Abstract
In quantum mechanics, a fundamental law prevents quantum communications to simultaneously achieve high rates and long distances. This limitation is well known for point-to-point protocols, where two parties are directly connected by a quantum channel, but not yet fully understood in protocols with quantum repeaters. Here we solve this problem bounding the ultimate rates for transmitting quantum information, entanglement and secret keys via quantum repeaters. We derive single-letter upper bounds for the end-to-end capacities achievable by the most general (adaptive) protocols of quantum and private communication, from a single repeater chain to an arbitrarily complex quantum network, where systems may be routed through single or multiple paths. We analytically establish these capacities under fundamental noise models, including bosonic loss which is the most important for optical communications. In this way, our results provide the ultimate benchmarks for testing the optimal performance of repeater-assisted quantum communications.
Similar content being viewed by others
Introduction
Today quantum technologies are being developed at a rapid pace1,2,3,4. In this scenario, quantum communications are very advanced, with the development and implementation of a number of point-to-point protocols of quantum key distribution (QKD)5, based on discrete variable (DV) systems6,7,8, such as qubits, or continuous variable (CV) systems, such as bosonic modes9,10. Recently, we have also witnessed the deployment of high-rate optical-based secure quantum networks11,12. These are advantageous not only for their multiple-user architecture but also because they may overcome the fundamental limitations that are associated with point-to-point protocols of quantum and private communication.
After a long series of studies that started back in 2009 with the introduction of the reverse coherent information of a bosonic channel13,14, ref. 15 finally showed that the maximum rate at which two remote parties can distribute quantum bits (qubits), entanglement bits (ebits), or secret bits over a lossy channel (e.g., an optical fiber) is equal to −log2(1 − η), where η is the channel’s transmissivity. This limit is the Pirandola–Laurenza–Ottaviani–Banchi (PLOB) bound15 and cannot be surpassed even by the most powerful strategies that exploit arbitrary local operations (LOs) assisted by two-way classical communication (CC), also known as adaptive LOCCs16.
To beat the PLOB bound, we need to insert a quantum repeater17 in the communication line. In information theory18,19,20,21, a repeater or relay is any middle node helping the communication between two end-parties. This definition is extended to quantum information theory, where quantum repeaters are middle nodes equipped with both classical and quantum operations, and may be arranged to compose linear chains or more general networks. In general, they do not need to have quantum memories (e.g., see ref. 22) even though these are generally required for guaranteeing an optimal performance.
In all the ideal repeater-assisted scenarios, where we can beat the PLOB bound, it is fundamental to determine the maximum rates that are achievable by two end-users, i.e., to determine their end-to-end capacities for transmitting qubits, distributing ebits, and generating secret keys. Finding these capacities not only is important to establish the boundaries of quantum network communications but also to benchmark practical implementations, so as to check how far prototypes of quantum repeaters are from the ultimate theoretical performance.
Here we address this fundamental problem. By combining methods from quantum information theory6,7,8,9,10 and classical networks18,19,20,21, we derive tight single-letter upper bounds for the end-to-end quantum and private capacities of repeater chains and, more generally, quantum networks connected by arbitrary quantum channels (these channels and the dimension of the quantum systems they transmit may generally vary across the network). More importantly, we establish exact formulas for these capacities under fundamental noise models for both DV and CV systems, including dephasing, erasure, quantum-limited amplification, and bosonic loss which is the most important for quantum optical communications. Depending on the routing in the quantum network (single- or multi-path), optimal strategies are found by solving the widest path23,24,25 or the maximum flow problem26,27,28,29 suitably extended to the quantum communication setting.
Our results and analytical formulas allow one to assess the rate performance of quantum repeaters and quantum communication networks with respect to the ultimate limits imposed by the laws of quantum mechanics.
Results
Ultimate limits of repeater chains
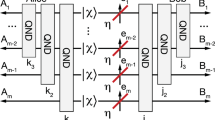
Consider Alice a and Bob b at the two ends of a linear chain of N quantum repeaters, labeled by r1, …, rN. Each point has a local register of quantum systems which may be augmented with incoming systems or depleted by outgoing ones. As also depicted in Fig. 1, the chain is connected by N + 1 quantum channels \(\{ {\cal{E}}_i\} = \{ {\cal{E}}_0, \ldots ,{\cal{E}}_i, \ldots ,{\cal{E}}_N\}\) through which systems are sequentially transmitted. This means that Alice transmits a system to repeater r1, which then relays the system to repeater r2, and so on, until Bob is reached.
Note that, in general, we may also have opposite directions for some of the quantum channels, so that they transmit systems towards Alice; e.g., we may have a middle relay receiving systems from both Alice and Bob. For this reason, we generally consider the “exchange” of a quantum system between two points by either forward or backward transmission. Under the assistance of two-way CCs, the optimal transmission of quantum information is related to the optimal distribution of entanglement followed by teleportation, so that it does not depend on the physical direction of the quantum channel but rather on the direction of the teleportation protocol.
In a single end-to-end transmission or use of the chain, all the channels are used exactly once. Assume that the end-points aim to share target bits, which may be ebits or private bits30,31. The most general quantum distribution protocol \({\cal{P}}_{{\mathrm{chain}}}\) involves transmissions which are interleaved by adaptive LOCCs among all parties, i.e., LOs assisted by two-way CCs among end-points and repeaters. In other words, before and after each transmission between two nodes, there is a session of LOCCs where all the nodes update and optimize their registers.
After n adaptive uses of the chain, the end-points share an output state \(\rho _{{\mathbf{ab}}}^n\) with nRn target bits. By optimizing the asymptotic rate limnRn over all protocols \({\cal{P}}_{{\mathrm{chain}}}\), we define the generic two-way capacity of the chain \({\cal{C}}(\{ {\cal{E}}_i\} )\). If the target are ebits, the repeater-assisted capacity \({\cal{C}}\) is an entanglement-distribution capacity D2. The latter coincides with a quantum capacity Q2, because distributing an ebit is equivalent to transmitting a qubit if we assume two-way CCs. If the target are private bits, \({\cal{C}}\) is a secret-key capacity K ≥ D2 (with the inequality holding because ebits are specific private bits). Exact definitions and more details are given in Supplementary Note 1.
To state our upper bound for \({\cal{C}}(\{ {\cal{E}}_i\} )\), we introduce the notion of channel simulation, as generally formulated by ref. 15 (see also refs. 32,33,34,35,36,37 for variants). Recall that any quantum channel \({\cal{E}}\) is simulable by applying a trace-preserving LOCC \({\cal{T}}\) to the input state ρ together with some bipartite resource state σ, so that \({\cal{E}}(\rho ) = {\cal{T}}(\rho \otimes \sigma )\). The pair \(({\cal{T}},\sigma )\) represents a possible “LOCC simulation” of the channel. In particular, for channels that suitably commute with the random unitaries of teleportation4, called “teleportation-covariant” channels15, one finds that \({\cal{T}}\) is teleportation and σ is their Choi matrix \(\sigma _{\cal{E}}: = {\cal{I}} \otimes {\cal{E}}(\Phi )\), where Φ is a maximally entangled state. The latter is also known as “teleportation simulation”.
For bosonic channels, the Choi matrices are energy-unbounded, so that simulations need to be formulated asymptotically. In general, an asymptotic state σ is defined as the limit of a sequence of physical states σμ, i.e., \(\sigma : = \mathop {\mathrm{{lim}}}\nolimits_\mu \sigma ^\mu\). The simulation of a channel \({\cal{E}}\) over an asymptotic state takes the form \(\left\Vert {{\cal{E}}(\rho ) - {\cal{T}}(\rho \otimes \sigma ^\mu )} \right\Vert_1\mathop { \to }\limits^\mu 0\) where the LOCC \({\cal{T}}\) may also depend on μ in the general case15. Similarly, any relevant functional on the asymptotic state needs to be computed over the defining sequence σμ before taking the limit for large μ. These technicalities are fully accounted in the Methods section.
