Abstract
Quantum entanglement is a building block of the entangled quantum networks of the quantum Internet. A fundamental problem of the quantum Internet is entanglement distribution. Since quantum entanglement will be fundamental to any future quantum networking scenarios, the distribution mechanism of quantum entanglement is a critical and emerging issue in quantum networks. Here we define the method of opportunistic entanglement distribution for the quantum Internet. The opportunistic model defines distribution sets that are aimed to select those quantum nodes for which the cost function picks up a local minimum. The cost function utilizes the error patterns of the local quantum memories and the predictability of the evolution of the entanglement fidelities. Our method provides efficient entanglement distributing with respect to the actual statuses of the local quantum memories of the node pairs. The model provides an easily-applicable, moderate-complexity solution for high-fidelity entanglement distribution in experimental quantum Internet scenarios.
Similar content being viewed by others
Introduction
Quantum entanglement has a central role in the quantum Internet1,2,3,4,5,6,7,8,9,10, quantum networking11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26, and long-distance quantum key distribution1,19,27,28. Entanglement distribution is a crucial phase for the construction of the entangled core network structure of the quantum Internet. In a quantum Internet scenario, quantum entanglement is a preliminary condition of quantum networking protocols27,29,30,31,32,33,34,35,36,37,38,39,40,41,42,43,44. Distant quantum nodes that share no quantum entanglement must communicate with their direct neighbors to distribute entanglement. To aim of entanglement distribution is to generate entanglement between a distant source node and a target node through a chain of intermediate quantum repeater nodes45,46,47,48,49,50,51,52,53,54,55,56,57. The intermediate quantum repeater nodes receive the entangled states, store them in their local quantum memories28,58,59, and apply a unitary operation (called entanglement swapping1,2,3,19) to extend the range of quantum entanglement. Storing quantum entanglement in the quantum nodes’ local quantum memories adds noise to the distribution process, since quantum memories are non-perfect devices34,60 and the error probabilities evolve in time1,49,50,51,52,53,54. As the error pattern of the evolution the quantum memories is predictable, the nodes can be characterized by a given storage success probability after a given time from the start of the storage.
The fidelity of entanglement61,62,63 is another critical parameter for entanglement distribution. In a quantum network with a chain of repeater nodes between a source and target nodes, for all pairs of entangled nodes (e.g., for nodes that share a common entanglement) a given lower bound in the fidelity of entanglement must be satisfied, otherwise the entanglement distribution fails1,64. The stored entangled states have a given amount of fidelity that is determined by the transmission procedure, such as the noise of the quantum channel, etc. The evolution of a given entangled system’s fidelity parameter is time-varying in quantum memory, since it evolves through time, from the beginning of storage to the actual current time. Therefore, it is necessary to consider the predictability of the evolution of both the error patterns of the nodes’ local quantum memories, and the evolution of the stored quantum states’ fidelity of entanglement. In our model, using these parameters, we define an appropriate cost function for the realization of entanglement distribution.
Here we define the method of opportunistic entanglement distribution for the quantum Internet. The proposed scheme utilizes a cost function that accounts for the error patterns of local quantum memories and also the evolution of entanglement fidelities. The opportunistic model defines distribution sets in the entangled quantum network of the quantum Internet. A distribution set contains those quantum nodes for which our cost function picks up a local minimum in comparison to the cost of the other nodes in the given distributing set. The distribution set selects a lowest-cost node from a given set of nodes to provide a maximal usability of stored entanglement. The cost function ensures that the nodes selected for entanglement distribution allow the lowest deviation in the entanglement fidelity from the start of storage, and that the behavior of the quantum memory error follows a predicted error model with respect to a given node pair. We also derive the computational complexity of the proposed method. The solution provides an easily-applicable, low-complexity solution for high-fidelity entanglement distribution in the quantum Internet.
The novel contributions of our manuscript are as follows:
-
1.
We define the method of opportunistic entanglement distribution for the quantum Internet.
-
2.
The proposed opportunistic model defines distribution sets that are aimed to select those quantum nodes for which the cost function picks up a local minimum. The cost function utilizes the error patterns of the local quantum memories and the predictability of the evolution of the entanglement fidelities.
-
3.
Our method provides efficient entanglement distributing with respect to the actual statuses of the local quantum memories of the node pairs.
-
4.
We derive the computational complexity of the model.
