for future use. Figure 1a, b visualizes how the X-protocol for a 9-qubit cluster state allows us to communicate between the nodes 1 and 9 while keeping a residual graph state for simultaneous communication between any pair of nodes in {3, 4, 7, 8}. Here, the residual graph state can be turned into the desired second EPR pair by two measurements. Note that if we would first isolate the path between nodes 1 and 9 and then apply standard repeater protocols, the distillation would require the measurement of at least six nodes and thereby render the extraction of a second EPR pair impossible (cf. Fig. 1c–e).
An EPR pair and a residual graph state (b) are distilled from a cluster state with 9 qubits (a) using the X-protocol (orange) on the path (1, 2, 5, 6, 9). Note that the combined neighborhood of nodes 1 and 9 is just the set {1, 9} after the qubits corresponding to nodes 2, 5, 6 are X-measured. The X-protocol in terms of local complementations is visualized in Fig. 3. The repeater protocol (blue) on the same path isolates the path (c) yielding the EPR pair between nodes 1 and 9 (d) after the measurement of the intermediate nodes 2, 5, 6
It is also beneficial to compare our protocol to the standard entanglement swapping methods based on directly sharing EPR pairs over the underlying network. To build the graph states of Fig. 1b over the underlying grid network using entanglement swapping, we need 12 EPR pairs, which is the same number required to build the cluster state in Fig. 1a. The crucial difference is that, while the cluster state can accommodate more communication requests, the direct generation of the graph states in Fig. 1b via entanglement swapping limits the communication scenarios that we can implement.
The following lemma enables the visualization of entanglement generation. The proof is given in Supplementary Information.
Lemma 1
(Equivalence of measurements). X-measurements along a shortest path between two nodes are equivalent to performing a series of local complementations on the path, followed by Z-measurements on the intermediate nodes.
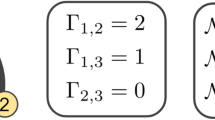
Lemma 1 allows us to transform the problem of establishing entanglement between nodes into finding suitable graphs by successive local complementations of the network graph. These repeated local complementations generate an orbit, the LC-orbit.24 If the only request for communication is between two nodes, then a shortest path with minimal neighborhood is chosen, in order to minimize the number of measurements. However, if the problem at hand is to connect more than one pair of nodes, the local complementation path will be chosen differently, according to the resulting graph. Even if not at first apparent, this is the strategy for the well-known butterfly network scheme.25,26 The butterfly network as a graph state is visualized in Fig. 2a, where in order to create EPR pairs between nodes {1, 6} and {2, 5} (cf. Fig. 2f), X-measurements are done on nodes 3 and 4. Via Lemma 1 this is equivalent to finding a graph in the LC-orbit of the butterfly, where edges (1, 6) and (2, 5) exist, and no edge between sets {1, 6} and {2, 5} exists. This graph is found via consecutive local complementations on nodes 1, 3 and 4 (Fig. 2b–d). A Z-measurement on nodes 3 and 4 allows to extract the two required EPR pairs (Fig. 2e, f). Note that without the second request for connection of nodes 2 and 5, the algorithm might have chosen another path to do X-measurements. Similarly, the sequence of subfigures in Fig. 3 demonstrates the equivalent process for the 9-qubit cluster state. In this sense, local complementation allows to bypass bottlenecks.
An EPR pair and a residual graph state are distilled from a cluster state with 9 qubits (a) using the X-protocol on the path (1, 2, 5, 6, 9). This is visualized by considering (b) local complementations with respect to nodes 1, 2, 5, 6, 1, followed by (c) the deletion of nodes 2, 5, 6 on the graph that describes the graph state
Bottleneck quantum networks
The butterfly network is of particular interest regarding quantum computing; in ref. 35 it was shown that any two-qubit unitary operation can be deterministically implemented over such a scheme. Concerning network efficiency, we say that a network has a bottleneck with respect to a given communication request if all possible routing solutions involve overlapping paths between at least two pairs of nodes. In quantum networks a bottleneck is equivalent to requiring more than one EPR pair per physical link when trying to establish long distance quantum communication via teleportation. For example, we observe that one of the butterfly’s edges becomes a bottleneck when we aim to build repeater lines to create entanglement between nodes {1, 6} and {2, 5} in Fig. 2a. The X-protocol solves the above communication task bypassing the bottleneck in the network. We can further show that the butterfly network is uniquely minimal with respect to the number of nodes. The following two propositions formalize this fact, and their proof is by exhaustive search.
