Abstract
We develop a protocol for entanglement generation in the quantum internet that allows a repeater node to use n-qubit Greenberger-Horne-Zeilinger (GHZ) projective measurements that can fuse n successfully entangled links, i.e., two-qubit entangled Bell pairs shared across n network edges, incident at that node. Implementing n-fusion, for n ≥ 3, is in principle not much harder than 2-fusions (Bell-basis measurements) in solid-state qubit memories. If we allow even 3-fusions at the nodes, we find—by developing a connection to a modified version of the site-bond percolation problem—that despite lossy (hence probabilistic) link-level entanglement generation, and probabilistic success of the fusion measurements at nodes, one can generate entanglement between end parties Alice and Bob at a rate that stays constant as the distance between them increases. We prove that this powerful network property is not possible to attain with any quantum networking protocol built with Bell measurements and multiplexing alone. We also design a two-party quantum key distribution protocol that converts the entangled states shared between two nodes into a shared secret, at a key generation rate that is independent of the distance between the two parties.
Similar content being viewed by others
Introduction
The Quantum Internet will provide the service of generating shared entanglement of different kinds, between distant end-user pairs and groups, on demand, and at high speeds. The entanglement generation rate between two nodes decays linearly with the transmissivity η of the channel connecting them, which turns into an exponentially rate-vs.-distance decay over optical fiber, since η = e−αL for a length-L fiber1. The maximum attainable rate is \(-\log (1-\eta )\approx 1.44\eta\), for η ≪ 1, ebits (pure Bell states shared between two parties) per transmitted optical mode2. Quantum repeaters need to be inserted along the length of the optical channel in order to circumvent this rate-vs.-loss limit3,4,5. In6, the ultimate capacity of entanglement generation between two nodes was found, assuming the network nodes were fully-equipped quantum processors. A consequence of this result was that multipath routing can improve entanglement rates over that attainable by routing along one path.
There is a wide variety of repeater and router protocols being researched using practical devices and systems, most of which use Bell state measurements (BSMs) as a building block. BSM is a two-qubit destructive measurement that can fuse two entangled links (each entangled link being a two-qubit Bell state, each shared across a network edge) incident at a node, into one entangled link over a two-hop path. For a linear chain of repeater nodes, where each repeater is equipped with quantum memories and employs BSMs and switches, the entanglement rate outperforms what can be attained with a direct connection connecting the communicating end parties, but the rate still decays exponentially with distance, i.e., R ~ e−sαL, with s < 13.
Various genres of quantum repeaters and associated error-correction codes are under investigation4. For the purposes of our paper, we will consider the following simple model, and show a surprising result—that the end-to-end entanglement rate between two uses Alice and Bob remains constant with increasing distance when network nodes are able to measure more than two qubits in a joint projective measurement. In each time slot, each network edge attempts to establish an entangled link: a Bell state of two qubits, each residing in a quantum memory at nodes on either end of the link. In every time slot, each link is established successfully, i.i.d., with probability p proportional to the transmissivity of the optical link. Subsequently, each node, based on local link-state information (i.e., which neighboring links succeeded in that time slot), and knowledge of the location of the communicating parties Alice and Bob, decides which pairs of successful links to fuse. The two qubits that are fused with a BSM at a node are destroyed in the measurement process, while creating an entangled (Bell) state among the two qubits at the far ends of the two links, thus creating a 2-hop entangled link traversing two network edges. A fusion attempt succeeds with probability q. It was shown recently that with a simple distance-vector fusion rule, the achievable entanglement generation rate exceeds what is possible with a fusion schedule along a pre-determined single shortest path connecting Alice and Bob7. Despite this rate advantage from multipath entanglement routing, the rate decays exponentially with the distance L between Alice and Bob, for any value of p or q less than 1. Interestingly, this exponential scaling of rate with multipath routing, is at odds with the network’s capacity proven in6, according to which the end-to-end rate does not even depend upon the distance between communicating parties. The protocol we develop in this paper addresses this gap.
In this paper, we develop a protocol that allows nodes to use n-qubit Greenberger-Horne-Zeilinger (GHZ) projective measurements, i.e., n-fusions, that can fuse n successful links at a node. When n = 2, the nodes implement a two-qubit BSM. For n = 1, the nodes implement a single-qubit Pauli measurement. Implementing n-fusion, for n≥3 is in principle no harder than 2-fusions (Bell measurements) in qubit memories, e.g., color centers in diamond8, and trapped-ion quantum processors9. We take the success probability of an n-fusion attempts as q. We report a surprising result: if we allow even 3-fusions at the repeater nodes, there is a non-trivial regime of (p, q) where our protocol generates entanglement at a rate that stays constant with L. This result comes from the percolation theory. We prove this is not possible with any quantum network protocol that only uses Bell measurements if q < 1 (see Supplementary Note 3). Our protocol only uses local link state knowledge, but requires a single round of classical communications that adds to the latency of the protocol (but, does not affect the rate). It can be easily extended to share GHZ states between multiple users at distance-independent rate. To achieve this, all the users (recipients of qubits that are part of the distributed GHZ state) would not perform fusions on their qubits. We believe such a protocol would also exhibit a percolation like behavior but with higher percolation thresholds based on a recent result on percolation between multiple points in a network10.
