Abstract
The random number generators (RNGs) are an indispensable tool for information security. Among various approaches, the radioactive decay has been considered as a promising candidate of RNGs for over half a century, on account of its seemingly unpredictable decay timings as quantum phenomena. However, the security of these radioactive RNGs has not been proven so far. Here we prove the security by a change of tactics, that is, by rewriting decay timings into decay directions, which allows us to ensure the secrecy with the help of the parity invariance deeply rooted in the fundamental law of nature. Our result demonstrates that the foundational properties of particle physics, such as the symmetry of interactions, can be used as a firm basis for the RNGs.
Similar content being viewed by others
Introduction
In information technology, random number generators (RNGs) refer in general to devices that output numbers distributed in a certain range uniformly. If one wishes to use them for information security purposes in particular, their outputs must be secret1 as well. If, in addition, the RNG is to be usable by anyone, these two properties need to be guaranteed by some objective evidence.
Suppose, for instance, that one buys a dice from a not-necessarily-reliable vendor and throws it alone in a closed room. For this process to generate a uniform distribution, one must be sure with evidence that the dice is fair. As for the secrecy, separate evidence is needed to ensure that the outputs are unpredictable and unknown to outside, even to the vendor or the manufacturer who had all the chances to tamper with the dice such that the outputs follow a certain pattern. But how can one find an objective basis of secrecy that anyone can agree with? Arguably, the most convincing basis of secrecy would be the laws of nature, that is, if nature assures the secrecy by law, then nothing can be utilized to predict the outputs. In this respect, the laws underlying quantum phenomena look promising for providing a secure RNG for which the output is rigorously proven to be secret.
The notion of secure RNG based on the laws of quantum mechanics is not new2,3,4,5,6,7,8,9,10,11,12,13,14,15,16. In fact, RNGs using photons have been studied intensively over the years, and some of them have now been strictly proven to be secure. For example, we have the single photon RNG which employs two complementary bases + , × of the polarization. Here, the legitimate user (henceforth, Alice) generates a single photon state possessing a polarization in one basis, say, the vertical polarization state \(\left|\updownarrow \right\rangle\) belonging to basis + , and then measures it in the other, diagonally slanted × basis. Alice adopts the measurement result as the random bits.
The major concern here is that the vendor of the light source may be an eavesdropper (henceforth, Eve). In that event, Eve could have tampered with the source to retain correlation with her own device, and may have access to the random bits as a result.
The security against such an eavesdropper can still be argued as follows. Being a pure state, the initial state \(\left|\updownarrow \right\rangle\) cannot be entangled with any state on the outside, and hence has no correlation with Eve’s device. When the state is measured in the complementary basis × , each measurement result, ⤡ or ⤢ , occurs with probability one half exactly. Thus the random bits are distributed uniformly, and they are uncorrelated with Eve. Unfortunately, the single photon RNGs have a practical drawback because the energy of the photon used in a typical device is minute and, accordingly, the detector must be highly sensitive. For this reason, the single photon RNGs are subject to constraints for reduction both in their size and cost.
Besides the single photon RNGs, there exists another type of RNG methods which also exploit quantum phenomena, that is, those using radiations from nuclear decays17,18,19,20,21,22. In these radioactive RNG methods one detects radiations and adopts the timings of the detections as random numbers. These methods, proposed prior to the single photon RNGs17, have the advantage that their device, which can be as small and simple as that of a single photon RNGs, requires no power supply22,23,24,25 for its (radioactive) source. Radioactive RNG chips of a few square millimeters have already been manufactured using 241Am26,27,28.
However, there is no rigorous security proof for the radioactive RNGs so far, despite that it has been known for more than half a century that they generate a uniform distribution19. The basic reason for this dissatisfying situation is that the decay-timing properties, which are essential for the security proof, are difficult to obtain in a precise manner with the phenomenological models such as Gamow’s theory29,30 for nuclear decays, where adjustable parameters are introduced to describe the exponential decays pertinent to various transitions realized physically.
Here we show, nevertheless, that the radioactive RNG can admit a rigorous security proof from the standpoint of the universally composable security31, provided that the radioactive decay is parity symmetric, i.e., invariant under space inversion. In fact, such cases are available generically for a nuclide (such as 241Am) that exhibits alpha decays caused by the parity-conserving strong interaction. The device structure we assume is as simple as before, consisting only of a radiation source with one or two detector(s) allowing for the parity symmetry to ensure the required security.
Results
RNG method
We consider the following type of the radioactive RNG method. By using a device consisting of a radiation source and a detector D (Fig. 1), Alice executes the following procedure (Fig. 2): Alice chooses integer parameters nfin, nthr, and N satisfying 0 < nfin ≤ nthr ≤ N. She also selects a function fs randomly from a predetermined set of functions \({{{{{{{\mathcal{F}}}}}}}}=\{{f}_{s}\}\), each of which outputs an nfin bit string (for example, \({{{{{{{\mathcal{F}}}}}}}}\) is a universal2 function family32; also see Methods). Then, our radioactive RNG is implemented in two steps:
-
(i)
Measurement of decay timings: Alice measures radiations from the source, using detector D, in time bins i = 1, …, N. She then records the measurement result as the list of time bins where a detection occurred; i.e. as \({{{{{{{\bf{i}}}}}}}}=({i}_{1},\ldots ,{i}_{{n}_{\det }})\), with \({n}_{\det }\) being the number of detections, and ij being in the increasing order, \(1\le {i}_{1} \, < \, {i}_{2} < \cdots < {i}_{{n}_{\det }}\le N\). Alice aborts if \({n}_{\det } \, < \, {n}_{{{{{{{{\rm{thr}}}}}}}}}\).