Proposition 1
(No bottleneck). There is no 5-node graph state that has a bottleneck for simultaneous communication between two pairs of nodes and that can be solved using local Cliffords and a Pauli measurement of a single node.
Proposition 2
(Bottleneck). There are only four 6-node graph states that have a bottleneck for simultaneous communication between two pairs of nodes and that can be solved using local Cliffords and Pauli measurements.
The four 6-node graph states that have a bottleneck for simultaneous communication between two pairs of nodes and that can be solved using local Cliffords and Pauli measurements are obtained by relabeling the butterfly network (cf. Fig. 2a). Specifically, if we intend to establish EPR pairs between nodes {1, 6} and {2, 5}, we obtain the four graphs by exchanging labels within the sets {3, 4} and {1, 6}. Note that in allowing arbitrary local Cliffords and Pauli measurements we considered a wider class of possible algorithms than just the aforementioned X-protocol.
Obtaining GHZ and other multi-partite resources
As a further aspect, we now turn to the key question of how to extract resource states such as GHZ states from a given graph state. The more general question, whether from a given graph state vector |G〉 we can extract another graph state vector |H〉 via a sequence of local measurements, has recently been proven to be NP-complete.31 This was done by solving a well-known problem in graph theory called the VERTEX-MINOR problem, which asks whether from a graph G, another graph H can be extracted via a sequence of (i) local complementations and (ii) deletion of vertices. Note that the NP-completeness of deciding whether graph H is a vertex-minor of G has been proven for labeled graphs, which are relevant for communication scenarios, since the nodes are distinct.
Having said that, there are polynomial-time algorithms that solve the problem for important instances. A first relevant instance involves GHZ states,36,37 which are essential resources for multi-partite schemes in quantum networks beyond point-to-point architectures, such as quantum secret sharing.8,9 Building upon the method described in Theorem 1, we can show the following corollary.
Corollary 1
(Extraction of GHZ3 states). We can always distill a 3-partite GHZ state between arbitrary vertices of a connected graph state in polynomial time.
In order to obtain a 3-partite GHZ state, we use a slightly altered version of the X-protocol. The proof examines different cases corresponding to distinct relative positions of the three vertices within the graph and is given in the Supplementary Information. We now propose a sufficient criterion in order to extract 4-partite GHZ states; note that the extraction of a complete graph of four nodes (which is a graph representing a GHZ4) is thought to be difficult in general.38
Proposition 3
(Extraction of GHZ4 states). We can distill a 4-partite GHZ state from a graph state when the underlying graph has a repeater line as vertex-minor, which contains all four nodes of the final GHZ state and at least one extra node between two pairs of the nodes.
The required criterion is very likely to be fulfilled for simple network architectures, over which the graph state will be shared. Figure 4 demonstrates this for a short-distance square-grid network, which is used to share a cluster state. Here, Fig. 4c visualizes the minimal repeater line that is described in Proposition 3. The proof of said proposition is given in the Supplementary Information.
Prototypical extraction of a GHZ4 state. In order to distill a GHZ4 state between the nodes 1, 2, 4 and 5 of a 12 qubit cluster state (a), we Z-measure three nodes (b) and X-measure the four remaining intermediate nodes, thus isolating a repeater line (c) in accordance with Proposition 3. We then perform consecutive local complementations on nodes 2 (d), 3 (e), and 4 (f). Node 3 is finally Z-measured (g) to establish the desired GHZ4 state
A more general result using the notion of rank-width is based on refs. 31,39,40,41,42. The rank-width k of a graph G is the minimum width of all its rank decompositions. This amounts to k being the smallest integer such that G can be related to a tree-like structure by recursively splitting its vertex set so that each cut induces a matrix of rank at most k. The rank-width is bounded iff the clique-width is bounded.43 Graphs with rank-width at most one are those where all connected induced subgraphs preserve distance.27
Observation
(Extraction of graph states from graph states with bounded rank-width). For a graph state vector |G〉 with an underlying graph of bounded rank-width, there exists a poly-time algorithm that decides if a graph state vector |H〉 can be extracted from |G〉 using local Clifford operations and Z-measurements, and gives the sequence of operations to be applied.
