Abstract
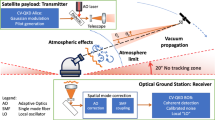
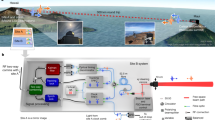
High-precision time synchronization for remote clocks plays an important role in fundamental science1,2,3 and real-life applications4,5. However, current time synchronization techniques6,7 have been shown to be vulnerable to sophisticated adversaries8. There is a compelling need for fundamentally new methods to distribute high-precision time information securely. Here, we propose a satellite-based quantum-secure time transfer (QSTT) scheme based on two-way quantum key distribution in free space and experimentally verify the key technologies of the scheme via the Micius quantum satellite. In QSTT, a quantum signal (for example, a single photon) is used as the carrier for both the time transfer and the secret-key generation, offering quantum-enhanced security for transferring the time signal and time information. We perform a satellite-to-ground time synchronization using single-photon-level signals and achieve a quantum bit error rate of less than 1%, a time data rate of 9 kHz and a time-transfer precision of 30 ps. These results offer possibilities towards an enhanced infrastructure for a time-transfer network, whose security stems from quantum physics.
This is a preview of subscription content, access via your institution
Access options
Access Nature and 54 other Nature Portfolio journals
Get Nature+, our best-value online-access subscription
$29.99 / 30 days
cancel any time
Subscribe to this journal
Receive 12 print issues and online access
$209.00 per year
only $17.42 per issue
Buy this article
- Purchase on Springer Link
- Instant access to full article PDF
Prices may be subject to local taxes which are calculated during checkout




Similar content being viewed by others
Data availability
Source data are available for this paper. All other data that support the plots within this paper and other findings of this study are available from the corresponding author upon reasonable request.
Code availability
All relevant codes or algorithms are available from the corresponding author upon reasonable request.
References
Riehle, F. Optical clock networks. Nat. Photon. 11, 25–31 (2017).
Kolkowitz, S. et al. Gravitational wave detection with optical lattice atomic clocks. Phys. Rev. D 94, 124043 (2016).
Marra, G. et al. Ultrastable laser interferometry for earthquake detection with terrestrial and submarine cables. Science 361, 486–490 (2018).
Corbett, J. C. et al. Spanner: Google’s globally distributed database. ACM Trans. Comput. Syst. 31, 1–22 (2013).
De La Ree, J., Centeno, V., Thorp, J. S. & Phadke, A. G. Synchronized phasor measurement applications in power systems. IEEE Trans. Smart Grid 1, 20–27 (2010).
Mills, D. L. Internet time synchronization: the network time protocol. IEEE Trans. Commun. 39, 1482–1493 (1991).
Lewandowski, W., Azoubib, J. & Klepczynski, W. J. GPS: primary tool for time transfer. Proc. IEEE 87, 163–172 (1999).
Humphreys, T. E., Ledvina, B. M., Psiaki, M. L., O’Hanlon, B. W. & Kintner, P. M. Assessing the spoofing threat: development of a portable GPS civilian spoofer. In Proceedings of the 21st International Technical Meeting of the Satellite Division of The Institute of Navigation (ION GNSS 2008) 2314–2325 (Institute of Navigation, 2008).
Kerns, A. J., Shepard, D. P., Bhatti, J. A. & Humphreys, T. E. Unmanned aircraft capture and control via GPS spoofing. J. Field Robot. 31, 617–636 (2014).
Bhatti, J. & Humphreys, T. E. Hostile control of ships via false GPS signals: demonstration and detection. Navigation J. Inst. Navigation 64, 51–66 (2017).
Allan, D. W. & Weiss, M. A. Accurate time and frequency transfer during common-view of a GPS satellite. In Proceedings of the 34th Annual Symposium on Frequency Control 334–346 (IEEE, 1980).
Warner, J. S. & Johnston, R. G. GPS spoofing countermeasures. Homel. Security J. 25, 19–27 (2003).
Smith, D. E. et al. Two-way laser link over interplanetary distance. Science 311, 53–53 (2006).
Samain, E. et al. Time transfer by laser link-the T2L2 experiment on Jason-2 and further experiments. Int. J. Mod. Phys. D 17, 1043–1054 (2008).
Giorgetta, F. R. et al. Optical two-way time and frequency transfer over free space. Nat. Photon. 7, 434–438 (2013).
Predehl, K. et al. A 920-kilometer optical fiber link for frequency metrology at the 19th decimal place. Science 336, 441–444 (2012).
Sinclair, L. C. et al. Comparing optical oscillators across the air to milliradians in phase and 10−17 in frequency. Phys. Rev. Lett. 120, 050801 (2018).
Treytl, A., Gaderer, G., Hirschler, B. & Cohen, R. Traps and pitfalls in secure clock synchronization. In Proceedings of the IEEE International Symposium on Precision Clock Synchronization for Measurement, Control and Communication 18–24 (IEEE, 2007).
Ullmann, M. & Vögeler, M. Delay attacks—implication on NTP and PTP time synchronization. In Proceedings of the International Symposium on Precision Clock Synchronization for Measurement, Control and Communication 1–6 (IEEE, 2009).