The other notion to introduce is that of entanglement cut between Alice and Bob. In the setting of a linear chain, a cut “i” disconnects channel \({\cal{E}}_i\) between repeaters ri and ri+1. Such channel can be replaced by a simulation with some resource state σi. After calculations (see Methods), this allows us to write
where ER(·) is the relative entropy of entanglement (REE). Recall that the REE is defined as38,39,40
where SEP represents the ensemble of separable bipartite states and \(S(\sigma ||\gamma ): = {\mathrm{Tr}}\left[ {\sigma (\mathrm{log}_2\sigma - \mathrm{log}_2\gamma )} \right]\) is the relative entropy. In general, for any asymptotic state defined by the limit \(\sigma : = \mathrm{lim}_\mu \sigma ^\mu\), we may extend the previous definition and consider
where γμ is a converging sequence of separable states15.
By minimizing Eq. (1) over all cuts, we may write
which establishes the ultimate limit for entanglement and key distribution through a repeater chain. For a chain of teleportation-covariant channels, we may use their teleportation simulation over Choi matrices and write
Note that the family of teleportation-covariant channels is large, including Pauli channels (at any dimension)7 and bosonic Gaussian channels9. Within such a family, there are channels \({\cal{E}}\) whose generic two-way capacity \({\cal{C}} = Q_2\), D2 or K satisfies
where \(D_1(\sigma _{\cal{E}})\) is the one-way distillable entanglement of the Choi matrix (defined as an asymptotic functional in the bosonic case15). These are called “distillable channels” and include bosonic lossy channels, quantum-limited amplifiers, dephasing and erasure channels15.
For a chain of distillable channels, we therefore exactly establish the repeater-assisted capacity as
In fact the upper bound (≤) follows from Eqs. (5) and (6). The lower bound (≥) relies on the fact that an achievable rate for end-to-end entanglement distribution consists in: (i) each pair, ri and \({\mathbf{r}}_{i + 1}\), exchanging \(D_1(\sigma _{{\cal{E}}_i})\) ebits over \({\cal{E}}_i\); and (ii) performing entanglement swapping on the distilled ebits. In this way, at least \({\mathrm{min}}_{i} {D}_{1}(\sigma_{{\cal{E}}_i})\) ebits are shared between Alice and Bob.
Lossy chains
Let us specify Eq. (7) to an important case. For a chain of quantum repeaters connected by lossy channels with transmissivities \(\{ \eta _i\}\), we find the capacity
Thus, the minimum transmissivity within the lossy chain establishes the ultimate rate for repeater-assisted quantum/private communication between the end-users. For instance, consider an optical fiber with transmissivity η and insert N repeaters so that the fiber is split into N + 1 lossy channels. The optimal configuration corresponds to equidistant repeaters, so that \(\eta _{{\mathrm{min}}} = \root {{N + 1}} \of {\eta }\) and the maximum capacity of the lossy chain is
This capacity is plotted in Fig. 2 and compared with the point-to-point PLOB bound \({\cal{C}}(\eta ) = {\cal{C}}_{{\mathrm{loss}}}(\eta ,0)\). A simple calculation shows that if we want to guarantee a performance of 1 target bit per use of the chain, then we may tolerate at most 3 dB of loss in each individual link. This “3dB rule” imposes a maximum repeater-repeater distance of 15 km in standard optical fiber (at 0.2dB/km).
Optimal performance of lossy chains. Capacity (target bits per chain use) versus total loss of the line (decibels, dB) for \(N = 1,2,10\) and 100 equidistant repeaters. Compare the repeater-assisted capacities (solid curves) with the point-to-point repeater-less bound15 (dashed curve)
Quantum networks under single-path routing
A quantum communication network can be represented by an undirected finite graph18 \({\cal{N}} = (P,E)\), where P is the set of points and E the set of all edges. Each point p has a local register of quantum systems. Two points pi and pj are connected by an edge \(({\mathbf{p}}_i,{\mathbf{p}}_j) \in E\) if there is a quantum channel \({\cal{E}}_{ij}: = {\cal{E}}_{{\mathbf{p}}_i{\mathbf{p}}_j}\) between them. By simulating each channel \({\cal{E}}_{ij}\) with a resource state \(\sigma _{ij}\), we simulate the entire network \({\cal{N}}\) with a set of resource states \(\sigma ({\cal{N}}) = \{ \sigma _{ij}\}\). A route is an undirected path \({\mathbf{a}} - {\mathbf{p}}_i - \cdots - {\mathbf{p}}_j - {\mathbf{b}}\) between the two end-points, Alice a and Bob b. These are connected by an ensemble of possible routes \(\Omega = \{ 1, \ldots ,\omega , \ldots \}\), with the generic route ω involving the transmission through a sequence of channels \(\{ {\cal{E}}_0^\omega , \ldots ,{\cal{E}}_k^\omega \ldots \}\). Finally, an entanglement cut C is a bipartition (A, B) of P such that \({\mathbf{a}} \in {\mathbf{A}}\) and \({\mathbf{b}} \in {\mathbf{B}}\). Any such cut C identifies a super Alice A and a super Bob B, which are connected by the cut-set \(\tilde C = \{ ({\mathbf{x}},{\mathbf{y}}) \in E:{\mathbf{x}} \in {\mathbf{A}},{\mathbf{y}} \in {\mathbf{B}}\}\). See the example in Fig. 3 and more details in Supplementary Notes 2 and 3.
Diamond quantum network \({\cal{N}}^\diamondsuit\). a This is a quantum network of four points \(P = \{ {\mathbf{p}}_0,{\mathbf{p}}_1,{\mathbf{p}}_2,{\mathbf{p}}_3\}\), with end-points \({\mathbf{p}}_0 = {\mathbf{a}}\) (Alice) and \({\mathbf{p}}_3 = {\mathbf{b}}\) (Bob). Two points pi and pj are connected by an edge \(({\mathbf{p}}_i,{\mathbf{p}}_j)\) if there is an associated quantum channel \({\cal{E}}_{ij}\). This channel has a corresponding resource state \(\sigma _{ij}\) in a simulation of the network. There are four (simple) routes: \(1:{\mathbf{a}} - {\mathbf{p}}_1 - {\mathbf{b}}\), \(2:{\mathbf{a}} - {\mathbf{p}}_2 - {\mathbf{b}}\), \(3:{\mathbf{a}} - {\mathbf{p}}_2 - {\mathbf{p}}_1 - {\mathbf{b}}\), and \(4:{\mathbf{a}} - {\mathbf{p}}_1 - {\mathbf{p}}_2 - {\mathbf{b}}\). As an example, route 4 involves the transmission through the sequence of quantum channels \(\{ {\cal{E}}_k^4\}\) which is defined by \({\cal{E}}_0^4: = {\cal{E}}_{01}\), \({\cal{E}}_1^4: = {\cal{E}}_{12}\) and \({\cal{E}}_2^4: = {\cal{E}}_{23}\). b We explicitly show route ω = 4. In a sequential protocol, each use of the network corresponds to using a single route ω between the two end-points, with some probability \(p_\omega\). c We show an entanglement cut C of the network, with super Alice A and super Bob B made by the points in the two clouds. These are connected by the cut-set \(\tilde C\) composed by the dotted edges
Let us remark that the quantum network is here described by an undirected graph where the physical direction of the quantum channels \({\cal{E}}_{ij}\) can be forward (pi → pj) or backward (pj → pi). As said before for the repeater chains, this degree of freedom relies on the fact that we consider assistance by two-way CC, so that the optimal transmission of qubits can always be reduced to the distillation of ebits followed by teleportation. The logical flow of quantum information is therefore fully determined by the LOs of the points, not by the physical direction of the quantum channel which is used to exchange a quantum system along an edge of the network. This study of an undirected quantum network under two-way CC clearly departs from other investigations41,42,43.