Finally, we develop a quantum key distribution (QKD) protocol that allows a pair of users Alice and Bob, situated in a network, to sift (two-party) secret keys starting from a pre-shared m + n-qubit Greenberger-Horne-Zeilinger (GHZ) state, m qubits of which are held by Alice and n by Bob. It is an extension of the BBM’92 protocol11, a simplification of the E’91 protocol12, which relies on shared Bell states and measurements by Alice and Bob in a matching pair of bases. Using our above described quantum network protocol that employs n-fusions at nodes, we thus have devised a QKD protocol over a quantum network whose secret key generation rate is constant with increasing distance between communicating parties, despite lossy channel segments between nodes and probabilistic successes of the n-fusions at nodes.
In related work, refs. 13,14 map entanglement spreading in a network to bond percolation, where multiple copies of imperfect-fidelity bell pairs across a single link are purified (which succeed probabilistically) into perfect bell states, which are then connected using ideal BSMs. However, these papers don’t consider entanglement routing protocols, i.e., algorithms for delivering entanglement among specific parties with nodes acting only with local link-state information. For the same reason, they also do not calculate entanglement generation rates. Refs. 15,16 take advantage of percolation theory to evaluate the robustness of quantum networks that route entanglement using Bell state measurements. Ref. 17 uses imperfect Bell states and imperfect gates, to grow the size of entanglement through a succession of self-similar graph state structures, to establish the desired GHZ state in a quantum network. The paper doesn’t provide a rate calculation, and does not use joint three or more qubit projective measurement on the GHZ basis like we do for our protocol.
In Section Fusing entanglement using GHZ-state projections, we discuss the elementary multi-qubit projective measurements used in our protocol. Section The Protocol describes the entanglement distribution protocol. We also map the problem of distributing entanglement over a quantum network to a mixed percolation problem studied in classical statistical mechanics. We discuss the origin of distance-independence of the shared entanglement rate, along with numerical calculations of the rate and comparisons with capacity, in Section Entanglement rates and the improved variation of the protocol in Section Improved n-GHZ protocol. Section Quantum key distribution describes the QKD protocol using GHZ states. We conclude in Section Discussion by summarizing the results and discussing open questions that can be studied as immediate extensions and applications of the proposed protocol.
Results
Fusing entanglement using GHZ-state projections
We use entanglement swapping operations, namely, Bell State Measurements (BSMs) and n-qubit GHZ projections at network nodes, for routing entanglement in a quantum network. An n-qubit GHZ projection is a von Neumann projective measurement, that projects the n measured qubits into one of the (2n) mutually-orthogonal n-qubit GHZ states, thereby producing a (random) n-bit classical measurement result. The well-known BSM is a 2-qubit GHZ projection. Entanglement swapping at a quantum (repeater) node extends the range of entanglement by fusing two Bell states shared across two adjacent edges of the network.
We refer to n-qubit stabilizer states18 with stabilizer generators of the form \(\{{(-1)}^{{g}_{1}}{X}_{1}{X}_{2}\ldots {X}_{n},{(-1)}^{{g}_{2}}{Z}_{1}{Z}_{2},{(-1)}^{{g}_{3}}{Z}_{1}{Z}_{3},\ldots ,{(-1)}^{{g}_{n}}{Z}_{1}{Z}_{n}\}\), gi ∈ {0, 1} as n-GHZs, which includes the case of n = 2 i.e., Bell states. Xi and Zi are single-qubit Pauli operators for the ith qubit. We use the (unconventional) notation of an n-star graph to represent an n-GHZ. This is not a star-topology commonly-known cluster state19. Furthermore, we refer to a projective measurement onto the n-GHZ basis as a (n-qubit) fusion. The size of an n-qubit GHZ state is n. An n-fusion on a set of GHZ states of size m1, m2, . . . . mn results in a single GHZ state of size \(\mathop{\sum }\nolimits_{i = 1}^{n}{m}_{i}-n\), obtained by removing the qubits that are fused from the original set of qubits and coalescing all the unmeasured qubits into a single GHZ state, as shown in Fig. 1.
Depending upon the choice of quantum memory and processor hardware at the quantum repeater node, fusion operations may be probabilistic. We model the result of a failed fusion attempt as performing an X-basis measurement on all qubits that were used as part of the fusion, as shown in Fig. 1. Measuring a qubit of an n-GHZ state in the Pauli-X basis results in a (n − 1)-GHZ state, unentangled with the measured qubit, as shown in Fig. 2.