For a graph G, there exist algorithms with runtime O(|G|3)30 that, for a fixed k, either give a rank decomposition of width at most 24k or reply that the rank-width is larger than k. Then, when such a rank decomposition is given, for a fixed graph H, a linear time algorithm can test whether H is a vertex minor of G and return the sequence of local complementations and vertex deletions to be applied.39 The local complementations on G correspond to local Clifford operations on |G〉. The vertex deletions correspond to measuring the relevant qubits of the resulting graph state in the Z-basis, which finally yields the graph state vector |H〉. Many structured graphs have bounded rank-width, e.g., highly sparse random graphs44 and graphs with bounded tree-width.45 For those graphs, the above observation readily applies, and it can be decided whether resource states can be extracted.
Discussion
In this work, we have discussed the manipulation of multi-partite entangled resources for applications in quantum routing and quantum communication across quantum networks. We have seen that via local complementation, quantum routing schemes with a reduced number of measurements outperforming standard repeater schemes can be found, bottlenecks in quantum networks can be treated and the question of extracting multi-partite resources largely addressed.
It is important to stress that, while these algorithms are classical, they apply to true multi-partite entangled quantum states and can potentially be used to achieve parallel quantum key distribution and notions of conference key agreement. It is worth examining how to extend the proposed methods in order to achieve teleportation of quantum states from one set of nodes (sources) to another (sinks), a problem analogous to the k-pair problem in classical network routing. To some extent, such schemes have been studied in the butterfly setting7,46,47,48,49,50 when bipartite entangled states are shared, and in the more general setting,26 by establishing a connection with measurement-based quantum computation.51,52,53 However, using linear codes (as in ref. 26) to map the network has a shortcoming; they require the generation of two-colorable graph states at each node, and it is not straightforward to see how to make this mapping to a given network structure, where each node holds a single qubit. A possible solution would be to extend the methods in this work, and to use local complementation and graph transformations in order to address this problem for specific network architectures.
Finally note that since every stabilizer state is equivalent to some graph state,54 the methods laid out here are also expected to be useful in the design of quantum error correcting codes. In conclusion, further studies of manipulating multi-partite entangled resources for quantum routing seem to be urgently needed, especially in the light of the rapid experimental progress on quantum networks.
References
Briegel, H.-J., Dür, W., Cirac, J. I. & Zoller, P. Quantum repeaters: the role of imperfect local operations in quantum communication. Phys. Rev. Lett. 81, 5932–5935 (1998).
Duan, L.-M., Lukin, M. D., Cirac, J. I. & Zoller, P. Long-distance quantum communication with atomic ensembles and linear optics. Nature 414, 413–418 (2001).
van Loock, P. et al. Hybrid quantum repeater using bright coherent light. Phys. Rev. Lett. 96, 240501 (2006).
Acin, A., Cirac, J. I. & Lewenstein, M. Entanglement percolation in quantum networks. Nat. Phys. 3, 256–259 (2007).
Acin, A. et al. The European quantum technologies roadmap. arXiv:1712.03773 [quant-ph] (2017).
Zwerger, M., Dür, W. & Briegel, H. J. Measurement-based quantum repeaters. Phys. Rev. A 85, 062326 (2012).
Pirandola, S., Eisert, J., Weedbrook, C., Furusawa, A. & Braunstein, S. L. Advances in quantum teleportation. Nat. Phot. 9, 641–652 (2015).
Cleve, R., Gottesman, D. & Lo, H.-K. How to share a quantum secret. Phys. Rev. Lett. 83, 648–651 (1999).
Bell, B. et al. Experimental demonstration of graph-state quantum secret sharing. Nat. Commun. 5, 5480 (2014).
Bao, N. & Yunger Halpern, N. Quantum voting and violation of arrow’s impossibility theorem. Phys. Rev. A 95, 062306 (2017).
Ribeiro, J., Murta, G. & Wehner, S. Fully device-independent conference key agreement. Phys. Rev. A 97, 022307 (2018).
Chen, K. & Lo, H.-K. Conference key agreement and quantum sharing of classical secrets with noisy ghz states. In Int. Sym. Inf. Th. 1607–1611 (2005).
Epping, M., Kampermann, H. & Bruß, D. Large-scale quantum networks based on graphs. New J. Phys. 18, 053036 (2016).