-
(ii)
Randomness extraction: Alice calculates the final bits r = fs(i) of length nfin.
The purpose of randomness extraction is to extract from a measurement result i, which may be partially known to Eve, random bits r completely unknown to Eve. In the above picture, i being partially known to Eve is expressed by its being a mixture of black (unknown) and white (known) elements. The number of unknown bits equals the smooth conditional min-entropy \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\), a function of ρIE.
The purpose of each step is as follows (Fig. 2). Step (i) generates raw data i to be used as the source of the final bits r. For r to be secure, not all, but a certain fraction of i need to be unknown to Eve. The standard theoretical results say that the size of this unknown fraction equals a quantity called the smooth conditional min-entropy \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\), which is a function of the joint state ρIE of variable i and Eve (see Methods for the rigorous definitions).
In step (ii) she extracts these \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\) bits that are unknown, and generate r, which is completely unknown to Eve.
We denote the width of one time bin by Δt. In order to simplify later presentations, without loss of generality, we assume that in every time bin, Alice starts her measurement at the beginning of the time bin and finishes it in a finite time ≤Δt.
Conditions on the device
Hence the security analysis is reduced to lower bounding \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\). We are concerned with the possibility that the radiation source to be measured in step (i) may be entangled with Eve, and through that entanglement Eve may access i; i.e., \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\) may become too small to guarantee the security of r. The goal of this paper is to nullify such eavesdropping strategy by making use of the parity symmetry.
To this end, we assume the following three conditions on the device. The first two of them, (A) and (B), in particular, are introduced in order to realize the parity symmetry in the device.
-
(A)
Radiation source: At the beginning of each time bin (i.e., immediately before Alice’s measurement), the state of radiations is parity invariant.
-
(B)
Detector: Detector D is housed within one hemisphere around the source.
-
(C)
Effect on radiations by measurements: Effect on radiations in the vicinity of D, caused by Alice’s measurement of a time bin i, is washed away by the beginning of the next time bin i + 1.
In addition, we introduce the following notions for later convenience.
-
(D)
Detections, ‘double’ events and dark counts: Except with probability δ, there are at most ndouble‘double’ events, and at most ndark time bins where dark counts occur. Here the ‘double’ events are defined as follows: Suppose that, in addition to the actual detector D, there is another detector \({{{{{{{\rm{D}}}}}}}}^{\prime}\) that constitutes a parity symmetric configuration together with D. Then ‘double’ events are those for which detector D and \({{{{{{{\rm{D}}}}}}}}^{\prime}\) both detect the signal.
Note that the number ndouble of these events can be bounded from above by that of multi-particle events, nmulti. Therefore, one does not actually implement the extra detector \({{{{{{{\rm{D}}}}}}}}^{\prime}\), if nmulti is known.
The statements of condition (A) and (D) require some explanation, which we give now. In regards to condition (A), there are four types of fundamental interactions (electromagnetic, weak, strong, and gravitational interactions). Since α-decay and γ-decay are caused, respectively, by the strong interaction and the electromagnetic interaction, and not by the weak interaction, its radiation is parity (space inversion) invariant. This provides us with an ideal basis for supporting the randomness we hoped for, as it is ensured by a symmetry principle afforded by the fundamental particle interactions. Let \({{{{{{{{\mathcal{H}}}}}}}}}_{A}\) be the Hilbert space describing radiated particles in the vicinity of detector D. Also, let \({{{{{{{{\mathcal{H}}}}}}}}}_{E}\) be that describing all degrees of freedom of Eve (cf. Fig. 2). We assume that in \({{{{{{{{\mathcal{H}}}}}}}}}_{A}\) the parity operator PA is well defined and satisfies \({P}_{A}^{2}=1\). (Throughout the paper, we use the convention of omitting the identity operators included in a tensor product; hence e.g., PA is an abbreviation of PA ⊗ 1E.) Under this setup, we say that the joint state ρAE(t) of \({{{{{{{{\mathcal{H}}}}}}}}}_{A}\) and \({{{{{{{{\mathcal{H}}}}}}}}}_{E}\) at time t is parity invariant, if it satisfies
Condition (A) says that the parity invariance (1) holds at the beginning of each time bin, i.e. at t = 0, Δt, …, (N − 1)Δt.
Next we discuss the feasibility of each of the conditions given above.
First, condition (A) is widely believed to be true for a nuclide which decays by parity-conserving interactions (e.g., strong and electromagnetic interactions, as in the α- and the γ-decays)33. It has been well-tested through the measurement of the energy spectrum and the angular distribution of the decay with the comparison to the phenomenological model29,30.
However, as we deal here with an RNG, we must be aware of a possible scenario where such a choice may not be sufficient for guaranteeing condition (A). For instance, the nuclide could have been tampered with by Eve, before purchased by Alice, to the extent of destroying the parity invariance. We point out that, even in that event, Alice can still verify condition (A) by performing a random sampling test on the source, that is, she measures the radiation from the source and checks if the results, such as the energy spectrum and the angular distribution, are always consistent with condition (A). As far as the nuclei remain to be in the quantum domain and described by the standard nuclear theory, this is enough for ensuring condition (A). One may, however, go beyond and wonder if Eve could generate the seemingly parity invariant measurement results with a deterministic source supplied by some classical means. Although highly inconceivable given the fact that nuclear decay is intrinsically quantum and does not allow any classical intervention, this possibility will still be disposed of by examining the parity eigenvalue of the radiation state, i.e., if it has a definite parity, either ‘even’ or ‘odd’, under the operation PA. This is analogous to the tomography performed when we examine whether the source emitting polarized photons ⤡ and ⤢ with equal probability is operated deterministically or not. In that case, finding the state to be in a definite polarization, either ↕ or ↔ , ensures that the source is a superposition of ⤡ and ⤢ , and this corresponds to finding the radiation to be in either ‘even’ or ‘odd’ state in our case of nuclear decay.