This paper is organized as follows. In Section 2 the preliminaries are summarized. Section 3 defines the method, while Section 4 proposes the results. Finally, Section 5 concludes the results.
Preliminaries
System Model
The quantum Internet setting is modeled as follows8. Let V refer to the nodes of an entangled quantum network N, with a transmitter quantum node \(A\in V\), a receiver quantum node \(B\in V\), and quantum repeater nodes \({R}_{i}\in V\), \(i=1,\ldots ,q\). Let \(E=\{{E}_{j}\}\), \(j=1,\ldots ,m\), refer to a set of edges between the nodes of V, where each Ej identifies an Ll-level entangled connection, \(l=1,\ldots ,r\), between quantum nodes xj and yj of edge Ej, respectively. The entanglement levels of the entangled connections in the entangled quantum network structure are defined as follows.
Entanglement Levels
In a quantum Internet setting, an \(N=(V,E)\) entangled quantum network consists of single-hop and multi-hop entangled connections, such that the single-hop entangled nodes (The l-level entangled nodes x, y refer to quantum nodes x and y connected by an entangled connection Ll.) are directly connected through an L1-level entanglement, while the multi-hop entangled nodes communicate through Ll-level entanglement. Focusing on the doubling architecture1,2,3 in the entanglement distribution procedure, the number of spanned nodes is doubled in each level of entanglement swapping (entanglement swapping is applied in an intermediate node to create a longer distance entanglement1). Therefore, the \(d{(x,y)}_{{{\rm{L}}}_{l}}\) hop distance in N for the Ll-level entangled connection between x, \(y\in V\) is denoted by8
with \(d{(x,y)}_{{{\rm{L}}}_{l}}-1\) intermediate quantum nodes between x and y. Therefore, l = 1 refers to a direct entangled connection between two quantum nodes x and y without intermediate quantum repeaters, while \(l > 1\) identifies a multilevel entanglement.
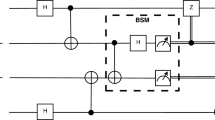
An entangled quantum network N is illustrated in Fig. 1. The quantum network integrates single-hop entangled nodes (depicted by gray nodes) and multi-hop entangled nodes (depicted by blue and orange nodes) connected by edges. The single-hop entangled nodes are directly connected through an L1-level entangled connection, while the multi-hop entangled nodes are connected by L2 and L3-level entangled connection.
Opportunistic entanglement distribution in a quantum Internet setting, \(N=(V,{\mathscr{S}})\). The entangled contacts of transmitter node A define the distributing set \({{\mathscr{D}}}_{A}\). From set \({{\mathscr{D}}}_{A}\), a quantum repeater node R1 is selected. Node R1 shares L2-level entanglement with A. The entangled contacts of the repeater node R1 define the distributing set \({{\mathscr{D}}}_{{R}_{1}}\). The iteration is repeated until target node B is reached via a quantum repeater node. In this network setting, B is reached via node R3 from set \({{\mathscr{D}}}_{{R}_{2}}\), where R3 shares L3-level entanglement with B. Applying the opportunistic entanglement distribution for the nodes of the network, a path between A and B is selected (depicted in bold).
The fidelity of entanglement of an Ll-level entangled connection E(x, y) between x, \(y\in V\) depends on the physical attributes of the quantum network.
Terms and Definitions
Entanglement Fidelity
Let
be the target Bell state subject to be created at the end of the entanglement distribution procedure between a particular source node A and receiver node B. The entanglement fidelity F at an actually created noisy quantum system σ between A and B is
where F is a value between 0 and 1, F = 1 for a perfect Bell state and F < 1 for an imperfect state. Without loss of generality, in an experimental quantum Internet setting, an aim is to reach F ≥ 0.98 over long distances1,3.
Some properties of F are as follows4,19. The fidelity for two pure quantum states \(|\phi \rangle \), \(|\psi \rangle \) is defined as
The fidelity of quantum states can describe the relation of a pure state \(|\psi \rangle \) and mixed quantum system \(\sigma ={\sum }_{i=0}^{n-1}\,{p}_{i}{\rho }_{i}={\sum }_{i=0}^{n-1}\,{p}_{i}|{\psi }_{i}\rangle \langle {\psi }_{i}|\), as
Fidelity can also be defined for mixed states σ and ρ, as
Method
Before giving the details of the algorithm, we briefly summarize the method of opportunistic entanglement distribution in a quantum Internet setting in Method 1.