The protocol
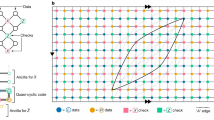
In this paper, we study two kinds of quantum networks: a two-dimensional square-grid, and a configuration-model random graph with a given node degree distribution20. First, let us consider a square-grid graph. Each node is a quantum repeater (blue circles in Fig. 3a) with four quantum memories (black dots in Fig. 3a) associated with each neighboring edge. Each repeater is either a ‘consumer’ of entanglement i.e., Alice and Bob, or a ‘helper’ i.e., they help to establish entanglement between the consumer nodes. In the first time step, each network edge attempts to establish an entangled link: a Bell state of two qubits, each residing in a quantum memory at nodes on either end of the link. Each link is established successfully, i.i.d., with probability p, which is proportional to the transmissivity of the respective optical link1,2. The repeater nodes have only local link-state knowledge, i.e., a repeater knows the success-failure outcomes at each time slot of its own link generation attempts (across its neighboring edges). Each repeater is also aware whether it is a consumer or a helper node, knows the overall network topology, and the location of the consumer nodes (if it is a helper node). In the next time step, all helper nodes that have more than one successfully created link, attempt fusions on the qubits held in their respective quantum memories tied to a subset of those successful links. The fusion success probability is taken to be q. A successful fusion at a repeater creates a Bell pair or a GHZ state shared between a subset of its neighbors. If a helper node has only one link success in a time slot, it performs an X-basis measurement on the corresponding locally-held qubit, which unentangles and dissociates that qubit from any others in the network.
a The quantum network after link generation. The successfully generated links are shown using black solid lines. The green triangles and rectangles denote the successful fusions. Their red counterparts represent the failed fusion attempts. The quantum memories marked in red perform X-basis measurements on the qubits held in them. b The three GHZ states (green, orange, and magenta lines) generated after performing fusions at the repeaters. b The m-qubit GHZ state shared between Alice and Bob (orange (m = 2), and magenta (m = 3) lines).
We consider three protocols for the square-grid network, which differ in the operations available at repeater nodes, and allow for different entanglement generation rates: (1) the 4-GHZ protocol, (2) the 3-GHZ protocol and (3) the 3-GHZ brickwork protocol.
In the 4-GHZ protocol, a repeater performs a fusion on all locally-held qubits successfully entanlged with neighboring nodes at each time step. Hence, the largest measurement in such a protocol is a 4-GHZ measurement, which is done when all 4 links are successfully created. In a time step when only 3 or 2 links are successful, a 3-GHZ measurement or a 2-GHZ (i.e., Bell) measurement is performed. If only one link is successful, the corresponding qubit is measured in the X-basis. In the 3-GHZ protocol, the maximum size of the GHZ projection allowed is limited to 3, which may be imposed due to hardware constraints. If the number of successful neighboring links of a helper node is less than or equal to three, the repeater performs a fusion between the corresponding qubits, i.e., behaves the same as the 4-GHZ protocol. However, if four neighboring links are successful, the repeater randomly chooses three qubits and performs a fusion on them. It performs an X measurement on the fourth remaining qubit if this happens. Every helper node sends its local link state knowledge, fusion success outcomes, and X-basis measurement outcomes to the consumers Alice and Bob using a classical communication overlay channel. This classical communication time determines the overall latency of the entanglement generation protocol, but the entanglement rate is determined by the rate at which each entangled link is attempted across each network edge.
It is important to note that all Bell state measurements, GHZ projections and Pauli X-basis measurements across the entire network are performed during the same time step. This is allowed because all of these operations and measurements commute with one another. At the end of this step, the consumers obtain (potentially more than one) shared m-qubit GHZ state(s) (2≤m≤8 for square grid) with a probability that depends on the network topology, p, q, and which of the two protocols described above is used. If the desired shared entangled state is a 2-GHZ or a Bell state, the consumers can easily convert the m-GHZ state into a Bell pair by locally performing X-basis measurements.
We discuss the rules for the Brickwork protocol in Section Improved n-GHZ protocol, which instead of being fully randomized as above, imposes some additional structure on which fusions to attempt, and can outperform the 3-GHZ protocol in certain regimes.
We also study the n-GHZ protocol for a random graph network, with an arbitrary node degree distribution pk. Here, pk is the probability that a randomly chosen node has degree k. In other words, it is the probability that a randomly chosen quantum repeater node has k edges. In an n-GHZ protocol, each repeater performs m-GHZ projections for fusions where \(m=\min (n,\,{{\mbox{no. of successful links at the repeaters}}}\,)\) i.e., repeaters can perform up to n-fusions. For the n-GHZ protocol over a random network, if a degree k helper node has l successful links in a time slot such that l ≤ n, it performs an l-GHZ fusion. If l > n, it performs an n-GHZ fusion on the n qubits corresponding to n randomly chosen links (of the l). The remaining steps are same as the 3- and 4-GHZ protocols described above for the square grid.