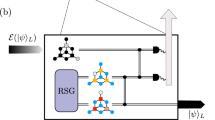
In a sequential protocol \({\cal{P}}_{{\mathrm{seq}}}\), the network is initialized by a preliminary network LOCC, where all the points communicate with each other via unlimited two-way CCs and perform adaptive LOs on their local quantum systems. With some probability, Alice exchanges a quantum system with repeater pi, followed by a second network LOCC; then repeater pi exchanges a system with repeater pj, followed by a third network LOCC and so on, until Bob is reached through some route in a complete sequential use of the network (see Fig. 4). The routing is itself adaptive in the general case, with each node updating its routing table (probability distribution) on the basis of the feedback received by the other nodes. For large n uses of the network, there is a probability distribution associated with the ensemble Ω, with the generic route ω being used \(np_\omega\) times. Alice and Bob’s output state \(\rho _{{\mathbf{ab}}}^n\) will approximate a target state with \(nR_n\) bits. By optimizing over \({\cal{P}}_{{\mathrm{seq}}}\) and taking the limit of large n, we define the sequential or single-path capacity of the network \({\cal{C}}({\cal{N}})\), whose nature depends on the target bits.
Network protocols of quantum and private communication. a In a sequential protocol, systems are routed through a single path probabilistically chosen by the points. Here it is \({\mathbf{a}} - {\mathbf{p}}_1 - {\mathbf{p}}_2 - {\mathbf{b}}\). Each transmission occurs between two adaptive LOCCs, where all points of the network perform LOs assisted by two-way CC. b In a flooding protocol, systems are simultaneously routed from Alice to Bob through a sequence of multipoint communications in such a way that each edge of the network is used exactly once in an end-to-end transmission. Here we show a possible sequence \({\mathbf{a}} \to \{ {\mathbf{p}}_1,{\mathbf{p}}_2\}\), \({\mathbf{p}}_2 \to \{ {\mathbf{p}}_1,{\mathbf{b}}\}\), \({\mathbf{p}}_1 \to \{ {\mathbf{b}}\}\). Each multipoint communication occurs between two adaptive LOCCs
To state our upper bound, let us first introduce the flow of REE through a cut. Given an entanglement cut C of the network, consider its cut-set \(\tilde C\). For each edge (x, y) in \(\tilde C\), we have a channel \({\cal{E}}_{{\mathbf{xy}}}\) and a corresponding resource state \(\sigma _{{\mathbf{xy}}}\) associated with a simulation. Then we define the single-edge flow of REE across cut C as
The minimization of this quantity over all entanglement cuts provides our upper bound for the single-path capacity of the network, i.e.,
which is the network generalization of Eq. (4). For proof see Methods and further details in Supplementary Note 4.
In Eq. (11), the quantity \(E_{\mathrm{R}}(C)\) represents the maximum entanglement (as quantified by the REE) “flowing” through a cut. Its minimization over all the cuts bounds the single-path capacity for quantum communication, entanglement distribution and key generation. For a network of teleportation-covariant channels, the resource state \(\sigma _{{\mathbf{xy}}}\) in Eq. (10) is the Choi matrix \(\sigma _{{\cal{E}}_{{\mathbf{xy}}}}\) of the channel \({\cal{E}}_{{\mathbf{xy}}}\). In particular, for a network of distillable channels, we may also set
for any edge (x, y). Therefore, we may refine the previous bound of Eq. (11) into \({\cal{C}}({\cal{N}}) \le \mathop {{\mathrm{min}}}\nolimits_C {\cal{C}}(C)\) where
is the maximum (single-edge) capacity of a cut.
Let us now derive a lower bound. First we prove that, for an arbitrary network, \(\mathop {\mathrm{min}}\nolimits_C {\cal{C}}(C) = \mathop {\mathrm{max}}\nolimits_\omega {\cal{C}}(\omega )\), where \({\cal{C}}(\omega ): = \mathop {{\mathrm{min}}}\nolimits_i {\cal{C}}({\cal{E}}_i^\omega )\) is the capacity of route ω (see Methods and Supplementary Note 4 for more details). Then, we observe that \({\cal{C}}(\omega )\) is an achievable rate. In fact, any two consecutive points on route ω may first communicate at the rate \({\cal{C}}({\cal{E}}_i^\omega )\); the distributed resources are then swapped to the end-users, e.g., via entanglement swapping or key composition at the minimum rate \(\mathop {\mathrm{min}}\nolimits_i {\cal{C}}({\cal{E}}_i^\omega )\). For a distillable network, this lower bound coincides with the upper bound, so that we exactly establish the single-path capacity as
Finding the optimal route \(\omega _ \ast\) corresponds to solving the widest path problem24 where the weights of the edges \(({\mathbf{x}},{\mathbf{y}})\) are the two-way capacities \({\cal{C}}({\cal{E}}_{{\mathbf{xy}}})\). Route \(\omega _ \ast\) can be found via modified Dijkstra’s shortest path algorithm25, working in time \(O(\left| E \right|\mathop {{\log}}\nolimits_2 \left| P \right|)\), where \(\left| E \right|\) is the number of edges and \(\left| P \right|\) is the number of points. Over route \(\omega _ \ast\) a capacity-achieving protocol is non adaptive, with point-to-point sessions of one-way entanglement distillation followed by entanglement swapping4. In a practical implementation, the number of distilled ebits can be computed using the methods from ref. 44. Also note that, because the swapping is on ebits, there is no violation of the Bellman’s optimality principle45.
An important example is an optical lossy network \({\cal{N}}_{{\mathrm{loss}}}\) where any route ω is composed of lossy channels with transmissivities \(\{ \eta _i^\omega \}\). Denote by \(\eta _\omega : = \mathop {\mathrm{min}}\nolimits_i \eta _i^\omega\) the end-to-end transmissivity of route ω. The single-path capacity is given by the route with maximum transmissivity
In particular, this is the ultimate rate at which the two end-points may generate secret bits per sequential use of the lossy network.
Quantum networks under multi-path routing
In a network we may consider a more powerful routing strategy, where systems are transmitted through a sequence of multipoint communications (interleaved by network LOCCs). In each of these communications, a number M of quantum systems are prepared in a generally multipartite state and simultaneously transmitted to M receiving nodes. For instance, as shown in the example of Fig. 4, Alice may simultaneously sends systems to repeaters p1 and p2, which is denoted by \({\mathbf{a}} \to \{ {\mathbf{p}}_1,{\mathbf{p}}_2\}\). Then, repeater p2 may communicate with repeater p1 and Bob b, i.e., \({\mathbf{p}}_2 \to \{ {\mathbf{p}}_1,{\mathbf{b}}\}\). Finally, repeater p1 may communicate with Bob, i.e., \({\mathbf{p}}_1 \to {\mathbf{b}}\). Note that each edge of the network is used exactly once during the end-to-end transmission, a strategy known as “flooding” in computer networks46. This is achieved by non-overlapping multipoint communications, where the receiving repeaters choose unused edges for the next transmissions. More generally, each multipoint communication is assumed to be a point-to-multipoint connection with a logical sender-to-receiver(s) orientation but where the quantum systems may be physically transmitted either forward or backward by the quantum channels.
Thus, in a general quantum flooding protocol \({\cal{P}}_{{\mathrm{flood}}}\), the network is initialized by a preliminary network LOCC. Then, Alice a exchanges quantum systems with all her neighbor repeaters \({\mathbf{a}} \to \{ {\mathbf{p}}_k\}\). This is followed by another network LOCC. Then, each receiving repeater exchanges systems with its neighbor repeaters through unused edges, and so on. Each multipoint communication is interleaved by network LOCCs and may distribute multi-partite entanglement. Eventually, Bob is reached as an end-point in the first parallel use of the network, which is completed when all Bob’s incoming edges have been used exactly once. In the limit of many uses n and optimizing over \({\cal{P}}_{{\mathrm{flood}}}\), we define the multi-path capacity of the network \({\cal{C}}^{\mathrm{m}}({\cal{N}})\).