Kimble, H. J. The quantum internet. Nature 453, 1023–1030 (2008).
Schoute, E., Mancinska, L., Islam, T., Kerenidis, I. & Wehner, S. Shortcuts to quantum network routing. arXiv:1610.05238 [cs.NI] (2016).
Zwerger, M., Pirker, A., Dunjko, V., Briegel, H. J. & Dür, W. Long-range big quantum-data transmission. Phys. Rev. Lett. 120, 030503 (2018).
Żukowski, M., Zeilinger, A., Horne, M. A. & Ekert, A. K. “event-ready-detectors” bell experiment via entanglement swapping. Phys. Rev. Lett. 71, 4287–4290 (1993).
Sun, Q.-C. et al. Entanglement swapping with independent sources over an optical-fiber network. Phys. Rev. A 95, 032306 (2017).
Hein, M., Eisert, J. & Briegel, H. J. Multiparty entanglement in graph states. Phys. Rev. A 69, 062311 (2004).
Hein, M. et al. General scheme for perfect quantum network coding with free classical communication. Proceedings of the International School of Physics ‘Enrico Fermi’ on ‘Quantum Computers, Algorithms and Chaos’ (pp. 115–218. IOS Press, Amsterdam, 2005).
Kruszynska, C., Miyake, A., Briegel, H. J. & Dür, W. Entanglement purification protocols for all graph states. Phys. Rev. A 74, 052316 (2006).
Pirker, A., Wallnöfer, J. & Dür, W. Modular architectures for quantum networks. New J. Phys. 20, 053054 (2018).
Markham, D. & Krause, A. A simple protocol for certifying graph states and applications in quantum networks. arXiv:1801.05057 [quant-ph] (2018).
Bouchet, A. Graphic presentations of isotropic systems. J. Comb. Th. B 45, 58–76 (1988).
Leung, D., Oppenheim, J. & Winter, A. Quantum network communication – the butterfly and beyond. IEEE Trans. Inf. Th. 56, 3478–3490 (2010).
Epping, M., Kampermann, H. & Bruß, D. Robust entanglement distribution via quantum network coding. New J. Phys. 18, 103052 (2016).
Oum, S.-I. Rank-width and vertex-minors. J. Comb. Th. B 95, 79–100 (2005).
Hoyer, P., Mhalla, M. & Perdrix, S. Resources required for preparing graph states. In Algorithms and Computation ISAAC 2006 (ed. Asano, T.) vol. 4288 (Springer, 2006).
Bahramgiri, M. & Beigi, S. Enumerating the classes of local equivalency in graphs. arXiv:math/0702267 [math.CO] (2008).
Oum, S.-I. Approximating rank-width and clique-width quickly. ACM Trans. Algor. 5, 1 (2008).
Dahlberg, A., Helsen, J. & Wehner, S. How to transform graph states using single-qubit operations: computational complexity and algorithms. arXiv:1805.05306 [quant-ph] (2018).
Van den Nest, M., Dehaene, J. & De Moor, B. Graphical description of the action of local clifford transformations on graph states. Phys. Rev. A 69, 022316 (2004).
Van den Nest, M., Dehaene, J. & De Moor, B. Efficient algorithm to recognize the local clifford equivalence of graph states. Phys. Rev. A 70, 034302 (2004).
Chen, L. & Hayashi, M. Multicopy and stochastic transformation of multipartite pure states. Phys. Rev. A 83, 022331 (2011).
Akibue, S. & Murao, M. Network coding for distributed quantum computation over cluster and butterfly networks. IEEE Trans. Inf. Theory 62, 6620–6637 (2016).
Greenberger, D. M., Horne, M. A. & Zeilinger, A. Going beyond bell’s theorem. In Bell’s Theorem, Quantum Theory, and Conceptions of the Universe (ed. Kafatos, M.) 69–72 (Kluwer, 1989).
Wallnöfer, J., Zwerger, M., Muschik, C., Sangouard, N. & Dür, W. Two-dimensional quantum repeaters. Phys. Rev. A 94, 052307 (2016).
Dabrowski, K. K. et al. Recognizing small pivot-minors (2018). Accepted to the 44th International Workshop on Graph-Theoretic Concepts in Computer Science (WG2018).