Immediately after the time slot when all helper nodes perform their measurements and sends, via unicast communications, the requisite classical communication to the consumer nodes, the network edges re-attempt entanglement generation in the next time step, and the helper nodes again make their measurements based on the protocol described above using local link state information, until the end of the protocol’s duration. The length of each time step determines the rate of the protocol, whereas the classical communication time determines the latency. Consumers hold on to all their qubits for the time required to receive the classical information regarding the results of measurements made during a specific time slot from every helper node in the network. They use the local link state knowledge from the helpers to determine which one of their qubits (from the corresponding time slot) are part of a shared entangled state held between Alice and Bob. In each time slot, Alice and Bob generate 0, 1, 2, 3, or 4 shared GHZ states. Each of those shared GHZ states could have more than 2 qubits. For example, Alice and Bob could generate one 3-qubit GHZ state two of whose qubits are held by Alice and one by Bob, and one 2-qubit GHZ (i.e., Bell) state one qubit of which is with Alice and the other with Bob.
At this point, Alice and Bob can use their shared entangled state for a quantum information processing protocol, e.g., QKD, entanglement enhanced sensing, or distributed quantum computing implemented by a teleported gate. If the protocol requires a particular n-GHZ state as a resource, it is always possible for Alice and Bob to correct the state by applying local unitary operations, or for some protocols such as QKD by correcting the outcome of the protocol during classical post-processing using the measurement results received from the helpers.
Entanglement rates
We calculate the shared entanglement generation rate for the square-grid topology of the quantum network under three different fusion rules (Fig. 3) as a function of link and fusion success probabilities (p, q) and the distance between the consumers. We define rate as expected number of n-GHZs (including Bell pairs) shared between the consumers per cycle. We can think of the quantum network shown in Fig. 3a as a graph G(V, E) such that each quantum memory is a vertex v ∈ V, and each link e ∈ E is created with probability p (a successfully created link Bell pair). Fusion operations are then executed at vertices with at least two neighbors creating a new graph \(G^{\prime} (V^{\prime} ,E^{\prime} )\). In this graph, \(v\in V^{\prime}\) is a quantum memory that has undergone a fusion operation. \(G^{\prime} (V^{\prime} ,E^{\prime} )\) has additional edges that represent the edges created between quantum memories at the same repeater due to successful fusions between vertices (green triangles or rectangles in Fig. 3a). In addition, consumers Alice and Bob have four vertices each. They share an entangled state at the end of the fusion stage, if they belong to the same connected component of graph \(G^{\prime}\). The number of GHZ states shared between Alice and Bob equals the number of disconnected sub-graphs of \(G^{\prime}\) containing at least one vertex each from both Alice and Bob. Hence, the maximum value the rate can take would be 4 m-qubit GHZ states/cycle where m ≤ 8 for a square grid network. In the following sections, we compute and compare the shared entanglement generation rates for the different protocols over square-grid and random networks. We refer to the protocol in which repeaters can perform up to n-qubit GHZ projections as n-GHZ protocol.
Perfect repeaters
We first study the case where repeaters always successfully perform fusions, i.e., q = 1. In the n-GHZ protocol over a certain network topology, calculating the probability that the consumers are a part of the same connected component of \(G^{\prime} (V^{\prime} ,E^{\prime} )\) translates to a bond percolation problem on the underlying network topology21. The link generation probability p is equivalent to the bond occupation probability in the percolation problem. Percolation is a phase transition phenomenon such that when p < pc (sub-critical regime), where pc is a threshold that depends on the lattice geometry, the probability that two randomly chosen sites are connected decays exponentially with distance between the two sites. On the other hand, if p > pc (super-critical regime), this probability remains constant with the distance. This result forms the basis of our protocols to achieve distance-independent shared entanglement generation rates.
In Fig. 4a, we plot the expected number of GHZ states shared by the consumers—at different Manhattan distance separations—at the end of each cycle for the 4-GHZ protocol, as a function of p. As expected, we see that as p goes above the bond percolation threshold of the square grid, \({p}_{c}^{(4)}=0.5\), (a) the rate increases sharply, and (b) the rate becomes independent of the separation between the consumers.
We see that (a) for the 4-GHZ protocol above the threshold p > pc, the entanglement rate becomes independent of the distance between communicating parties while it scales with the Manhattan distance when p < pc; and (b) for the random 3-GHZ protocol, the threshold pc is higher (0.53 versus 0.5) for the 3-GHZ protocol. The threshold pc for the 4-GHZ protocol is the standard bond percolation threshold of the 2D square lattice.