Discussion
In Step 1, distributing entanglement between i and the direct contacts of i defines the distributing set \({{\mathscr{D}}}_{i}\), which can contain different levels of entangled contacts. In our opportunistic approach, the heterogonous entangled contacts leads to diverse hop-distances, specifically for an Ll-level entanglement \(l=1,\ldots ,r\), the \(d{(i,y)}_{{{\rm{L}}}_{l}}\), the hop-distance between a source node i and target node \({{\mathscr{D}}}_{i}\in y\) from the distributing set \({{\mathscr{D}}}_{i}\) is determined via (4) as \(d{(i,y)}_{{{\rm{L}}}_{l}}={2}^{l-1}\)1,2,3,8.
In Step 2, the next node j from a set \({{\mathscr{D}}}_{i}\) is selected by the same cost metric used for the selection of node i in Step 1. The cost metric65,66 used in the opportunistic node selection procedure in Steps 1–2 ensures the selection of those nodes that can preserve the entangled quantum states with the highest fidelity in their local quantum memories. From a given distributing set \({\mathscr{D}}\), only one node is selected in each iteration step. The cost function will be clarified later in the algorithm.
Finally, Step 3 provides an iteration to reach from the source node to the target node.
Figure 1 illustrates the method of opportunistic entanglement distribution in a quantum repeater network N. A given distributing set \({{\mathscr{D}}}_{i}\) of a node i can contain several different levels Ll of entangled contacts. From a distributing set \({{\mathscr{D}}}_{i}\), only one repeater node is selected in each level of iteration. Those quantum nodes that share L1-level entanglement are referred to as single-hop entangled nodes, while the other entangled nodes are referred to as multi-hop entangled nodes.
Ethics statement
This work did not involve any active collection of human data.
Results
Parameterization
Let \({{\mathscr{D}}}_{i}\) be a distributing set of a node i, and let \({p}_{i,j}^{{F}^{\ast }}\) be the probability of the shared entanglement stored in the quantum memories of nodes (i, j), where \(j\in {{\mathscr{D}}}_{i}\) identifies a repeater node Rj from the distributing set \({{\mathscr{D}}}_{i}\), with a fidelity \({F}^{\ast }\ge {F}_{crit}\), where Fcrit is a critical lower bound on the fidelity of entanglement.
Then, let \({p}_{i,{{\mathscr{D}}}_{i}}^{{F}^{\ast }}\) be the probability that \({F}^{\ast }\ge {F}_{crit}\) is satisfied between node i and at least one repeater node from \({{\mathscr{D}}}_{i}\).
Using \({p}_{i,{{\mathscr{D}}}_{i}}^{{F}^{\ast }}\) and \({p}_{i,j}^{{F}^{\ast }}\), a cost function \(f({p}_{i,{{\mathscr{D}}}_{i}}^{{F}^{\ast }})\) can be defined65,66 as
Similarly, with \({p}_{{{\mathscr{D}}}_{i},B}^{{F}^{\ast }}\) as the probability that there exists entanglement between a node \(j\in {{\mathscr{D}}}_{i}\) of \({{\mathscr{D}}}_{i}\) and the target node B with fidelity criterion \({F}^{\ast }\ge {F}_{crit}\), a cost function between a repeater node \(j\in {{\mathscr{D}}}_{i}\) and a target node B can be defined as
where \({p}_{j,B}^{{F}^{\ast }}\) is the probability of \({F}^{\ast }\ge {F}_{crit}\) fidelity entangled contact between a given \(j\in {{\mathscr{D}}}_{i}\) and B, while \({\varphi }_{i,j}\) is the probability that a given repeater node j is selected from \({{\mathscr{D}}}_{i}\) for i, defined66 as
where
From equations (7) and (8), the cost function between a quantum node i and a target node B at a distributing set \({{\mathscr{D}}}_{i}\), such that \({F}^{\ast }\ge {F}_{crit}\) holds for the fidelity of all entangled contacts from i to B, is therefore
The \({p}_{i,j}^{{F}^{\ast }}\) probabilities depend on the actual state of the quantum memory (particularly, on the εi error probability of the quantum memory of node i) and on the F fidelity of the stored entanglement. Parameters ε and F are time-varying in our model, which is denoted by ε(t) and F(t), where t refers to the storage time in quantum memory. Time t0 refers to the start of the storage of a quantum system in quantum memory.