Second, condition (B) can always be verified visually.
Third, condition (C) is a pure assumption, but it is commonly presupposed in the literature of quantum key distribution and physical RNGs including the single photon RNG mentioned in the Introduction.
Finally, the parameters in condition (D) can be estimated as follows. For the dark counts ndark, we simply recall that their rate can generally be bounded from the property of detector D, and hence the number ndark in total round of N can be statistically evaluated by the standard interval estimation methods.
As for the number of ‘double’ events ndouble, the most straightforward evaluation method is to install the additional detector \({{{{{{{\rm{D}}}}}}}}^{\prime}\) (which is supposed to be parity symmetric to D) mentioned in condition (D), and count the number of coincidence events where both D and \({{{{{{{\rm{D}}}}}}}}^{\prime}\) click. In case D and the actual detector installed for \({{{{{{{\rm{D}}}}}}}}^{\prime}\), which we denote by D″, is not quite parity symmetric to D and does not share exactly the same properties, we may consider the completely positive maps (elements of completely positive instruments) \({M}_{{{{{{{{\rm{D}}}}}}}}}^{\prime}\) and \({M}_{{{{{{{{\rm{D}}}}}}}}}^{^{\prime\prime} }\) describing \({{{{{{{\rm{D}}}}}}}}^{\prime}\) and D″, respectively. With this, if we have, e.g., \({M}_{{{{{{{{\rm{D}}}}}}}}}^{^{\prime\prime} } \, > \, {M}_{{{{{{{{\rm{D}}}}}}}}}^{\prime}\) (or \({M}_{{{{{{{{\rm{D}}}}}}}}}^{^{\prime\prime} }-{M}_{{{{{{{{\rm{D}}}}}}}}}^{\prime}\) is a positive map), then we find an upperbound for ndouble from the coincidence counts measured with D and D″.
We also mention that, although somewhat artificial, one may simplify the process by imposing an additional assumption (which amounts to relaxing the security assumptions to some extent) that the source behaves the same way regardless of whether the user is estimating the parameters or not. This allows us to estimate the rate of ‘double’ events ndouble at any time, such as at the time of shipment from the factory or at the initial setting before the actual use, based on the standard interval estimation methods again.
Security of measurement result i
Under these conditions, the security of measurement result i can be guaranteed as follows.
Theorem 1
The smooth min-entropy \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\) of i, conditioned on Eve’s degree of freedom E, is bounded as
By combining the leftover hashing lemma34 and Theorem 1, we can guarantee the security of r as follows.
Corollary 1
For a given security parameter ε > 0, the sequence of the final bits r is ε + δ-secure, if Alice uses a universal2 hash function f32 for randomness extraction, and if its output length nfin satisfies
Recall that ndouble and ndark depend on δ through condition (D). Hence the right hand side of (3) depends on both ε and δ.
Proof of Theorem 1
The outline of the proof is as follows. On one hand in the actual implementation, we use detection timings as the origin of randomness. On the other hand in the security analysis, we instead analyze the absence/presence (denoted by zi = 0, 1) of detection in each time bin i. This is possible since they are merely two different formats of the same measurement results. Now, by temporarily limiting ourselves to an ideal situation that the radiation consists of one particle and also that the detector has a unit efficiency with no dark count and covers the entire lower hemisphere, we show that variables zi correspond to measuring the direction, up or down, in the radiation. Hence, measuring a parity symmetric radiation in this setting means measuring a parity invariant state using a pair of projectors interchangeable under parity operation. It then follows that the values zi = 0, 1 occur with an equal probability, and in addition, the resulting (sub-normalized) states on Eve’s side remain fixed irrespective of the values zi. In other words, Eve can gain no information of zi by any measurement, which establishes the security we want. The security in non-ideal situations can also be shown by essentially the same argument.
In order to simplify the analysis, we use the virtual protocol approach (also known as game transform in modern cryptography). In this approach, instead of analyzing the actual RNG directly, one modifies it and construct a virtual RNG, as well as a quantity \(H^{\prime}\) arising there which lower bounds \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\). Then analyzing the virtual RNG, one obtains a lower bound on \(H^{\prime}\), which also lower bounds \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\) by definition. With the virtual RNG and \(H^{\prime}\) designed properly, this allows one to obtain a lower bound on \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\) by a simpler analysis. We stress that virtual RNGs will only be used for simplifying the theoretical analysis, and never need to be implemented in practice.