As before, given an entanglement cut C, consider its cut-set \(\tilde C\). For each edge (x, y) in \(\tilde C\), there is a channel \({\cal{E}}_{{\mathbf{xy}}}\) with a corresponding resource state \(\sigma _{{\mathbf{xy}}}\). We define the multi-edge flow of REE through C as
which is the total entanglement (REE) flowing through a cut. The minimization of this quantity over all entanglement cuts provides our upper bound for the multi-path capacity of the network, i.e.,
which is the multi-path generalization of Eq. (11). For proof see Methods and further details in Supplementary Note 5. In a teleportation-covariant network we may simply use the Choi matrices \(\sigma _{{\mathbf{xy}}} = \sigma _{{\cal{E}}_{{\mathbf{xy}}}}\). Then, for a distillable network, we may use \(E_{\mathrm{R}}(\sigma _{{\cal{E}}_{{\mathbf{xy}}}}) = {\cal{C}}({\cal{E}}_{{\mathbf{xy}}})\) from Eq. (12), and write the refined upper bound \({\cal{C}}^{\mathrm{m}}({\cal{N}}) \le \mathop {\mathrm{min}}\nolimits_C {\cal{C}}^{\mathrm{m}}(C)\), where
is the total (multi-edge) capacity of a cut.
To show that the upper bound is achievable for a distillable network, we need to determine the optimal flow of qubits from Alice to Bob. First of all, from the knowledge of the capacities \({\cal{C}}({\cal{E}}_{{\mathbf{xy}}})\), the parties solve a classical problem of maximum flow26,27,28,29 compatible with those capacities. By using Orlin’s algorithm47, the solution can be found in \(O(|P| \times |E|)\) time. This provides an optimal orientation for the network and the rates \(R_{{\mathbf{xy}}} \le {\cal{C}}({\cal{E}}_{{\mathbf{xy}}})\) to be used. Then, any pair of neighbor points, x and y, distill \(nR_{{\mathbf{xy}}}\) ebits via one-way CCs. Such ebits are used to teleport \(nR_{{\mathbf{xy}}}\) qubits from x to y according to the optimal orientation. In this way, a number nR of qubits are teleported from Alice to Bob, flowing as quantum information through the network. Using the max-flow min-cut theorem26,27,28,29,47,48,49,50,51,52,53, we have that the maximum flow is \(n{\cal{C}}^{\mathrm{m}}(C_{{\mathrm{min}}})\) where \(C_{{\mathrm{min}}}\) is the minimum cut, i.e., \({\cal{C}}^{\mathrm{m}}(C_{{\mathrm{min}}}) = \mathop {\mathrm{min}}\nolimits_C {\cal{C}}^{\mathrm{m}}(C)\). Thus, that for a distillable \({\cal{N}}\), we find the multi-path capacity
which is the multi-path version of Eq. (14). This is achievable by using a non adaptive protocol where the optimal routing is given by Orlin’s algorithm47.
As an example, consider again a lossy optical network \({\cal{N}}_{{\mathrm{loss}}}\) whose generic edge (x, y) has transmissivity \(\eta _{{\mathbf{xy}}}\). Given a cut C, consider its loss \(L_C: = \mathop {\prod}\nolimits_{({\mathbf{x}},{\mathbf{y}}) \in \tilde C} (1 - \eta _{{\mathbf{xy}}})\) and define the total loss of the network as the maximization \(L_{\cal{N}}: = \mathop {\mathrm{max}}\nolimits_C L_C\). We find that the multi-path capacity is just given by
It is interesting to make a direct comparison between the performance of single- and multi-path strategies. For this purpose, consider a diamond network \({\cal{N}}_{{\mathrm{loss}}}^\diamondsuit\) whose links are lossy channels with the same transmissivity η. In this case, we easily see that the multi-path capacity doubles the single-path capacity of the network, i.e.,
As expected the parallel use of the quantum network is more powerful than the sequential use.
Formulas for distillable chains and networks
Here we provide explicit analytical formulas for the end-to-end capacities of distillable chains and networks, beyond the lossy case already studied above. In fact, examples of distillable channels are not only lossy channels but also quantum-limited amplifiers, dephasing and erasure channels. First let us recall their explicit definitions and their two-way capacities.
A lossy (pure-loss) channel with transmissivity \(\eta \in (0,1)\) corresponds to a specific phase-insensitive Gaussian channel which transforms input quadratures \({\hat{\mathbf{x}}} = (\hat q,\hat p)^T\) as \({\hat{\mathbf{x}}} \to \sqrt \eta {\hat{\mathbf{x}}} + \sqrt {1 - \eta } {\hat{\mathbf{x}}}_E\), where E is the environment in the vacuum state9. Its two-way capacities (Q2, D2 and K) all coincide and are given by the PLOB bound15
A quantum-limited amplifier with an associated gain g > 1 is another phase-insensitive Gaussian channel but realizing the transformation \({\hat{\mathbf{x}}} \to \sqrt g {\hat{\mathbf{x}}} + \sqrt {g - 1} {\hat{\mathbf{x}}}_E\), where the environment E is in the vacuum state9. Its two-way capacities all coincide and are given by15
A dephasing channel with probability p ≤ 1/2 is a Pauli channel of the form \(\rho \to (1 - p)\rho + pZ\rho Z\), where Z is the phase-flip Pauli operator7. Its two-way capacities all coincide and are given by15
where \(H_2(p): = - p\mathop {{\log}}\nolimits_2 p - (1 - p)\mathop {{\log}}\nolimits_2 (1 - p)\) is the binary Shannon entropy. Finally, an erasure channel with probability \(p \le 1/2\) is a channel of the form \(\rho \to (1 - p)\rho + p\left| e \right\rangle \left\langle e \right|\), where \(\left| e \right\rangle \left\langle e \right|\) is an orthogonal state living in an extra dimension7. Its two-way capacities all coincide to15,54,55
Consider now a repeater chain \(\{ {\cal{E}}_i\}\), where the channels \({\cal{E}}_i\) are distillable of the same type (e.g., all quantum-limited amplifiers with different gains gi). The repeater-assisted capacity can be computed by combining Eq. (7) with one of the Eqs. (22)–(25). The final formulas are shown in the first column of Table 1. Then consider a quantum network \({\cal{N}} = (P,E)\), where each edge \(({\mathbf{x}},{\mathbf{y}}) \in E\) is described by a distillable channel \({\cal{E}}_{{\mathbf{xy}}}\) of the same type. For network \({\cal{N}}\), we may consider both a generic route \(\omega \in \Omega\), with sequence of channels \({\cal{E}}_i^\omega\), and a entanglement cut C, with corresponding cut-set \(\tilde C\). By combining Eqs. (14) and (19) with Eqs. (22)–(25), we derive explicit formulas for the single-path and multi-path capacities. These are given in the second and third columns of Table 1 where we set
Let us note that the formulas for dephasing and erasure channels can be easily extended to arbitrary dimension d. In fact, a qudit erasure channel is formally defined as before and its two-way capacities are15,54,55
Therefore, it is sufficient to multiply by \(\mathop {{\log}}\nolimits_2 d\) the corresponding expressions in Table 1. Then, in arbitrary dimension d, the dephasing channel is defined as
where pk is the probability of k phase flips and \(Z_d^k\left| i \right\rangle = {\mathrm{exp}}(2\pi ikd^{ - 1})\left| i \right\rangle\). Its generic two-way capacity is15
where \(H(\{ p_k\} ): = - \mathop {\sum}\nolimits_k p_k \log_2p_k\) is the Shannon entropy. Here the generalization is also simple. For instance, in a chain \(\{ {\cal{E}}_i\}\) of such d-dimensional dephasing channels, we would have N + 1 distributions \(\{ p_k^i\}\). We then compute the most entropic distribution, i.e., we take the maximization \(\mathop {\mathrm{max}}\nolimits_i H(\{ p_k^i\} )\). This is the bottleneck that determines the repeater capacity, so that
Generalization to dimension d is also immediate for the two network capacities \({\cal{C}}\) and \({\cal{C}}^{\mathrm{m}}\).