Let \({\varepsilon }_{i,j}({t}_{0}+{\rm{\Delta }}t)\) identify the error probability of quantum memories in nodes (i, j) such that \({\varepsilon }_{i,j}\in [0,{\varepsilon }_{crit}]\) holds, which allows storing an \({F}^{\ast }\ge {F}_{crit}\) fidelity entanglement in the nodes after Δt time from start time t0. Therefore, at a εcrit critical upper bound on the quantum memories,
holds, where \({\zeta }_{i}({t}_{0}+{\rm{\Delta }}t)\) characterizes the change of the error probability of the quantum memory of node i at \({t}_{0}+{\rm{\Delta }}t\), as in
where \({\zeta }_{i}({t}_{0})\) is the εi error probability of the quantum memory of node i at t0, while \({\phi }_{i}({t}_{0},{\rm{\Delta }}t)\) is the change of εi from t0 to \({t}_{0}+{\rm{\Delta }}t\).
Let \({\eta }_{i}(t)=({\varepsilon }_{i}(t),1-{F}_{i}(t))\) identify the εi(t) quantum memory error probability and the Fi(t) stored entanglement fidelity in node i at time t. Then, the di,j distance between ηi and ηj in \({{\mathbb{R}}}^{2}\) identifies a \({d}_{i,j}\in [0,{d}_{{\rm{\max }}}]\), where dmax is the maximal allowable distance in \({{\mathbb{R}}}^{2}\), which forms an upper bound to the distances for which \({p}_{i,j}^{{F}^{\ast }} > 0\) holds, as
and
where
where
and
The fidelities Fi(t0) and \({F}_{i}({t}_{0},{\rm{\Delta }}t)\) refer to the fidelities of stored entanglement in a node i at t0 and t0, \({\rm{\Delta }}\)t, respectively, with relation for nodes (i, j)
where Fi,j is the difference of entanglement fidelities Fi and Fj, while FΔ is an upper bound on the fidelity difference.
From equation (15), the following relation holds for \({p}_{i,j}^{{F}^{\ast }}\):
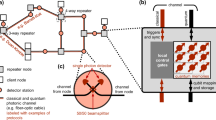
Figure 2 illustrates the evolution of the error probabilities of the local quantum memories and the fidelities of the stored entangled states. Time t0 refers to the start of storage in the quantum memory and time \({t}_{0}+{\rm{\Delta }}t\) is the current time. The distance \({d}_{i,j}({t}_{0}+{\rm{\Delta }}t)\) measures the difference of \({\eta }_{i}({t}_{0}+{\rm{\Delta }}t)\) and \({\eta }_{j}({t}_{0}+{\rm{\Delta }}t)\) of a node pair \((i,j)\). From the time evolution of the error probability of the quantum memory, it follows that \(\varepsilon ({t}_{0}+{\rm{\Delta }}t) > \varepsilon ({t}_{0})\), and \(F({t}_{0}+{\rm{\Delta }}t) < F({t}_{0})\) holds for the time evolution of the fidelity of the stored entanglement.
Evolution of the \({d}_{i,j}({t}_{0})\) and \({d}_{i,j}({t}_{0}+{\rm{\Delta }}t)\) distances in \({{\mathbb{R}}}^{2}\) with respect to a given node pair \((i,j)\); ε is the error probability of the local quantum memory and F is the fidelity of the stored entanglement in the local quantum memory. The initial states (storage starting at t0) of the nodes \((i,j)\) are identified by \({\eta }_{i}({t}_{0})\) and \({\eta }_{j}({t}_{0})\), the current states at time \({t}_{0}+{\rm{\Delta }}t\) of the nodes are \({\eta }_{i}({t}_{0}+{\rm{\Delta }}t)\) and \({\eta }_{j}({t}_{0}+{\rm{\Delta }}t)\). As \({d}_{i,j}({t}_{0}+{\rm{\Delta }}t) > {d}_{{\rm{\max }}}\), where dmax is a threshold, the yielding probability is \({p}_{i,j}^{{F}^{\ast }}=0\).