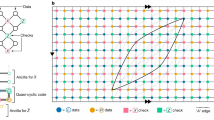
As the first example of such virtual RNGs, we consider the case where Alice records the measurement result i in a different format z = (z1, …, zN) where zi = 0 (zi = 1) indicates the absence (presence) of a detection in time bin i (Fig. 3). In other words, Alice records measurement results zi of all time bins i = 1, …, N, instead of timings i where a detection occurs. It is straightforward to see that i and z are in a one-to-one correspondence, and are thus equally unknown to Eve,
Thus to lower bound \({H}_{\min }^{\delta }({{{{{{{\bf{I}}}}}}}}| E)\), it suffices to bound \({H}_{\min }^{\delta }({{{{{{{\bf{Z}}}}}}}}| E)\); this is an example of the quantity \(H^{\prime}\), mentioned above.
Next we will modify this virtual RNG outputting z further, such that the parity transform PA, is related to bit flips of zi. Then we will make use of this relation to lower bound \({H}_{\min }^{\delta }({{{{{{{\bf{Z}}}}}}}}| E)\).
Ideal situation
To elucidate this relation with a situation simplified from the actual one (Fig. 4(a)), we temporarily idealize conditions (A) and (B) as follows.
-
(A')
At the beginning of each time bin, the state of radiations is parity invariant and consists of exactly one particle.
-
(B')
Detector D is perfect (i.e., with a unit efficiency and no dark counts) and covers exactly the entire lower hemisphere (Fig. 4(b)). Hence D goes off iff one particle or more go downward.
Then we can modify our radioactive RNG further such that bit flips of zi and PA become equivalent.
Panel (a) on the left shows the side view of our radioactive RNG. We assume that the detector D is housed within one (the lower) hemisphere (condition (B)). Panels (b), (c) and (d) depict theoretical models introduced for simplifying the description of the security proof, although these three never need to be implemented in practice. Panel (b) depicts the idealized setting satisfying conditions (A') and (B'), where the detector D alone can determine the direction, up or down, of the emitted particle. Similarly, panel (c) depicts the setting with two idealized detectors placed above and below the source. The layout given in (c) is, in effect, equivalent to the that given in (b) of the virtual RNG using two ideal detectors. Likewise, the layout depicted in (d) describes the virtual RNGs corresponding to the case (a).
To see this, first note that detector D alone can determine whether the particle went upward or downward. Indeed, if D detected the particle (zi = 1), it means that it went down due to (B’); and if not (zi = 0), two conditions together say that it went up.
These results zi = 0, 1 can alternatively be obtained by a pair of perfect detectors, D↓ and D↑, each exactly covering the upper and the lower hemispheres (Fig. 4(c)). Thus we can define another virtual RNG satisfying (4).
Virtual RNG 1: Using D↓ and D↑, Alice measures the source in time bins i = 1, …, N, and records the result as wi ∈ {↑, ↓}. She then lets zi = 0, 1 if wi = ↑, ↓.
Detectors D↑, D↓ are ‘covariant’ under PA; that is, if we let \({E}_{A}^{\uparrow }\), \({E}_{A}^{\downarrow }\) be projection operators on the upper and the lower hemispheres corresponding to D↑, D↓, they satisfy
Hence PA is equivalent to the flip of arrows wi = ↑, ↓, and thus to the bit flip of zi.
Next we use this parity covariance to show that wi are secure. Recall that ρAE before measurement is always parity invariant. Hence each wi is the result of measuring a parity invariant state ρAE using parity covariant projections \({E}_{A}^{\uparrow }\), \({E}_{A}^{\downarrow }\). Thus wi = ↑, ↓ occur with an equal probability, and in addition, the resulting (sub-normalized) states on Eve’s side are a fixed state, irrespective of wi,
due to properties (1) and (5). In other words, all elements of w = (w1, …, wN) are distributed uniformly, and Eve gains no information of it by any measurement. In terms of the min-entropy, this means
This completes the proof of Theorem 1 for the ideal situation.
General situation
We proceed to the proof of the general situation. We again construct a virtual RNG where a correspondence between bit flips of zi and PA holds. Alice again uses a detector pair D↓ and D↑ with D↓ being the actual detector D and D↑ being the parity transformed image of D (Fig. 4(d)).
As we no longer impose conditions (A’) and (B’), it is possible that none or both of this detector pair, instead of one, go off in a time bin. Hence each wi takes four values, wi ∈ {↑, ↓, none, double} (Table 1, 1st row).
In this case, the output zi of D ( = D↓) alone can be emulated from wi, by ignoring outputs of D↑ (Table 1, second row). Thus we can define a virtual RNG as follows.
Virtual RNG 2: Using D↓ and D↑, Alice measures the source in time bins i = 1, …, N, and records the result as wi ∈ {↑, ↓, none, double}. She then lets zi = g(wi), using function g specified in the second row of Table 1, where the output g(wi) satisfies
We will use a similar argument to the one in the ideal situation to bound the right hand side of (8) by exploiting the relation between measurement results and the parity transform PA. However, the argument needs to be modified, as the relation is not the same as in the ideal situation.
That is, unlike in the ideal situation, the bit flip of zi and PA may not be equivalent in general. This is because zi = 0, 1 may come from measurement results wi = ‘none’ or ‘double’, whose quantum measurements are not in general covariant under PA. On the other hand, measurements of wi = ↑ and ↓ are still covariant under PA, by definition of D↓, D↑.
Hence if we evaluate the min-entropy of wi in single detection events (i.e., time bins i where wi = ↑ or ↓; see Table 1, 3rd row), we have the ideal situation again, and the security can be shown by the same reasoning as before. The min-entropy thus obtained lower bounds \({H}_{\min }(g({{{{{{{\bf{W}}}}}}}})| E)\) on the right hand side of (8), since in general, the entropy of a part is not greater than that of the total. As a result, \({H}_{\min }(g({{{{{{{\bf{W}}}}}}}})| E)\) is lower bounded by the number of single detection events. (For the rigorous proof of statements made in this paragraph, see Methods.)