The 3-GHZ protocol described above translates to a different bond percolation problem on the square lattice, where up to 3 occupied bonds incident at a node can be stuck together to form connected components. For this problem, the bond percolation threshold \({p}_{c}^{(3)}\approx 0.53\) (Fig. 4b). For both of these fusion rules at the repeaters, when \(p \,>\, {p}_{c}^{(3)}\), the rate doesn’t decay exponentially with the distance between the consumers, but remains constant instead.
Imperfect repeaters
Depending on the quantum hardware used at the repeaters, fusion operations can be probabilistic22. In this paper, if a repeater fails to perform fusion, it is equivalent to performing X-basis measurements on the qubits involved in the fusion. Calculating the probability that a pair of users end up with shared entanglement when both link generation and fusions are probabilistic, now, becomes a site-bond percolation problem23 over the underlying network topology lattice (e.g., the square lattice). Site-bond percolation is the generalized version of a percolation problem in which sites and bonds are present with probabilities q and p, respectively. The boundary between the super- and sub-critical regimes becomes a curve in the (p, q) plane. For our protocol, the fusion success probability at each repeater translates to the site occupation probability q. Here, we assume that all fusion operations succeed with the same probability q. We analytically calculate the site-bond region for an n-GHZ protocol over a random graph in Supplementary Note 1. Figure 5(a) shows the site-bond region for the lattices formed after the fusion step in 3- and 4-GHZ projection protocols on a square-grid network, simulated using the Newman-Ziff method24 and 3-GHZ protocol on a constant degree-4 random graph network using the analytical formula. The site-bond curve gives the percolation thresholds (pc, qc) of the underlying lattice. The probability that the two consumers are connected is distance-independent when p > pc and q > qc. Thus, the link generation and fusion success probabilities need to lie above the site-bond curve to achieve distance-independent rate. To demonstrate this, we plot the rate as a function of distance for three pairs of (p, q) that lie in three different regions of the site bond curves of the 4- and 3- GHZ protocols in Fig. 5b.
a Site-bond percolation regions for the percolation problems corresponding to the 4-GHZ protocol over square-grid network, 3-GHZ protocol over square-grid and constant degree-4 random graph networks. The curves represent the critical regime of percolation. p and q need to lie above the curves for distance-independent rate. b Rate vs distance for points in three different regions of the site-bond curve marked in (a) for the square-grid network. The dashed and solid lines correspond to 4- and random 3-GHZ protocols, respectively.
Rate upper bound
Ref. 6 gave the capacity upper bound for a quantum network with repeaters that can perform arbitrary quantum operations, including multi-qubit projective measurements. This work transforms the entanglement routing protocol to a flow problem. A pair of achievability and converse proofs established that the capacity of generating entanglement between two network nodes Alice and Bob is given by the max-flow (or the min-cut) of the underlying network topology, where the capacity of an individual link of transmissivity η is \(-{\log }_{2}(1-\eta )\) ebits per mode2. This ultimate capacity of a square-grid network topology with equal link capacities, translates to \(-4{\log }_{2}(1-\eta )\) ebits/mode (see red dashed plot in Fig. 6). This hence must serve as an upper bound for rates achieved by our protocol.
Upper bound to our 4-GHZ protocol’s rate F(p)2, the actual rate attained by our protocol when nodes use 4-GHZ projections, the actual rate attained by our protocol when nodes use 3-GHZ projections, upper bound from6 given by the max-flow, and the ultimate capacity (\(-4\log (1-\eta )\)) as a function of channel transmissivity η. Alice and Bob are assumed to one hop away from the diametrically-opposite corner points of a 100-by-100 square grid.
The most natural realization of the protocols presented in this paper would be with single-photon dual-rail (e.g., polarization-encoded) qubits. For this qubit encoding, if everything else other than the link loss were ideal (unit-efficiency memory, perfect detectors, deterministic entanglement sources with no multi-pair emissions), the success probability of a link, per mode, p = η. When q = 1, the max-flow is given by 4p (see green dotted plot in Fig. 6), which serves as an upper bound to the rates achieved by our specific protocols. To achieve the high rates at low loss predicted by6, one must use high-order, e.g., continuous-variable modulation formats.
This upper bound of 4p is clearly independent of the distance between the consumers Alice and Bob, which is consistent with our protocol’s having such a property. Ref. 6’s result implies that this upper bound would be achievable with perfect quantum memories and perfect BSMs at all nodes. This is simple to see since the link-level entangled qubit pairs can be stored perfectly for a long time. So, after k time steps, each link would have accumulated roughly kp successfully entangled Bell states, at which point, they can be connected into 4kp end-to-end Bell states along four edge-disjoint paths connecting Alice and Bob using BSMs, achieving a rate of 4kp/k = 4p ebits per cycle.