The normalized increase of distance di,j between nodes therefore yields a quantity \({\omega }_{i,j}\), \({\omega }_{i,j}\in [0,1]\), which characterizes the usability of a stored entanglement in \((i,j)\) from t0 to \({t}_{0}+{\rm{\Delta }}t\), as
As \({\omega }_{i,j}=1\), if no change occurs in the initial distance \({d}_{i,j}({t}_{0})\) in \({{\mathbb{R}}}^{2}\), thus
while \({\omega }_{i,j}=0\), if
so the yielding relation between \({p}_{i,j}^{{F}^{\ast }}\) and \({\omega }_{i,j}\) is
Equation (21) also characterizes the future behavior of the quantum memories in the nodes, i.e., the predictability of the error model of the quantum memories after a given time after beginning storage. The highest values of \({\omega }_{i,j}\) are therefore assigned to those memory units for which the error probabilities and the entanglement fidelities evolve by a given pattern.
For a given path \({\mathscr{P}}\) with \({A}_{\delta ,{U}_{k}}\) and \({B}_{\delta ,{U}_{k}}\) as the source and target nodes, respectively, associated with a demand δ of user Uk, \(k=1,\ldots ,K\), where K is the number of users; thus, the overall usability coefficient \({\omega }_{{A}_{\delta ,{U}_{k}},{B}_{\delta ,{U}_{k}}}\) for \({\mathscr{P}}\) is
To determine those quantum nodes for which both \({\omega }_{i,j}\) (21) and \({p}_{i,j}^{{F}^{\ast }}\) are high, a redefined cost function, ci,j, can be defined for a given \((i,j)\) as
which assigns the lowest cost to those node pairs for which \({\omega }_{i,j}\) and \({p}_{i,j}^{{F}^{\ast }}\) are high.
The remaining quantities from equations (7) and (9) can therefore be rewritten as
and
which yields the redefined cost of equation (8) as
The total cost between i and B such that \({F}^{\ast }\ge {F}_{crit}\) holds for all entangled contacts between quantum nodes i and B is therefore65,66
Opportunistic Entanglement Distribution
The aim of the opportunistic entanglement distribution algorithm \({{\mathscr{A}}}_{O}\) is to determine a shortest path \({{\mathscr{P}}}^{\ast }\) with respect to our cost function. The shortest path \({{\mathscr{P}}}^{\ast }\) contains those node pairs for which \({\omega }_{i,j}\) and \({p}_{i,j}^{{F}^{\ast }}\) are maximal, and therefore the resulting cost function (26) is the lowest in a quantum network N. Thus, the algorithm finds the repeater nodes for entanglement distribution by maximizing the usability of stored entanglement.
Some preliminary notations for the algorithm are as follows. Let \({A}_{\delta ,{U}_{k}}\) and \({B}_{\delta ,{U}_{k}}\) be the source and target nodes, respectively, associated with a demand δ of user Uk. The algorithm selects those nodes that provide the lowest cost with respect to ci,j for a given \((i,j)\) to distribute entanglement from \({A}_{\delta ,{U}_{k}}\) to \({B}_{\delta ,{U}_{k}}\). Assume that for a set S′ of nodes there exists a path to \({B}_{\delta ,{U}_{k}}\) in a quantum network N = (V, S). Let \(\tilde{S}\) refer to a set of nodes for which the shortest path to \({B}_{\delta ,{U}_{k}}\) is not yet determined.
The \({{\mathscr{A}}}_{O}\) algorithm of the minimal-cost opportunistic entanglement distribution is detailed in Algorithm 1.
Computational Complexity
The computational complexity of the minimal-cost \({{\mathscr{A}}}_{O}\) opportunistic entanglement distribution is as follows.
Let N = (V, E) be a quantum repeater network with |V| quantum nodes. Applying a \( {\mathcal L} \) logarithmic search67 to find a node with an actual minimal cost requires at most
steps, via \({\mathscr{O}}(\mathrm{log}\,|V|)\) comparisons.
Since the number of nodes is |V|, setting the final path cost for all quantum nodes requires at most
steps.
From (31) and (32) follows straightforwardly that the complexity of the minimal-cost opportunistic entanglement distribution algorithm is bounded above by
Conclusions
Here we defined a method for entanglement distribution in the quantum Internet. Our method utilizes distributing sets for quantum nodes, which can preserve quantum entanglement with the highest fidelity in their local quantum memories. The algorithm is opportunistic, since in each iteration step a node is selected from a distributing set that can provide optimal conditions. The cost function includes the utilization of the evolution of the error model of the local quantum memories, and the fidelities of the stored entangled states. A usability parameter quantifies the predictability of the evolution of the error model, and of the evolution of the entanglement fidelity. The computational complexity of the method is moderate, which allows for direct application in experimental quantum Internet scenarios and in long-distance quantum communications.
