Abstract
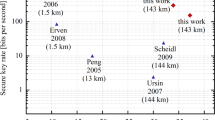
Quantum key distribution (QKD)1,2,3 is a theoretically secure way of sharing secret keys between remote users. It has been demonstrated in a laboratory over a coiled optical fibre up to 404 kilometres long4,5,6,7. In the field, point-to-point QKD has been achieved from a satellite to a ground station up to 1,200 kilometres away8,9,10. However, real-world QKD-based cryptography targets physically separated users on the Earth, for which the maximum distance has been about 100 kilometres11,12. The use of trusted relays can extend these distances from across a typical metropolitan area13,14,15,16 to intercity17 and even intercontinental distances18. However, relays pose security risks, which can be avoided by using entanglement-based QKD, which has inherent source-independent security19,20. Long-distance entanglement distribution can be realized using quantum repeaters21, but the related technology is still immature for practical implementations22. The obvious alternative for extending the range of quantum communication without compromising its security is satellite-based QKD, but so far satellite-based entanglement distribution has not been efficient23 enough to support QKD. Here we demonstrate entanglement-based QKD between two ground stations separated by 1,120 kilometres at a finite secret-key rate of 0.12 bits per second, without the need for trusted relays. Entangled photon pairs were distributed via two bidirectional downlinks from the Micius satellite to two ground observatories in Delingha and Nanshan in China. The development of a high-efficiency telescope and follow-up optics crucially improved the link efficiency. The generated keys are secure for realistic devices, because our ground receivers were carefully designed to guarantee fair sampling and immunity to all known side channels24,25. Our method not only increases the secure distance on the ground tenfold but also increases the practical security of QKD to an unprecedented level.
This is a preview of subscription content, access via your institution
Access options
Access Nature and 54 other Nature Portfolio journals
Get Nature+, our best-value online-access subscription
$29.99 / 30 days
cancel any time
Subscribe to this journal
Receive 51 print issues and online access
$199.00 per year
only $3.90 per issue
Buy this article
- Purchase on Springer Link
- Instant access to full article PDF
Prices may be subject to local taxes which are calculated during checkout



Similar content being viewed by others
Data availability
The data that support the findings of this study are available from the corresponding authors on reasonable request.
References
Bennett, C. H. & Brassard, G. Quantum cryptography: public key distribution and coin tossing. In Proc. Int. Conf. on Computers, Systems and Signal Processing 175–179 (1984).
Ekert, A. K. Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67, 661 (1991).
Bennett, C. H., Brassard, G. & Mermin, N. D. Quantum cryptography without Bell’s theorem. Phys. Rev. Lett. 68, 557 (1992).
Peng, C.-Z. et al. Experimental long-distance decoy-state quantum key distribution based on polarization encoding. Phys. Rev. Lett. 98, 010505 (2007).
Rosenberg, D. et al. Long-distance decoy-state quantum key distribution in optical fiber. Phys. Rev. Lett. 98, 010503 (2007).
Yin, H.-L. et al. Measurement-device-independent quantum key distribution over a 404 km optical fiber. Phys. Rev. Lett. 117, 190501 (2016).
Boaron, A. et al. Secure quantum key distribution over 421 km of optical fiber. Phys. Rev. Lett. 121, 190502 (2018).
Liao, S.-K. et al. Satellite-to-ground quantum key distribution. Nature 549, 43 (2017).
Liao, S.-K. et al. Space-to-ground quantum key distribution using a small-sized payload on Tiangong-2 Space Lab. Chin. Phys. Lett. 34, 090302 (2017).
Yin, J. et al. Satellite-to-ground entanglement-based quantum key distribution. Phys. Rev. Lett. 119, 200501 (2017).
Schmitt-Manderbach, T. et al. Experimental demonstration of free-space decoy-state quantum key distribution over 144 km. Phys. Rev. Lett. 98, 010504 (2007).
Ursin, R. et al. Entanglement-based quantum communication over 144 km. Nat. Phys. 3, 481 (2007).