For our protocol, this upper bound is not achievable because we assume limited memory coherence time (equivalent to the classical communication latency of a link), limited quantum processing available at every node, and act without the advantage of global link-state knowledge. Assuming that the consumers are far apart, when \(p \,<\, {p}_{c}^{(l)}\), for l = 3 or l = 4 (depending upon which of the two protocols is being used), with high probability, they will not share a connected path. When \(p \,>\, {p}_{c}^{(l)}\), the consumers will with high probability, we part of the giant connected component (GCC), a unique O(N)-size connected component where N is the total number of bonds in the underlying network. Hence, in this super-critical regime, at the end of each cycle, with high probability, the consumers share a perfect GHZ state.
Let us say that the probability of a random node belonging to the GCC is F(p). In order for Alice and Bob to share a GHZ state at the end of a cycle, they both have to be a part of the GCC. Hence, the rate achieved by our protocol is upper bounded by F(p)2 (see black dash-dotted plot in Fig. 6). Finally, we plot the actual rates achieved by our 4-GHZ and 3-GHZ protocols for comparison, in Fig. 6 (solid magenta and blue dash-dotted, respectively).
Improved n-GHZ protocol
We observe a curious turnaround in the site-bond curves for the 3-GHZ and some n-GHZ protocols over square-grid and random networks, respectively. For the 3-GHZ protocol, when two neighboring repeaters have four link successes each and they are limited to doing 3-GHZ projections, while one repeater might sacrifice the shared edge, the other might not as the repeaters don’t communicate with each other to decide which links to choose to perform fusion on. It effectively disconnected the two repeaters even though they shared a link. This effect is even more pronounced when q < 1 because a repeater might choose to fuse with a failed neighboring repeater instead of a functioning one. This negatively affects the overall connectivity of the lattice. As a result of the adversarial nature of the rule, in high p regime, the rate starts decaying with p when q < 1 (Fig. 7), which shows that the rule is sub-optimal. The site-bond region for this 3-GHZ fusion rule clearly depicts this behavior in Fig. 5a. Similar arguments can be made to explain the turnaround for the n-GHZ protocol for the random network. In the following sections, we discuss three strategies to improve the turnaround.
Thinning the network
Let p* be the link generation probability at which the turnaround occurs. The adversarial behavior of the protocol is observed only beyond p*. We can get rid of the turnaround by randomly removing links in the high p regime. We modify the protocol such that when p > p*, each link is deleted with probability (p − p*)/p. This makes the effective link generation probability p* when p > p* as shown in Fig. 5a.
The Brickwork network
The random selection of the links to fuse degrades the rate when repeaters can fail. To overcome this issue, we propose a deterministic link selection rule that doesn’t let neighboring repeaters make conflicting fusions. Consider the square-grid topology of the quantum repeaters. This network has two types of links - red and black. Both red and black links have the same success probability p. Links are arranged such that the black links form a brickwork lattice. Each repeater has a maximum three black links and one red link. In the fusion step of the protocol, a repeater uses the red link only if it has two or fewer black links, as shown in Fig. 8b. This protocol is equivalent to percolation over a brickwork lattice with an extra optional bond at each site. Hence, we observe in Fig. 9 that the repeater success probability threshold is equal to the site percolation threshold of the brickwork lattice. And the link success probability is higher than the bond percolation threshold of the brickwork lattice due to the additional bond. This fixed selection rule gets rid of the adversarial nature of the previous protocol without having neighboring repeaters communicate with each other. Figure 8c shows the rate vs. link success probability (p) curve doesn’t decay when the repeaters fail to perform fusions (q < 1).
The brickwork protocol over the square-grid network - (a) The dotted lines show the red and black link generation attempt. The dotted black lines form a brickwork lattice. (b) Red links are used for fusion only if there are less than 3 black links present. (c) Comparison between the 3-GHZ protocol and the brickwork protocol for q = 0.85 and Manhattan distance = 85 units. The rate for the brickwork protocol does not degrade when p is high and q < 1 but stays constant irrespective of distance.
The brickwork model can be adapted for random graphs as well by dividing the edges into two categories - black and red. The lattice formed by the black edges is not a brickwork lattice in this case. For the n-GHZ protocol over a random network to make the protocol partially deterministic, each node can have maximum n black edges and the rest are red edges. If the total number of edges at a node is less that n, all of them are black. Each repeater (node) uses the red links for fusion only if it has less than n black links. We compare the site-bond regions for the 3-GHZ brickwork protocol for various network topology with mean degree ≈ 4. We observe that configuration graphs do better than the square-grid as they offer long-range connectivity. We notice that although this strategy improves the site-bond region, it doesn’t remove the turnaround for all combinations of network topologies and n as shown in Supplementary Fig. 3. The analytical expression for the site-bond region of this brickwork-like model for random graphs is derived in Supplementary Note 2.