Discussion
This work establishes the ultimate boundaries of quantum and private communications assisted by repeaters, from the case of a single repeater chain to an arbitrary quantum network under single- or multi-path routing. Assuming arbitrary quantum channels between the nodes, we have shown that the end-to-end capacities are bounded by single-letter quantities based on the relative entropy of entanglement. These upper bounds are very general and also apply to chains and networks with untrusted nodes (i.e., run by an eavesdropper). Our theory is formulated in a general information-theoretic fashion which also applies to other entanglement measures, as discussed in our Methods section. The upper bounds are particularly important because they set the tightest upper limits on the performance of quantum repeaters in various network configurations. For instance, our benchmarks may be used to evaluate performances in relay-assisted QKD protocols such as MDI-QKD and variants56,57,58. Related literature and other developments59,60,61,62,63,64,65,66 are discussed in Supplementary Note 6.
For the lower bounds, we have employed classical composition methods of the capacities, either based on the widest path problem or the maximum flow, depending on the type of routing. In general, these simple and classical lower bounds do not coincide with the quantum upper bounds. However this is remarkably the case for distillable networks, for which the ultimate quantum communication performance can be completely reduced to the resolution of classical problems of network information theory. For these networks, widest path and maximum flow determine the quantum performance in terms of secret key generation, entanglement distribution and transmission of quantum information. In this way, we have been able to exactly establish the various end-to-end capacities of distillable chains and networks where the quantum systems are affected by the most fundamental noise models, including bosonic loss, which is the most important for optical and telecom communications, quantum-limited amplification, dephasing and erasure. In particular, our results also showed how the parallel or “broadband” use of a lossy quantum network via multi-path routing may greatly improve the end-to-end rates.
Methods
We present the main techniques that are needed to prove the results of our main text. These methods are here provided for a more general entanglement measure EM, and specifically apply to the REE. We consider a quantum network \({\cal{N}}\) under single- or multi-path routing. In particular, a chain of quantum repeaters can be treated as a single-route quantum network.
For the upper bounds, our methodology can be broken down in the following steps: (i) Derivation of a general weak converse upper bound in terms of a suitable entanglement measure (in particular, the REE); (ii) Simulation of the quantum network, so that quantum channels are replaced by resource states; (iii) Stretching of the network with respect to an entanglement cut, so that Alice and Bob’s shared state has a simple decomposition in terms of resource states; (iv) Data processing, subadditivity over tensor-products, and minimization over entanglement cuts. These steps provide entanglement-based upper bounds for the end-to-end capacities. For the lower bounds, we perform a suitable composition of the point-to-point capacities of the single-link channels by means of the widest path and the maximum flow, depending on the routing. For the case of distillable quantum networks (and chains), these lower bounds coincide with the upper bounds expressed in terms of the REE.
General (weak converse) upper bound
This closely follows the derivation of the corresponding point-to-point upper bound first given in the second 2015 arXiv version of ref. 15 and later reported as Theorem 2 in ref. 16. Consider an arbitrary end-to-end \((n,R_n^\varepsilon ,\varepsilon )\) network protocol \({\cal{P}}\) (single- or multi-path). This outputs a shared state \(\rho _{{\mathbf{ab}}}^n\) for Alice and Bob after n uses, which is ε-close to a target private state30,31 ϕn having \(nR_n^\varepsilon\) secret bits, i.e., in trace norm we have \(\left\| {\rho _{{\mathbf{ab}}}^n - \phi ^n} \right\|_1 \le \varepsilon\). Consider now an entanglement measure EM which is normalized on the target state, i.e.,
Assume that EM is continuous. This means that, for d-dimensional states ρ and σ that are close in trace norm as \(\left\Vert {\rho - \sigma } \right\Vert_1\, \le \varepsilon\), we may write
with the functions g and h converging to zero in ε. Assume also that EM is monotonic under trace-preserving LOCCs \(\bar \Lambda\), so that
a property which is also known as data processing inequality. Finally, assume that EM is subadditive over tensor products, i.e.,
All these properties are certainly satisfied by the REE ER and the squashed entanglement (SQ) ESQ, with specific expressions for g and h (e.g., these expressions are explicitly reported in Sec. VIII.A of ref. 16).
Using the first two properties (normalization and continuity), we may write
where d is the dimension of the target private state. We know that this dimension is at most exponential in the number of uses, i.e., \(\log_2d \le \alpha nR_n^\varepsilon\) for constant α (e.g., see ref. 15 or Lemma 1 in ref. 16). By replacing this dimensional bound in Eq. (39), taking the limit for large n and small ε (weak converse), we derive
Finally, we take the supremum over all protocols \({\cal{P}}\) so that we can write our general upper bound for the end-to-end secret key capacity (SKC) of the network
In particular, this is an upper bound to the single-path SKC \({\cal{K}}\) if \({\cal{P}}\) are single-path protocols, and to the multi-path SKC \({\cal{K}}^m\) if \({\cal{P}}\) are multi-path (flooding) protocols.
In the case of an infinite-dimensional state \(\rho _{{\mathbf{ab}}}^n\), the proof can be repeated by introducing a truncation trace-preserving LOCC T, so that \(\delta _{{\mathbf{ab}}}^n = {\boldsymbol{T}}(\rho _{{\mathbf{ab}}}^n)\) is a finite-dimensional state. The proof is repeated for \(\delta _{{\mathbf{ab}}}^n\) and finally we use the data processing \(E_{\mathrm{M}}(\delta _{{\mathbf{ab}}}^n) \le E_{\mathrm{M}}(\rho _{{\mathbf{ab}}}^n)\) to write the same upper bound as in Eq. (41). This follows the same steps of the proof given in the second 2015 arXiv version of ref. 15 and later reported as Theorem 2 in ref. 16. It is worth mentioning that Eq. (41) can equivalently be proven without using the exponential growth of the private state, i.e., using the steps of the third proof given in the Supplementary Note 3 of ref. 15.
Network simulation
Given a network \({\cal{N}} = (P,E)\) with generic point \({\mathbf{x}} \in P\) and edge \(({\mathbf{x}},{\mathbf{y}}) \in E\), replace the generic channel \({\cal{E}}_{{\mathbf{xy}}}\) with a simulation over a resource state σxy. This means to write \({\cal{E}}_{{\mathbf{xy}}}(\rho ) = {\cal{T}}_{{\mathbf{xy}}}(\rho \otimes \sigma _{{\mathbf{xy}}})\) for any input state ρ, by resorting to a suitable trace-preserving LOCC \({\cal{T}}_{{\mathbf{xy}}}\) (this is always possible for any quantum channel15). If we perform this operation for all the edges, we then define the simulation of the network \(\sigma ({\cal{N}}) = \{ \sigma _{{\mathbf{xy}}}\} _{({\mathbf{x}},{\mathbf{y}}) \in E}\) where each channel is replaced by a corresponding resource state. If the channels are bosonic, then the simulation is typically asymptotic of the type \({\cal{E}}_{{\mathbf{xy}}}(\rho ) = \mathop {{\lim}}\nolimits_\mu {\cal{E}}_{{\mathbf{xy}}}^\mu (\rho )\) where \({\cal{E}}_{{\mathbf{xy}}}^\mu (\rho ) = {\cal{T}}_{{\mathbf{xy}}}^\mu (\rho \otimes \sigma _{{\mathbf{xy}}}^\mu )\) for some sequence of simulating LOCCs \({\cal{T}}_{{\mathbf{xy}}}^\mu\) and sequence of resource states \(\sigma _{{\mathbf{xy}}}^\mu\).
Here the parameter μ is usually connected with the energy of the resource state. For instance, if \({\cal{E}}_{{\mathbf{xy}}}\) is a teleportation-covariant bosonic channel, then the resource state \(\sigma _{{\mathbf{xy}}}^\mu\) is its quasi-Choi matrix \(\sigma _{{\cal{E}}_{{\mathbf{xy}}}}^\mu : = {\cal{I}} \otimes {\cal{E}}_{{\mathbf{xy}}}({\mathrm{\Phi }}^\mu )\), with \(\Phi ^\mu\) being a two-mode squeezed vacuum state (TMSV) state9 whose parameter \(\mu = \bar n + 1/2\) is related to the mean number \(\bar n\) of thermal photons. Similarly, the simulating LOCC \({\cal{T}}_{{\mathbf{xy}}}^\mu\) is a Braunstein-Kimble protocol67,68 where the ideal Bell detection is replaced by the finite-energy projection onto α-displaced TMSV states \(D(\alpha ){\mathrm{\Phi }}^\mu D( - \alpha )\), with D being the phase-space displacement operator9.