Data Availability
This work does not have any experimental data.
References
Van Meter, R. Quantum Networking. ISBN 1118648927, 9781118648926 (John Wiley and Sons Ltd, 2014).
Van Meter, R., Ladd, T. D., Munro, W. J. & Nemoto, K. System Design for a Long-Line Quantum Repeater. IEEE/ACM Transactions on Networking 17(3), 1002–1013 (2009).
Van Meter, R., Satoh, T., Ladd, T. D., Munro, W. J. & Nemoto, K. Path selection for quantum repeater networks. Networking Science 3(1–4), 82–95 (2013).
Gyongyosi, L., Imre, S. & Nguyen, H. V. A Survey on Quantum Channel Capacities. IEEE Communications Surveys and Tutorials, https://doi.org/10.1109/COMST.2017.2786748 (2018).
Lloyd, S. et al. Infrastructure for the quantum Internet. ACM SIGCOMM Computer Communication Review 34, 9–20 (2004).
Kimble, H. J. The quantum Internet. Nature 453, 1023–1030 (2008).
Van Meter, R. & Devitt, S. J. Local and Distributed Quantum Computation. IEEE Computer 49(9), 31–42 (2016).
Gyongyosi, L. & Imre, S. Decentralized Base-Graph Routing for the Quantum Internet, Physical Review A, https://doi.org/10.1103/PhysRevA.98.022310 (American Physical Society, 2018).
Gyongyosi, L. & Imre, S. Dynamic topology resilience for quantum networks. Proc. SPIE 10547, Advances in Photonics of Quantum Computing, Memory, and Communication XI, 105470Z, https://doi.org/10.1117/12.2288707 (22 February 2018).
Gyongyosi, L. & Imre, S. Topology Adaption for the Quantum Internet. Quantum Information Processing, https://doi.org/10.1007/s11128-018-2064-x (Springer Nature, 2018).
Pirandola, S., Laurenza, R., Ottaviani, C. & Banchi, L. Fundamental limits of repeaterless quantum communications, Nature Communications, 15043, https://doi.org/10.1038/ncomms15043 (2017).
Pirandola, S. et al. Theory of channel simulation and bounds for private communication. Quantum Sci. Technol. 3, 035009 (2018).
Pirandola, S. Capacities of repeater-assisted quantum communications. arXiv:1601.00966 (2016).
Laurenza, R. & Pirandola, S. General bounds for sender-receiver capacities in multipoint quantum communications. Phys. Rev. A 96, 032318 (2017).
Gyongyosi, L. & Imre, S. A Survey on Quantum Computing Technology. Computer Science Review, https://doi.org/10.1016/j.cosrev.2018.11.002, ISSN: 1574-0137 (Elsevier, 2018).
Gyongyosi, L. & Imre, S. Multilayer Optimization for the Quantum Internet. Scientific Reports, https://doi.org/10.1038/s41598-018-30957-x (Nature, 2018).
Gyongyosi, L. & Imre, S. Entanglement Availability Differentiation Service for the Quantum Internet. Scientific Reports, https://doi.org/10.1038/s41598-018-28801-3, https://www.nature.com/articles/s41598-018-28801-3 (Nature, 2018).
Gyongyosi, L. & Imre, S. Entanglement-Gradient Routing for Quantum Networks. Scientific Reports, https://doi.org/10.1038/s41598-017-14394-w, https://www.nature.com/articles/s41598-017-14394-w (Nature, 2017).
Imre, S. & Gyongyosi, L. Advanced Quantum Communications - An Engineering Approach. (New Jersey, Wiley-IEEE Press, 2013).
Caleffi, M. End-to-End Entanglement Rate: Toward a Quantum Route Metric, 2017 IEEE Globecom, https://doi.org/10.1109/GLOCOMW.2017.8269080 (2018).
Caleffi, M. Optimal Routing for Quantum Networks. IEEE Access Vol 5, https://doi.org/10.1109/ACCESS.2017.2763325 (2017).
Caleffi, M., Cacciapuoti, A. S. & Bianchi, G. Quantum Internet: from Communication to Distributed Computing. aXiv:1805.04360 (2018).