Dividing the network
As discussed earlier, the entanglement generation rate is proportional to the number of disconnected sub-graphs of the graph generated after fusion (\(G^{\prime} (V,E)\)) that are shared between the consumers. In the high (p, q) regime, for the square-grid network, due to 3-/4-qubit projections, as the overall connectivity of \(G^{\prime} (V,E)\) improves, its disconnected sub-graphs start merging together. Hence, this framework fails to achieve the maximum rate possible for the underlying network topology, (4-GHZ states/cycle in our case). When p and q both equal one, we end up with only one GHZ state shared between the consumers. This issue can be overcome by dividing the network into four disconnected sub-graphs such that exactly one quantum memory from each consumer resides in one sub-graph. The sub-graphs are never allowed to merge into each other by permanently erasing the edges joining them.
Quantum key distribution
In this section, we briefly discuss a Quantum Key generation protocol to share a secret key between a pair of users using GHZ states. This protocol is an extension of the BBM’92 quantum key distribution protocol11. The protocol consists of the following steps -
-
Step 1: Alice and Bob start with multiple m + l ≥ 2 qubit GHZ states such that Alice and Bob have m- and l qubits of the GHZ state.
$$\left|{\psi }_{AB}\right\rangle =\frac{{\left|0\right\rangle }_{A}^{\otimes m}{\left|0\right\rangle }_{B}^{\otimes l}+{\left|1\right\rangle }_{A}^{\otimes m}{\left|1\right\rangle }_{B}^{\otimes l}}{\sqrt{2}}$$Here, m and l can vary across the collection of shared GHZ states Alice and Bob possess.
-
Step 2: They independently and randomly choose between the computational basis (0/1-basis) and the Hadamard basis (+/− -basis) for measurement. Each user measures all their qubits of the GHZ state using (their) randomly chosen measurement. Alice and Bob get m − and l - bit results, respectively, after performing the measurements.
-
Step 3: They use a classical channel to inform each other the basis they have used to measure their respective qubits. The measurements instances where Alice and Bob used the same basis are used for key generation. This step is similar to the BBM’92 protocol.
-
Step 4: If both of them used the computational basis in a given round of the protocol, they get bit string of either all 0’s or all 1’s. In this case, that bit becomes the key. When Alice and Bob both use the Hadamard basis, they get measurement outcome bits strings a1a2…am and b1b2…bl, respectively, such that \(({a}_{1}+{a}_{2}+\cdots +{a}_{m})\,{{\mathrm{mod}}}\,\,2=({b}_{1}+{b}_{2}+\cdots +{b}_{l})\,{{\mathrm{mod}}}\,\,2\). Here, the key would be the parity of their respective bit strings.
An example of this protocol is shown in Table 1. We leave the security proof for this protocol as an open question. But we believe that it can be done as an extension of the security proof for BBM’92.
Discussion
We have designed a quantum-network-based entanglement generation protocol, which affords a rate that is independent of the distance between the users. The protocol only uses local link state information, and has the aforesaid property of distance-independent entanglement rate in a certain region of the link-level entanglement success probability p (which is proportional to the link’s optical transmissivity, and hence range) and an individual repeater’s success probability q (in performing an n-GHZ projective measurement). This (p, q) region that achieves distance-independent rate is the site-bond region of a modified mixed percolation problem, defined on the underlying network such that the bond and site occupation probabilities are given by the link generation and repeater success probabilities, respectively. Our protocol requires only certain local Clifford operations, Pauli measurements, and classical communications. We perform multi-qubit projections at each node of the 2D network making it a multipath routing protocol. It outperforms the multipath routing protocol that only uses Bell state measurements (BSMs)7. All BSM based entanglement protocols exhibit rates that decay with distance even those that use non-local-link state knowledge. To study our protocol for complex quantum networks, we analytically derived the site-bond region for a configuration-model random network with an arbitrary node degree distribution. This shows an excellent match with the numerically-evaluated site-bond region of our modified mixed percolation problem using the Newman-Ziff algorithm. We also discussed a two-party quantum key distribution protocol that can be implemented using the shared entangled state obtained from the entanglement generation protocol.
A few other questions that can be solved as an extension of this protocol are - (1) generating shared entanglement between multiple consumer pairs simultaneously (2) The repeater failure model we have assumed here is very simple. One can study more realistic models repeater failure due to unsuccessful fusions, photon loss, etc. The effects of noisy quantum state and gate imperfections are to be explored in the future. This problem would also require entanglement purification scheduling to achieve good quality entangled states at the end of the protocol. We do expect, however, that when GHZ projections are allowed at network node, even if the link-level (Bell state) entanglement is noisy, i.e., subunity Fidelity, there will still be a percolation-threshold-like region–between the parameters p (link success probability), F (fidelity of the individual link level Bell state), and q (success probability of the GHZ projection at any network node), when the end to end rate, now defined as the distillable entanglement rate measured in ebits per second at a target Fidelity, will go through a phase transition.