Given an asymptotic simulation of a quantum channel, the associated simulation error is correctly quantified by employing the energy-constrained diamond distance15, which must go to zero in the limit, i.e.,
Recall that, for any two bosonic channels \({\cal{E}}\) and \({\cal{E}}'\), this quantity is defined as
where \(D_{\bar N}\) is the compact set of bipartite bosonic states with \(\bar N\) mean number of photons (see ref. 69 for a later and slightly different definition, where the constraint is only on the B part). Thus, in general, if the network has bosonic channels, we may write the asymptotic simulation \(\sigma ({\cal{N}}) = \mathop {{\lim}}\nolimits_\mu \sigma ^\mu ({\cal{N}})\) where \(\sigma ^\mu ({\cal{N}}): = \{ \sigma _{{\mathbf{xy}}}^\mu \} _{({\mathbf{x}},{\mathbf{y}}) \in E}\).
Stretching of the network
Once we simulate a network, the next step is its stretching, which is the complete adaptive-to-block simplification of its output state (for the exact details of this procedure see Supplementary Note 3). As a result of stretching, the n-use output state of the generic network protocol can be decomposed as
where \(\bar \Lambda\) represents a trace-preserving LOCC (which is local with respect to Alice and Bob). The LOCC \(\bar \Lambda\) includes all the adaptive LOCCs from the original protocol besides the simulating LOCCs. In Eq. (44), the parameter nxy is the number of uses of the edge (x, y), that we may always approximate to an integer for large n. We have nxy ≤ n for single-path routing, and nxy = n for flooding protocols in multi-path routing.
In the presence of bosonic channels and asymptotic simulations, we modify Eq. (44) into the approximate stretching
which tends to the actual output \(\rho _{{\mathbf{ab}}}^n\) for large μ. In fact, using a “peeling” technique15,16 which exploits the triangle inequality and the monotonicity of the trace distance under completely-positive trace-preserving maps, we may write the following bound
which goes to zero in μ for any finite input energy \(\bar N\), finite number of uses n of the protocol, and finite number of edges |E| in the network (the explicit steps of the proof can be found in Supplementary Note 3).
Stretching with respect to entanglement cuts
The decomposition of the output state can be greatly simplified by introducing cuts in the network. In particular, we may drastically reduce the number of resource states in its representation. Given a cut C of \({\cal{N}}\) with cut-set \(\tilde C\), we may in fact stretch the network with respect to that specific cut (see again Supplementary Note 3 for exact details of the procedure). In this way, we may write
where \(\bar \Lambda _{{\mathbf{ab}}}\) is a trace-preserving LOCC with respect to Alice and Bob (differently from before, this LOCC now depends on the cut C, but we prefer not to complicate the notation). Similarly, in the presence of bosonic channels, we may consider the approximate decomposition
which converges in trace distance to \(\rho _{{\mathbf{ab}}}^n(C)\) for large μ.
Data processing and subadditivity
Let us combine the stretching in Eq. (47) with two basic properties of the entanglement measure EM. The first property is the monotonicity of EM under trace-preserving LOCCs; the second property is the subadditivity of EM over tensor-product states. Using these properties, we can simplify the general upper bound of Eq. (41) into a simple and computable single-letter quantity. In fact, for any cut C of the network \({\cal{N}}\), we write
where \(\bar \Lambda _{{\mathbf{ab}}}\) has disappeared. Let us introduce the probability of using the generic edge (x, y)
so that we may write the limit
Using the latter in Eq. (41) allows us to write the following bound, for any cut C
In the case of bosonic channels and asymptotic simulations, we may use the triangle inequality
Then, we may repeat the derivations around Eqs. (39)–(41) for \(\rho _{{\mathbf{ab}}}^{n,\mu }\) instead of \(\rho _{{\mathbf{ab}}}^n\), where we also include the use of a suitable truncation of the states via a trace-preserving LOCC T (see also Sec. VIII.D of ref. 16 for a similar approach in the point-to-point case). This leads to the μ-dependent upper-bound
Because this is valid for any μ, we may conservatively take the inferior limit in μ and consider the upper bound
Finally, by introducing the stretching of Eq. (48) with respect to an entanglement cut C, and using the monotonicity and subadditivity of EM with respect to the decomposition of \(\rho _{{\mathbf{ab}}}^{n,\mu }(C)\), we may repeat the previous reasonings and write
which is a direct extension of the bound in Eq. (53).
We may formulate both Eqs. (53) and (57) in a compact way if we define the entanglement measure EM over an asymptotic state \(\sigma : = \mathop {{\lim}}\nolimits_\mu \sigma ^\mu\) as
It is clear that, for a physical (non-asymptotic) state, we have the trivial sequence σμ = σ for any μ, so that Eq. (58) provides the standard definition. In the specific case of REE, we may write
where γμ is a sequence of separable states that converges in trace norm; this means that there exists a separable state γ such that \(\left\| {\gamma ^\mu - \gamma } \right\|_1\mathop { \to }\limits^\mu 0\). Employing the extended definition of Eq. (58), we may write Eq. (53) for both non-asymptotic σxy and asymptotic states \(\sigma _{{\mathbf{xy}}}: = \mathop {{\lim}}\nolimits_\mu \sigma _{{\mathbf{xy}}}^\mu\).
Minimum entanglement cut and upper bounds
By minimizing Eq. (53) over all possible cuts of the network, we find the tightest upper bound, i.e.,
Let us now specify this formula for different types of routing. For single-path routing, we have \(p_{{\mathbf{xy}}} \le 1\), so that we may use
in Eq. (53). Therefore, we derive the following upper bound for the single-path SKC
where we introduce the single-edge flow of entanglement through the cut
In particular, we may specify this result to a single chain of N points and N + 1 channels \(\{ {\cal{E}}_i\}\) with resource states {σi}. This is a quantum network with a single route, so that the cuts can be labeled by i and the cut-sets are just composed of a single edge. Therefore, Eqs. (62) and (63) become
For multi-path routing, we have pxy = 1 (flooding), so that we may simplify
in Eq. (53). Therefore, we can write the following upper bound for the multi-path SKC
where we introduce the multi-edge flow of entanglement through the cut
In these results, the definition of EM(σxy) is implicitly meant to be extended to asymptotic states, according to Eq. (58). Then, note that the tightest values of the upper bounds are achieved by extending the minimization to all network simulations \(\sigma ({\cal{N}})\), i.e., by enforcing \(\min_C \to \min_{\sigma ({\cal{N}})}\min_C\) in Eqs. (62) and (66).
Specifying Eqs. (62), (64), and (66) to the REE, we get the single-letter upper bounds
which are Eqs. (4), (11) and (17) of the main text. The proofs of these upper bounds in terms of the REE can equivalently be done following the “converse part” derivations in Supplementary Note 1 (for chains), Supplementary Note 4 (for networks under single-path routing), and Supplementary Note 5 (for networks under multi-path routing). Differently from what presented in this Methods section, such proofs exploit the lower semi-continuity of the quantum relative entropy8 in order to deal with asymptotic simulations (e.g., for bosonic channels).