We can bound the number of single detection events as follows. The number D of the detection events is no larger than the sum of the number of the single detection events and the ‘double’ events. The ‘double’ events can occur if the multiparticle emission or the dark count occurs in either detector. Then due to condition (D), the number of single detection events can be further lower bounded by nthr − ndouble − 2ndark, except for probability δ, and we obtain Theorem 1.
As an example, we consider the performance of the RNG which has a prototype26 based on 241Am. In this RNG, the length of each time bin is 1 millisecond and the detection rate is about 0.055 per time bin. We may thus assume that it can be bounded by 0.05 from below and by 0.06 from above. Choosing the number N = 105 for the total rounds, we consider the protocol \(\epsilon ^{\prime}\)-secure with \(\epsilon ^{\prime} ={2}^{-50}\) following the standard practice and set nthr = N × 0.05. Although the rate of ‘double’ events is not measured directly, it is reasonable to estimate that the rate is bounded from above by (0.06)2/2 per time bin, since each nucleus decays independently and identically. This implies that, except with probability \(\epsilon ^{\prime} /2\), there are at most 305 ‘double’ events in N rounds35. The dark count rate is negligible and can be put to zero in effect, because the energy of α-decay of 241Am is around 5 MeV, which is much higher than the typical energy 1 eV of the optical photon. To sum up, the parameters in condition (D) are found to be \(\delta =\epsilon ^{\prime} /2,{n}_{{{{{{{{\rm{thr}}}}}}}}}=5000,{n}_{{{{{{{{\rm{double}}}}}}}}}=305,{n}_{{{{{{{{\rm{dark}}}}}}}}}=0\). Setting the parameter \(\epsilon =\epsilon ^{\prime} /2\) in Corollary 1, we find that this protocol is \(\epsilon ^{\prime}\)-secure and generates a random number of the length nfin = 4595 unless the protocol is aborted.
Conclusions
With the help of the parity symmetry, we solved the problem on the security of the radioactive RNG which had remained open over half a century, and further showed that this type of RNG can realize the universally composable security.
Unlike the model dependent description of decay-timing properties, the parity symmetry inherent to the system is much easier to handle from the first principle. When combined with the purely quantum nature of nuclear decays, it leads to the detection outcomes with intrinsic randomness. This is analogous to the high speed RNG36, where the laser phase fluctuations arising from spontaneous emissions, which are purely quantum, are responsible for the randomness. These two RNGs are different in strategy in that, while our radioactive RNG exploits the parity invariance, the optical quantum RNG36 uses a theoretical model of laser emission as the basic ingredient.
We stress that our proof method is quite distinct from those previously employed for photon RNGs. This can be seen most clearly in the property that one does not need any condition on the state ρAE except for the parity invariance Eq. (1). This gives a major merit to our method, exempting us from discussing any other properties, let alone an actual realization of the state ρAE. It should be noted that the condition in Eq. (1) is much stronger than PAρA(t)PA = ρA(t) which cannot ensure the security by itself.
We also note that, since previous arguments17,18,19,20,21,22 on radiation RNGs employed phenomenological models, it was impractical to assume any reliable conditions on the state ρAE (such as being the coherent state) at an arbitrary accuracy. In contrast, the parity invariance we used is a fundamental property of particle interactions and, as such, it can provide a robust basis for ensuring the security of random numbers.
Methods
Definition of security and the leftover hashing
We review definition of the security of RNG, as well as techniques for guaranteeing it.
The sequence of final bits r is secure when it is distributed uniformly and unknown to Eve. This can be formalized as follows. Given an actual state ρRE, we define the corresponding ideal state to be \({\rho }_{{{{{{{{\bf{R}}}}}}}}E}^{{{{{{{{\rm{ideal}}}}}}}}}={2}^{-{n}_{{{{{{{{\rm{fin}}}}}}}}}}{{\mathbb{I}}}_{{{{{{{{\bf{R}}}}}}}}}\otimes {\rho }_{E}\), \({\rho }_{E}={{{{{{{{\rm{tr}}}}}}}}}_{A}({\rho }_{AE})\), where r is distributed uniformly and is completely unknown to Eve. \({{{{{{{{\mathcal{H}}}}}}}}}_{{{{{{{{\bf{R}}}}}}}}}\) is the Hilbert space of the memory storing r. However, as it is practically difficult to always guarantee this ideal situation, it is customary to relax this notion and say that r is ε-secure if
where \({\parallel} A{\parallel }_{1}={{{{{{{\rm{tr}}}}}}}}\left(\sqrt{A{A}^{{{{\dagger}}} }}\right)\) denotes the L1-norm of an operator A. Intuitively, this says that the actual state cannot be discriminated from the ideal state except with probability ε. This notion of security using parameter ε is often called the universally composable security31.