Castelvecchi, D. The quantum internet has arrived. Nature, https://www.nature.com/articles/d41586-018-01835-3 (News and Comment, 2018).
Cacciapuoti, A. S. et al. Quantum Internet: Networking Challenges in Distributed Quantum Computing. arXiv:1810.08421 (2018).
Kok, P. et al. Linear optical quantum computing with photonic qubits. Rev. Mod. Phys. 79, 135–174 (2007).
Petz, D. Quantum Information Theory and Quantum Statistics (Springer-Verlag, Heidelberg, Hiv: 6, 2008).
Bacsardi, L. On the Way to Quantum-Based Satellite Communication. IEEE Comm. Mag. 51(08), 50–55 (2013).
Muralidharan, S., Kim, J., Lutkenhaus, N., Lukin, M. D. & Jiang, L. Ultrafast and Fault-Tolerant Quantum Communication across Long Distances. Phys. Rev. Lett. 112, 250501 (2014).
Biamonte, J. et al. Quantum Machine Learning. Nature 549, 195–202 (2017).
Lloyd, S., Mohseni, M. & Rebentrost, P. Quantum algorithms for supervised and unsupervised machine learning. arXiv:1307.0411 (2013).
Lloyd, S., Mohseni, M. & Rebentrost, P. Quantum principal component analysis. Nature Physics 10, 631 (2014).
Lloyd, S. Capacity of the noisy quantum channel. Physical Rev. A 55, 1613–1622 (1997).
Lloyd, S. The Universe as Quantum Computer. A Computable Universe: Understanding and exploring Nature as computation, Zenil, H. ed., arXiv:1312.4455v1 (World Scientific, Singapore, 2013).
Shor, P. W. Scheme for reducing decoherence in quantum computer memory. Phys. Rev. A 52, R2493–R2496 (1995).
Chou, C. et al. Functional quantum nodes for entanglement distribution over scalable quantum networks. Science 316(5829), 1316–1320 (2007).
Yuan, Z. et al. Experimental demonstration of a BDCZ quantum repeater node Nature 454, 1098–1101 (2008).
Kobayashi, H., Le Gall, F., Nishimura, H. & Rotteler, M. General scheme for perfect quantum network coding with free classical communication. Lecture Notes in Computer Science (Automata, Languages and Programming SE-52 vol. 5555) pp 622–633 (Springer, 2009).
Hayashi, M. Prior entanglement between senders enables perfect quantum network coding with modification, Physical Review A Vol. 76, 040301(R) (2007).
Hayashi, M., Iwama, K., Nishimura, H., Raymond, R. & Yamashita, S. Quantum network coding. Lecture Notes in Computer Science (STACS 2007 SE52 vol. 4393) eds Thomas, W. & Weil, P. (Berlin Heidelberg: Springer, 2007).
Chen, L. & Hayashi, M. Multicopy and stochastic transformation of multipartite pure states. Physical Review A 83(No. 2), 022331 (2011).
Schoute, E., Mancinska, L., Islam, T., Kerenidis, I. & Wehner, S. Shortcuts to quantum network routing. arXiv:1610.05238 (2016).
Lloyd, S. & Weedbrook, C. Quantum generative adversarial learning. Phys. Rev. Lett. 121, arXiv:1804.09139 (2018).
Gisin, N. & Thew, R. Quantum Communication. Nature Photon. 1, 165–171 (2007).
Xiao, Y. F. & Gong, Q. Optical microcavity: from fundamental physics to functional photonics devices. Science Bulletin 61, 185–186 (2016).
Briegel, H. J., Dur, W., Cirac, J. I. & Zoller, P. Quantum repeaters: the role of imperfect local operations in quantum communication. Phys. Rev. Lett. 81, 5932–5935 (1998).
Dur, W., Briegel, H. J., Cirac, J. I. & Zoller, P. Quantum repeaters based on entanglement purification. Phys. Rev. A 59, 169–181 (1999).
Duan, L. M., Lukin, M. D., Cirac, J. I. & Zoller, P. Long-distance quantum communication with atomic ensembles and linear optics. Nature 414, 413–418 (2001).
Van Loock, P. et al. Hybrid quantum repeater using bright coherent light. Phys. Rev. Lett. 96, 240501 (2006).
