Abstract
Reliable communication on the Internet is guaranteed by a standard set of protocols, used by all computers1. Here we show that these protocols can be exploited to compute with the communication infrastructure, transforming the Internet into a distributed computer in which servers unwittingly perform computation on behalf of a remote node. In this model, which we call ‘parasitic computing’, one machine forces target computers to solve a piece of a complex computational problem merely by engaging them in standard communication. Consequently, the target computers are unaware that they have performed computation for the benefit of a commanding node. As experimental evidence of the principle of parasitic computing, we harness the power of several web servers across the globe, which—unknown to them—work together to solve an NP complete problem2.
This is a preview of subscription content, access via your institution
Access options
Subscribe to this journal
Receive 51 print issues and online access
$199.00 per year
only $3.90 per issue
Buy this article
- Purchase on Springer Link
- Instant access to full article PDF
Prices may be subject to local taxes which are calculated during checkout



Similar content being viewed by others
References
Peterson, L. L. & Davie, B. S. Computer Networks, A Systems Approach 2nd edn (Morgan Kaufmann, San Francisco, 2000).
Garey, M. & Johnson, D. S. Computers and Intractability: A Guide to the Theory of NP-completeness (Freeman, San Francisco, 1979).
Boole, G. An Investigation of the Laws of Thought, on Which Are Founded the Mathematical Theories of Logic and Probabilities (Dover Advanced Mathematics, Macmillan, London, 1854).
Alderman, L. M. Molecular computation of solutions to combinatorial problems. Science 266, 1021–1024 (1994).
Ouyang, Q., Kaplan, P. D., Liu, S. & Libchaber, A. DNA solution of the maximal clique problem. Science 278, 446–449 (1997).
Schöning, U. in Proc. 40th Annu. IEEE Conf. Found. Comp. Sci. (FOCS) 410–414 (IEEE Comp. Sci., Los Alamitos, California, 1999).
Stevens, W. R. TCP/IP Illustrated 144–147 (Addison-Wesley, Reading, Massachusetts, 1994).
Stone, J. & Partridge, C. in Proc. ACM SIGCOMM 309–319 (2000).
Stone, J., Greenwald, M., Partridge, C. & Hughes, J. Performance of checksums and CRCs over real data. IEEE Trans. Networking 6, 529–543 (1998).
Foster, I. Internet computing and the emerging grid. Nature Web Matters at http://www.nature.com/nature/webmatters/grid/grid.html (7 Dec. 2000).
Cohen, R., Erez, K., ben-Avraham, D. & Havlin, S. Resilience of the Internet to random breakdowns. Phys. Rev. Lett. 85, 4626–4629 (2000).
Cohen, R., Erez, K. ben-Avraham, D. & Havlin, S. Breakdown of the Internet under intentional attack. Phys. Rev. Lett. 86, 3682–3685 (2001).
Lawrence, S. & Giles, C. L. Accessibility of information on the web. Nature 400, 107–109 (1999).
Lawrence, S. & Giles, C. L. Searching the World Wide Web. Science 280, 98 (1998).
Acknowledgements
We thank M. Crovella, G. W. Flake, L. Giles, S. Lawrence, D. Peenock and L. Peterson for comments on the manuscript. This work was supported by the NSF.
Author information
Authors and Affiliations
Corresponding author
Supplementary information
41586_2001_BF35091039_MOESM1_ESM.pdf
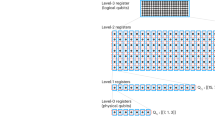
1. Encoding 3-SAT problem using TCP checksum. 2. Computing with TCP. 3. Algorithm. 4. Implementations. 5. Scalability. and references.
Rights and permissions
About this article
Cite this article
Barabási, AL., Freeh, V., Jeong, H. et al. Parasitic computing. Nature 412, 894–897 (2001). https://doi.org/10.1038/35091039
Received:
Accepted:
Issue Date:
DOI: https://doi.org/10.1038/35091039
This article is cited by
-
Bonus computing: towards free-of-charge metacomputing in the public cloud
Computing (2022)
-
Cloud-based evolutionary algorithms: An algorithmic study
Natural Computing (2013)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.