The conditional min-entropy \({H}_{\min }{({{{{{{{\bf{I}}}}}}}}| E)}_{{\rho }_{{{{{{{{\bf{I}}}}}}}}E}}\) of a sub-normalized state ρIE is defined to be the maximum real number λ, satisfying \({2}^{-\lambda }{{\mathbb{I}}}_{{{{{{{{\bf{I}}}}}}}}}\otimes {\sigma }_{E}\ge {\rho }_{{{{{{{{\bf{I}}}}}}}}E}\) for a normalized state σE34,37. We abbreviate \({H}_{\min }{({{{{{{{\bf{I}}}}}}}}| E)}_{{\rho }_{{{{{{{{\bf{I}}}}}}}}E}}\) as \({H}_{\min }({{{{{{{\bf{I}}}}}}}}| E)\), whenever the subscript ρIE is obvious from the context. The smooth conditional min-entropy \({H}_{\min }^{\delta }{({{{{{{{\bf{I}}}}}}}}| E)}_{{\rho }_{{{{{{{{\bf{I}}}}}}}}E}}\) is the maximum value of \({H}_{\min }{({\bar{\rho }}_{AE}| E)}_{{\bar{\rho }}_{{{{{{{{\bf{I}}}}}}}}E}}\) of sub-normalized states \({\bar{\rho }}_{{{{{{{{\bf{I}}}}}}}}E}\) that are δ-close to ρIE in terms of the purified distance37.
If Alice performs randomness extraction using a universal2 function family \({{{{{{{\mathcal{F}}}}}}}}\)32, the security of its output r satisfies the following.
Lemma 1
(Leftover hashing lemma (LHL,34)) Suppose a random function fs is universal2; i.e., \({f}_{s}\in {{{{{{{\mathcal{F}}}}}}}}\) is chosen with a probability p(s) satisfying
Then, we have
By combining this lemma and Theorem 1, we obtain Corollary 1.
Detailed descriptions of Radioactive RNG and Virtual RNG 2
We here give a detailed mathematical description of Radioactive RNG and Virtual RNG 2. We will describe Virtual RNG 2 only, but the same description applies also to Radioactive RNG if one neglects output of virtual detector D↑ (cf. Table 1, 1st and 2nd rows).
Description of the procedures of Virtual RNG 2
We will denote by \(\bar{{{{{{{{\rm{D}}}}}}}}}\) the measurements setup consisting of detector pair D↑, D↓. We denote four output patterns of from \(\bar{{{{{{{{\rm{D}}}}}}}}}\) in one time bin by \(w\in {{{{{{{\mathcal{W}}}}}}}}\), where \({{{{{{{\mathcal{W}}}}}}}}:= \{\uparrow ,\downarrow ,{{{{{{{\rm{none}}}}}}}},{{{{{{{\rm{double}}}}}}}}\}\) (Table 1, 1st row). For the convenience of the security proof, we classify w by how many of the detector pair D↑, D↓ go off in the time bin, using symbols \(\tilde{{{{{{{{\mathcal{W}}}}}}}}}:= \{\,{{\mbox{none}}}\,,{{{{{{{\rm{single}}}}}}}},{{{{{{{\rm{double}}}}}}}}\}\), where ‘single’ event means w = ↑ or ↓. A function h can be defined corresponding to this classification (Table 1, third row).
We continue to describe radiated particles by the Hilbert space \({{{{{{{{\mathcal{H}}}}}}}}}_{A}\). In addition, we introduce \({{{{{{{{\mathcal{H}}}}}}}}}_{B}\) to describe the radiation source.
We describe the quantum process (measurement and time evolution) occurring inside the RNG device, during the beginnings of adjacent time bins, by a completely positive map \({M}_{AB}^{w}:{{{{{{{{\mathcal{H}}}}}}}}}_{A}\otimes {{{{{{{{\mathcal{H}}}}}}}}}_{B}\to {{{{{{{{\mathcal{H}}}}}}}}}_{A}\otimes {{{{{{{{\mathcal{H}}}}}}}}}_{B}\). That is, if Alice measures the state σABE(jΔt) at the beginning of time bin j + 1 and obtains output w, the state at the beginning of next time bin is \({\sigma }_{ABE}^{w}((j+1){{\Delta }}t)={M}_{AB}^{w}({\sigma }_{ABE}(j{{\Delta }}t))\).
(We here extend the convention for operators, introduced above Eq. (1), to maps of states, and omit the identity operation included in a tensor product; hence e.g., \({M}_{AB}^{w}={M}_{AB}^{w}\otimes {{{{{{{{\rm{id}}}}}}}}}_{E}\) with idE being the identity operation in \({{{{{{{{\mathcal{H}}}}}}}}}_{E}\).)
Hence if Alice started Virtual RNG 2 with the state ρABE(0), and measured w1, …, wj in time bins 1, …, j, the (sub-normalized) state at the beginning of time bin j + 1 takes the form
When Virtual RNG 2 is finished, the joint state of the memory that stores the entire measurement result w = (w1, …, wN) and of Eve takes the form
Parity invariance of the measurement result w i
In this setting, we can argue that \({\rho }_{E}^{{{{{{{{\bf{w}}}}}}}}}\) are invariant under flips of arrows ↑ and ↓ included in wi, by essentially the same argument as in Eq. (6).
To see this, first note that condition (A) asserts that
Also note that the following relation holds for maps \({M}_{AB}^{\uparrow }\) and \({M}_{AB}^{\downarrow }\),
where \({\tilde{P}}_{A}({\rho }_{A}):= {P}_{A}{\rho }_{ABE}{P}_{A}\). Eq. (16) holds for the following two reasons: (i) Due to the construction of \(\bar{{{{{{{{\rm{D}}}}}}}}}\), obtaining the measurement result ↓ is equivalent to first applying the parity transform and then obtaining ↑. (ii) Due to condition (C), the effect caused on radiations by the measurement of a time bin i (which may depend on results wi = ↓, ↑) is washed away before the measurement of the next time bin i + 1 starts.