Lower bounds
To derive lower bounds we combine the known results on two-way assisted capacities15 with classical results in network information theory. Consider the generic two-way assisted capacity \({\cal{C}}_{{\mathbf{xy}}}\) of the channel \({\cal{E}}_{{\mathbf{xy}}}\) (in particular, this can be either D2 = Q2 or K). Then, using the cut property of the widest path (Supplementary Note 4), we derive the following achievable rate for the generic single-path capacity of the network \({\cal{N}}\)
For a chain \(\{ {\cal{E}}_i\}\), this simply specifies to
Using the classical max-flow min-cut theorem (Supplementary Note 5), we derive the following achievable rate for the generic multi-path capacity of \({\cal{N}}\)
Simplifications for teleportation-covariant and distillable networks
Recall that a quantum channel \({\cal{E}}\) is said to be teleportation-covariant15 when, for any teleportation unitary U (Weyl-Pauli operator in finite dimension or phase-space displacement in infinite dimension), we have
for some (generally-different) unitary transformation V. In this case the quantum channel can be simulated by applying teleportation over its Choi matrix \(\sigma _{\cal{E}}: = {\cal{I}} \otimes {\cal{E}}(\Phi )\), where Φ is a maximally-entangled state. Similarly, if the teleportation-covariant channel is bosonic, we can write an approximate simulation by teleporting over the quasi-Choi matrix \(\sigma _{\cal{E}}^\mu : = {\cal{I}} \otimes {\cal{E}}(\Phi ^\mu )\), where Φμ is a TMSV state. For a network of teleportation-covariant channels, we therefore use teleportation to simulate the network, so that the resource states in the upper bounds of Eqs. (68)–(70) are Choi matrices (physical or asymptotic). In other words, we write the sandwich relations
with the REE taking the form of Eq. (59) on an asymptotic Choi matrix \(\sigma _{{\cal{E}}_{{\mathbf{xy}}}}: = \mathop {{\lim}}\nolimits_\mu \sigma _{{\cal{E}}_{{\mathbf{xy}}}}^\mu\).
As a specific case, consider a quantum channel which is not only teleportation-covariant but also distillable, so that it satisfies15
where \(D_1(\sigma _{\cal{E}})\) is the one-way distillability of the Choi matrix \(\sigma _{\cal{E}}\) (with a suitable asymptotic expression for bosonic Choi matrices15). If a network (or a chain) is composed of these channels, then the relations in Eqs. (75)–(77) collapse and we fully determine the capacities
These capacities correspond to Eqs. (7), (14), and (19) of the main text. They are explicitly computed for chains and networks composed of lossy channels, quantum-limited amplifiers, dephasing and erasure channels in Table 1 of the main text.
Regularizations and other measures
It is worth noticing that some of the previous formulas can be re-formulated by using the regularization of the entanglement measure, i.e.,
In fact, let us go back to the first upper bound in Eq. (49), which implies
For a network under multi-path routing we have \(n_{{\mathbf{xy}}} = n\), so that we may write
By repeating previous steps, the latter equation implies the upper bound
which is generally tighter than the result in Eqs. (66) and (67). The same regularization can be written for a chain \(\{ {\cal{E}}_i\}\), which can also be seen as a single-route network satisfying the flooding condition \(n_{{\mathbf{xy}}} = n\). Therefore, starting from the condition of Eq. (83) with \(n_{{\mathbf{xy}}} = n\), we may write
which is generally tighter than the result in Eq. (64). These regularizations are important for the REE, but not for the squashed entanglement which is known to be additive over tensor-products, so that \(E_{{\mathrm{SQ}}}^\infty (\sigma ) = E_{{\mathrm{SQ}}}(\sigma )\).
Another extension is related to the use of the relative entropy distance with respect to partial-positive-transpose (PPT) states. This quantity can be denoted by RPPT and is defined by31
with an asymptotic extension similar to Eq. (59) but in terms of converging sequences of PPT states \(\gamma ^\mu\). The RPPT is tighter than the REE but does not provide an upper bound to the distillable key of a state, but rather to its distillable entanglement. This means that it has normalization \(E_{\mathrm{P}}\left( {\varphi ^n} \right) \ge nR_n\) on a target maximally-entangled state \(\varphi ^n\) with \(nR_n\) ebits.
The RPPT is known to be monotonic under the action of PPT operations (and therefore LOCCs); it is continuous and subadditive over tensor-product states. Therefore, we may repeat the derivation that leads to Eq. (41) but with respect to protocols \({\cal{P}}\) of entanglement distribution. This means that we can write
Using the decomposition of the output state \(\rho _{{\mathbf{ab}}}^n\) as in Eqs. (47) and (48), and repeating previous steps, we may finally write
for a chain \(\{ {\cal{E}}_i\}\) with resource states \(\{ \sigma _i\}\), and
for the single- and multi-path entanglement distribution capacities of a quantum network \({\cal{N}}\) with resource states \(\sigma ({\cal{N}}) = \{ \sigma _{{\mathbf{xy}}}\} _{({\mathbf{x}},{\mathbf{y}}) \in E}\).
Data availability
All data in this paper can be reproduced by using the methodology described.
Code availability
Code is available upon reasonable request to the author.
References
Kimble, H. J. The Quantum Internet. Nature 453, 1023–1030 (2008).
Van Meter, V. Quantum Networking (Wiley, 2014).
Pirandola, S. & Braunstein, S. L. Unite to build a quantum internet. Nature 532, 169–171 (2016).
Pirandola, S., Eisert, J., Weedbrook, C., Furusawa, A. & Braunstein, S. L. Advances in quantum teleportation. Nature Photon. 9, 641–652 (2015).
Gisin, N. et al. Quantum cryptography. Rev. Mod. Phys. 74, 145–195 (2002).
Watrous, J. The theory of quantum information. (Cambridge University Press, Cambridge, 2018).
Nielsen, M. A. & Chuang, I. L. Quantum computation and quantum information. (Cambridge University Press, Cambridge, 2002).
Holevo, A. Quantum systems, channels, information: A mathematical introduction. (De Gruyter, Berlin-Boston, 2012).
Weedbrook, C. et al. Gaussian quantum information. Rev. Mod. Phys. 84, 621–669 (2012).
Braunstein, S. L. & van Loock, P. Quantum information theory with continuous variables. Rev. Mod. Phys. 77, 513–577 (2005).
Fröhlich, B. et al. Quantum secured gigabit optical access networks. Sci. Rep. 5, 18121 (2015).
Bunandar, D. et al. Metropolitan quantum key distribution with silicon photonics. Phys. Rev. X 8, 021009 (2018).
García-Patrón, R., Pirandola, S., Lloyd, S. & Shapiro, J. H. Reverse coherent information. Phys. Rev. Lett. 102, 210501 (2009).
Pirandola, S., García-Patrón, R., Braunstein, S. L. & Lloyd, S. Direct and reverse secret-key capacities of a quantum channel. Phys. Rev. Lett. 102, 050503 (2009).
Pirandola, S., Laurenza, R., Ottaviani, C. & Banchi, L. Fundamental Limits of Repeaterless Quantum Communications. Nature Commun. 8, 15043 (2017).
Pirandola, S. et al. Theory of channel simulation and bounds for private communication. Quantum Sci. Technol. 3, 035009 (2018).
Briegel, H.-J., Dür, W., Cirac, J. I. & Zoller, P. Quantum repeaters: The role of imperfect local operations in quantum communication. Phys. Rev. Lett. 81, 5932–5935 (1998).
Slepian, P. Mathematical Foundations of Network Analysis. (Springer-Verlag, New York, 1968).
Cover, T. M. & Thomas, J. A. Elements of Information Theory. (Wiley, New Jersey, 2006).
El Gamal, A. & Kim, Y.-H. Network Information Theory (Cambridge Univ. Press 2011).
Schrijver, A. Combinatorial Optimization. (Springer-Verlag, Berlin, 2003).
Azuma, K., Tamaki, K. & Lo, H.-K. All-photonic quantum repeaters. Nat. Commun. 6, 6787 (2015).
Cormen, T., Leiserson, C. & Rivest, R. Introduction to Algorithms. (MIT Press, Cambridge, MA, 1990).
Pollack, M. The maximum capacity through a network. Oper. Res. 8, 733–736 (1960).
Medhi, D. & Ramasamy, K. Network Routing: Algorithms, Protocols, and Architectures. Second Edition (Morgan Kaufmann publishers, Cambridge MA, 2018).
Harris, T. E. & Ross, F. S. Fundamentals of a Method for Evaluating Rail Net Capacities. Research Memorandum, Rand Corporation (1955).
Ford, L. R. & Fulkerson, D. R. Maximal flow through a network. Canadian J. Math. 8, 399–404 (1956).
Elias, P., Feinstein, A. & Shannon, C. E. A note on the maximum flow through a network. IRE Trans. Inf. Theory 2, 117–119 (1956).