Tippenhauer, N. O., Pöpper, C., Rasmussen, K. B. & Capkun, S. On the requirements for successful GPS spoofing attacks. In Proceedings of the 18th ACM Conference on Computer and Communications Security 75–86 (ACM, 2011).
Jafarnia-Jahromi, A., Broumandan, A., Nielsen, J. & Lachapelle, G. GPS vulnerability to spoofing threats and a review of antispoofing techniques. Int. J. Navigation Observation 2012, 127072 (2012).
Narula, L. & Humphreys, T. Requirements for secure clock synchronization. IEEE J. Sel. Top. Signal Process. 12, 749–762 (2018).
Jozsa, R., Abrams, D. S., Dowling, J. P. & Williams, C. P. Quantum clock synchronization based on shared prior entanglement. Phys. Rev. Lett. 85, 2010–2013 (2000).
Ilo-Okeke, E. O., Tessler, L., Dowling, J. P. & Byrnes, T. Remote quantum clock synchronization without synchronized clocks. npj Quantum Inf. 4, 40 (2018).
Giovannetti, V., Lloyd, S. & Maccone, L. Quantum-enhanced positioning and clock synchronization. Nature 412, 417–419 (2001).
Valencia, A., Scarcelli, G. & Shih, Y. Distant clock synchronization using entangled photon pairs. Appl. Phys. Lett. 85, 2655–2657 (2004).
Marcikic, I., Lamas-Linares, A. & Kurtsiefer, C. Free-space quantum key distribution with entangled photons. Appl. Phys. Lett. 89, 101122 (2006).
Ho, C., Lamas-Linares, A. & Kurtsiefer, C. Clock synchronization by remote detection of correlated photon pairs. N. J. Phys. 11, 045011 (2009).
Lee, J. et al. Asymmetric delay attack on an entanglement-based bidirectional clock synchronization protocol. Appl. Phys. Lett. 115, 141101 (2019).
Komar, P. et al. A quantum network of clocks. Nat. Phys. 10, 582–587 (2014).
Lo, H. K. & Chau, H. F. Unconditional security of quantum key distribution over arbitrarily long distances. Science 283, 2050–2056 (1999).
Shor, P. W. & Preskill, J. Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85, 441–444 (2000).
Lo, H.-K., Curty, M. & Tamaki, K. Secure quantum key distribution. Nat. Photon. 8, 595–604 (2014).
Liao, S.-K. et al. Satellite-to-ground quantum key distribution. Nature 549, 43–47 (2017).
Yin, J. et al. Satellite-based entanglement distribution over 1200 kilometers. Science 356, 1140–1144 (2017).
Ren, J.-G. et al. Ground-to-satellite quantum teleportation. Nature 549, 70–73 (2017).
Choi, K. K., Ray, J., Griffiths, J. & Bae, T.-S. Evaluation of GPS orbit prediction strategies for the IGS ultra-rapid products. GPS Solut. 17, 403–412 (2013).
Ma, X., Qi, B., Zhao, Y. & Lo, H.-K. Practical decoy state for quantum key distribution. Phys. Rev. A 72, 012326 (2005).
Author information
Authors and Affiliations
Contributions
Q.Z., F.X., C.-Z.P. and J.-W.P. conceived the research. Q.S., J.Y., Y.-A.C., Q.Z., F.X., C.-Z.P. and J.-W.P. designed the experiments. F.X. analysed the security. H.D., Q.S., C.-Z.W., S.-L.L., W.-Y.L., W.-Q.C., S.-K.L., J.-G.R., J.Y., Y.-A.C., Q.Z., F.X., C.-Z.P. and J.-W.P. developed the satellite, the payloads and the single-photon time-transfer techniques. H.D., Q.S., C.-Z.W., S.-L.L., W.-Y.L. and W.-Q.C. carried out the experiment with assistance from all other authors. F.X. and J.-W.P. analysed the data and wrote the manuscript, with input from H.D., Q.S., C.-Z.W., Q.Z. and C.-Z.P. All authors contributed to the data collection, discussed the results and reviewed the manuscript.
Corresponding authors
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Peer review information Nature Physics thanks Alexander Ling and the other, anonymous, reviewer(s) for their contribution to the peer review of this work.
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Supplementary Information
Supplementary Note, Fig. 1 and Tables 1 and 2.
Source data
Source Data Fig. 3
Source data for Fig.3 in main text.
Source Data Fig. 4
Source data for Fig. 4a–c in main text.
Rights and permissions
About this article
Cite this article
Dai, H., Shen, Q., Wang, CZ. et al. Towards satellite-based quantum-secure time transfer. Nat. Phys. 16, 848–852 (2020). https://doi.org/10.1038/s41567-020-0892-y
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1038/s41567-020-0892-y
This article is cited by
-
Enhanced Performance of Measurement-device-independent Quantum Key Distribution over Turbulent Channels through Adaptive Optics
Quantum Information Processing (2024)
-
Quantum-secured time transfer between precise timing facilities: a field trial with simulated satellite links
GPS Solutions (2024)
-
Coherent phase transfer for real-world twin-field quantum key distribution
Nature Communications (2022)
-
An integrated space-to-ground quantum communication network over 4,600 kilometres
Nature (2021)