From relations (15), (16), we see that the (sub-normalized) state at the beginning of time bin j + 1 satisfies
Further, combining this with Eq. (12), we see that \({\rho }_{E}^{{{{{{{{\bf{w}}}}}}}}}\) are invariant under flips of arrows ↑ and ↓ included in wi. Or in terms of classification \(\tilde{{{{{{{{\mathcal{W}}}}}}}}}=\{\,{{\mbox{none}}}\,,{{{{{{{\rm{single}}}}}}}},{{{{{{{\rm{double}}}}}}}}\}\)
where h(w) ≔ (h(w1), …, h(wN)). That is, \({\rho }_{E}^{{{{{{{{\bf{w}}}}}}}}}\), \({\rho }_{E}^{{{{{{{{\bf{w}}}}}}}}^{\prime} }\) are equal, if it holds for all time bin i that the number of detectors that went off in time bin i is equal, \(h({w}_{i})=h(w^{\prime} )\in \tilde{{{{{{{{\mathcal{W}}}}}}}}}\).
Supplement to the proof of Theorem 1
We argued that the right hand side of (8) is lower bounded by the number of single detection events. The argument made there was in fact rather intuitive and not sufficiently rigorous. Below we give a rigorous proof.
Under these settings, we consider the following virtual RNG. This corresponds to the situation where Alice intentionally reveals h(w) to Eve.
Virtual RNG 3: After executing Virtual RNG 2, Alice tells Eve h(w).
The min-entropy corresponding to this case lower bounds the right hand side of (8), since Eve’s ambiguity never increases on receiving an extra information h(w).
After Virtual RNG 3, Alice and Eve both know the classical random variable \(\tilde{{{{{{{{\bf{w}}}}}}}}}=h({{{{{{{\bf{w}}}}}}}})\), so the overall state becomes a classical ensemble of those labeled by \(\tilde{{{{{{{{\bf{w}}}}}}}}}\). Thus it suffices to analyze each \(\tilde{{{{{{{{\bf{w}}}}}}}}}\) separately. We rephrase this rigorously34 (See Lemma 3.1.8) as
where the minimum is evaluated for all values of \(\tilde{{{{{{{{\bf{w}}}}}}}}}\) possible, i.e., all \(\tilde{{{{{{{{\bf{w}}}}}}}}}\in {\tilde{{{{{{{{\mathcal{W}}}}}}}}}}^{N}\) satisfying \(\Pr (h({{{{{{{\bf{w}}}}}}}})=\tilde{{{{{{{{\bf{w}}}}}}}}}\,| \,{\rho }_{{{{{{{{\bf{W}}}}}}}}E}) \, > \, 0\).
\({H}_{\min }(g({{{{{{{\bf{W}}}}}}}})| h({{{{{{{\bf{W}}}}}}}})=\tilde{{{{{{{{\bf{w}}}}}}}}},E)\) on the right hand side of (20) measures the fraction of g(w) unknown to Eve, under the restriction that w takes values satisfying \(h({{{{{{{\bf{w}}}}}}}})=\tilde{{{{{{{{\bf{w}}}}}}}}}\). As can easily be seen by definition of functions g and h in Table 1, under this restriction, function g becomes one-to-one, and thus the min-entropies of g(w) and w are equal,
The right hand side of (21) can be evaluated using the parity symmetry (18). Let \(s(\tilde{{{{{{{{\bf{w}}}}}}}}})\) be the number of ‘single’ symbols included in \(\tilde{{{{{{{{\bf{w}}}}}}}}}\) (i.e., the number of single events), then there are \({2}^{s(\tilde{{{{{{{{\bf{w}}}}}}}}})}\) values of w satisfying \(h({{{{{{{\bf{w}}}}}}}})=\tilde{{{{{{{{\bf{w}}}}}}}}}\). Because of (18), Eve’s (sub-normalized) states \({\rho }_{E}^{\tilde{{{{{{{{\bf{w}}}}}}}}}}\) are equal for all these values of \(\tilde{{{{{{{{\bf{w}}}}}}}}}\), and thus the corresponding entropy takes the value
Finally, combining Eqs. (19)–(22) together, we obtain
Data availability
The authors declare that the data supporting the findings of this study are available within the paper.
References
Shannon, C. E. Communication theory of secrecy systems. Bell Syst. Tech. J. 28, 656–715 (1949).
Acín, A. & Masanes, L. Certified randomness in quantum physics. Nature 540, 213–219 (2016).
Ma, X., Yuan, X., Cao, Z., Qi, B. & Zhang, Z. Quantum random number generation. npj Quantum Inf. 2, 16021 (2016).
Herrero-Collantes, M. & Garcia-Escartin, J. C. Quantum random number generators. Rev. Modern Phys. 89, 015004 (2017).
Bierhorst, P. et al. Experimentally generated randomness certified by the impossibility of superluminal signals. Nature 556, 223–226 (2018).
Stefanov, A., Gisin, N., Guinnard, O., Guinnard, L. & Zbinden, H. Optical quantum random number generator. J. Modern Opt. 47, 595–598 (2000).
Rarity, J. G., Owens, P. C. & Tapster, P. R. Quantum random-number generation and key sharing. J. Modern Opt. 41, 2435–2444 (1994).
Dynes, J. F., Yuan, Z. L., Sharpe, A. W. & Shields, A. J. A high speed, postprocessing free, quantum random number generator. Appl. Phys. Lett. 93, 031109 (2008).