Dahlberg, A. & Wehner, S. Transforming graph states using single-qubit operations. arXiv:1805.05305 [quant-ph] (2018).
Oum, S.-I. Rank-width: Algorithmic and structural results. Disc. Appl. Math. 231, 15–24 (2017).
Courcelle, B. & Oum, S.-I. Vertex-minors, monadic second-order logic, and a conjecture by seese. J. Comb. Th. B 97, 91–126 (2007).
Courcelle, B., Makowsky, J. A. & Rotics, U. Linear time solvable optimization problems on graphs of bounded clique-width. Th. Comp. Sys. 33, 125–150 (2000).
Oum, S.-I. & Seymour, P. Approximating clique-width and branch-width. J. Comb. Th. B 96, 514–528 (2006).
Lee, C., Lee, J. & Oum, S.-I. Rank-width of random graphs. J. Graph Th. 70, 339–347 (2012).
Oum, S.-I. Rank-width is less than or equal to branch-width. J. Graph Th. 57, 239–244 (2008).
Hayashi, M., Iwama, K., Nishimura, H., Raymond, R. & Yamashita, S. Quantum network coding. In Annual Symposium on Theoretical Aspects of Computer Science, 610–621 (Springer, 2007).
Hayashi, M. Prior entanglement between senders enables perfect quantum network coding with modification. Phys. Rev. A 76, 040301 (2007).
Owari, M., Kato, G. & Hayashi, M. Single-shot secure quantum network coding on butterfly network with free public communication. Quantum Sci. Technol. 3, 014001 (2017).
Kobayashi, H., Le Gall, F., Nishimura, H. & Rötteler, M. General scheme for perfect quantum network coding with free classical communication. In Automata, Languages and Programming, 622–633 (Springer, 2009).
Kobayashi, H., Gall, F. L., Nishimura, H. & Rötteler, M. Constructing quantum network coding schemes from classical nonlinear protocols. In 2011 IEEE International Symposium on Information Theory Proceedings, 109–113 (2011).
Raussendorf, R. & Briegel, H. J. A one-way quantum computer. Phys. Rev. Lett. 86, 5188 (2001).
Gross, D. & Eisert, J. Novel schemes for measurement-based quantum computation. Phys. Rev. Lett. 98, 220503 (2007).
de Beaudrap, N. & Rötteler, M. Quantum linear network coding as one-way quantum computation. In 9th Conference on the Theory of Quantum Computation, Communication and Cryptography (TQC 2014), vol. 27, 217–233 (2014).
Schlingemann, D. Stabilizer codes can be realized as graph codes. Quantum Info Comput. 2, 307–323 (2002).
Acknowledgements
We thank S. Wehner and A. Dahlberg for discussions. Upon completion of this work, we became aware of work similarly motivated 31,39. A.P. acknowledges support from the Alexander von Humboldt Foundation and from European Union’s Horizon 2020 Research and Innovation program under Marie Sklodowska-Curie Grant Agreement No. 841534. F.H. acknowledges support from the Studienstiftung des Deutschen Volkes, F.H. and J.E. support from the BMBF (Q.Com-Q, Q.Link.X), J.E. from the DFG (EI 519/14-1, EI 519/9-1), the Templeton Foundation, and the ERC (TAQ).
Author information
Authors and Affiliations
Contributions
F.H., A.P. and J.E. performed the theoretical analysis. F.H. developed numerical software tools. J.E. conceived and supervised the project. F.H., A.P. and J.E. wrote the manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note: Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Hahn, F., Pappa, A. & Eisert, J. Quantum network routing and local complementation. npj Quantum Inf 5, 76 (2019). https://doi.org/10.1038/s41534-019-0191-6
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41534-019-0191-6
This article is cited by
-
Optimal quantum key distribution networks: capacitance versus security
npj Quantum Information (2024)
-
Mlora-CBF: efficient cluster-based routing protocol against resource allocation using modified location routing algorithm with cluster-based flooding
Wireless Networks (2024)
-
Quantum teleportation based on non-maximally entangled graph states
Quantum Information Processing (2023)
-
Quantum NETwork: from theory to practice
Science China Information Sciences (2023)
-
Efficient Mobile Ad Hoc Route Maintenance Against Social Distances Using Attacker Detection Automation
Mobile Networks and Applications (2023)