Ahuja, R. K., Magnanti, T. L. & Orlin, J. B. Network Flows: Theory, Algorithms and Applications (Prentice Hall 1993).
Horodecki, K., Horodecki, M., Horodecki, P. & Oppenheim, J. Secure key from bound entanglement. Phys. Rev. Lett. 94, 160502 (2005).
Horodecki, K., Horodecki, M., Horodecki, P. & Oppenheim, J. General paradigm for distilling classical key from quantum states. IEEE Trans. Inf. Theory 55, 1898–1929 (2009).
Cope, T. P. W., Hetzel, L., Banchi, L. & Pirandola, S. Simulation of non-Pauli Channels. Phys. Rev. A 96, 022323 (2017).
Laurenza, R. & Pirandola, S. General bounds for sender-receiver capacities in multipoint quantum communications. Phys. Rev. A 96, 032318 (2017).
Laurenza, R., Braunstein, S. L. & Pirandola, S. Finite-resource teleportation stretching for continuous-variable systems. Sci. Rep. 8, 15267 (2018).
Laurenza, R. et al. Tight finite-resource bounds for private communication over Gaussian channels. Preprint at https://arxiv.org/abs/1808.00608 (2018).
Pirandola, S., Laurenza, R. & Lupo, C. Fundamental limits to quantum channel discrimination. Preprint at https://arxiv.org/abs/1803.02834 (2018).
Pirandola, S., Laurenza, R. & Banchi, L. Conditional channel simulation. Ann. Phys. 400, 289–302 (2019).
Vedral, V. The role of relative entropy in quantum information theory. Rev. Mod. Phys. 74, 197–234 (2002).
Vedral, V., Plenio, M. B., Rippin, M. A. & Knight, P. L. Quantifying Entanglement. Phys. Rev. Lett. 78, 2275–2279 (1997).
Vedral, V. & Plenio, M. B. Entanglement measures and purification procedures. Phys. Rev. A. 57, 1619–1633 (1998).
Hayashi, M., Iwama, K., Nishimura, H., Raymond, R. & Yamashita, S. Quantum network coding. Lect. Notes. Comput. Sci. 4393, 610–621 (2007).
Hayashi, M., Owari, M., Kato, G. & Cai, N. Secrecy and robustness for active attacks in secure network coding and its application to network quantum key distribution. Preprint at https://arxiv.org/abs/1703.00723 (2017).
Song, S. & Hayashi, M. Secure quantum network code without classical communication. Proc. IEEE Inf. Theory Workshop 2018 (ITW 2018), Guangzhou, China, November 25–29, 2018, pp. 126–130.
Van Meter, R. et al. Path selection for quantum repeater. Networks. Netw. Sci. 3, 82–95 (2013).
Di Franco, C. & Ballester, D. Optimal path for a quantum teleportation protocol in entangled networks. Phys. Rew. A 85, 010303(R) (2012).
Tanenbaum, A. S. & Wetherall, D. J. Computer Networks (5th Edition, Pearson, 2010).
Orlin, J. B. Max flows in O(nm) time, or better. STOC’13 Proceedings of the Forty-fifth Annual ACM Symposium on Theory of Computing, pp. 765–774 (2013).
Edmonds, J. & Karp, R. M. Theoretical improvements in algorithmic efficiency for network flow problems. J. ACM 19, 248–264 (1972).
Dinic, E. A. Algorithm for solution of a problem of maximum flow in a network with power estimation. Soviet Math. Doklady 11, 1277–1280 (1970).
Alon, N. Generating pseudo-random permutations and maximum flow algorithms. Inf. Processing Lett. 35, 201–204 (1990).
Ahuja, R. K., Orlin, J. B. & Tarjan, R. E. Improved time bounds for the maximum flow problem. SIAM J. Comput. 18, 939–954 (1989).
Cheriyan, J., Hagerup, T. & Mehlhorn, K. Can a maximum flow be computed in O(nm) time? Proceedings of the 17th International Colloquium on Automata, Languages and Programming, pp. 235–248 (1990).
King, V., Rao, S. & Tarjan, R. A faster deterministic maximum flow algorithm. J. Algorithms 17, 447–474 (1994).
Goodenough, K., Elkouss, D. & Wehner, S. Assessing the performance of quantum repeaters for all phase-insensitive Gaussian bosonic channels. New J. Phys. 18, 063005 (2016).
Bennett, C. H., DiVincenzo, D. P. & Smolin, J. A. Capacities of quantum erasure channels. Phys. Rev. Lett. 78, 3217–3220 (1997).
Braunstein, S. L. & Pirandola, S. Side-channel-free quantum key distribution. Phys. Rev. Lett. 108, 130502 (2012).
Lo, H.-K., Curty, M. & Qi, B. Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2012).
Pirandola, S. et al. High-rate measurement-device-independent quantum cryptography. Nature Photon. 9, 397–402 (2015).
Azuma, K., Mizutani, A. & Lo, H.-K. Fundamental rate-loss trade-off for the quantum internet. Nat. Commun. 7, 13523 (2016).
Azuma, K. & Kato, G. Aggregating quantum repeaters for the quantum internet. Phys. Rev. A 96, 032332 (2017).
Rigovacca, L. et al. Versatile relative entropy bounds for quantum networks. New J. Phys. 20, 013033 (2018).
Cope, T. P. W., Goodenough, K. & Pirandola, S. Converse bounds for quantum and private communication over Holevo-Werner channels. J. Phys. A: Math. Theor. 51, 494001 (2018).
Pant, M. et al. Routing entanglement in the quantum internet. Preprint at https://arxiv.org/abs/1708.07142 (2017).
Bäuml, S., Azuma, K, Kato, G. & Elkouss, D. Linear programs for entanglement and key distribution in the quantum internet. Preprint at https://arxiv.org/abs/1809.03120 (2018).
Lucamarini, M., Yuan, Z. L., Dynes, J. F. & Shields, A. J. Overcoming the rate–distance limit of quantum key distribution without quantum repeaters. Nature 557, 400–403 (2018).
Ma, X., Zeng, P. & Zhou, H. Phase-matching quantum key distribution. Phys. Rev. X 8, 031043 (2018).
Braunstein, S. L. & Kimble, J. Teleportation of continuous quantum variables. Phys. Rev. Lett. 80, 869–872 (1998).
Pirandola, S., Laurenza, R. & Braunstein, S. L. Teleportation simulation of bosonic Gaussian channels: Strong and uniform convergence. Eur. Phys. J. D 72, 162 (2018).
Shirokov, M. E. Energy-constrained diamond norms and their use in quantum information theory. Prob. Inf.Transm. 54, 20–33 (2018).
Acknowledgements
This work has been supported by the EPSRC via the ‘UK Quantum Communications HUB’ (EP/M013472/1) and ‘qDATA’ (EP/L011298/1), and by the European Union via Continuous Variable Quantum Communications (CiViQ, Project ID: 820466). The author would like to thank Seth Lloyd, Koji Azuma, Bill Munro, Richard Wilson, Edwin Hancock, Rod Van Meter, Marco Lucamarini, Riccardo Laurenza, Thomas Cope, Carlo Ottaviani, Gaetana Spedalieri, Cosmo Lupo, Samuel Braunstein, Saikat Guha and Dirk Englund for feedback and discussions.
Author information
Authors and Affiliations
Contributions
S.P. developed the theory, carried out the entire work, and wrote the manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note: Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Pirandola, S. End-to-end capacities of a quantum communication network. Commun Phys 2, 51 (2019). https://doi.org/10.1038/s42005-019-0147-3
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s42005-019-0147-3
This article is cited by
-
Trust evaluation model immune to decoherent noise in quantum communication network
Optical and Quantum Electronics (2024)
-
Surpassing the repeaterless bound with a photon-number encoded measurement-device-independent quantum key distribution protocol
npj Quantum Information (2023)
-
Complex quantum network models from spin clusters
Communications Physics (2023)
-
Breaking universal limitations on quantum conference key agreement without quantum memory
Communications Physics (2023)
-
Conference key agreement in a quantum network
npj Quantum Information (2023)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.