Ma, H.-Q., Xie, Y. & Wu, L.-A. Random number generation based on the time of arrival of single photons. Appl. Opt. 44, 7760 (2005).
Nie, Y. Q. et al. Practical and fast quantum random number generation based on photon arrival time relative to external reference. Appl. Phys. Lett. 104, 051110 (2014).
Wayne, M. A., Jeffrey, E. R., Akselrod, G. M. & Kwiat, P. G. Photon arrival time quantum random number generation. J. Modern Opt. 56, 516–522 (2009).
Wahl, M. et al. An ultrafast quantum random number generator with provably bounded output bias based on photon arrival time measurements. Appl. Phys. Lett. 98, 171105 (2011).
Yan, Q., Zhao, B., Liao, Q. & Zhou, N. Multi-bit quantum random number generation by measuring positions of arrival photons. Rev. Sci. Instru. 85, 103116 (2014).
Ren, M. et al. Quantum random-number generator based on a photon-number-resolving detector. Phys. Rev. A—Atomic Mol. Opt. Phys. 83, 023820 (2011).
Applegate, M. J. et al. Efficient and robust quantum random number generation by photon number detection. Appl. Phys. Lett. 107, 071106 (2015).
Wayne, M. A., Jeffrey, E. R., Akelsrod, G. M. & Kwiat, P. G. High-speed quantum random number generation. Conference on Quantum Electronics and Laser Science (QELS) - Technical Digest Series 18, 13029 (2008).
Ishida, M. & Ikeda, H. Random number generator. Ann. Inst. Stat. Math. 8, 119–126 (1956).
Manelis, B. Generating random noise. Electronics 8 Sep., 66–69 (1961).
Schmidt, H. Quantum-mechanical random-number generator. J. Appl. Phys. 41, 462–468 (1970).
Silverman, M. P., Strange, W., Silverman, C. R. & Lipscombe, T. C. Tests of alpha-, beta-, and electron capture decays for randomness. Phys. Lett. Section A: Gen. Atomic Solid State Phys. 262, 265–273 (1999).
Walker, J. "HotBits: Genuine random numbers, generated by radioactive decay” (1996).
Alkassar, A., Nicolay, T. & Rohe, M. Obtaining true-random binary numbers from a weak radioactive source. In Lecture Notes in Computer Science, vol. 3481, 634-646 (Springer, Berlin, Heidelberg, 2005).
Lutz, G. Semiconductor radiation detectors (Springer- Verlag, Berlin/Heidelberg, 2007).
Knoll, G. F. Radiation detection and measurement (Wiley, New York, 2010).
Rochas, A. et al. First fully integrated 2-d array of single-photon detectors in standard CMOS technology. IEEE Photonics Tech. Lett. 15, 963–965 (2003).
Quantaglion Co. Ltd. QNT series.
Tsuyuzaki, N. Random pulse generation source, and semiconductor device, method and program for generating random number and/or probability using the source (2005).
EYL Inc. Quantum Entropy Chip-EYL.
Segre, E.Nuclei and particles : an introduction to nuclear and subnuclear physics (Reading, Mass. : W. A. Benjamin, 1977).
Stephens, F. The study of nuclear states observed in alpha decay. Pure Appl. Phys. 9, 170 (1960).
Ben-Or, M., Horodecki, M., Leung, D. W., Mayers, D. & Oppenheim, J. The universal composable security of quantum key distribution. In Lecture Notes in Computer Science, vol. 3378, 386-406 (Springer Verlag, 2005).
Carter, J. L. & Wegman, M. N. Universal classes of hash functions. J. Comput. Syst. Sci. 18, 143–154 (1979).
Evaluated Nuclear Structure Data File, http://www.nndc.bnl.gov/ensdf (2022).
Renner, R. Security of Quantum Key Distribution. Diss. eth no. 16242, ETH ZURICH (2005).
Hoeffding, W. Probability inequalities for sums of bounded random variables. J. Am. Stat. Assoc. 58, 13–30 (1963).
Zhou, H., Yuan, X. & Ma, X. Randomness generation based on spontaneous emissions of lasers. Phys. Rev. A 91, 062316 (2015).
Tomamichel, M.A Framework for non-asymptotic quantum information. Theory. Diss. eth no. 20213, ETH ZURICH (2012).
Acknowledgements
T.S. is supported in part by Cross-ministerial Strategic Innovation Promotion Program (SIP) (Council for Science, Technology and Innovation (CSTI)); CREST (Japan Science and Technology Agency) JPMJCR1671; JSPS KAKENHI Grant Number JP18K1 3469. T.S. also thanks Quantaglion Co. Ltd. for useful information and discussion about the actual implementation of the radioactive RNG.
Author information
Authors and Affiliations
Contributions
T.T., T.S, and I.T. contributed to the initial conception of the ideas, to the working out of details, and to the writing and editing of the manuscript.
Corresponding author
Ethics declarations
Competing interests
T.S. borrowed a radioactive RNG from Quantaglion Co. Ltd. All other authors declare no competing interests.
Peer review
Peer review information
Communications Physics thanks Xiongfeng Ma and the other, anonymous, reviewer(s) for their contribution to the peer review of this work. Peer reviewer reports are available.
Additional information
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Tsurumaru, T., Sasaki, T. & Tsutsui, I. Secure random number generation from parity symmetric radiations. Commun Phys 5, 147 (2022). https://doi.org/10.1038/s42005-022-00915-1
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s42005-022-00915-1
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.