Elliott, C. et al. Current status of the DARPA quantum network. In Quantum Information and Computation III Vol. 5815, 138–150 (International Society for Optics and Photonics, 2005).
Peev, M. et al. The SECOQC quantum key distribution network in Vienna. New J. Phys. 11, 075001 (2009).
Chen, T.-Y. et al. Field test of a practical secure communication network with decoy-state quantum cryptography. Opt. Express 17, 6540 (2009).
Sasaki, M. et al. Field test of quantum key distribution in the Tokyo QKD network. Opt. Express 19, 10387–10409 (2011).
Qiu, J. et al. Quantum communications leap out of the lab. Nature 508, 441 (2014).
Liao, S.-K. et al. Satellite-relayed intercontinental quantum network. Phys. Rev. Lett. 120, 030501 (2018).
Koashi, M. & Preskill, J. Secure quantum key distribution with an uncharacterized source. Phys. Rev. Lett. 90, 057902 (2003).
Ma, X., Fung, C.-H. F. & Lo, H.-K. Quantum key distribution with entangled photon sources. Phys. Rev. A 76, 012307 (2007).
Briegel, H.-J., Dur, W., Cirac, J. I. & Zoller, P. Quantum repeaters: the role of imperfect local operations in quantum communication. Phys. Rev. Lett. 81, 5932–5935 (1998).
Yang, S.-J., Wang, X.-J., Bao, X.-H. & Pan, J.-W. An efficient quantum light–matter interface with sub-second lifetime. Nat. Photon. 10, 381 (2016).
Yin, J. et al. Satellite-based entanglement distribution over 1200 kilometers. Science 356, 1140 (2017).
Lo, H.-K., Curty, M. & Tamaki, K. Secure quantum key distribution. Nat. Photon. 8, 595 (2014).
Xu, F., Ma, X., Zhang, Q., Lo, H.-K. & Pan, J.-W. Secure quantum key distribution with realistic devices. Rev. Mod. Phys. 92, 025002 (2020).
Lydersen, L. et al. Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photon. 4, 686 (2010).
Zhao, Y., Fung, C.-H., Qi, B., Chen, C. & Lo, H.-K. Quantum hacking: experimental demonstration of time-shift attack against practical quantum-key-distribution systems. Phys. Rev. A 78, 042333 (2008).
Weier, H. et al. Quantum eavesdropping without interception: an attack exploiting the dead time of single-photon detectors. New J. Phys. 13, 073024 (2011).
Li, H.-W. et al. Attacking a practical quantum-key-distribution system with wavelength-dependent beam-splitter and multiwavelength sources. Phys. Rev. A 84, 062308 (2011).
Sajeed, S. et al. Security loophole in free-space quantum key distribution due to spatial-mode detector-efficiency mismatch. Phys. Rev. A 91, 062301 (2015).
Clauser, J. F., Horne, M. A., Shimony, A. & Holt, R. A. Proposed experiment to test local hidden-variable theories. Phys. Rev. Lett. 23, 880 (1969).
Koashi, M. Simple security proof of quantum key distribution based on complementarity. New J. Phys. 11, 045018 (2009).
Tomamichel, M., Lim, C. C. W., Gisin, N. & Renner, R. Tight finite-key analysis for quantum cryptography. Nat. Commun. 3, 634 (2012).
Peng, C.-Z. et al. Experimental free-space distribution of entangled photon pairs over 13 km: towards satellite-based global quantum communication. Phys. Rev. Lett. 94, 150501 (2005).
Cao, Y. et al. Bell test over extremely high-loss channels: towards distributing entangled photon pairs between earth and the moon. Phys. Rev. Lett. 120, 140405 (2018).
Ladd, T. D. et al. Quantum computers. Nature 464, 45–53 (2010).
Makarov, V., Anisimov, A. & Skaar, J. Effects of detector efficiency mismatch on security of quantum cryptosystems. Phys. Rev. A 74, 022313 (2006).