Data availability
The data sets generated during and or analyzed during the current study are available from the corresponding author on reasonable request.
Code availability
The code used to generate this data will be made available to the interested reader upon reasonable request.
References
Takeoka, M., Guha, S. & Wilde, M. M. Fundamental rate-loss tradeoff for optical quantum key distribution. Nat. Commun. 5, 5235 (2014).
Pirandola, S., Laurenza, R., Ottaviani, C. & Banchi, L. Fundamental limits of repeaterless quantum communications. Nat. Commun. 8, 15043 (2017).
Guha, S. et al. Rate-loss analysis of an efficient quantum repeater architecture. Phys. Rev. A 92, 022357 (2015).
Muralidharan, S. et al. Optimal architectures for long distance quantum communication. Sci. Rep. 6, 20463 (2016).
Pant, M., Krovi, H., Englund, D. & Guha, S. Rate-distance tradeoff and resource costs for all-optical quantum repeaters. Phys. Rev. A 95, 012304 (2017).
Pirandola, S. End-to-end capacities of a quantum communication network. Commun. Phys. 2, 1–10 (2019).
Pant, M. et al. Routing entanglement in the quantum internet. npj Quantum Inf. 5, 1–9 (2019).
Bhaskar, M. K. et al. Experimental demonstration of memory-enhanced quantum communication. Nature 580, 60–64 (2020).
Brown, K. R., Kim, J. & Monroe, C. Co-designing a scalable quantum computer with trapped atomic ions. npj Quantum Inf. 2, 16034 (2016).
Manna, S. & Ziff, R. M. Bond percolation between k separated points on a square lattice. Phys. Rev. E 101, 062143 (2020).
Bennett, C. H., Brassard, G. & Mermin, N. D. Quantum cryptography without bell’s theorem. Phys. Rev. Lett. 68, 557–559 (1992).
Ekert, A. K. Quantum cryptography based on bell’s theorem. Phys. Rev. Lett. 67, 661–663 (1991).
Acín, A., Cirac, J. I. & Lewenstein, M. Entanglement percolation in quantum networks. Nat. Phys. 3, 256–259 (2007).
Perseguers, S., Cavalcanti, D., Lapeyre Jr, G., Lewenstein, M. & Acín, A. Multipartite entanglement percolation. Phys. Rev. A 81, 032327 (2010).
Das, S., Khatri, S. & Dowling, J. P. Robust quantum network architectures and topologies for entanglement distribution. Phys. Rev. A 97, 012335 (2018).
Khatri, S., Matyas, C. T., Siddiqui, A. U. & Dowling, J. P. Practical figures of merit and thresholds for entanglement distribution in quantum networks. Phys. Rev. Res. 1, 023032 (2019).
Wallnöfer, J., Zwerger, M., Muschik, C., Sangouard, N. & Dür, W. Two-dimensional quantum repeaters. Phys. Rev. A 94, 052307 (2016).
Poulin, D. Stabilizer formalism for operator quantum error correction. Phys. Rev. Lett. 95, 230504 (2005).
Nielsen, M. A. Cluster-state quantum computation. Rep. Math. Phys. 57, 147–161 (2006).
Newman, M. E., Strogatz, S. H. & Watts, D. J. Random graphs with arbitrary degree distributions and their applications. Phys. Rev. E 64, 026118 (2001).
Grimmett, G. What is percolation? In Percolation, 1–31 (Springer, 1999).
Ewert, F. & van Loock, P. 3/4-efficient bell measurement with passive linear optics and unentangled ancillae. Phys. Rev. Lett. 113, 140403 (2014).
Hammersley, J. M. Comparison of atom and bond percolation processes. J. Math. Phys. 2, 728–733 (1961).
Newman, M. E. J. & Ziff, R. M. Fast Monte Carlo algorithm for site or bond percolation. Phys. Rev. E 64, 1–16 (2001).
Acknowledgements
We thank Stefano Pirandola for useful discussions. A.P. and S.G. acknowledge the National Science Foundation (NSF) EFRI-ACQUIRE program, grant number ECCS-1640959. D.T.’s work was supported in part by the NSF under grant CNS-1617437.
Author information
Authors and Affiliations
Contributions
M.P., D.E., and S.G. conceived the idea. A.P., M.P, D.T, and S.G. developed the theory. A.P. performed the simulations. M.P. developed the QKD protocol. D.T. and S.G. helped A.P. to develop the configuration graph model and verified the calculations. All authors discussed the results and contributed to the final manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Patil, A., Pant, M., Englund, D. et al. Entanglement generation in a quantum network at distance-independent rate. npj Quantum Inf 8, 51 (2022). https://doi.org/10.1038/s41534-022-00536-0
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41534-022-00536-0