Zhao, B., Chen, Z. B., Chen, Y. A., Schmiedmayer, J. & Pan, J. W. Robust creation of entanglement between remote memory qubits. Phys. Rev. Lett. 98, 240502 (2007).
Goebel, A. M. et al. Multistage Entanglement Swapping. Phys. Rev. Lett. 101, 080403 (2008).
Simon, C. et al. Quantum Repeaters with Photon Pair Sources and Multimode Memories. Phys. Rev. Lett. 98, 190503 (2007).
Tittel, W. et al. Photon-echo quantum memory in solid state systems. Laser Photon. Rev. 4, 244–267 (2009).
Sangouard, N., Dubessy, R. & Simon, C. Quantum repeaters based on single trapped ions. Phys. Rev. A 79, 042340 (2009).
Dur, W. & Briegel, H. J. Entanglement purification and quantum error correction. Rep. Prog. Phys 70, 1381–1424 (2007).
Sheng, Y. B. & Zhou, L. Distributed secure quantum machine learning. Science Bulletin 62, 1025–1019 (2017).
Leung, D., Oppenheim, J. & Winter, A. Quantum network communication; the butterfly and beyond. IEEE Trans. Inf. Theory 56, 3478–90 (2010).
Kobayashi, H., Le Gall, F., Nishimura, H. & Rotteler, M. Perfect quantum network communication protocol based on classical network coding. Proceedings of 2010 IEEE International Symposium on Information Theory (ISIT) pp 2686–90 (2010).
Zhang, W. et al. Quantum Secure Direct Communication with Quantum Memory. Phys. Rev. Lett. 118, 220501 (2017).
Enk, S. J., Cirac, J. I. & Zoller, P. Photonic channels for quantum communication. Science 279, 205–208 (1998).
Shor, P. W. Fault-tolerant quantum computation. 37th Symposium on Foundations of Computing pp. 56–65 (IEEE Computer Society Press, 1996).
Jozsa, R. Fidelity for Mixed Quantum States. J. Mod. Optics 41, 2315 (1995).
Nielsen, M. A. The entanglement fidelity and quantum error correction. arXiv:quant-ph/9606012 (1996).
Schumacher, B. Sending quantum entanglement through noisy channels. Phys Rev A 54(4), 2614–2628 (1996).
Fedrizzi, A. et al. High-fidelity transmission of entanglement over a high-loss free-space channel. Nature Physics 5(6), 389–392 (2009).
Leepila, R. Routing Schemes for Survivable and Energy-Efficient Networks, PhD Thesis (Department of Information and Communication Engineering, The University of Electro-Communications, 2014).
Rak, J. Resilient Routing in Communication Networks (Springer, 2015).
Knuth, D. Sorting and searching. The Art of Computer Programming, ISBN 978-0-201-89685-5 (Addison-Wesley Professional, 1998).
Acknowledgements
This work was partially supported by the European Research Council through the Advanced Fellow Grant, in part by the Royal Society’s Wolfson Research Merit Award, in part by the Engineering and Physical Sciences Research Council under Grant EP/L018659/1, by the Hungarian Scientific Research Fund - OTKA K-112125, and by the National Research Development and Innovation Office of Hungary (Project No. 2017-1.2.1-NKP-2017-00001), and in part by the BME Artificial Intelligence FIKP grant of EMMI (BME FIKP-MI/SC).
Author information
Authors and Affiliations
Contributions
L.GY. designed the protocol and wrote the manuscript. L.GY. and S.I. analyzed the results. All authors reviewed the manuscript.
Corresponding author
Ethics declarations
Competing Interests
The authors declare no competing interests.
Additional information
Publisher’s note: Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Gyongyosi, L., Imre, S. Opportunistic Entanglement Distribution for the Quantum Internet. Sci Rep 9, 2219 (2019). https://doi.org/10.1038/s41598-019-38495-w
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-019-38495-w
This article is cited by
-
Optimal quantum network decongestion strategies
Scientific Reports (2023)
-
Multi-qubit teleportation and multi-bit superdense coding via cascade splitting
Optical and Quantum Electronics (2023)
-
Quantum stretching protocol to share states among three nonlocal qubits
Optical and Quantum Electronics (2023)
-
The theorem of unified locality
SN Applied Sciences (2023)
-
Quantum Fourier states and gates: teleportation via rough entanglement
Optical and Quantum Electronics (2023)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.