Qi, B., Fung, C.-H.F., Lo, H.-K. & Ma, X. Time-shift attack in practical quantum cryptosystems. Quantum Inf. Comput. 7, 73 (2007).
Gerhardt, I. et al. Experimentally faking the violation of Bell’s inequalities. Phys. Rev. Lett. 107, 170404 (2011).
Bugge, A. N. et al. Laser damage helps the eavesdropper in quantum cryptography. Phys. Rev. Lett. 112, 070503 (2014).
Lo, H.-K., Curty, M. & Qi, B. Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2012).
Scarani, V. et al. The security of practical quantum key distribution. Rev. Mod. Phys. 81, 1301–1350 (2009).
Shor, P. & Preskill, J. Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85, 441 (2000).
Gottesman, D., Lo, H.-K., Lütkenhaus, N. & Preskill, J. Security of quantum key distribution with imperfect devices. Quantum Inf. Comput. 4, 325 (2004).
Mayers, D. J. Unconditional security in quantum cryptography. J. Assoc. Comput. Mach. 48, 351–406 (2001).
Lo, H. K. & Chau, H. F. Unconditional security of quantum key distribution over arbitrarily long distances. Science 283, 2050 (1999).
Ben-Or, M., Horodecki, M., Leung, D. W., Mayers, D. & Oppenheim, J. In Proc. 2nd Int. Conf. on Theory of Cryptography (TCC'05) 386–406 (Springer, 2005).
Renner, R. Security of quantum key distribution. PhD thesis, ETH Zurich (2005); preprint at https://arxiv.org/abs/quant-ph/0512258.
Tsurumaru, T. Leftover hashing from quantum error correction: unifying the two approaches to the security proof of quantum key distribution. Preprint at https://arxiv.org/abs/1809.05479 (2018).
Serfling, R. J. Probability inequalities for the sum in sampling without replacement. Ann. Stat. 2, 39–48 (1974).
Curty, M. et al. Finite-key analysis for measurement-device-independent quantum key distribution. Nat. Commun. 5, 3732 (2014).
Fung, C.-H. F., Tamaki, K., Qi, B., Lo, H.-K. & Ma, X. Security proof of quantum key distribution with detection efficiency mismatch. Quantum Inf. Comput. 9, 131–165 (2009).
Marøy, Ø., Lydersen, L. & Skaar, J. Security of quantum key distribution with arbitrary individual imperfections. Phys. Rev. A 82, 032337 (2010).
Acknowledgements
We acknowledge discussions with X. Ma and C. Jiang. We thank colleagues at the National Space Science Center, China Xi’an Satellite Control Center, National Astronomical Observatories, Xinjiang Astronomical Observatory, Purple Mountain Observatory, and Qinghai Station for their management and coordination. We thank G.-B. Li, L.-L. Ma, Z. Wang, Y. Jiang, H.-B. Li, S.-J. Xu, Y.-Y. Yin, W.-C. Sun and Y. Wang for their long-term assistance in observation. This work was supported by the National Key R&D Program of China (grant number 2017YFA0303900), the Shanghai Municipal Science and Technology Major Project (grant number 2019SHZDZX01), the Anhui Initiative in Quantum Information Technologies, Science and Technological Fund of Anhui Province for Outstanding Youth (grant number 1808085J18) and the National Natural Science Foundation of China (grant numbers U1738201, 61625503, 11822409, 11674309, 11654005 and 61771443).
Author information
Authors and Affiliations
Contributions
C.-Z.P., A.K.E. and J.-W.P. conceived the research. J.Y., C.-Z.P. and J.-W.P. designed the experiments. J.Y., Y.-H.L., S.-K.L., M.Y., Y.C., J.-G.R., S.-L.L., C.-Z.P. and J.-W.P. developed the follow-up optics and monitoring circuit. J.Y., Y.-M.H., C.-Z.P. and J.-W.P. developed the efficiency telescopes. J.Y., S.-K.L., Y.C., L.Z., W.-Q.C., R.S., L.D., J.-Y.W., C.-Z.P. and J.-W.P. designed and developed the satellite and payloads. J.Y., L.Z., W.-Q.C., W.-Y.L. and C.-Z.P. developed the software. F.X., X.-B.W., A.K.E. and J.-W.P. performed the security proof and analysis. L.L., Q.Z., N.-L.L., Y.-A.C., X.-B.W., F.X., C.-Z.P., A.K.E. and J.-W.P. contributed to the theoretical study and implementation against device imperfections. F.X., C.-Y.L., C.-Z.P. and J.-W.P. analysed the data and wrote the manuscript, with input from J.Y., Y.-H.L., M.Y., Y.C. and A.K.E. All authors contributed to the data collection, discussed the results and reviewed the manuscript. J.-W.P. supervised the whole project.
Corresponding authors
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Extended data figures and tables
Extended Data Fig. 1 Satellite-to-Delingha link efficiencies under different weather conditions.
a, The data in previous work23 was taken in different orbits during the period of 7 December 2016 to 22 December 2016. b, The data in current work was taken in different orbits during the period of 6 September 2018 to 22 October 2018. Here the change of link efficiencies on different days was caused by the weather conditions.
Extended Data Fig. 2 Multiple orbits of satellite-to-Delingha link efficiencies under good weather conditions.
Stable and high collection efficiencies were observed during the period of October 2018 to April 2019.
Extended Data Fig. 3 The comparison of satellite-to-Delingha link efficiency under the best-orbit condition.
a, After improving the link efficiency with high-efficiency telescopes and follow-up optics, on average, the current work shows a 3-dB enhancement in the collection efficiency over that of ref. 23. The lines are linear fits to the data. b, Some representative values.
Extended Data Fig. 4 The finite-key secret key rate R versus the QBER.
For the 3,100 s of data collected in our experiment, a QBER of below about 6.0% is required to produce a positive key. The previous work23 demonstrated a QBER of 8.1%, which is not sufficient to generate a secret key. In this work, a QBER of 4.5% and a secret key rate of 0.12 bits per second are demonstrated over 1,120 km. If one ignores the important finite-key effect, the QBER in ref. 23 is slightly lower than the well known asymptotic limit of 11% (ref. 43).
Extended Data Fig. 5 Schematics of the detection and blinding-attack monitoring circuit.
The biased voltage (HV) is applied to an avalanche photodiode through a passive quenching resistance (Rq = 500 kΩ) and a sampling resistance (Rs = 10 kΩ). The avalanche signals are read out as click or no-click events through a signal-discrimination circuit. The blinding signal monitor is shown in the dot-dash diagram. A resistor-capacitor filter and a voltage follower are used to smooth and minimize the impact on the signals. The outputs of an analogue to digital converter (ADC), at a sampling rate of 250 kHz, are registered by computer data acquisition (PC-DAQ). R1, resistor; C1, capacitor; OA, operational amplifier.
Extended Data Fig. 6
The transmission of the beam splitter within the selected bandwidth of wavelength.
Rights and permissions
About this article
Cite this article
Yin, J., Li, YH., Liao, SK. et al. Entanglement-based secure quantum cryptography over 1,120 kilometres. Nature 582, 501–505 (2020). https://doi.org/10.1038/s41586-020-2401-y
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1038/s41586-020-2401-y
This article is cited by
-
Verifying the security of a continuous variable quantum communication protocol via quantum metrology
npj Quantum Information (2024)
-
Quantum key distribution over a mimicked dynamic-scattering channel
Science China Information Sciences (2024)
-
Quantum-secured time transfer between precise timing facilities: a field trial with simulated satellite links
GPS Solutions (2024)
-
Analysis and protection to user privacy in quantum private query with non-ideal light source
Quantum Information Processing (2024)
-
Enhanced Performance of Measurement-device-independent Quantum Key Distribution over Turbulent Channels through Adaptive Optics
Quantum Information Processing (2024)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.